Rapid7 AppSpider Connector Guide
Summary: How to set up and use the Rapid7 AppSpider connector in Ivanti Neurons.
Overview
The RiskSense platform provides an API-based connector that integrates with Rapid7’s AppSpider Enterprise that enables customers to bring their AppSpider findings into RiskSense to gain visibility of their overall risk due to vulnerabilities in their applications, thereby enabling a more simplified and efficient way to manage those vulnerabilities.
RiskSense users can configure the connector to pull scan data from AppSpider on a periodic basis. Data from AppSpider is ingested as Applications/Application Findings.
AppSpider Enterprise Overview
AppSpider Enterprise is a single console that includes multiple AppSpider Pro scan engines. It is an on-premises installation that manages scan configurations and schedules from a centralized location. It includes unique capabilities and integrations that enable teams to automate more of the security testing program across the entire software development lifecycle (SDLC), from creation through production.
AppSpider Enterprise Connector Setup Prerequisites
-
Connector setup in Ivanti Neurons requires the on-premises installation of AppSpider Enterprise.
-
Perform scans for the desired applications.
-
The AppSpider Enterprise connector pulls these files based on the schedule defined during configuration and processes the data, categorizing them into Applications and Application Findings.
-
Since AppSpider Enterprise is an on-premises installation, an OVA setup is required to connect with the Ivanti Neurons platform. Refer to this knowledge base article for more details.
User Access and Permissions
To set up the connector, the user account must have API access to AppSpider Enterprise. The credentials used for creating a connector can be either a multi-client or normal user; RiskSense handles both scenarios.
In a multi-client user’s case, the RiskSense connector will pull all scan files associated with multiple clients and process them, as well.
AppSpider Enterprise Role Permissions
The user account associated with the connector must have the following Roles enabled for the connector to pull scan reports from AppSpider Enterprise:
-
Report viewer
-
Scan runner
-
Issues viewer
-
Issues manager
Fetching the API Token Expiry from AppSpider Enterprise
When configuring the connector in Ivanti Neurons, you will need the API token expiry from AppSpider Enterprise. The API token expiry can be retrieved from the IIS Manager configuration file where AppSpider Enterprise is installed. This is custom to each user, and it can be retrieved by following these steps:
-
In the AppSpider Enterprise machine (where it is installed):
-
Go to the following File Path: C:\Program Files (x86)\Rapid 7\AppSpider Enterprise 3.8\NET\Web.config
-
Open the file in a text editor and locate the following line of code:
-
<authentication mode="Forms"><forms name="NTOE32_FORMAUTH" enableCrossAppRedirects="false"
loginUrl="/Account/Login" timeout="15" cookieless="AutoDetect" protection="All" defaultUrl="/" />
</authentication>
By default, the timeout is set to 15 minutes. You can change it as needed. For example, change it to 120 for a 2-hour timeout. Save the file and restart IIS for the change to take effect.
Creating the AppSpider Enterprise Connector
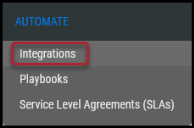
Navigate to the Automate > Integrations page.
Using the search bar in the upper-right corner of the Integrations page, type AppSpider Enterprise to find the connector.
Locate the AppSpider Enterprise card on the page and click Configuration.
Complete the following fields. These fields include:
-
Name: Connector name.
-
URL: Add theAppSpider Enterprise on-premises Instance URL with the port and context path, e.g., https://<InstanceName:Port>/<ContextPath>. Refer to the screenshot below for another example.
-
User Name and Password: AppSpider Enterprise user name and password with the roles provided from the previous section.
-
Network: Network name in Ivanti Neurons. Ingested data will be associated with this network.
-
SSL: For self-signed domains, add the SSL certificate.
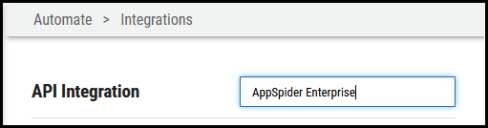
Once the fields are complete, click Test Credentials to verify the credentials are correct and can connect to the AppSpider Enterprise instance.
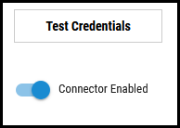
Configure the desired schedule for the connector to retrieve results from the AppSpider Enterprise instance and optionally turn on Enable auto URBA (Update Remediation by Assessment). Under Connector Specific Options, complete the mandatory field with the user’s API token expiry. Refer to the Fetching the API Token Expiry from AppSpider Enterprise section of this guide for how to obtain the API token expiry.
Once connector configuration is complete, click Save to create the connector.
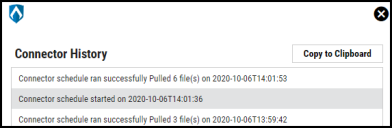
After creating the connector, it starts pulling data from AppSpider Enterprise. After configuring the connector, a new entry for it appears at the top of the Integrations page. The connector’s card shows the next scheduled time and date it will fetch results. Check the connector’s status by clicking the History button.
To run the connector on demand, click the Sync icon.
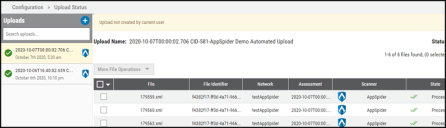
Files pulled from AppSpider Enterprise are viewable on the Uploads page.
Data Visualization in the Ivanti Neurons Platform
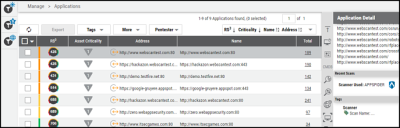
Scan data pulled from AppSpider Enterprise via the connector is available on the Manage > Applications and Manage > Application Findings pages.
Assets discovered from the scan data are added to the Manage > Applications page.
The Manage > Application Findings page displays all identified vulnerability details, as shown below.