Palo Alto Networks GlobalProtect
|
Item |
Description |
||||||||||||||||||
|
Name |
Enter a short phrase that identifies this VPN setting. |
||||||||||||||||||
|
Description |
Provide a description that clarifies the purpose of these settings. |
||||||||||||||||||
|
Connection Type |
Select Palo Alto Networks GlobalProtect. |
||||||||||||||||||
|
Always-on VPN (supervised only) |
Select to enable the VPN connection to remain on at all times. This setting applies only to supervised devices. |
||||||||||||||||||
|
Allow user to disable automatic connection |
Select to allow device users to disconnect automatically triggered connections. This setting applies only to supervised devices. |
||||||||||||||||||
|
Use same tunnel configuration for Cellular and Wi-Fi |
Select to configure one VPN tunnel for both cellular and wi-fi data. This setting applies only to supervised devices. |
||||||||||||||||||
|
Cellular/Wi-Fi (Cellular and wi-fi configurations appear separately when you select Always-on VPN.) |
|||||||||||||||||||
|
Server |
Enter the IP address, hostname, or URL for the VPN server. |
||||||||||||||||||
|
Local Identifier |
Required. Identifier of the IKEv2 client in one of the following formats:
|
||||||||||||||||||
|
Remote Identifier |
Required. Remote identifier in one of the following formats:
|
||||||||||||||||||
|
Dead Peer Detection Rate |
Optional. Defaults to Medium. Select one of the following:
|
||||||||||||||||||
|
Use IPv4/IPv6 Internal Subnet Attributes |
Optional. If selected, negotiations should use IKEv2 Configuration Attribute INTERNAL_IP4_SUBNET and INTERNAL_IP6_SUBNET. Disabled by default. Available in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. |
||||||||||||||||||
|
Disable Mobility and Multihoming |
Select to disable mobility and multihoming (MOBIKE). Available in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. |
||||||||||||||||||
|
Disable redirects |
Optional. If selected, disables IKEv2 redirect. If not selected, the IKEv2 connection would be redirected if a redirect request is received from the server. By default, not selected. Available in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. |
||||||||||||||||||
|
Enable NAT keepalive |
Optional. Select to enable Network Address Translation (NAT) Keepalive offload for Always On VPN IKEv2 connections. Keepalive packets are used to maintain NAT mappings for IKEv2 connections. These packets are sent at regular intervals when the device is awake. If selected, Keepalive packets would be sent by the chip even while the device is asleep. The default interval for the Keepalive packets for Always On VPN is 20 seconds over WiFi and 110 seconds over Cellular interface. Available in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. |
||||||||||||||||||
|
NATKeepAliveInterval |
Optional. Controls the interval over which Keepalive packets are sent by the device. The minimum value is 20 seconds. If no key is specified, the default is 20 seconds. Available in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. |
||||||||||||||||||
|
EnablePFS |
Optional. Select to enable Perfect Forward Secrecy for IKEv2 connections. By default, not selected. Available in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. |
||||||||||||||||||
|
Authentication |
|||||||||||||||||||
|
Machine Authentication |
Select Shared Secret/Group Name or Certificate. |
||||||||||||||||||
|
Shared Secret |
If you select Shared Secret/Group Name, enter shared secret to be used for IKE authentication. |
||||||||||||||||||
|
Identity Certificate |
If you select Certificate, select the identity certificate to be used as the account credential. If you select Certificate, and extended authentication (EAP) is not used, this certificate will be sent out for IKE client authentication. If extended authentication is used, this certificate can be used for EAP-TLS. |
||||||||||||||||||
|
Server Certificate Issuer Common Name |
Optional. The Common Name of the server certificate issuer. If set, this field will cause IKE to send a certificate request based on this certificate issuer to the server. |
||||||||||||||||||
|
Server Certificate Common Name |
Optional. The Common Name of the server certificate. This name is used to validate the certificate sent by the IKE server. If not set, the Remote Identifier will be used to validate the certificate. |
||||||||||||||||||
|
Enable EAP |
Select to enable extended authentication. |
||||||||||||||||||
|
Authentication Type |
Select Certificate or Username/Password. |
||||||||||||||||||
|
Identity Certificate |
If you selected Certificate as the EAP authentication type, select the identity certificate you want to use for extended authentication from the drop-down list. |
||||||||||||||||||
|
Username |
If you selected Username/Password as the EAP authentication type, enter a value for the username. Required. Include at least one of the following variables: $USERID$, $EMAIL$, $USER_CUSTOM1$, $USER_CUSTOM2$, $USER_CUSTOM3$, $USER_CUSTOM4$, $NULL$ You can use combinations such as the following:
Enter $NULL$ if you want the field presented to the user to be blank. Users will need to fill in the relevant username. |
||||||||||||||||||
|
Password |
If you selected Username/Password as the EAP authentication type, enter a value for the password. Required. Include at least one of the following variables: $USERID$, $EMAIL$, $PASSWORD$, $USER_CUSTOM1$, $USER_CUSTOM2$, $USER_CUSTOM3$, $USER_CUSTOM4$, $NULL$ You can use combinations such as $EMAIL$:$PASSWORD$ Enter $NULL$ if you want the field presented to the user to be blank. Users will need to fill in the relevant password. |
||||||||||||||||||
|
IKE SA Params (A Security Association establishes shared security attributes between two network entities to support secure communication.) |
|||||||||||||||||||
|
Encryption algorithm |
Optional. Select one of the following:
|
||||||||||||||||||
|
Integrity algorithm |
Optional. Select one of the following:
|
||||||||||||||||||
|
Diffie-Hellman Group |
