Introduction
The Secure Boot feature offers protection against unauthorized bootloader and kernel images, malware, and rootkits, and ensures compliance with secure-by-design principle while improving boot time security validation. This feature is supported on ISA6000/ISA8000 Hardware Appliances, VMware for ICS release 22.8R2/25.1.0.0, Hyper-V, OpenStack and Azure for ICS release 25.1.1.0.
For deploying on Hyper-V, see Deploying Ivanti Connect Secure Appliance on Hyper-V.
For deploying on Openstack KVM, see Deploying Ivanti Connect Secure Appliance on OpenStack KVM.
For deploying on Azure, see Deploying Ivanti Connect Secure Appliance on Azure.
Abbreviations Used in This Guide
|
Term |
Description |
|---|---|
|
BIOS and UEFI |
Basic input / output system (BIOS) is a program fixed and embedded on a device's microprocessor that helps to initialize hardware operations. Unified Extensible Firmware Interface (UEFI) offers users a faster and sleeker experience. It supports secure booting of the bootloader. BIOS uses 16-bit mode and has a limited user interface, UEFI uses 32-bit or 64-bit mode and offers a more advanced graphical user interface. |
|
MBR and GPT |
Master Boot Record (MBR) is the information in the first sector of a hard disk or a removable drive. GUID Partition Table (GPT) is introduced as part of the Unified Extensible Firmware Interface (UEFI) initiative.
GPT provides a more flexible mechanism for partitioning disks than the older Master Boot Record (MBR) partitioning scheme. |
|
GRUB and GRUB2 |
GRand Unified Bootloader (GRUB or GNU GRUB) is a Multiboot boot loader for Linux and other Unix-based OSes. GRUB2 bootloader is the bootloader on x86 systems that is used to load the linux kernel or any other OS. GRUB2 is allowed to load by UEFI if its signature matches the signature in the UEFI’s whitelist DB. |
|
ICS |
Ivanti Connect Secure (ICS) provides a seamless, cost-effective SSL VPN solution for remote and mobile users from any web-enabled device to corporate resources. |
| ISA | Ivanti Secure Access hardware appliance. |
Benefits of Secure Boot Feature
•Protection from unauthorized bootloader images - Secure Boot prevents booting unauthorized bootloader (GRUB) images via signature verification of the bootloader (GRUB) from UEFI.
•Protection from unauthorized kernel images - Secure Boot prevents booting unauthorized kernel images via signature verification of the kernel from GRUB bootloader.
•Protection against malware and rootkits - Secure Boot prevents loading malware/rootkits via chain of trust from UEFI to GRUB to Kernel using signatures verification.
•Compliance with Security By Design principle for boot protection.
This feature is supported on:
•Connect Secure 22.8R2 Release
•Connect Secure 25.1.x Release
Connect Secure 22.8R2 Release
The upgrade process for hardware appliances involves uploading the 22.8R2 package, importing logs and configurations, converting MBR to GPT partitions, and transitioning from Legacy BIOS to UEFI.
|
Note |
|
Upgrading from Non-Secure Boot to Secure Boot
To upgrade from non-Secure Boot 22.x release to Secure Boot newer 22.8R2 release:
1.Log into the Admin portal.
2.Upload the 22.8R2 package using standard upgrade process. For details, see ICS Administration Guide.
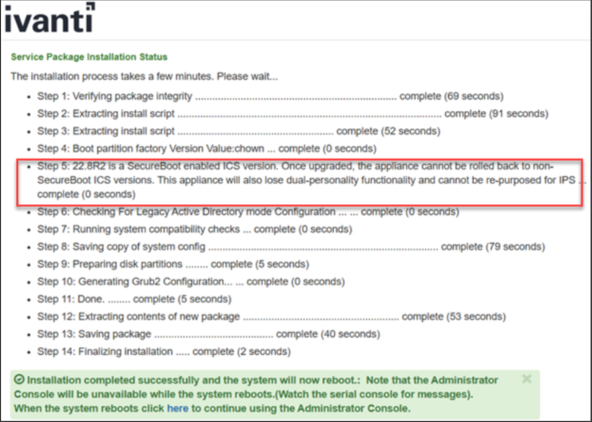
The system performs the following actions, which requires multiple reboots as part of the upgrade.
•All the logs, configs are imported from previous non-Secure Boot to Secure Boot supported 22.8R2 release builds.
•Converts MBR to GPT partitions.
