OAuth for Ivanti Standalone Sentry on Ivanti Neurons for MDM
OAuth is supported with Ivanti Standalone Sentry for Office 365. The following scenarios must be compliant for OAuth to function correctly:
-
The email client must support OAuth (iOS Native Mail, iOS Email+ and Android Email+)
-
UEM must push an OAuth configuration to the email client
-
UEM must enable Sentry for OAuth
Sentry 9.14 supports Azure AD Conditional Access Policy.
For more information, see Configuring conditional access rules in Azure.
Configuring Sentry on Ivanti Neurons for MDM for OAuth
You must configure Sentry to enable OAuth and provide the endpoints.
Before you begin
-
Verify that you have Sentry 9.12.0 or later and Ivanti Neurons for MDM 75 or later.
Procedure
| 1. | Login to Ivanti Neurons for MDM with admin credentials. |
| 2. | Click Admin > Sentry > Add Sentry Profile.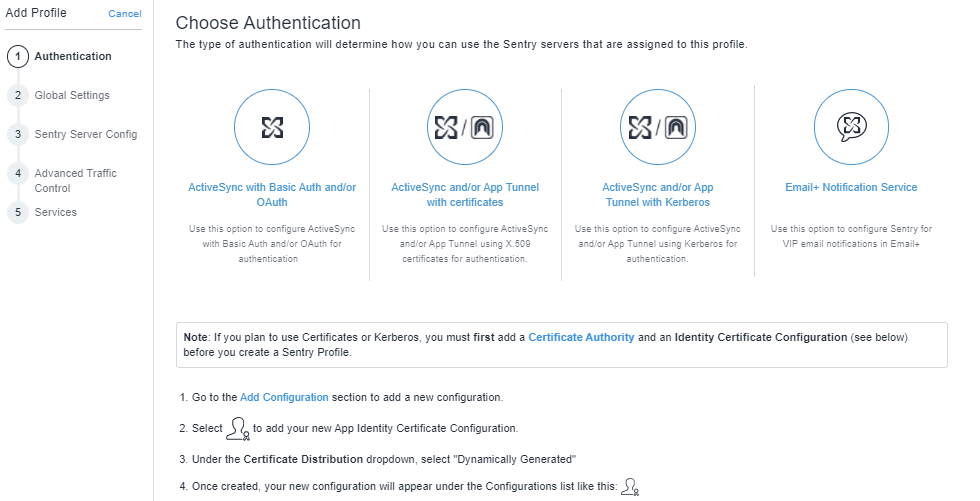 |
| 3. | Select ActiveSync with Basic Auth and/or OAuth and click Next. |
| 4. | Enter the Name, Hostname, and Port details and click Next. |
| 5. | Enter the Sentry Server Configuration details and click Next. |
| 6. | Click Exchange ActiveSync and enter the following details: |
-
Destination OAuth2 Authorization Endpoint: https://login.windows.net/common/oauth2/authorize
-
Destination OAuth2 Token Endpoint: https://login.windows.net/common/oauth2/token
-
Sentry Resource: https://<SentryHostname>
-
Destination Resource: https://outlook.office365.com
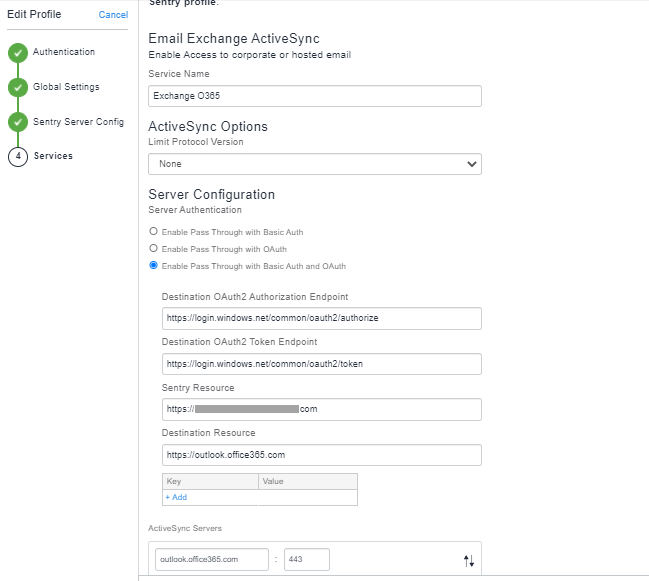
| 7. | Click Next > Save. |
Configuring iOS native email configuration with OAuth
You must enter the Sentry OAuth Sign In URL.
