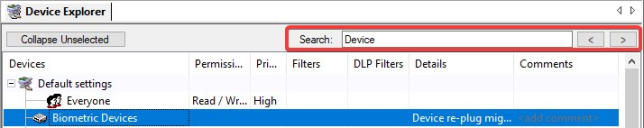
Device Explorer Window
An administrator uses the Device Explorer hierarchy to create and manage device and computer user groups, as well as assign permission rules for online, offline, temporary and scheduled device use. The Device Explorer module is also used to create and manage file shadowing rules.
A search bar at the top of the Device Explorer module enables you to search through all the fields visible in the Device Explorer and automatically moves the focus to the string found. You can also use the keyboard to move to the next search result (F3) or move to the previous result (Shift + F3).
The main window of the Device Explorer module displays a hierarchical structure of device classes, which is divided into two primary levels:
- Default settings which contain the user access permission rules that apply to every computer.
- Machine-specific settings which contain unique user access permission rules that apply to a specific computer or group of computers.
The Device Explorer window is further divided into the following columns:
|
Column |
Description |
|---|---|
|
Devices |
Lists device classes and users or user groups with permission to access devices. |
|
Permissions |
Shows a description of the type of permission provided to users and user groups listed in the Devices column. |
|
Priority |
Shows a priority of High or Low assigned to rules listed in the Permissions column. |
|
Filters |
Shows a description of the file type filtering rules assigned to rules listed in the Permissions column. |
|
DLP Filters |
Shows the Data Loss Prevention filters assigned. |
|
Details |
Shows a description of permissions rules details. |
|
Comments |
Ivanti Device and Application Control administrators can select permission rules and enter comments by clicking the Comments column heading. |