•Legacy BIOS is converted to UEFI
•For ISA6000, 2-stage UEFI upgrade process. Admin can expect at least two additional reboots in this case.
•For ISA8000, single-stage UEFI upgrade process. Admin can expect one additional reboot in this case.
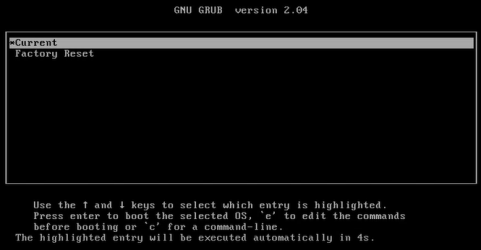
•Factory Reset partition will be upgraded from previous 22.x release build to the Secure Boot 22.8R2 release build.
After the upgrade to the Secure Boot build (detailed above) is complete, the images on an ICS would look like the following:

If you decide NOT to upgrade to the first Secure Boot release, i.e. 22.8R2, but wait till the next available release, then you need to upgrade in the following order:
- First upgrade to 22.8R2 Secure Boot release as described above.
- Next upgrade to the newer version.
Deploying Virtual ICS from OVF
ICS 22.8R2 needs vTPM to be enabled at the ESXi infrastructure. To enable vTPM, you need VMware vSphere and a key provider, such as Native Key Provider. vTPM and Native Key Provider are licensed for use in all vSphere versions. Supported ESXi versions are 7.0.x and 8.0.x.
vTPM is a VMware component, and for the latest documentation please refer to VMware product documentation.
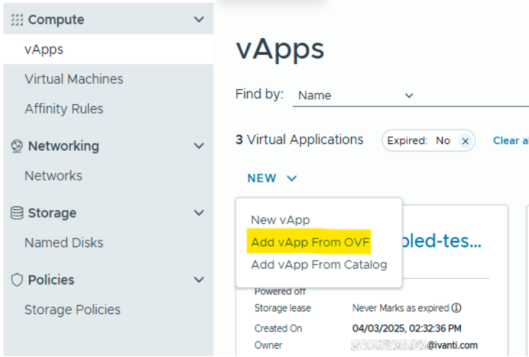
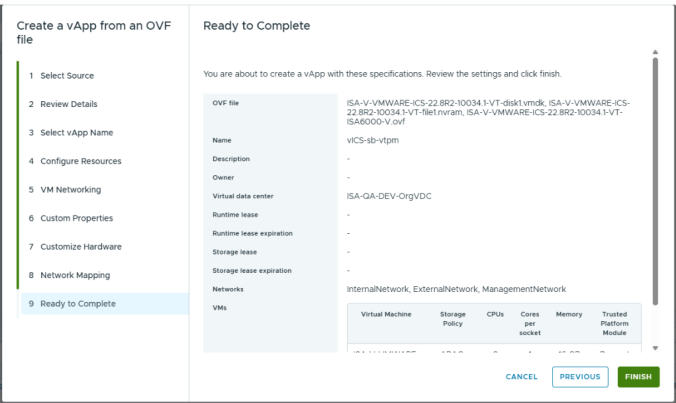
To deploy Virtual ICS (vICS) from OVF:
1.Select Compute > vApps > New, and then select the Add vAPP From OVF option.
2.Select all three files required for deployment of vICS:
•OVF file - example: ISA-V-VMWARE-ICS-22.8R2-<build-number>-VT-ISA8000-V.ovf
•NVRAM file - example: ISA-V-VMWARE-ICS-22.8R2-<build-number>-VT-file1.nvram
•VMDK file - example: ISA-V-VMWARE-ICS-22.8R2-<build-number>-VT-disk1.vmdk
3.Follow the wizard and configure the necessary details as per your requirement. Click Finish.
