Creating compliance policy rules and device groups
Within Ivanti Mobile Threat Defense Solution, there are three threat types. Within each type there are severity levels: Critical, Elevated, Normal and Low. Altogether you have:
- Device - Critical, Elevated, Normal and Low severity levels
- Network - Critical, Elevated, Normal and Low severity levels
- App - Critical, Elevated, Normal and Low severity levels
For each threat type, you create compliance policy rules based on the threat severity. Each of the policy types have a predefined condition, with the exception of custom policies, that determines when a device is not compliant. The administrator can choose from a list of compliance actions to be taken against violating devices.
As a best practice, you should have the following compliance policy rules:
- For Low and Normal threat types - use Send Alert
- For Elevated threat type - use Block Access and/or Quarantine
-
For Critical threat type - use Quarantine or Tier Compliance:
- Block - notify
- Notification
- Quarantine - remove. If Low, send notification and let user decide what action to take.
- Tiered Compliance 23 hours
- Tiered Compliance 4 hours
Important! If a policy has previously been triggered on a device, adding the tiered policy will reset the policy and any compliance actions that had previously been applied. The new custom policy will be applied at the next device check-in.
Example
A managed Ivanti Go client user connects to hotel Wi-Fi:
- Tier 1 - Warn - Ivanti Mobile Threat Defense alerts the device user "You just connected to unsecure Wi-Fi."
- Tier 2 - Block - After 2 hours, Ivanti Mobile Threat Defense blocks the user's access to email and AppConnect apps.
- Tier 3 - Quarantine - After 4 hours, MTD quarantines and blocks the Wi-Fi; removes user's access to the company network.
Creating standard policies
You can choose from a wide array of Ivanti Neurons for MDM policy templates, that you can use or modify to create robust compliance policies. As an example, let's set up a policy to restart an iOS device if the jail-breaking policy is violated.
For reference and other information about these options, see Policy > Adding a custom policy in the Ivanti Neurons for MDM Administrator Guide.
Procedure
-
From the Ivanti Neurons for MDM administrator console, click Policies. The Policies page displays.
-
Click +Add for policy options. The Choose Policy Type page displays.
-
Click Compromised Devices. The Compromised Devices menu displays.
-
Give the policy a useful name in the Name field. Add an optional description, if you desire.
-
From the Choose Actions section, click Monitor to configure tiered compliance actions.
Ivanti Sentry version 9.0.0 or later is required to utilize the tiered compliance actions.
-
In the first Actions field, select an option from the menu:
Figure 1. Tiered compliance action menu
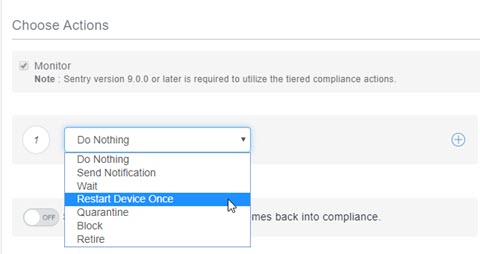
- Do Nothing (the default) – Take no action.
- Send Notification – Follow the prompts to create a warning email.
- Wait – Select the waiting time in minutes, days, or hours.
- Restart Device Once – When a device goes out of compliance, the device is restarted. This will bring some devices back into compliance.
- Quarantine – Configure default and optional quarantine actions.
- Block – Uses Ivanti Sentry to block managed devices from accessing email and AppConnect-enabled applications. Sentry version 9.0.0 or later is required to utilize the block action.
- Retire – Retires the device. This action cannot be undone.
-
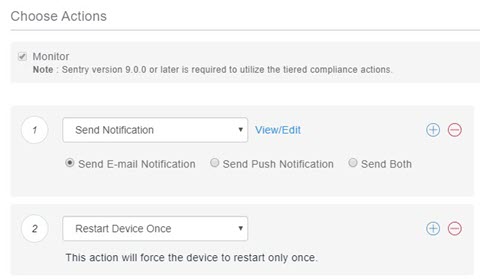
For example, you might want your first action to be an email or text message to the user. So select Send Notification, and configure your message.
-
To add more compliance levels, click the plus (+) icon to the right of the action. To delete any level, click the red minus (–).
-
For the second action, select Restart Device Once. No configuration for this option is needed.
Figure 2. Restart Device Once option to limit notifications
-
Click Yes, I understand... after you read how these policies will affect devices.
-
Click Next. The Distribute page displays.
-
Select a distribution option.
-
Click Done. The policy is pushed to devices at the next check-in.
Creating custom policies
This section discusses how to define and create compliance actions using custom policies based on the MTD custom attributes. The compliance actions are evaluated during the regularly scheduled client check-in event, and the selected compliance actions are enforced on the client by Ivanti Neurons for MDM when the device is determined to be non-compliant with policy.
With custom compliance actions, you can create actions to better manage access control. With tiered compliance actions, you can customize them to include up to four levels of action to better manage compliance actions: Critical, Elevated, Normal, and Low.
Procedure
- In Ivanti Neurons for MDM administrator console, go to Policies.
- Click + Add.
- Select Custom Policy.
- Enter mtdnotify as the policy name.
- Under Conditions, select Custom Device Attribute.
- Select mtdnotify from the drop-down box and set the condition is equal to 1.
- Under Choose Actions, select Monitor and Send Email and Push Notification.
- Under Email Message fields, enter your preferred subject and body text.
- Under Push Notification, enter your preferred message text.
- Click Yes,Next, and Done.
-
Repeat this procedure to add the following policies (and any other custom policies you create) :
Table 10. Recommended policies Policy Name Custom Device Attribute Attribute mtdblock
mtdblock
- Monitor
- Send Email and Push Notification
- Block
mtdquarantine
mtdquarantine
- Monitor
- Send Email and Push Notification
- Quarantine
mtdtiered4hours
mtdtiered4hours
- Monitor
- Send Email and Push Notification
- All compliance actions
Creating device groups
You can create and match device groups with custom policies you have created.
Procedure
- In the Ivanti Neurons for MDM administrator console, go to Devices > Device Groups.
- Click + Add.
- Enter mtdNotify as the device group name.
- Under Dynamically Managed groups, select Custom Device Attribute.
- Select mtdnotify from the drop-down box and set the condition is equal to 1.
- Click Save.
-
Repeat this procedure to add the following device groups (and any other custom device groups you create):
Table 11. Recommended device groups Device Group Name Custom Device Attribute mtdBlock
mtdblock
mtdQuarantine
mtdquarantine
mtdTiered4hours
mtdtiered4hours