Microsoft Intune Integration
You can use Microsoft Intune integration to automate publishing of the DSM client MSI and NCP files into Intune. This feature enables new endpoints to register automatically into DSM when end users start using their endpoint devices for the first time. Without this feature, for a new endpoint to be registered in DSM, it must be connected to the company network for DSM to push the DSM client package and/or be auto-inserted in DSM.
This feature leverages the Autopilot, Intune, and Azure AD infrastructure from Microsoft.
Besides automating the publishing process, the integration also enables you to:
•Identify the endpoints registered with Intune within the DSMC (AutoInsert rules).
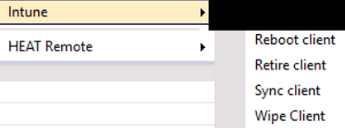
•Execute Intune actions on clients from within the DSMC (reboot, retire, sync, wipe).
Prerequisites
•Install Microsoft .NET Framework 4.8 on the BLS server and other endpoints where integration is to occur.
•Activate TLS 1.2 on both the BLS server and HTTP depot. See this article for details: TLS 1.2 enforcement for Azure AD Connect.
•Configure a hybrid Azure AD join for managed domains. See this article for details: Configure hybrid Azure AD join. Note that Azure AD needs to be synced with the local domain that DSM is using.
•Have a Microsoft 365 subscription for Microsoft Endpoint Manager, with this configuration:
•Activate MDM: Go to the Azure portal (portal.azure.com) and select Azure Active Directory. Select Microsoft Intune, then select All to enable the MDM user scope and All to enable the MAM user scope.
•Activate enrollment: Go to the Azure portal (portal.azure.com) and select Azure Active Directory. Select Mobility (MDM and MAM) > Microsoft Intune Enrollment, then select All to enable the MDM user scope.
•Create an Azure "DSM Intune" application (a tenant) manually. See this article for details: Use the portal to create an Azure AD application and service principal that can access resources.
•Assign application permissions in Intune for the Microsoft Graph API. The list of required permissions is:
•Group – Read, Write
•Directory – Read, Write
•DeviceManagementApps – Read, Write
•DeviceManagementConfiguration – Read, Write
•DeviceManagementServiceConfig – Read, Write
•DeviceManagementManagedDevices – Read, Write, PrivilegedOperations
•Applications – Read, Write
•Device – Read, Write
•User – Read, Write
Configuring DSM
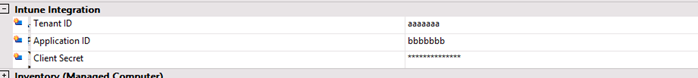
DSM has three text fields in Infrastructure (advanced mode) used to connect to your Azure environment. The fields to store in DSM are found at the Azure portal (portal.azure.com), under App registrations. Select the created apps:
•Tenant ID – “Directory (tenant) ID”
•Application ID – “Application (client) ID”
•Client Secret (stored encrypted in DSM) – found in “Certificates & secrets”
The DSM Infrastructure tab with the Intune Integration section looks like this:
To enable the Intune action items, you also need to install the corresponding Management Point role:
Using the feature in DSM
Intune integration occurs via the DSM Settings > Upload DSM Client To Intune menu.
This single-click menu automates several steps:
•Packages the DSM client MSI and NCP files into .intune file format, as required by Intune.
•The menu calls a tool from Microsoft to perform this action (C:\DSM\DSMIntuneConnector.exe, included in the ISO). Before using, you must agree with the license located here: Microsoft License Terms For Win32 Content Prep Tool. This tool produces a log located at C:\Program Files (x86)\Common Files\enteo\NiLogs\BLS\bls_DSMIntune.log.
•Uploads the package to Azure storage.
•Assigns the new application to all endpoints.
You need to use this menu each time a new DSM version is installed, or relevant settings are changed in the ICDB (DSM Configuration). This is required so that new endpoints will pick up the latest version of the DSM client and NCP file; otherwise, changes in the newer versions may prevent older clients from connecting to the updated BLS server.
Each new menu action updates the existing DSM client package from Intune (the package will be overwritten).
The client application in https://endpoint.microsoft.com/ is called Ivanti DSM Client and includes the version number.
The DSM client package is pushed to endpoint devices and installed after the end user logs in.