Ivanti Standalone Sentry deployment scenarios
In a deployment, Ivanti Standalone Sentry works with the UEM platform secures access to backend resources by preventing wrongful access from devices. The UEM can be Ivanti EPMM on a Physical or Virtual Appliance or it can be an Ivanti Neurons for MDM deployment. This section provides various deployment scenarios with Ivanti Standalone Sentry.
These deployments include:
•Deployment with Ivanti Standalone Sentry in the DMZ
•Deployment with multiple Ivanti Standalone Sentry servers
•Deployment with Ivanti Standalone Sentry behind a proxy
•Deployment with multiple ActiveSync servers or backend resources
Deployment with Ivanti Standalone Sentry in the DMZ
Ivanti Standalone Sentry can be located in the DMZ, along with UEM, but this configuration is not required. You can alternatively:
•Put Ivanti Standalone Sentry in the DMZ and put UEM behind the corporate firewall.
•Put UEM in the DMZ and put Ivanti Standalone Sentry behind the corporate firewall.
•Put both Ivanti Standalone Sentry and UEM behind the corporate firewall.
Deployment with multiple Ivanti Standalone Sentry servers
Use multiple Ivanti Standalone Sentrys in the following situations:
•Ivanti Standalone Sentry and Integrated Sentry for High Availability
Multiple Standalone Sentrys and Integrated Sentrys can back each other up to provide High Availability access to ActiveSync Servers or backend resources. In this configuration, each Sentry points to the same server or server cluster. Contact Professional Services to set up this configuration.
•Your ActiveSync server has more users than one Ivanti Standalone Sentry can support.
An Ivanti Standalone Sentry has an upper limit for the number of registered ActiveSync devices that it can support, depending on its configuration. If your ActiveSync server supports more devices than this limit, use multiple Standalone Sentrys. Configure each Standalone Sentry to point to the same ActiveSync server (or servers if multiple ActiveSync servers back each other up).
For more information about Standalone Sentry capacity, see the Standalone Sentry On-Premise Installation Guide.
•You have multiple ActiveSync or backend resources, each of which supports a different organization.
Use one Ivanti Standalone Sentry for each organization. Configure the Ivanti Standalone Sentry to point to the server (or servers if multiple servers back each other up) for that organization.
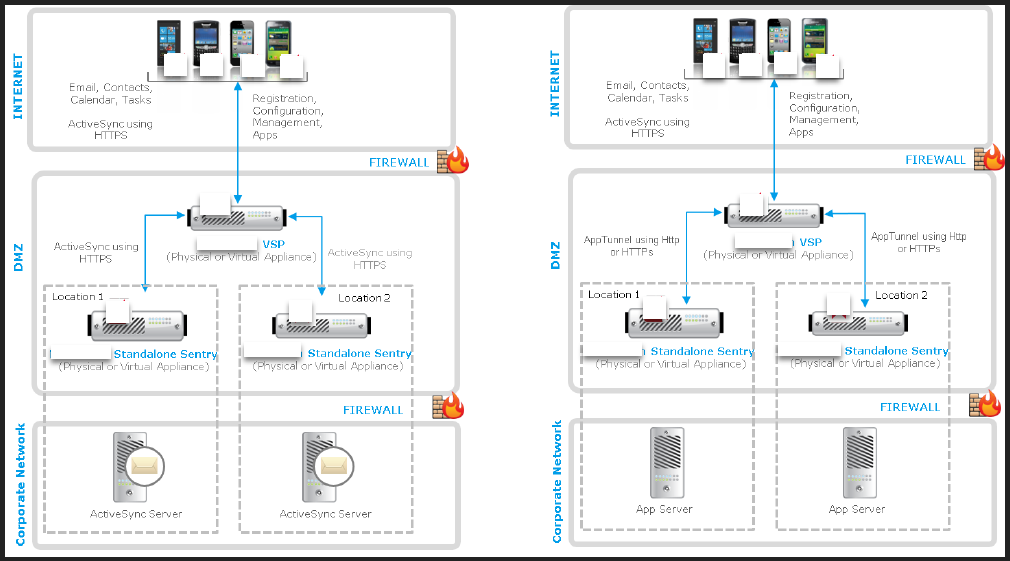
•You have ActiveSync or backend resources in different locations.
If you have ActiveSync or backend resources in different locations, use an Ivanti Standalone Sentry for each location. By co-locating the Standalone Sentry with the ActiveSync or backend resource, you minimize latency between Sentry and the server. Configure each Sentry to point to its co-located server (or servers if multiple servers back each other up).
Figure 1. Sentry in different locations
Typically, you use load balancers when using multiple Standalone Sentrys. For information about using load balancers with Standalone Sentry, contact Professional Services.
For more information about deploying Standalone Sentry for high availability and load balancing, see the following knowledge base articles:
•Sentry HA Networking Overview and Recommendations
•Mail Server Resource Consumption
Deployment with Ivanti Standalone Sentry behind a proxy
You can configure the Ivanti Standalone Sentry to be deployed behind a proxy, for example, an Apache or an F5 server. This allows for SSL termination to occur in front of Sentry even when using certificate based authentication.
By terminating SSL in the DMZ, Standalone Sentry enables an added layer of security, as well as accommodates the DMZ firewall policies.
Leveraging this configuration requires:
•Setting up an Apache or F5 proxy to front-end the Ivanti Standalone Sentry.
•Enabling this feature on Sentry via the UEM UI.
•Additional minor changes to references to hostname in some profiles.
Contact Professional Services or a certified partner to set up this deployment.
Deployment with multiple ActiveSync servers or backend resources
You can configure one Ivanti Standalone Sentry to work with multiple ActiveSync servers or backend resources that are backing each other up. You control when Standalone Sentry switches to another ActiveSync Server or backend resource by setting parameters involving communication failures Ivanti Standalone Sentry and the active ActiveSync servers or backend resource.