Optional. Select one of the following: 0, 1, 2 (Default), 5, 14, 15, 16, 17, 18, 19, 20, 21. |
||||||||||||||||||
|
Lifetime In Minutes |
Optional security association lifetime (rekey interval) in minutes. Valid values are 10 through 1440. Defaults to 1440 minutes. |
||||||||||||||||||
|
Child SA Params (A Child SA is any SA that was negotiated via the IKE SA.) |
|||||||||||||||||||
|
Encryption algorithm |
Optional. Select one of the following:
|
||||||||||||||||||
|
Integrity algorithm |
Optional. Select one of the following:
|
||||||||||||||||||
|
Diffie-Hellman Group |
Optional. Select one of the following: 0, 1, 2 (Default), 5, 14, 15, 16, 17, 18, 19, 20, 21. |
||||||||||||||||||
|
Lifetime In Minutes |
Optional security association lifetime (rekey interval) in minutes. Valid values are 10 through 1440. Defaults to 1440 minutes. |
||||||||||||||||||
|
Service Exceptions (Configure exceptions to VPN tunnel. This section is only displayed if the Always-on VPN (supervised only) option is selected at the top of the window.) |
|||||||||||||||||||
|
Voice Mail |
Select one of the following options for voicemail:
|
||||||||||||||||||
|
Air Print |
Select one of the following options for Air Print:
|
||||||||||||||||||
|
Allow traffic from captive web sheet outside the VPN tunnel |
Select to allow traffic from captive web sheets outside the VPN tunnel. |
||||||||||||||||||
|
Allow traffic from all captive networking apps outside the VPN tunnel |
Select to allow traffic from all captive networking apps outside the VPN tunnel. When selecting this item, skip to the proxy server section. |
||||||||||||||||||
|
Captive Networking App Bundle Identifiers |
Specify the apps whose traffic you want to allow outside the VPN tunnel. Captive networking apps may require additional entitlements to operate in a captive environment. Click Add+ to add the bundle ID of a relevant app to the list of apps allowed outside the VPN tunnel. Note: This section is only displayed if the Allow traffic from all captive networking apps outside the VPN tunnel option is not selected. |
||||||||||||||||||
|
Proxy |
Select None, Manual, or Automatic to configure a proxy. If you select Manual, you must specify the proxy server name and port number. If you select Automatic, you must specify the proxy server URL. |
||||||||||||||||||
|
Proxy Server URL |
Automatic Proxy Enter the URL for the proxy server. Enter the URL of the location of the proxy auto-configuration file. |
||||||||||||||||||
|
Proxy Server |
Manual Proxy Enter the name for the proxy server. |
||||||||||||||||||
|
Proxy Server Port |
Manual Proxy Enter the port number for the proxy server. |
||||||||||||||||||
|
Type |
Manual Proxy Select Static or Variable for the type of authentication to be used for the proxy server. |
||||||||||||||||||
|
Proxy Server User Name |
Manual Proxy If the authentication type is Static, enter the username for the proxy server. If the authentication type is Variable, the default variable selected is $USERID$. |
||||||||||||||||||
|
Proxy Server Password |
Manual Proxy If the authentication type is Static, enter the password for the proxy server. Confirm the password in the field below. If the authentication type is Variable, the default variable selected is $PASSWORD$. |
||||||||||||||||||
|
Proxy Domains (iOS only) |
The VPN will only proxy for the domain and domain suffixes specified here (.com and .org are examples of top-level domain suffixes). Domain suffixes can be used to match multiple domains. For example, .com would include all .com domains, and example.com would include all domains ending in example.com, such as pages.example.com and mysite.example.com. Wildcards are not supported. Click Add+ to add a domain. |
||||||||||||||||||
|
VPN On Demand |
Select Enable to enable VPN On Demand. On Demand rules are associated with an array of dictionaries that define the network match criteria identifying a particular network location. VPN On Demand matches the dictionaries in the On Demand Rules against properties of your current network connection to determine whether domain-based rules should be used in determining whether to connect, then handles the connection as follows:
VPN On Demand rules are applied when the device's primary network interface changes, for example when the device switches to a different Wi-Fi network. Note the following:
|
||||||||||||||||||
|
Per-App VPN |
Per-app VPN for IKEv2 for iOS is only supported in iOS 9.0 through the most recently released version of iOS as supported by MobileIron. Select Yes to create a per-app VPN setting. An additional license may be required for this feature. You cannot delete a per-app VPN setting that is being used by an app. Remove the per-app VPN setting from the app before you delete the setting. You can enable per-app VPN for an app when you:
|
||||||||||||||||||
|
Provider Type |
|
||||||||||||||||||
|
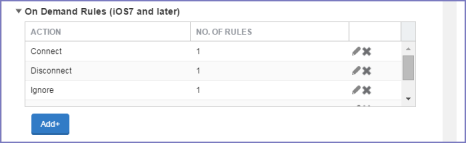
On-Demand Rules (iOS 7 and later) |
|||||||||||||||||||
|
Whenever a network change is detected, the VPN On Demand service compares the newly connected network against the match network criteria specified in each set of rules (in order) to determine whether VPN On Demand should be allowed or not on the newly joined network. Rule sets are checked sequentially, beginning with the first. A rule set matches the current network only if all of the specified policies in that rule set match. If a rule set matches the current network, a server probe is sent if a URL is specified in the profile. VPN then acts according to the policy defined in the dictionary (for example, Allow, Ignore, Evaluate Connection, Connect, or Disconnect). Define sets of evaluation rules for each action that can be taken by VPN On Demand: Allow, Connect, Disconnect, Evaluate Connection, and Ignore. You can define more than one set of rules for each type of action that can be taken. For each set of evaluation rules, the number of rules defined for that set is indicated in the No. of Rules column.
