Configuring certificate authentication using AppTunnel with TCP tunneling for Android AppConnect apps
Configuring certificate authentication with AppTunnel using TCP tunneling for Android AppConnect apps requires the following:
- AppTunnel TCP services on the Standalone Sentry that require certificate authentication.
-
The user certificate for the app to present to the enterprise server.
This certificate can be specifically for the enterprise server only, or a default user certificate if you do not require a specific certificate for a service. One other option is to use the same certificate that the app presents to the Standalone Sentry.
The certificate is either an identity certificate or a group certificate.
- Specifying the TCP service and the associated certificate in the app's app configuration on Ivanti Neurons for MDM.
The following sample configuration summarizes the configuration in Standalone Sentry and the AppConnect app configuration for a Finance app and Helpdesk app:
Sample configuration for certificate authentication with TCP tunneling
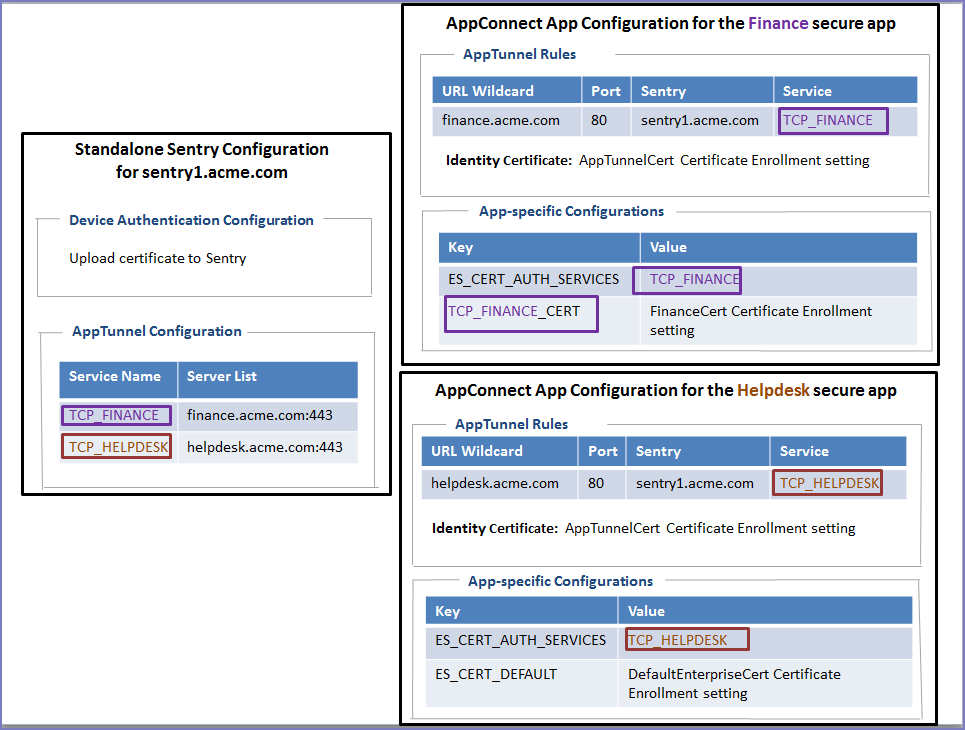
The Finance app and the Helpdesk app:
-
Authenticate to Standalone Sentry using the certificate defined by the AppTunnelCert Certificate Enrollment setting.
This Certificate Enrollment setting is specified as the Identity Certificate in the AppTunnel rules for the AppConnect app configuration for each app.
-
Use AppTunnel with TCP tunneling to access the TCP_FINANCE service and TCP_HELPDESK service, respectively.
-
Use certificate authentication with AppTunnel with TCP tunneling.
In each app’s AppConnect app configuration, the value of ES_CERT_AUTH_SERVICES lists the service that uses certificate authentication.
The two apps use different certificates to authenticate to their respective enterprise servers. The Finance app uses a specific certificate, defined in the FinanceCert Certificate Enrollment setting. The Helpdesk app uses a a default certificate, defined in the DefaultEnterpriseCert Certificate Enrollment setting, to authenticate to its enterprise server. Other apps that access other enterprise services also can use this certificate.
