Advanced Settings
Advanced Settings are accessed from the Manage ribbon and allow you to assign global settings to the Application Control Configuration file. Specify the required global components using the Policy Settings and Custom Settings tabs.
In this section:
Policy Settings
Application Control Policy Settings are available in the Advanced Settings dialog and provide general Application Control settings to apply to all application and process execution requests.
General Features
| Option | Description |
|---|---|
| Make local drives allowed by default | The configuration default for local drives is a blacklist, meaning that everything on the local drive is allowed unless it fails trusted ownership checking or is specified in a Denied Items list . Deselect this option to make the configuration a whitelist, so that everything on the local drive is blocked unless it is specified in an Allowed Items list. |
| Allow cmd.exe for batch files | It is expected that administrators explicitly prohibit cmd.exe in their Application Managers configuration. When cmd.exe is denied and 'Allow cmd.exe for batch files' is disabled, batch files will be evaluated and blocked if they fail the Application Managers policy. If the option is not selected and cmd.exe is explicitly denied, all batch files are blocked, they aren't even evaluated. If this option is selected and cmd is explicitly denied, cmd.exe still can't be run on its own, but batch files are evaluated against Application Control rules. If cmd.exe is not explicitly denied, all batch files run no matter whether this option is ticked or not. |
| Ignore restrictions during logon | During logon the computer may execute a number of essential applications. Blocking these can cause the computer to function incorrectly, or not at all. Hence, this option is selected by default. |
| Extract self-extracting ZIP files | A self-extracting
file is an executable that contains a ZIP file and a small program
to extract it. These files are sometimes used as an alternative
to installing an application by an MSI file. A number of administrators
prefer applications to only be installed by an MSI file.
Only self-extracting EXEs formatted using the ZIP specification are supported. For additional information, see ZIP Specifications The Extract self-extracting ZIP files option allows a denied executable file, which is a self-extracting ZIP file, to be extracted by the ZIP Extractor. If this option is deselected (the default setting) the file is subject to the normal rule processing as though it is an executable file. Once the contents have been extracted, any executable content it contains is still subject to the normal Trusted Ownership checks and is prevented from executing if the user is not a Trusted Owner. This is useful for scenarios where the self-extracting ZIP file may contain non-executable content such as a document that the user requires. By default, this option is deselected, and the self-extracting ZIP file is treated as a standard executable and can be prevented from executing (and hence extracting its contents) subject to the normal rule processing. |
| Ignore Restrictions during Active Setup | By default, all applications which run during Active Setup are subject to Application Control rules. Select this option to make these applications exempt from rules checks during Active Setup phase. |
| Use Signature Rules only to allow files on removable media |
Select this option (default setting)
to remove the global restrictions on removable media and switch to Signature Rules for governance.
Removable media is whatever the call to GetDriveType determines
it to be. Due to the nature of removable media, the drive letter
may change depending on how an endpoint is setup. For example:
On one computer the removable media drive may be identified as
the E: drive and on another F:
When this setting is enabled, a file on removable media can only be allowed with a Signature Rule. |
| Deny files on network shares | The configuration default for network shares is a whitelist, meaning that everything on the network share is denied unless it is specified in an Allowed Items list. Deselect this option to make the configuration a blacklist, so that everything on the network share is allowed unless it fails trusted ownership checking or is specified in a Denied Items list. |
Validation
| Option | Description |
|---|---|
| Validate System processes | Select this option to validate any files executed by the system user. Note that it is not recommended to select this option as it increases the amount of validation occurring on the endpoint computer and can block crucial applications from running. Selecting this option means all executables launched by the system are subject to rule validation. |
| Validate WSH (Windows Script Host) scripts | Selecting this option
specifies that the command line contents of scripts ran using
wscript or cscript are subject to rule validation.
Scripts can introduce viruses and malicious code. It is recommended to validate WSH scripts. |
| Validate MSI (Windows Installer) packages | MSI files are the standard method of installing Windows applications. It is recommended that the user is not allowed to freely install MSI applications. Selecting this option means all MSIs are subject to rule validation. Deselecting this option means that only the Windows installer itself, msiexec.exe, is validated by the Application Control rule processing, and not the MSI file that it is trying to run. |
| Validate Registry files | Select this option
to enable rule validation for regedit.exe and regini.exe.
