Collecting Web@Work log data
Administrators can enable Web@Work logging by setting key-value pairs in the Web@Work configuration in the Core Admin Portal.
This feature allows administrators to view log files generated by Web@Work, making it easier to diagnose and troubleshoot any issues.
Collecting log data for iOS devices
For information about using AppConnect log data, see the section “Logging for AppConnect apps for iOS” in the AppConnect and AppTunnel Guide.
To collect and view log data for Web@Work on iOS devices:
| 1. | In the Admin Portal, go to Policies & Configs > Configurations. |
| 2. | Select the Web@Work configuration and click Edit. |
| 3. | Under Custom Configurations, click Add to add a key-value pair. |
| 4. | Enter the following key-value pairs for Web@Work: |
|
Key |
Value |
Description |
|
log_files_limit |
0-10 |
This key limits the number of log files generated by Web@Work. The default value is 10. A value of 0 means there is no limit to the number of log files that can be generated. Each log file is 256KB. |
|
feedback_email_address |
the administrator’s email address |
This key configures the email address to which the Web@Work log files are sent. It also creates a Feedback button in Web@Work on users’ devices. Device users tap the Feedback button to send logs to the email address associated with the feedback_email_address key. |
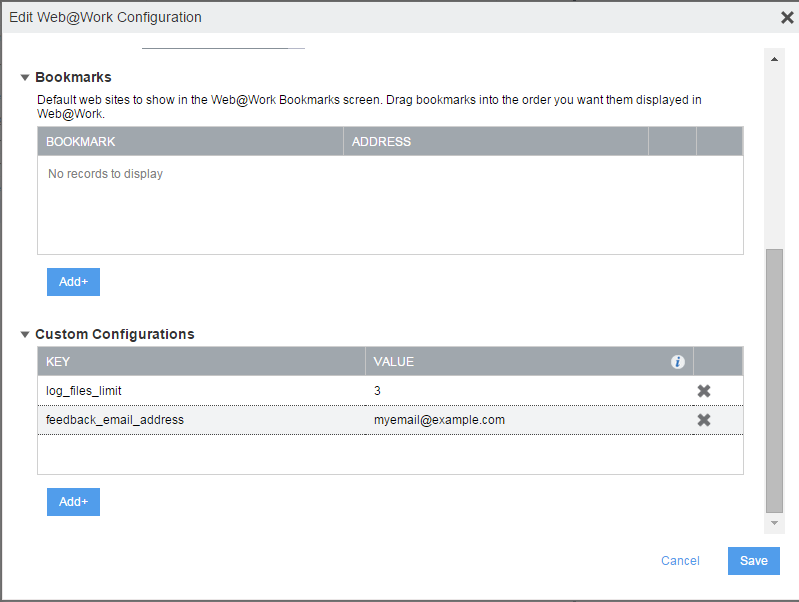
| 5. | Click Save. |
Collecting log data for Android devices
To collect and view log data for Web@Work on Android devices:
| 1. | In the Admin Portal, go to Policies & Configs > Configurations. |
| 2. | Select the Web@Work configuration and click Edit. |
| 3. | Under Custom Configurations, click Add to add a key-value pair. |
| 4. | Enter the following key-value pair for Web@Work: |
|
Key |
Value |
Description |
|
vlog_level |
1 |
Enables debug level of logs |
| 5. | Click Save. |
The log data will show the list of allowed and disallowed URLs that are configured using the whitelist and blacklist key-value pairs.