Creating an AC Configuration
You configure the Application Control functionality within the Application Controll Configuration Editor. The configuration needs to be assigned to an agent policy so it can be deployed to an agent on a managed endpoint.
Use the Configuration Editor to define the configuration settings, rule collections, and rule sets. The Editor can be launched directly from the menu options and also from within the Agent Policy Editor.
Rule Matching
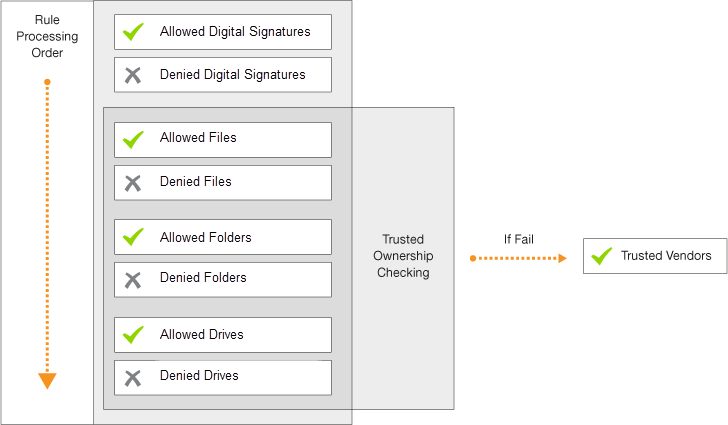
Rule matching takes place when Application Control intercepts a file execution request and checks the configuration policy to determine whether a file is allowed to run.
The Application Control agent applies rules by making a suitable match for the file type.
Matching is based on a three stage approach that considers security, matching order, and policy decisions:
Security:
- Is the user restricted?
- Is ownership of the executable item trusted?
- Where is the executable located?
Matching:
- Does the executable match a signature?
- Does the executable match an allowed or denied Item?
Policy:
- Is Trusted Ownership checking enabled?
- Is there a timed exception?
- Is there an application limit?
Example: File confidential.doc is held within folder 'common'. A rule specifies that file confidential.doc is denied but folder 'common' is allowed. The more granular rule takes precedence and the file confidential.doc will be denied.