Deselecting this option means that the regedit.exe
and regini.exe, is no longer blocked by default. Additionally,
the .reg script, the regedit.exe and regini.exe it is trying to
run is no longer validated by Application Control rules processing.
It is not recommended to allow users to access the registry or registry files. |
| Validate PowerShell scripts | When enabled, this setting denies powershell.exe and powershell_ise.exe. However, if a PowerShell script (PS1 file) is found on the command line, then, it is subjected to a full rules check to see if it is configured for elevation, allowed, or denied. |
| Block -Command |
For security purposes, when enabled (default condition in new configurations), any PowerShell command lines that includes -command will be blocked. To shift to a different security level, any admin needs to uncheck this option. When running a PowerShell script from Explorer, by right-clicking a ps1 file and selecting Run with PowerShell, Explorer will add -command automatically to query the current Execution Policy and prompt the user asking them if they want to change it. For Application Control to evaluate ps1 files run via Explorer’s right-click menu item Run with PowerShell, and not just block them, disable the Block -Command option. Please see the Ivanti Community article Validate PowerShell scripts does not work if the command line contains "-command" for further details. You will need to log into Ivanti Community to access. Be aware that when unchecked, any ps1 trusted file can be modified with malicious code inserted via a -command argument and will run because the file, itself, is trusted. |
| Validate Java archives | When enabled, this setting denies java.exe and javaw.exe. However, if a Java archive (JAR file) is found on the command line, then, it is subjected to a full rules check to see if it is allowed or denied. |
Functionality
| Option | Description |
|---|---|
| Enable Application Access Control | Select to enable Application Access Control. Deselect to not validate or block executables. |
| Enable Application Network Access Control | Select to enable the Application Network Access Control feature. Deselect to not validate or block outbound network connections. |
| Enable User Privilege Management | Select to enable the User Privilege Management feature. Deselect to not apply any User Privilege policies. Disabling this option allows all applications to run with the permissions and privileges provided by default, by operating system. Application Control ignores anything in the User Privileges section of the rules and will not change or alter any of the user's privileges. |
| Enable URL Redirection | Select to enable the URL Redirection feature. If you deselect this option, configured redirections are ignored and users are not redirected when they enter a suspicious or unwanted URL. Any URL allows you have configured will also not execute. Deselecting this option has the same effect as having no items in the Browser Control policy set and selecting this feature. When you disable this feature the browser extensions are disabled. See also Browser Control. |
Signatures
| Option | Description |
|---|---|
| Algorithm |
Select the algorithm type. There are three options available:
•SHA1 •SHA256 •Adler3 For more information, see Signature Hashing. |
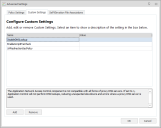
Custom Settings
Custom Settings allow you to configure additional settings which will be applied on managed endpoints when an Application Control configuration is deployed. If a new configuration is deployed that contains new custom settings, any pre-existing custom settings in place on the end point will be deleted.
Manage Custom Settings
- Open a configuration in the Application Control Console and navigate to the Manage ribbon.
-
Click Advanced Settings and select the Custom Settings tab.
The Configure Advanced Settings dialog displays.
- Select the Custom Settings tab and click Add to display the list of advanced settings.
-
Select the settings you want to configure and click OK.
-
The selected settings are added to the Configure Advanced Settings dialog.
Settings which are added will be configured on the endpoint. However, any setting which already exists on an endpoint will be used.
- Set the values as required.
- Click OK.
The settings are applied when the configuration is deployed to your managed endpoints.