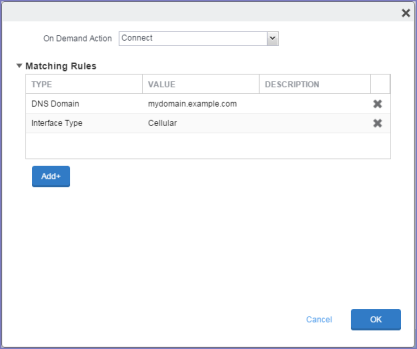
Click Add+ to add a new set of On Demand evaluation rules. A rule creation window is displayed. |
|||||||||||||||||||
|
From the On Demand Action drop-down list, select the action you want to be taken when the rules you create below are matched. The following actions are available:
|
|||||||||||||||||||
|
Matching Rules |
|||||||||||||||||||
|
For each rule you create, enter one of the following types:
Enter a value for each rule and an optional description. After adding your rules, click OK. |
|||||||||||||||||||
|
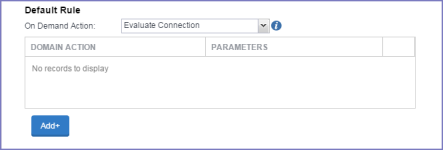
Default Rule |
Define a default rule that simply specifies a default VPN On Demand action in case none of the On Demand rules match, or if no On Demand rules have been defined. From the On Demand Action drop-down list, select the action you want to be taken by default, if none of the rules match or none are defined. The following actions are available:
|
||||||||||||||||||
|
If you select Evaluate Connection, a domain actions table is displayed:
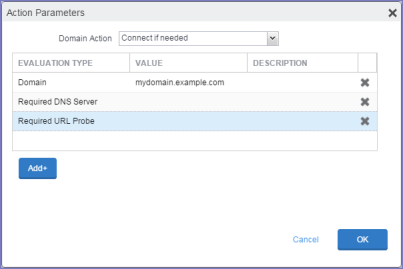
Click Add+ to add a domain action. The Action Parameters window is displayed. |
|||||||||||||||||||
|
From the Domain Action drop-down list, select one of the following actions to be taken for the domains listed in the table:
|
|||||||||||||||||||
|
Click Add+ to any of the following:
Add a value and optional description for each entry. Click OK to save your domain action parameters. |
|||||||||||||||||||
Domains
Safari Domains
Applicable to: Safari Domains (iOS 7 and later; macOS 10.11 and later)
| NOTE: | You must update your VPN software to a version that supports Per-app VPN. |
If the server ends with one of these domain names, a VPN connection is started automatically.
- Add+ - Click to add a domain.
- Safari Domain - Enter a domain name. Only alphanumeric characters and periods (.) are supported.
- Description - Enter a description for the domain.
Calendar Domains
Applicable to: Calendar Domains (iOS 13 and later; macOS 10.15 and later)
If the server ends with one of these domain names, a VPN connection is started automatically.
- Add+ - Click to add a domain.
- Calendar Domain - Enter a domain name. Only alphanumeric characters and periods (.) are supported.
- Description - Enter a description for the domain.
Contact Domains
Applicable to: Contact Domains (iOS 13 and later; macOS 10.15 and later)
If the server ends with one of these domain names, a VPN connection is started automatically.
- Add+ - Click to add a domain.
- Contact Domain - Enter a domain name. Only alphanumeric characters and periods (.) are supported.
- Description - Enter a description for the domain.
Mail Domains
Applicable to: Mail Domains (iOS 13 and later; macOS 10.15 and later)
If the server ends with one of these domain names, a VPN connection is started automatically.
- Add+ - Click to add a domain.
- Mail Domain - Enter a domain name. Only alphanumeric characters and periods (.) are supported.
- Description - Enter a description for the domain.
Custom Data
- Add+ - Click to add a new key / value pair.
- Key / Value - Enter the Key / value pairs necessary to configure the VPN setting. The app creator should provide the necessary key / value pairs.