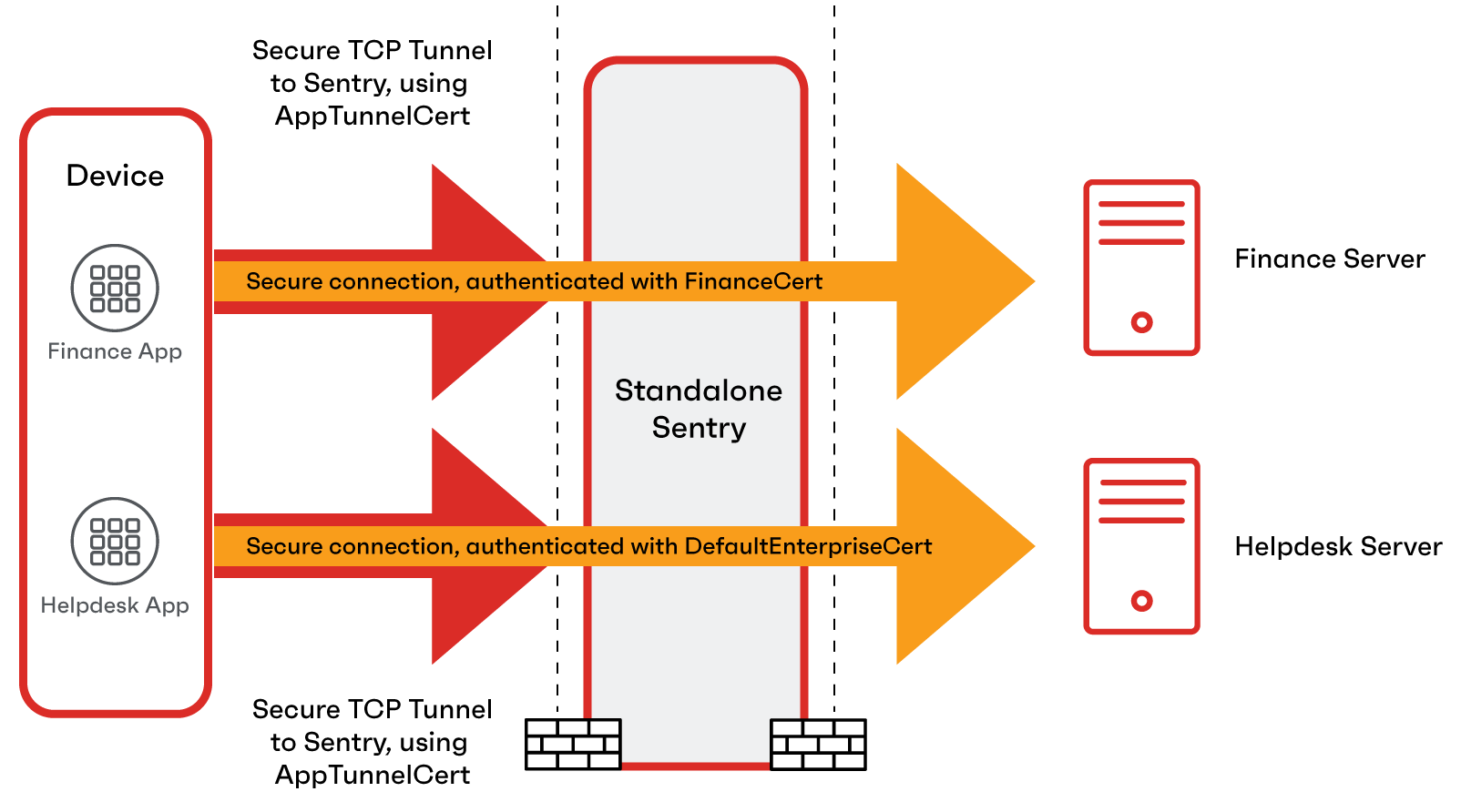
The following diagram illustrates the use of the certificates:
Certificate usage in certificate authentication with TCP tunneling
Before you begin
-
Configure the TCP AppTunnel service in Standalone Sentry profile.
For information about creating a AppTunnel service, see "Configuring Standalone Sentry for AppTunnel" and "AppTunnel Service" in the Standalone Sentry Guide for Ivanti Neurons for MDM.
-
Configure the certificate to authenticate to the enterprise server.
Add a Certificate Authority and create an Identity Certificate setting in Ivanti Neurons for MDM.
- Add the Certificate Authority in Admin > Certificate Authority.
- Create an Identity Certificate setting in Configuration > Add > Identity Certificate.
See the "Identity Certificate" in the Ivanti Neurons for MDM Administrator Guide.
-
Added an AppTunnel configuration app's app configuration.
Procedure
- On Ivanti Neurons for MDM, go to the App Catalog.
- Click the Android AppConnect app to edit its configurations.
- Go to the App Configurations tab.
- For AppConnect Custom Configurations, click +.
-
Enter the key-value pairs as described in the following table:
Table 24. Certificate key-value pairs Key
Value
AppConnect Custom Configuration
ES_CERT_AUTH_SERVICES
Enter th AppTunnel services that the app uses. Typically, apps use only one services. However, using mutliple services is supported. Separate each service witha semi-colon. The service name must match the service names created in the Sentry profile.
Example
TCP_HELPDESK
TCP_HELPDESK;TCP_WIKI;TCP_FINANCE
AppConnect Certificate Configuration
<service_name>_CERT
where <service_name> is one of the AppTunnel services that the app uses, which you listed in Configuring certificate authentication using AppTunnel with TCP tunneling for Android AppConnect apps.
Example:
TCP_HELPDESK_CERT
The key is case sensitive. Make sure that the <service_name> exactly matches, including case, the AppTunnel service name.
The Certificate Enrollment setting for a certificate used specifically for this AppTunnel service.
The configured Certificate Enrollment settings appear in the value field’s dropdown list.
Note the following:
-
If you do not add a
<service_name>_CERT key for a service that uses certificate authentication, the certificate specified for the key ES_DEFAULT_CERT is used for that service. -
If you do not add the ES_DEFAULT_CERT key, the certificate that authenticates the user to the Standalone Sentry is used.
ES_DEFAULT_CERT
The key is case sensitive.
The Certificate Enrollment setting for a default certificate used for services that do not require a specific certificate.
The configured Certificate Enrollment appear in the value field’s dropdown list.
-