Available Custom Settings
| Setting | Data Type | Description |
|---|---|---|
| ADComputerGroupMembershipTimeoutSecs | Numeric | Timeout, in seconds, for nested computer group lookups. The default setting is 120 seconds and setting this value to 0 disables the timeout. |
| ADQueriesEnabled | Numeric | This setting controls the types of AD queries used to determine the system's Distinguished Name and computer group membership. A value of 0 disables queries made to AD and the use of computer groups and OU in the configuration. The default value of 1 causes the agent to perform both the Distinguished Name and direct (non-nested) computer group AD queries. Nested computer groups in the configuration are ignored. A value of 2 causes the agent to perform the Distinguished Name, direct and nested computer group AD queries. This setting could cause performance issues on the DC due to high CPU usage. |
| AgentAssistWaitTime | Numeric | Timeout (in seconds) when waiting for an Agent Assist process to start. Setting this value to 0 disables the timeout. |
| AlternateTOCheck | Numeric | Trusted Ownership checks have occasionally caused excessive CPU usage in the SYSTEM process when third party filter drivers are installed on the system. Enabling this setting, using a value of 1, causes Application Control to use an alternative method of looking up Trusted Ownership, which mitigates this issue in some cases. |
| AMFileSystemFilterFailSafe | Numeric | This setting configures whether the file system filter driver operates in a Fail Safe or Fail Secure mode. If there is a problem with the Agent and it stops responding, the driver disconnects in Fail Safe mode and does not intercept anymore requests. A value of 1 indicates Fail Safe, 0 indicates Fail Secure. Fail Safe is the default. Changing this setting requires an Agent restart to take effect. |
| AppHookDelayLoad | Text | This setting causes the AmAppHook Dll to load after a configurable number of milliseconds (ms) delay. This setting is configured on a per filename basis. The format is <filename+extension>,<delay>. The filename and extension can contain wildcards. Each pair is semi colon delimited. For example 'calc.exe,2000;note*.exe,6000' |
| AppHookEx | Text | Application Control utilizes a Windows hook as
part of the Application Network Access Control (ANAC) feature.
In rare cases, applications can display unexpected behavior when
hooked. This setting is a list of applications in which ANAC specific
functions are not hooked and therefore not subject to the ANAC
rules.
If an application is named in both AppHookEx and UrmHookEx, the AmAppHook.dll is not loaded. Multiple entries are delimited by a semi-colon (;). |
| AppInitDllPosition | Numeric | Use this setting to specify whether the AsModLdr
driver or the Appinit registry key is used to inject the Application Control hook. This setting is also used to determine the position
of AMLdrAppinit.dll in the AppInit_DLL registry value. Set one of the following values:
This setting should only be used under the guidance of the Ivanti, Inc. Support Team. |
| AssumeActiveSetupDespiteCitrix | Numeric |
This setting controls the checks performed to detect Citrix involvement at client logon. Possible values are: 1 or 2.
Note, when Application Control detects the client is using Citrix at logon it assumes that Windows Active Setup will not be initiated (on the basis that the user logon is to Citrix; not Windows). However, under certain circumstances blocked apps have been allowed to run – that is, when with Ignore Restrictions during Active Setup is applied, the client is using published apps, and Explorer is run. Setting this key value to 1 addresses this scenario. |
| BaseConfigMergeBehavior | Text | Use to control whether the new configuration.aamp
replaces or re-merges the existing merged_configuration.aamp.
