Ivanti® Endpoint Manager 2024 server certificate configuration
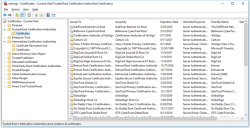
This topic contains information about configuring Trusted Root Certification Authorities.
The problem
For Microsoft Internet Information Services (IIS) to properly handle client certificate-based authentication, it's important that the certificates in the Trusted Root Certification Authorities container be properly configured. The certificates contained in this container should all be self-signed certificates. If non-self-signed certificates are installed on this container, it can cause certificate-based authentication for IIS to fail with HTTP error 403. For a description of the HTTP 403.16 and 403.7 errors, see this website:
Resolution
Part 1: Remove non-self-signed certificates from Trusted Root Certification Authorities
This issue can be addressed by removing all non-self-signed certificates from the Trusted Root Certification Authorities in Certificate Manager (certmgr.msc) and moving them to the appropriate location instead, such as Intermediate Certification Authorities. Make these changes with caution, because other software may be affected; you'll need to run software tests to ensure everything still works properly.
Part 2: Change the SCHANNEL Settings in the Windows Registry
On some systems, it may be necessary to change the following registry keys that affect how certificates are trusted:
- Set HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL, Value name: ClientAuthTrustMode, Value type: REG_DWORD, Value data: 2
- Set HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL Value name: SendTrustedIssuerList Value type: REG_DWORD Value data: 0 (False, or delete this key entirely)
For information about the SCHANNEL registry key and its uses, see these websites:
- http://stackoverflow.com/questions/27232340/iis-8-5-mutual-certificates-authentication-fails-with-error-403-16
- http://blogs.technet.com/b/configurationmgr/archive/2013/08/13/support-tip-a-configmgr-2012-management-point-enabled-for-ssl-fails-with-403-forbidden.aspx
- http://configmgrblog.com/2014/02/23/configmgr-2012-r2-internet-facing-mp-windows-server-2012-r2-note/