Before you begin
Verify that you have added the Sentry profile with OAuth settings.
With iOS 14 and newer versions, password prompts appear on the devices for iOS Native email client when the exchange profile with OAuth configuration is pushed to the devices.
Procedure
-
Login to Ivanti Neurons for MDM with admin credentials.
-
Click Configurations> Add> Exchange.
-
Enter the name and description.
-
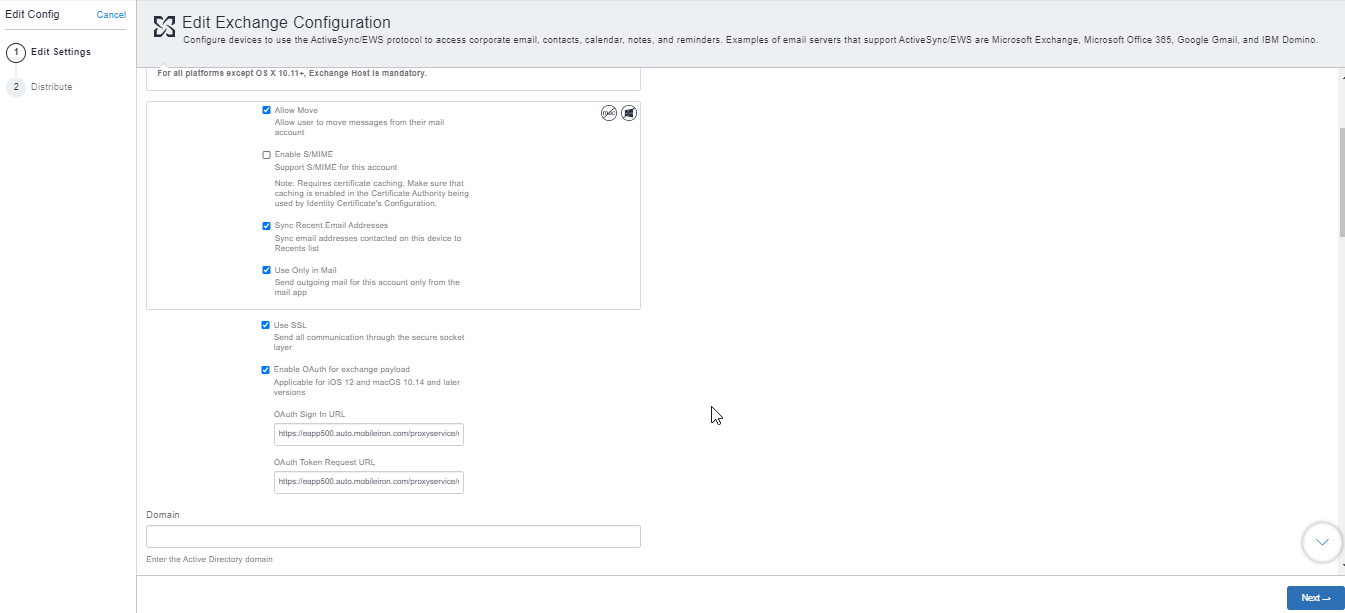
In Configuration Setup, select Enable OAuth for exchange payload.