The accepted values for this setting are replace
and remerge. When you merge using GPO the Replace value is ignored and automatically defaults to Remerge. |
| BrowserAppStorePort | Numeric | Enter the port used to allow the Browser Control Chrome extension to be installed. |
| BrowserCommsPort | Numeric | Enter the port used for communications from browser extensions to the agent. |
| BrowserExtensionInstallHive | Numeric | This engineering setting allows the administrator to choose which registry hive the Application Control Chrome browser extension will be installed in. Options are:
0 is where the administrator must manually configure their own enterprise appstore to deploy the Application Control Chrome Extension. The default behaviour is 2 - for the chrome extension to be installed in HKCU. |
| BrowserHookEx | Text | The value can be set to 'Chrome.exe' to stop the Application Control browser hook (BrowserHook.dll) from being injected into it. The browser hook prevents all network communications until the Chrome Extension has established a connection with the Application Control Agent. No core functionality is affected by this custom setting. |
| BrowserInPrivatePolicyManage | Numeric |
By default, the private browsing* policy setting of supported Chromium based browsers is managed by Application Control as follows:
• If Browser Control functionality is configured then private browsing will be disabled •If Browser Control functionality is not configured, private browsing will be enabled. If you wish to control the private browsing policy externally, set the value to 0 (disabled). * InPrivateModeAvailability for Edge and IncognitoModeAvailability for Chrome. |
| BrowserNavigateEx | Text | A pipe (|) delimited list of navigation URLs that bypass the navigate event processing. The URLs in this list are not subject to URL redirection. |
| ComputerOUThrottle | Numeric | This setting limits an Active Directory look-up per connecting client for checking Organizational Unit membership by limiting the number of concurrent queries. This throttling helps reduce the amount of query-traffic on a domain if handling a large volume of connecting clients. Set this value between 0 and 65535. |
| ConfigFileProtection | Numeric | Lock configuration AAMP files and the merged config folder to prevent configurations being updated by unauthorized users. This feature is disabled by default - set to a value to 1 to enable. Care should be taken when applying this setting in test environments - you may not be able to turn it off as your configuration cannot be updated. If this occurs, contact Ivanti, Inc. Support. |
| DFSLinkMatching | Numeric | DFS Link paths can be added to the rules. DFS Links and DFS Targets are treated as separate independent items to be matched. There is no conversion from Link to Target before applying the rules. Set this value to 1 to enable DFS Link matching. |
| DirectHookNames | Text | Application Control's Windows hook is loaded into all processes that load user32.dll by default. Applications which do not load this DLL are not hooked. Any applications which do not load user32.dll should be included in this setting as part of a semi-colon delimited list of full paths or filenames. |
| DisableAppV5AppCheck | Numeric | By default, any application launched using AppV5 is exempt from Trusted Ownership checking. Use this setting to disable this behavior with a value of 1. |
| DisableCustomRulesPreCheck | Numeric | This setting improves the performance of Custom Rules checking by only processing items that are configured within the policies of each custom rule collections. By default this setting is Off and set to '0'. Set the value to '1' to allow all potential requests through the custom rules. |
| DisableDNSLookup | Numeric | The Application Network Access Control (ANAC) component is not compatible with all forms of proxy DNS servers. If set to 1, Application Control will not perform DNS lookups, reducing unexpected slowdowns and errors where a proxy DNS server is used. |
| DisableSESecondDesktop | Numeric | By default, the auditing dialog for Self-Elevation displays on the primary desktop. To display the dialog on a second desktop (and so emulate the bahavior of Windows UAC), set the value to 0. Note this custom setting is deprecated and will be removed in a future release. |
| DoNotWalkTree | Numeric | By default, process rules check the entire parent key for a match. This setting instructs process rules to only look at the direct parent of the process and not check the entire tree. A value of 1 enables this setting. |
| DriverHookEx | Text |
A semi-colon delimited list of applications that will not have the Application Control Hook (AMAppHook.Dll) injected. Application Control requires the hook to be loaded for certain functionality to work. This custom setting should only be used under the guidance of Ivanti technical support.
Note: Privilege Management, Application Network Access Control, Application Access Control - Script Host Processing and Policy Change Request will not function for any applications that are in the list, or whose parent process is in the list. |
| EnableCustomRulesDllChecking | Numeric |
By default this setting if off (set to 0) meaning only executables and URLs are processed. This setting improves the performance of Custom Rules checking by controlling whether DLLs are allowed through the rule collections. Set the value to 1 to allow all DLLs to be processed in addition to the default.
Note, enabling this setting can have an impact on performance. Consider using Process Rules as an alternative solution. |
| EnableScriptPreCheck | Numeric | Whilst scripts within scripted rules are
processing, they are treated as though they have returned a false
value. The length of time scripts take, varies according to
their content. This setting provides the best performance during computer
start-up and user logon because anything depending on the result
of a script is not delayed. Set the value to 1 to make processes wait until the relevant script
has finished.
