What you configure on EPMM to use derived credentials
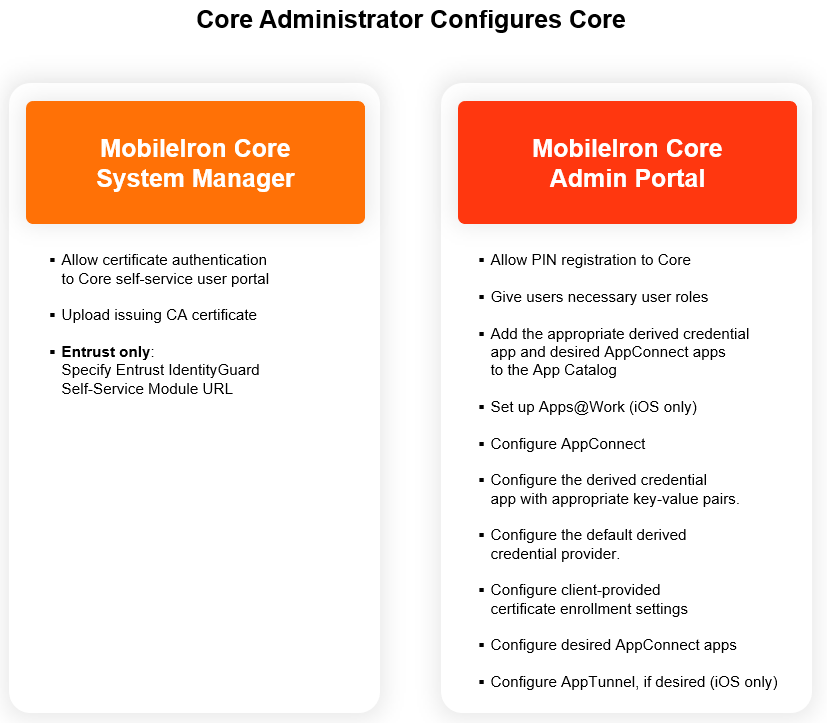
The following diagram summarizes the Ivanti EPMM configuration for using derived credentials, and shows whether you do the configuration on the System Manager or the Admin Portal.
The table following the diagram:
-
Describes each configuration task.
-
Indicates to which derived credential providers and device platform (iOS or Android) the task applies.
Note the following:
-
The task list assumes you use Apps@Work to distribute apps to iOS devices. However, using Apps@Work is not required. Various methods are available for device users to get the app on their iOS devices. Therefore, tasks related to using Apps@Work are optional.
-
The task list assumes that you want device users to register Mobile@Work using a registration PIN rather than with a user ID and password, since typically, device users who use smart cards do not have passwords. However, using a registration PIN is a requirement only with Entrust derived credentials. For other derived credential providers, it is not a requirement, and therefore the related tasks are optional.