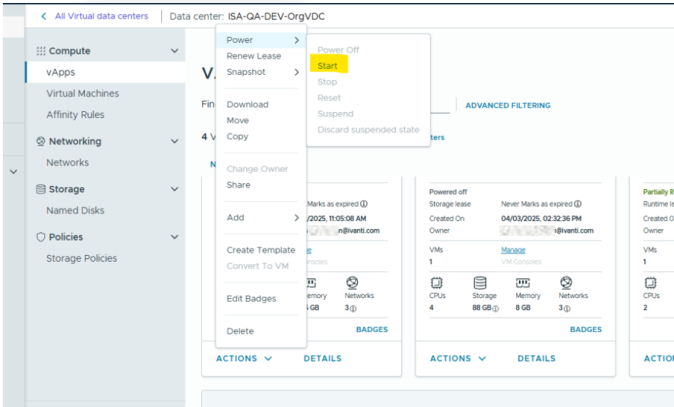
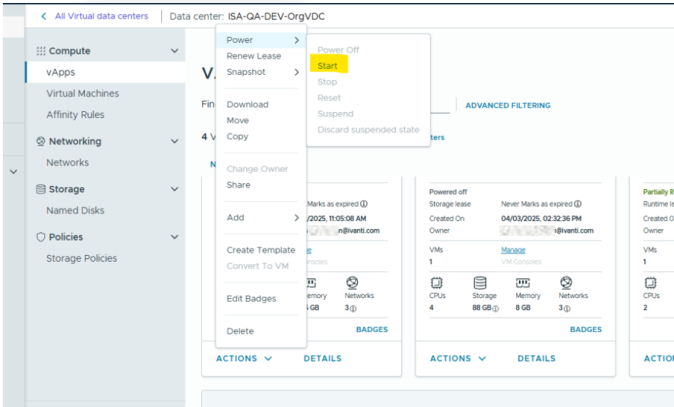
4.Click Start to power on vICS.
vTPM on ESXi 8.0.x
No additional steps are required to add vTPM when the ESXi itself is enabled with vTPM support.
Prerequisites
•vCenter license
•ESXi license
•Key Management Server on vCenter
•vTPM requirements as specified by Broadcom https://techdocs.broadcom.com/us/en/vmware-cis/aria/aria-automation/all/vtpm-overview.html
vTPM on ESXi 7.x
If ESXi 7.2 is used as hypervisor, then vTPM does not get attached automatically on deploying virtual ICS. Attach vTPM by selecting Settings > ADD NEW DEVICE > Trusted Platform Module.
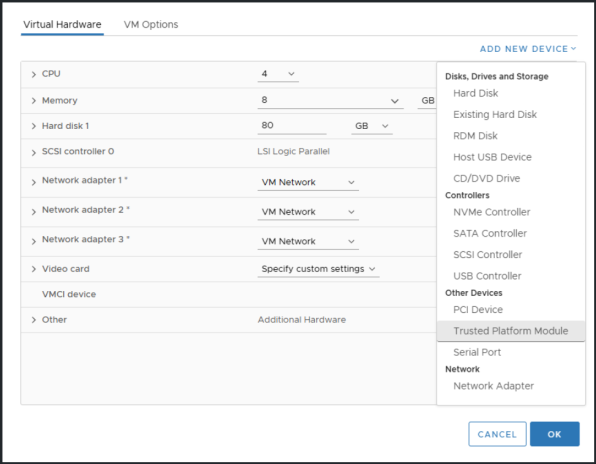
Due to VMware limitations, sometimes Trusted Platform Module is not visible in ADD NEW DEVICE option. In such scenario, follow the below steps.
1.Navigate to Settings > VM Options > General Options.
2.Change Guest OS Family from Other to Linux.
3.Change Guest OS Version from Other (64-bit) to TPM supported version like Ubuntu Linux (64-bit).
4.Click OK.
5.Attach vTPM by selecting Settings > ADD NEW DEVICE > Trusted Platform Module.
6.Revert Guest OS Family from Linux to Other.
7.Revert Guest OS Version from TPM supported version like Ubuntu Linux (64-bit) to Other (64-bit).
Limitations
•Upgrade from older 22.7R2.x release to rel-22.8R2 release is not supported for virtual ICS on VMware platform.
•Removing vTPM from virtual ICS can make virtual ICS non recoverable.
•Cloning virtual ICS with replace TPM option is not supported.
•Exporting virtual ICS with vTPM to template is not supported by VMware.
Connect Secure 25.1.x Release
25.1.0.0 Release
The upgrade process for hardware appliances involves uploading the 25.1.0.0 package, importing logs and configurations.
|
Note |
|
Upgrading from 22.8R2 Release to 25.1.0.0 Release
To upgrade from 22.8R2 release to 25.1.0.0 release:
1.Log into the Admin portal.
2.Upload the 25.1.0.0 package using standard upgrade process. For details, see ICS Administration Guide.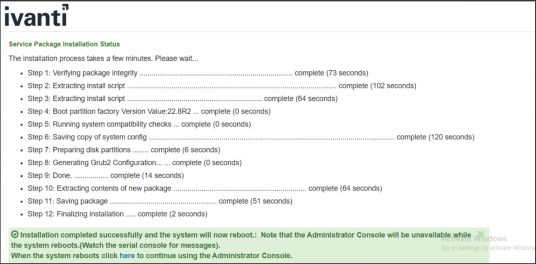
The system performs actions, which requires multiple reboots as part of the upgrade.
