Adding a profile
If you selected Ivanti Access + Standalone Sentry, the Add Profile screen appears. Use the Profile page to create a profile for Ivanti Access and set up Ivanti Access + Standalone Sentry.
Before you begin
- The certificate must be signed by a trusted third-party CA, and must have its associated private key as part of the PKCS 12 file.
-
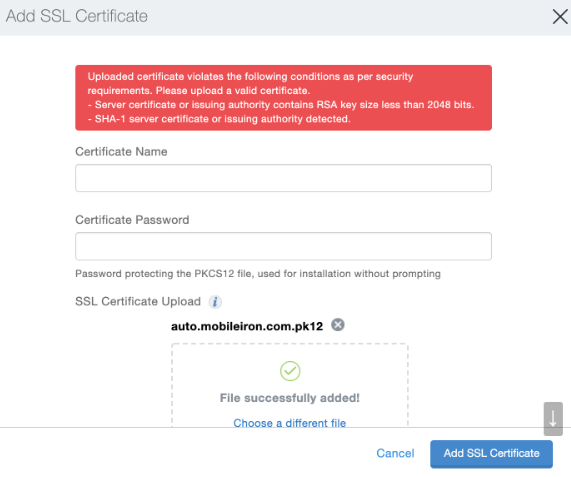
The certificate must comply with security requirements. See Error conditions for SSL certificate. For more information about error conditions, see Adding a profile . If the SSL certificate does not comply with the security requirements, then the following error displays.
-
Associate the SSL certificate with the Sentry second hostname.
Procedure
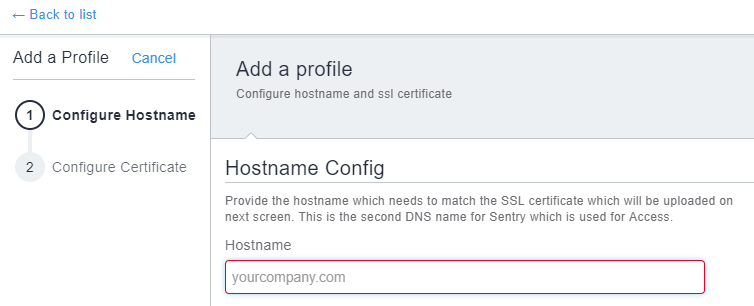
| 1. | For Hostname, enter the second hostname for the Standalone Sentry. |
The second hostname will be associated with Ivanti Access.
Figure 1. Configure hostname
| 2. | Click on Next. |
Figure 2. Configure certificate
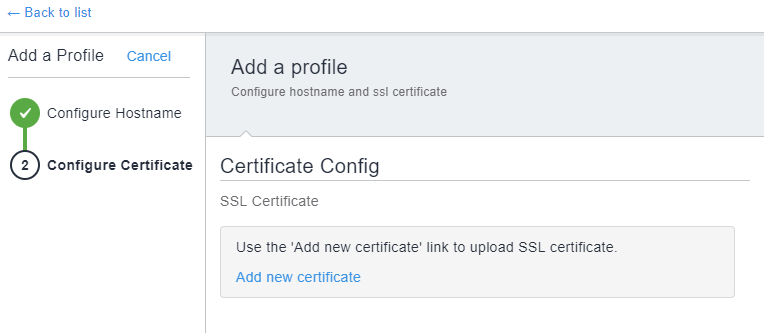
| 3. | Click Add new certificate to upload the SSL certificate associated with the second hostname. |
Figure 3. add new certificate
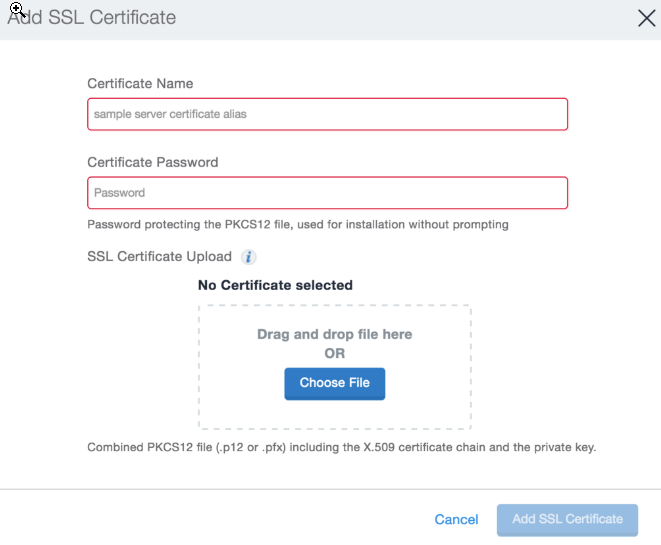
| 4. | For Certificate Name, enter a name by which you can identify the certificate. |
| 5. | For Certificate Password, enter the password required to open the certificate. |
| 6. | Click Choose File to navigate to the location of the certificate file or drag and drop the certificate file. |
| 7. | Click Add SSL Certificate to complete the process of adding the certificate. |
| 8. | Click Done to complete the profile setup. |
Figure 4. Complete profile setup
| 9. | Click Continue to view the profile in the Overview page. |
You will now have created a profile. You can now add a cloud service provider (SP) and identity provider (IdP) federated pair to this profile.
Next steps
Register a Standalone Sentry to Ivanti Access. See Registering a Standalone Sentry.
See Federated Pairs for information about adding an SP and an IdP federated pair.
Error conditions for SSL certificate
The SSL certificate you upload to the Sentry profile must meet the security requirements from Apple. If the certificate does not meet the security requirements the system displays error messages. Ivanti Access checks for the following error conditions:
-
SHA-1 server certificate or issuing authority detected.
-
Server certificate or issuing authority contains RSA key size less than 2048 bits.
-
Server certificate does not contain DNS name of the server in the Subject Alternative Name extension.
The following conditions are applicable only if the server certificate is issued after July 1, 2019 as indicated in the certificate. For more information, see the requirements provided by Apple: https://support.apple.com/en-us/HT210176
-
Server certificate does not contain an ExtendedKeyUsage (EKU) extension containing the id-kp-serverAuth OID.
-
TLS server certificates have validity period of more than 825 days.