Figure 1. Derived credential configuration summary on Ivanti EPMM
|
Task |
Notes |
|
1. Allow device users to authenticate to the Ivanti EPMM self-service user portal with the identity certificate on their smart cards. |
Allowing certificate authentication includes uploading to EPMM a valid issuing (CA) certificate or a valid supporting certificate chain. Entrust This task is required for Entrust derived credentials, because it is a prerequisite for configuring EPMM to use the Entrust IdentityGuard Self-Service Module (SSM) URL. All other derived credentials providers Although not strictly required for other derived credential providers, device users who use smart cards typically do not have passwords. Therefore, if you want them to be able to access the self-service user portal to, for example, generate a registration PIN, this step is required. |
|
2. Provide the Entrust IdentityGuard Self-Service Module (SSM) URL to EPMM. |
Entrust EPMM uses this URL to get derived credentials from Entrust. The device user will use the PIV-D Manager app to activate the derived credential on a device. |
|
3. Allow device users to register Mobile@Work on their devices to EPMM using a one-time registration PIN. |
Entrust This task is required for Entrust derived credentials because device users need a registration PIN to request an Entrust derived credential. All other derived credentials providers Although not strictly required for other derived credential providers, device users who use smart cards typically do not have passwords. Therefore, if you want them to be register Mobile@Work using a one-time registration PIN, this step is required. |
|
4. Give device users the necessary user roles to use the Ivanti EPMM self-service user portal. |
All derived credentials providers From the user portal, the device users can:
Additionally, when using Entrust From the user portal, device users get an Entrust derived credential, which includes getting the Entrust activation password to enter later on the device to activate the derived credential. This capability has no corresponding user portal role. |
|
5. Add the derived credential app to the App Catalog on EPMM. |
Entrust on Android Add the PIV-D Manager app for Android to the App Catalog on EPMM. Intercede on Android Add the Intercede derived credential app for Android to the App Catalog on EPMM. Entrust and DISA Purebred on iOS Add the PIV-D Manager app for iOS to the App Catalog on EPMM Other derived credential providers on iOS Add the appropriate third-party derived credential app to the App Catalog on EPMM. NOTE for iOS Devices
|
|
6. Add the AppConnect apps that will use the derived credential to the App Catalog on EPMM. |
All derived credentials providers NOTE for iOS Devices
|
|
7. Set up Apps@Work for device users. |
All derived credentials providers iOS only This task assumes you use Apps@Work for iOS. However, various methods are available for device users to get apps on their devices. |
|
8. Configure AppConnect. |
All derived credentials providers Configuring AppConnect allows device users to use AppConnect apps, including the derived credential app. |
|
9. Configure the PIV-D Manager app for iOS. |
Configure the PIV-D Manager app for iOS as follows: Entrust
DISA Purebred
For both Entrust and DISA Purebred
|
|
10. Configure the PIV-D Manager app for Android. |
Entrust on Android Configure the PIV-D Manager app for Android to:
|
|
11. Configure the Intercede derived credential app for Android |
Intercede on Android Configure the Intercede derived credential app for Android to receive its app-specific settings from EPMM, as defined by Intercede. |
|
12. Configure a third-party iOS derived credential app. |
On iOS, derived credential providers other than Entrust or DISA Purebred You configure a third-party derived credential app to receive app-specific settings from EPMM, as defined by the app vendor or developer. |
|
13. Configure the default derived credential provider. |
All derived credentials providers iOS only Select which derived credential provider is the default choice. If necessary, add a derived credential provider to the list. |
|
14. Configure client-provided certificate enrollment settings. |
All derived credentials providers The activated derived credentials are stored in Mobile@Work for iOS or Secure Apps Manager for Android. You configure an AppConnect app to use derived credentials by referencing a client-provided certificate enrollment setting from the app’s AppConnect app configuration (or Web@Work setting or Docs@Work setting). You configure a client-provided certificate enrollment setting for one of these purposes, as needed: authentication, signing, encryption, or decryption. The certificate enrollment setting is called client-provided because Mobile@Work for iOS or Secure Apps Manager for Android, known as client apps, provide the identity certificate to the AppConnect app. |
|
15. Configure Web@Work. |
All derived credentials providers This task is necessary only if your device users use Web@Work |
|
16. Configure Docs@Work. |
All derived credentials providers This task is necessary only if your device users use Docs@Work. |
|
17. Configure Email+. |
All derived credentials providers This task is necessary only if your device users use Email+. |
|
18. Configure third-party and in-house AppConnect apps. |
All derived credentials providers This task is necessary only if your device users use other AppConnect apps that use derived credentials. |
|
19. Configure AppTunnel with |
All derived credentials providers iOS only This task is necessary only if you want to use:
Using AppTunnel with HTTP/S tunneling, you authenticate the user to the Standalone Sentry using a derived credential. |
|
20. Configure AppTunnel with |
All derived credentials providers iOS only This task is necessary only if you want to use:
Using per-app VPN with Tunnel for iOS (AppTunnel with TCP tunneling), AppConnect apps can authenticate to the backend resource with a derived credential. |