This can significantly slow down computer start-up and user login. Application Control does not wait indefinitely for scripts results - a 30 second timeout is applied. |
| EnableSignatureOptimization | Numeric | This setting improves the performance of rules
checking, when using signatures. Files that do not match the full
path are not hashed as it is assumed they are not the same file.
Set to 1 to enable. Enabling this setting and ExtendedAuditInfo will not show any hashed file name in auditing metadata. |
| ExplicitShellProgram | Text | This setting is used by Application Access Control (AAC). Application Control treats the launch of the shell program (by default explorer.exe) as the trigger for that session to be considered logged on. Different environments and technologies can change the shell application and the agent on occasion can't detect what the shell program is. Application Control uses the applications in this list (in addition to the default shell applications) to determine when a session is deemed to have logged on. This is a semi-colon delimited list of full paths or filenames. |
| ExProcessNames | Text | A list of semicolon (or space) separated filenames that should
be excluded from the filter driver.
Changing this setting requires an Agent restart to take effect. |
| ExtendedAuditInfo | Numeric | This setting extends the file information for
audited events. It reports the Secure Hash Algorithm 1 (SHA-1)
hash, file size, file and product version, file description, vendor,
company name, and product name for each file in its audited events.
The information is added immediately after the file name in the
event log. This setting is on by default. To turn it off, enter
a value of 0.
The generation of a hash or checksum is disabled when the EnableSignatureOptimization setting is enabled. |
| ForestRootDNQuery | Numeric | Set the value to 1 to enable the Application Control Agent to perform a forest root query. The query includes chasing referrals to determine the Distinguished Name of connecting devices for the purposes of OU and Computer Group membership in Device Rules. |
| ImageHijackDetectionInclude | Text | A list of process names against which all child processes are verified to ensure the child image is running without corruption or modification and is a match for the one that was initially requested. This is a semi-colon delimited list of full paths or file names.
Note that if the child process is not verified, it is terminated and an event (ID 8005) audited in the local application event log. |
| MultipleHostsSameIP | Numeric | Allows Application Network Access Control (ANAC) to work with multiple hosts with the same IP Address. It takes out the caching of domain names to IP Addresses and allows different domains to work when running from the same server. Set to a value of 1 to enable. |
| NetEnableRevDNS | Numeric | Used by Application Network Access Control (ANAC), this setting globally enables a reverse DNS lookup check on each request to access a network resource. Enabling this setting overrides the NetEnabledRevDNSList and RevDNSList settings. Set to a value of 1 to enable. This feature requires the administrator to enable and configure Reverse Lookup Zones on the company's DNS servers. |
| NetEnableRevDNSList | Numeric | Used by Application Network Access Control (ANAC), this setting enables a reverse DNS lookup check for only the IP addresses listed
in the RevDNSList. This setting must be used in conjunction
with the RevDNSList setting - set to a value of 1 to enable. This feature requires the administrator to enable and configure Reverse Lookup Zones on the company's DNS servers. |
| OwnershipChange | Numeric | Application Control detects if a trusted file is changed by a non-trusted owner. In such a case, the file owner is changed to the untrusted user and any execute requests are blocked. Some applications overwrite files in such a way that Application Control does not detect it by default, therefore the owner of the file is not changed. When enabled, Application Control performs additional checks to catch all file changes and overwrites should be caught. Set to a value of 1 to enable. |
| PCRRetainOnNewConfig | Numeric |
Control how Policy Change Requests (PCR) are dealt with when a new configuration is issued. This feature is disabled by default - authorized PCRs are removed upon receipt of a new configuration.
Set a value of 1 to retain authorized Policy Change Requests when a new configuration is issued. |
| RdmHookEx | Text | A list of applications, used in Privilege Discovery Mode (PDM), in which PDM specific functions are not hooked by Application Control's Windows hook. The values should be a semi-colon delimited list of filenames. |
| RemoveDFSCheckOne | Numeric | When files are stored on a DFS drive, the Application Control agent uses a number of strategies to evaluate the correct UNC path. One of these strategies can cause delays during login if large numbers of scripts and executables are stored in and replicated by, Active Directory. Set to a value of one to enable, causing Application Control to ignore this strategy and increase performance in this situation. |
| RevDNSList | Varies | This setting is only applicable when used in conjunction with
NetEnableRevDNSList and is used by Application Network Access Control (ANAC).
