Rule Set Executable Control
The Rule Set Executable Controls allow you to specify Allowed and Denied Items, and the Security Level for the Rule Set.
Any Allowed or Denied Items added to the rule set will display in the work area, with the item type, for example File, Folder, Drive, the name of that item and any Options or descriptions that have been applied to it.
Right-click an item to see the context menu. You can edit the file from here and also toggle the state between Disable/Enable.
Security Levels
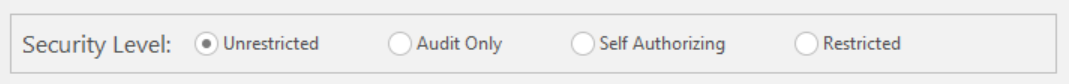
Application Control configuration rule security levels specify how to manage requests to run unauthorized applications by the users, groups, or devices that a rule matches:
- Unrestricted - All actions are permitted without event logging or auditing settings for specifying the levels of restrictions to execute files.
- Audit only - All actions are permitted but events are logged and audited, for monitoring purposes.
- Self Authorizing - Users are prompted for decisions about blocking or running unauthorized files on the host device. Unauthorized files either do not belong to the Trusted Owners list or are not specified in the Allowed Items list of a given rule.
A self-authorizing user prompt includes the following options:
- Allow - Allows the application to run.
- Block - Blocks the application from running.
When a DLL file is allowed to run, a message notifies the user that the application which uses the DLL may need to be restarted.
Users can also decide how long the setting is applied for:
- Remember my decision for this session only - The authorization decision is upheld only for the current session. The user is prompted again for an authorization decision when attempting to run an application in any future sessions.
- Remember my decisions permanently - The user decision is upheld for all future sessions.
If neither of these options are selected, the decision is upheld only for the current instance the user is attempting to run. The self-authorization prompt is reissued for any future attempts to run instances of the application.
- Restricted - Only authorized applications can run. These include files owned by members of the Trusted Owners list and files listed in Allowed Items.
You can test whether security levels are being implemented correctly. The following example shows you how to test the self authorizing level.
- Create a User rule that applies to a test user account that is not a member of a group that belongs to the Trusted Owners list.
- Set the Security Level to Self Authorizing to allow the test user to self-authorize applications to run.
- Save the configuration.
- Run the Registry Editor. The application should be prohibited and a message box displays with a prompt for a decision to allow the file to run, informing that the action will be logged.
Related Topics
Configuration Settings Executable Control