-
Enter the following details:
-
OAuth Sign In URL: https://<Sentry HostName>/proxyservice/oauth2/authorize
-
OAuth Token Request URL: https://<Sentry HostName>/proxyservice/oauth2/token
-
-
To modify the Exchange settings:
-
Enter the VPN profile's Safari domains for Tunnel requests to go through the domains used in OAuth and multi-factor Authentication:
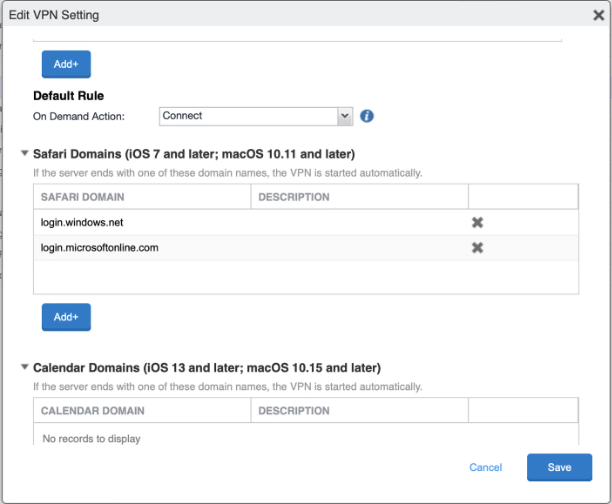
-
Click Save.
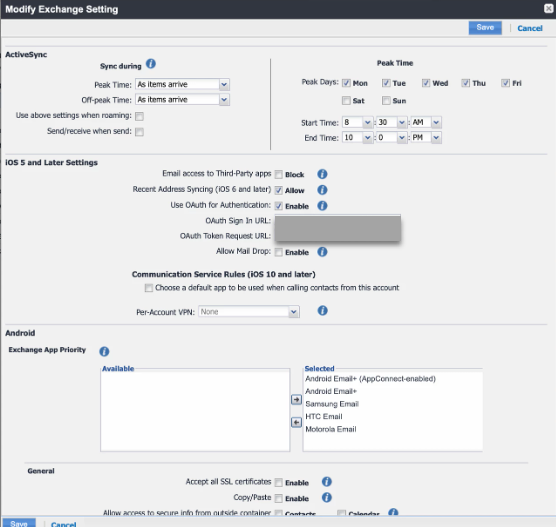
Configuring Android and iOS Email+ configuration with OAuth
-
Login to Ivanti Neurons for MDM with admin credentials.
-
Click Apps> App Catalog> Add.
-
Select Email+ 3.8.0. (Android AppConnect) for Android configuration.
-
Enter the details and click Next to add the application.
Figure 1. android email+ configuration
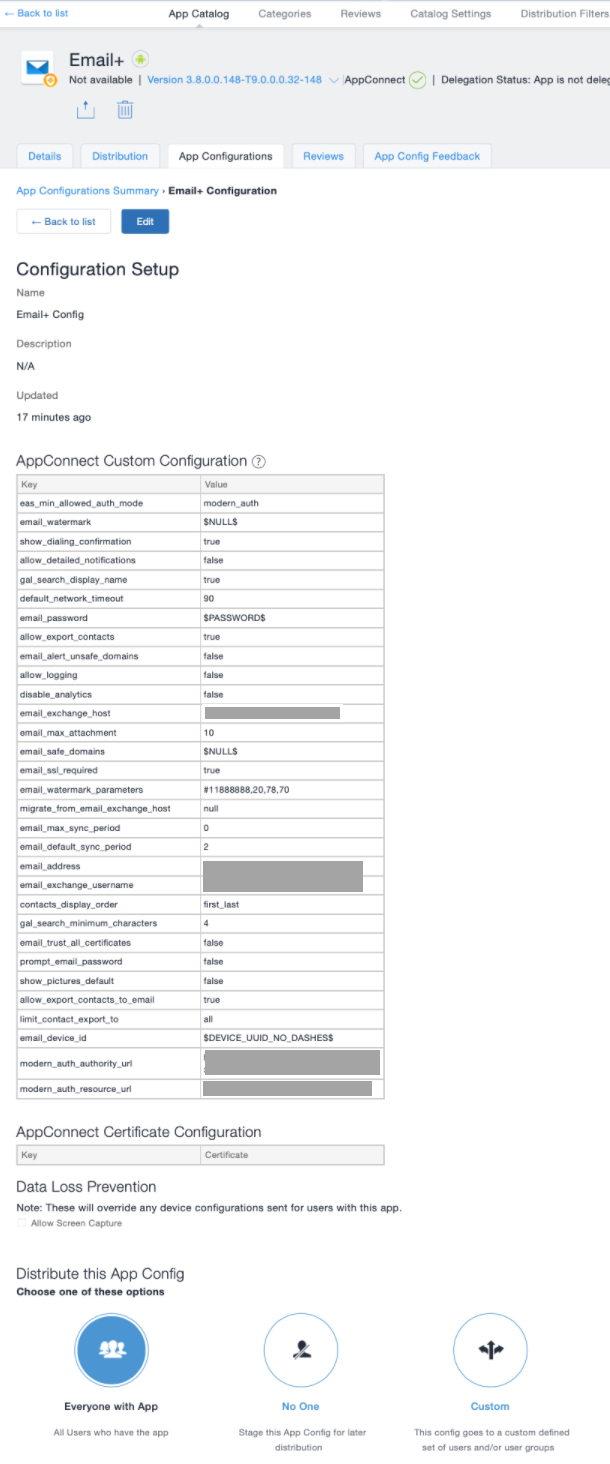
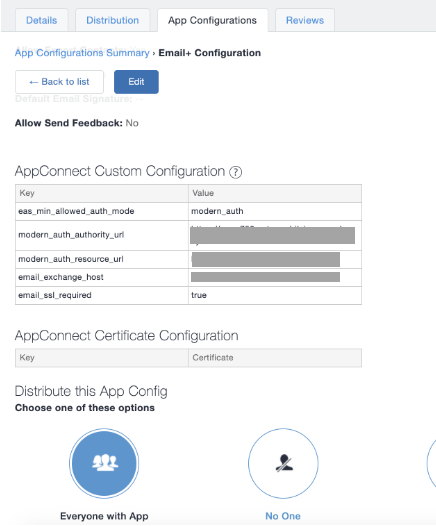
Figure 2. ios email+ configuration
-
Email+ iOS also has AppTunnel definitions that send traffic to specific domains through Ivanti Tunnel.

For more information on adding an application on Ivanti Neurons for MDM, see "Adding an In-house app" in the Ivanti Neurons for MDM Administrator Guide.
KVPs for Email+ configuration
-
eas_min_allowed_auth_mode: modern_auth
-
modern_auth_authority_url: https://<SentryHostname>/proxyservice
-
modern_auth_resource_url: https://<SentryHostname>
-
email_exchange_host =<sentry_address>
Configuring conditional access policy in Azure AD
You can configure the conditional access rules in Azure for OAuth to function correctly.
-
Login to Azure portal with admin credentials.
The admin has to be super admin who has premium features to configure Conditional Access rules. -
Click Azure AD Conditional Access > Named Locations > IP Range Locations > New IP Range Location.
-
Click Add and enter the IPv4 or IPv6 address range.
-
Configure a name and Sentry IP address with Subnet > Add > and enable Mark as Trusted location > Create.
-
On the Home tab, click Conditional Access Policies > Create New Policy.
-
Under Users and Groups, select Users and Groups.
-
Search for the appropriate Users or Groups and click Select.
-
Under Cloud apps or actions, select apps > Office 365.
-
Under Conditions > Locations > Any Location > Configure "Yes" under Include to "Any Location".
-
Under list of locations, select Selected locations under Exclude.
-
Select Grant access as block access > require one of the selected controls.
-
Select Enable Policy > On> Create.