It contains IP addresses that will have a reverse DNS lookup check. The IP addresses should be in IPv4 dotted decimal format (n.n.n.n) and in a semi-colon delimited list.
This setting requires the administrator to enable and configure Reverse Lookup Zones on the company's DNS servers. |
| SECancelButtonText | Text | The text displayed by the cancel button on the Self-Elevation dialog. |
| SelfElevatePropertiesEnabled | Numeric | Set this value to '1' to enable self-elevation of properties. This feature is disabled by default. |
| SelfElevatePropertiesMenuText | Text | The text in the context menu option for self-elevation of properties. |
| SEOkButtonText | Text | The text displayed by the OK button on the Self-Elevation dialog. |
| TVChecking | Numeric | Enabling this setting causes Application Control to ignore Trusted Vendor checking for all files, even if the configuration contains entries for Trusted Vendors. Set to a value of 0 to enable this setting. This setting is Intended for troubleshooting issues. |
| UrlRedirectionSecPolicy | Numeric | By default, the security policy is ignored by the URL Redirection feature. This engineering setting allows the administrator to force URL Redirection to follow the configured security policy. Set to a value of 1 to enable. Self Authorization is not supported. |
| UrmForceMediumIntegrityLevel | Text |
A User Privilege Management (UPM) custom setting used to override the integrity level when user privileges are elevated applications, which by default sets the integrity level to high. When this setting is used, the level is reduced to medium. This value should be a semi-colon delimited list of file names. This custom setting applies configuration-wide. To assign on a per-token basis, refer to User Privileges. |
| UrmHookEx | Text | Application Control utilizes a Windows hook as part of the User Privilege Management feature. In rare cases, applications display unexpected behavior when hooked. This setting lists the applications where User Privilege Management specific functions are not hooked. If an application is named in both AppHookEx and UrmHookEx, the AmAppHook.dll is not loaded. Multiple entries are delimited by a semi-colon. Note: Privilege Management, Application Access Control – Script Host Processing and Policy Change requests will not function for any applications that are in the list, or whose parent process is in the list. |
| UrmPauseConsoleExit | Text | Used by the User Privilege Management feature. When a console application is elevated, a new application can appear in a new console window. The application runs to completion then closes. This is a problem if the user wants to see the output of the program. This setting causes the application to remain until a key is pressed. This is a semi-colon delimited list of full paths or filenames. |
| UrmSecPolicy | Numeric | By default, the security policy is mostly ignored by the User Privilege Management feature. User Privilege Management rules are applied in all cases except for when Audit Only mode is selected. This custom setting allows administrators to force User Privilege Management to follow the configured security policy. For Unrestricted and Self-Authorize security levels, User Privilege Management rules are not applied. For the Restricted level, User Privilege Management rules are applied. Set to a value of 1 to enable this setting. |
Additional Engineering Key - GroupSidRefresh
Application Control requires the Security Identifier (SID) of all Group Rules to successfully perform rule matching. With this engineering key set, the agent will resolve the SID of the Group Rule at runtime whilst the endpoint is online and write it back into the Configuration (AAMP file). This can be useful if the endpoint is subsequently used offline as the SID stored in the configuration will be used.
The Application Control Console will resolve the SID if possible when the configuration is saved. This setting is only needed if the console could not perform the group SID lookup.
Settings
HKLM\Software\Appsense Technologies\Application Control\Engineering
Name
GroupSidRefresh
Type
String (REG_SZ)
Parameters
0 - Off
1 - only resolve groups that currently have no SID values
2 - resolve all group SIDs –useful if the domain is specified by an environment variable so t is subject to change.
Self-Elevation File Associations
For further information, see Self-Elevation File Associations.