Administration - Web Console
The effectiveness of your Ivanti Application Control for Linux system requires the administration of policies, devices and rules tailored to meet the requirements of your organization. Administration is performed using the Web Console and this help page section describes the concepts and functionality available.
Accessing the Web Console
Access to the administration console is only available to users who are able to authenticate with either a local Windows account or Active Directory credentials. Both the user name and password need to be created before access is granted. Other than the Home page, you are prompted to input a user name and password for access.
Sessions timeout after 5 minutes of inactivity.
Home Tab
The Home tab is the entry point to the web console. It acts as a dashboard, displaying the most relevant data from your system. The Home tab includes links to further resources such as Help, Support, Community Articles and Ivanti-specific training.
Policies Tab
The Policies tab is where you create new policies and manage existing ones.
All Device Policies Section
The All Device Policiess section lists all policies, displaying their deployment, contents, current status and execution mode.
-
Select the ellipses icon menu to access relevant functions. The menu includes options to view deployed/active policies, duplicate existing ones, edit draft policies, and remove policies.
-
Policies can be edited or removed only until they are deployed. Once successfully deployed, the policy becomes active.
-
Deployed (active) policies can only be viewed or duplicated; they cannot be edited or removed.
New Policy Section
The New Policy section enables you to create policies, create a version for the policy, compose a rule set, create the list of devices where policies will be deployed - and establish the mode (Audit or Restrict) in which the new policy will behave on the targeted Linux endpoints. Please note, a version for the policy needs to be created before you are able to create rules. Also, each policy needs to have a unique name (alpha-numeric).
On an individual rule you can specify if the execution of the target should be allowed or denied. The rule includes full or relative paths or binaries.
If required, you can use environment variables and symbolic links. To view examples, refer to the Rule Set Examples section.
For binaries, the Use Hashing option allows you to ensure the target is identified by signature rather than location. This means that even if the target is copied into another location, the enforcement of the rule cannot be circumvented. Refer to Configuration for further information on the use of hashing.
The list of rules allows you to filter rules and further inspect them. Functions allow you to edit previously existing rules, modify their type (Allowed or Denied), enable, or disable the use of hashing, enable, or disable a rule entirely, or remove it from the list.
Add Devices Tab
The Add Devices tab enables you to specify where you want your policy to be deployed. You can add individual devices or groups of devices. For further information refer to Deployment to Groups.
The list of Added Devices indicates if a device belongs to any group, and if a policy is currently active for that device. You can filter the list, and/or remove individual or multiple devices.
Notes
-
Until a policy is deployed it can be edited. You are advised to periodically save your changes (for further information refer to Save Without Deploying).
-
In the Deploy Policy tab you can see a summary of your policy, and save or deploy the created rules to the device(s) specified.
Devices Tab
The Devices tab lists devices that are registered to your server instance.
In the list of devices you can view: whether the device belongs to a group, whether they have an active policy, and the deployment progress and/or status of that policy.
The list can be filtered for ease of navigation and administration.
View Device Details
To view device-specific details select the required device name from those listed. Device details are displayed in four tabs:
-
Device Summary
The Device Summary summarizes relevant hardware, software, and network information. The information is extracted at the point of registration from the Linux distribution installed on the device.
-
Restrict Log Tab
Restrict Log shows all the information pertaining to restrictions on the device in a new, filterable format. Administrators can now easily sort through and search the events that show what as been restricted as part of the policy.
The data can be filtered for ease of navigation and further inspection. It can be valuable in troubleshooting the current state of your endpoint.
For those familiar with the Debug Info tab (prior to 2021.4), logs can be found in the ACDatabase, under dbo.DebugInfo , via an sql query. However, the old data will not be displayed in the console due to changed formatting.
See also Audit vs Restrict for further information.
-
Audit Log Tab
Audit logs detail Application Control-specific events as they are audited and reported from the Application Control for Linux engine on the device. The audit log events are based upon the operations executed and include operations executed by the system, various systems services, individual applications, or by users.
Events are audited whether the deployed policy mode is Audit or Restrict. Audited events apply to the currently active policy (including policy defaults and local allowlisting).
Audit log data can be filtered for ease of navigation and inspection and is valuable in auditing the current behavior of your endpoint - whether allowed and denied.
See also Audit vs Restrict for further information.
-
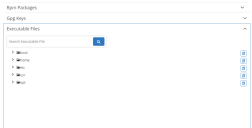
Device Contents
Local Allowlist Changes - This is an RPM package and GPG keys extractor.
Once the device and backend connection have been established, the information will start to flow and collect on the backend and DB side.
The Refresh RPM information button is an on-demand action that will refresh the table when new keys or new RPM packages have been added to the Linux endpoint.
-
Executable Files
The list can be searched for specific file names so their location in the hierarchy can be quickly identified. Having identified an executable that the administrator would like to add to a policy, there is a new button that copies the full path to the clipboard, eliminating errors in typing the path manually.
Device Groups
The Device Groups tab allows you to organize your registered devices into logical groups.
The groups are listed and the number of devices included currently is displayed. To remove a device group select the ellipses icon to open the context menu, then select Remove.
The list can be filtered for ease of navigation and administration.
Create a Group Section
The Create a Group section allows you to organize your devices into a new logical group.
Add Devices
Devices can only belong to one group at a time.
The add devices search returns only relevant registered devices, note that this will exclude any device that is currently a group member.
Note: If a device belonging to one group is added to a new group its original group membership is removed.
Devices (list)
The list of devices allows you to filter, and then further inspect added devices. The list displays current group membership for the devices and their currently active policies.
Group member devices can be selected individually or in multiples and removed using the Remove button.
Import Devices
Import bulk registered devices into groups from the Registered Devices list in the console.
The file format needs to be csv.
If you click on Import Devices button, a dialog will appear allowing you to select a csv file. Ensure the correct file is selected, if an incorrect file is selected, nothing will be imported.
Related Topics:
Installation (opens UWM Help)