Search for vulnerabilities by CVE name
Patch and Compliance supports the Common Vulnerabilities and Exposures (CVE) naming standard. You can search for a downloaded vulnerability by its CVE name. You can also view the CVE names associated with an individual vulnerability.
What is CVE?
Common Vulnerabilities and Exposures (CVE) is a collaborative initiative by several leading security technology organizations. They maintain a list of standardized names for vulnerabilities and other information security exposures. The CVE naming standard makes it easier to search for, access, and share data across vulnerability databases and security tools.
Ivanti compatibility with the CVE naming standard
Ivanti products—including Endpoint Manager, Endpoint Security for Endpoint Manager, and Patch Manager—fully support the CVE standard.
When you download vulnerability definition updates, they include CVE names. Additionally, the vulnerability definition includes a hyperlink to the CVE dictionary web site where you can find the most recent CVE version information.
Search for vulnerabilities by their CVE name
Patch and Compliance lets you search for vulnerabilities by their CVE names or view the CVE details for a specific vulnerability.
To find security vulnerability definitions by using CVE names
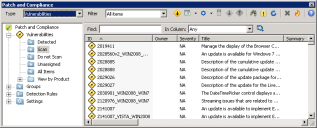
1.In the Patch and Compliance tool window, select Vulnerabilities from the Type drop-down list. A complete list of downloaded vulnerability definitions displays.
2.Enter the CVE name (CVE ID) in the Find field, select Any or CVE ID from the In Column list, and then click the Search button. (You can enter the entire CVE ID, including the cve- prefix, or as much of the ID as you know, and search your downloaded security repository for matching vulnerabilities.)
3.If a vulnerability with a matching CVE ID is found in the repository of vulnerabilities you've downloaded, it displays in the list.
4.Right-click the vulnerability to access its shortcut menu for available options.
To find CVE names for downloaded security vulnerability definitions
1.In Patch and Compliance, select Vulnerabilities or All Types from the Type list. A list of downloaded definitions displays. (If the column for CVE ID data has been selected, you can view CVE IDs in the item list. To configure columns, right-click a column title bar, select Columns, and make sure the CVE ID column is in the Selected Columns list.)
2.Double-click a vulnerability definition (or right-click the definition and select Properties) to open its Properties dialog box.
3.Click the Description page.
4.If the selected vulnerability has a CVE name, it displays in the CVE ID list. Some vulnerabilities might have more than one CVE name, which you can access by scrolling through the list.
5.To access the Web page for a specific CVE ID, click the More information for CVE ID link. The CVE Web site provides detailed information about each vulnerability with a CVE name, including its current status with the CVE board (approved Entry, or Candidate under review).