After the upgrade to the Secure Boot build (detailed above) is complete, the images on an ICS would look like the following:

Deploying Virtual ICS from OVF
ICS 25.1.0.0 needs vTPM to be enabled at the ESXi infrastructure. To enable vTPM, you need VMware vSphere and a key provider, such as Native Key Provider. vTPM and Native Key Provider are licensed for use in all vSphere versions. Supported ESXi versions are 7.0.x and 8.0.x.
vTPM is a VMware component, and for the latest documentation please refer to VMware product documentation.
To deploy Virtual ICS (vICS) from OVF:
1.Select Compute > vApps > New, and then select the Add vAPP From OVF option.
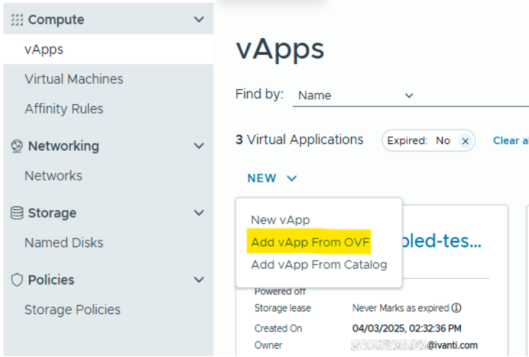
2.Select all three files (OVF, NVRAM, VMDK) required for deployment of vICS:
•OVF file - Select the OVF file based on your deployment requirement.
For example:
•ISA-V-VMWARE-ICS-25.1.0.0-<build-number>-VT-ISA8000-V.ovf
•ISA-V-VMWARE-ICS-25.1.0.0-<build-number>-VT-ISA6000-V.ovf
•ISA-V-VMWARE-ICS-25.1.0.0-<build-number>-VT-ISA4000-V.ovf
•NVRAM file - example: ISA-V-VMWARE-ICS-25.1.0.0-<build-number>-VT-file1.nvram
•VMDK file - example: ISA-V-VMWARE-ICS-25.1.0.0-<build-number>-VT-disk1.vmdk
3.Follow the wizard and configure the necessary details as per your requirement. Click Finish.
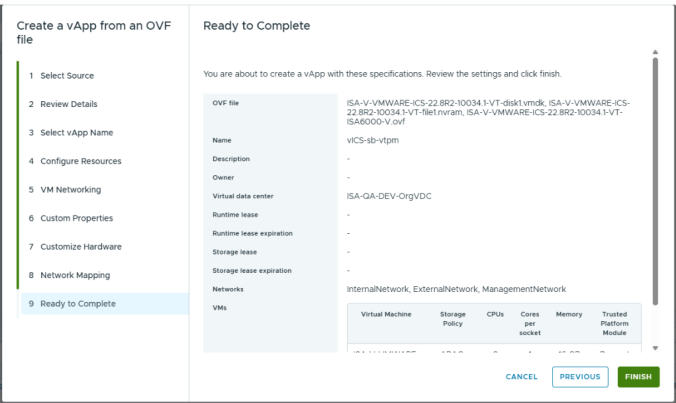
4.Click Start to power on vICS.
vTPM on ESXi 8.0.x
No additional steps are required to add vTPM when the ESXi itself is enabled with vTPM support.
Prerequisites
•vCenter license
•ESXi license
•Key Management Server on vCenter
•vTPM requirements as specified by Broadcom https://techdocs.broadcom.com/us/en/vmware-cis/aria/aria-automation/all/vtpm-overview.html
vTPM on ESXi 7.x
If ESXi 7.2 is used as hypervisor, then vTPM does not get attached automatically on deploying virtual ICS. Attach vTPM by selecting Settings > ADD NEW DEVICE > Trusted Platform Module.
