Security Levels
Overview
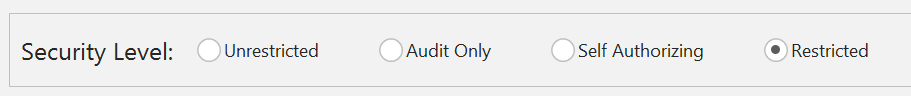
Application Control rules allow you to set security levels to specify how to manage requests to run unauthorized applications by the users, groups, or devices that a rule matches.
Apply security levels to control whether the user, group, and devices specified in a rule are fully restricted by rules, unrestricted, audited only, or granted self-authorization status entitling the user to decide whether to run an application.
All actions are permitted without event logging or auditing settings for specifying the levels of restrictions to execute files. By default, the ‘BUILTIN\Administrators’ group is set at this level.
Select to permit all actions but log and audit events for monitoring purposes.
Select to prompt users, groups, and devices in the rule to decide whether to allow execute requests for each unauthorized file. Unauthorized files either do not belong to the Trusted Owners list or are not specified in the Allowed Items list of a given rule.
In some environments it's necessary for users to add new executables to a computer, for example, developers who constantly update or test internal software, or power users who require access to new or unknown applications. Self-Authorization allows nominated power users to execute applications they have introduced into the system. These power users can add applications to a secured endpoint while outside the office without relying on IT support. This provides development teams, power users and administrators the flexibility to install and test software while still offering a high level of protection against hidden malware and executables.
Any user configured as self-authorizing will have the option of allowing an untrusted executable to run, either once, every time during the current session, or always. Comprehensive auditing details information such as application name, time and date of execution, and device. What's more, a copy of the application can be taken and stored centrally for examination.
The restrictive security level sets Application Control into its most secure mode. Users, Groups and Devices defined in rules will only be allowed to run authorized applications. These include files owned by members of the Trusted Owners list and files listed in the Allowed Items node.
Try it yourself
You can test whether Security Levels are being implemented correctly. The following example shows you how to test the Self-Authorizing level.
- Create a rule in the User rules node that applies to a test user account that is not a member of a group that belongs to the Trusted Owners list.
- Set the security control level to Self-Authorizing to allow the test user to self-authorize applications to run.
- Save and deploy the configuration.
Test it
- Login as the test user.
- Attempt to run the Registry Editor.
- You should see the application is prohibited and a message display with a prompt for a decision to allow the file to run, informing that the action will be logged.