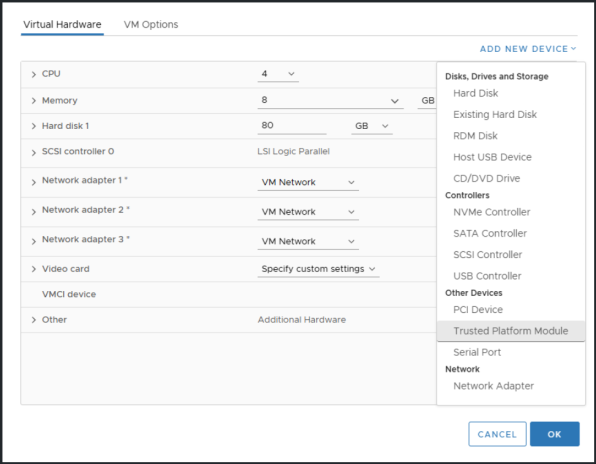
Due to VMware limitations, sometimes Trusted Platform Module is not visible in ADD NEW DEVICE option. In such scenario, follow the below steps.
1.Navigate to Settings > VM Options > General Options.
2.Change Guest OS Family from Other to Linux.
3.Change Guest OS Version from Other (64-bit) to TPM supported version like Ubuntu Linux (64-bit).
4.Click OK.
5.Attach vTPM by selecting Settings > ADD NEW DEVICE > Trusted Platform Module.
6.Revert Guest OS Family from Linux to Other.
7.Revert Guest OS Version from TPM supported version like Ubuntu Linux (64-bit) to Other (64-bit).
Limitations
•Removing vTPM from virtual ICS can make virtual ICS non recoverable.
•Cloning virtual ICS with replace TPM option is not supported.
•Exporting virtual ICS with vTPM to template is not supported by VMware.
25.1.1.0 Release
Deploying Ivanti Connect Secure Appliance on Hyper-V
Overview of ICS Hyper-V Enablement
Ivanti Security Appliance are now supported on Microsoft's Hyper-V hypervisor in addition to VMWare platform.
The following table contains data regarding the Number of cores to be allocated to each Hyper-V model:
|
Platform |
Cores Per VM |
RAM |
Disk Space |
|---|---|---|---|
|
ISA4000-V |
4 |
8 GB |
80 GB |
|
ISA6000-V |
8 |
16 GB |
80 GB |
|
ISA8000-V |
12 |
32 GB |
80 GB |
Limitations
•Hyper-V Deployment with secure boot is only qualified for ICS 25.1.1.0 release onwards.
•Upgrade from 22.X to 25.X as well as rollback from 25.1.1.0 to any older release is not supported.
•Only Fresh install is supported.
•The image supports only IDE disks and will support only the ‘Generation 2’ type of Virtual machine in Hyper-V Manager because secure-boot is only supported on Gen2 onwards.
•VM Cloning is no longer a valid scenario because for every VM we should store unique keys in TPM, hence we can’t use same TPM while cloning.
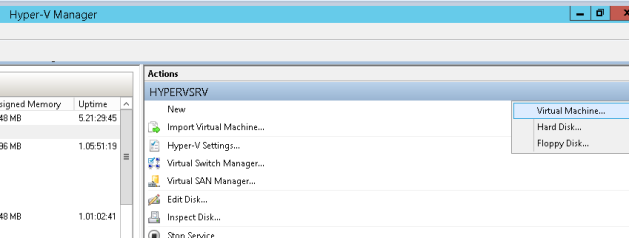
Deploying a Hyper-V ISA-V through the Hyper-V Manager
To deploy a Ivanti Security appliance through the Hyper-V Manager:
1.Copy the Hyper-V ISA-V Package to the Hyper-V Server.
2.Open Hyper-V Manager.
3.Deploy Hyper-V ISA-V.
4.On the Before you Begin screen, click Next.
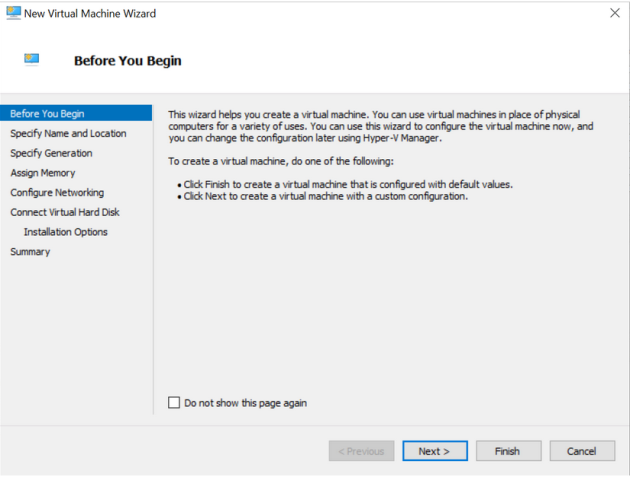
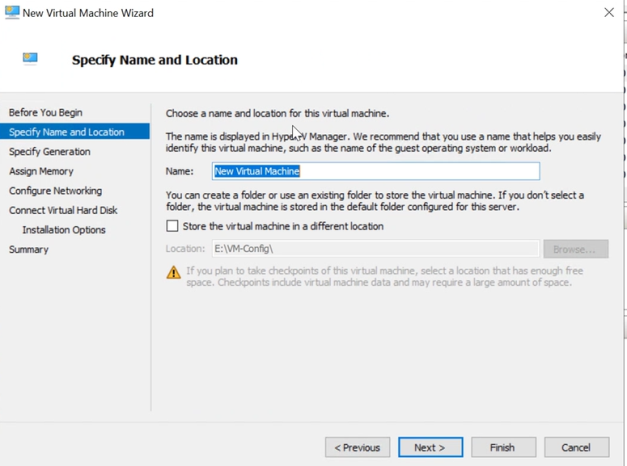
5.Enter Specify Name and Location and click Next.
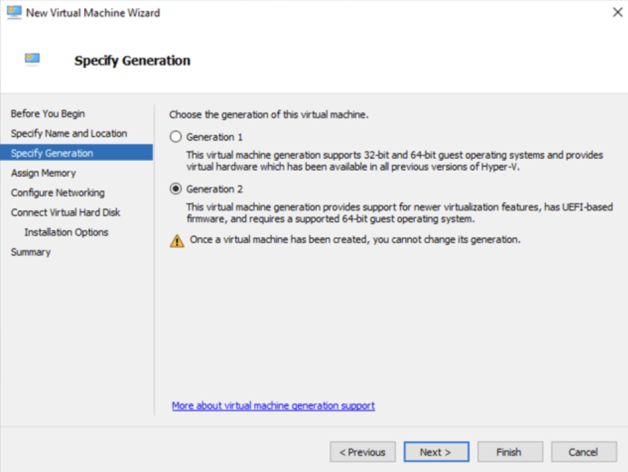
6.Select Generation 2 only as Hyper-V ISA-V does not support older Generation 1, and click Next.
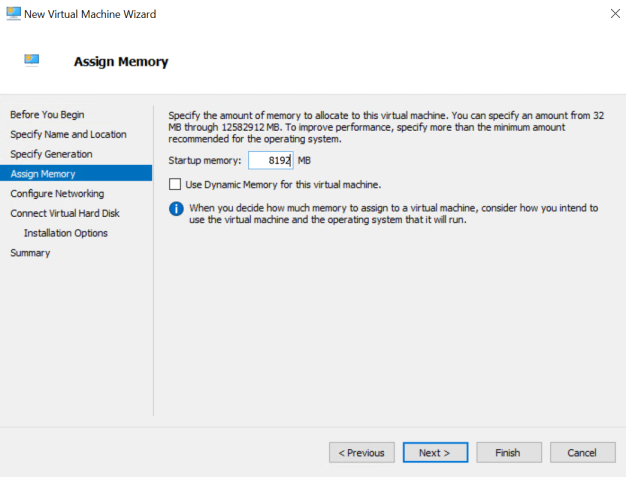
7.Now assign the appropriate memory. Enter 8192 MB for ISA-V, and click Next.
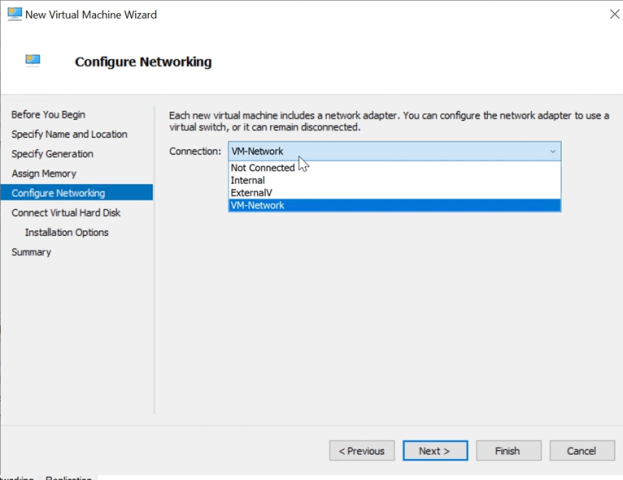
8.The Configure Networking page opens. Select a virtual switch to be used by the network adapter, and click Next.
9. The Connect Virtual Hard Disk page appears. Select the Use an existing virtual hard disk button and provide the location of the Hyper-V ISA-V package.vhdx (step 1).
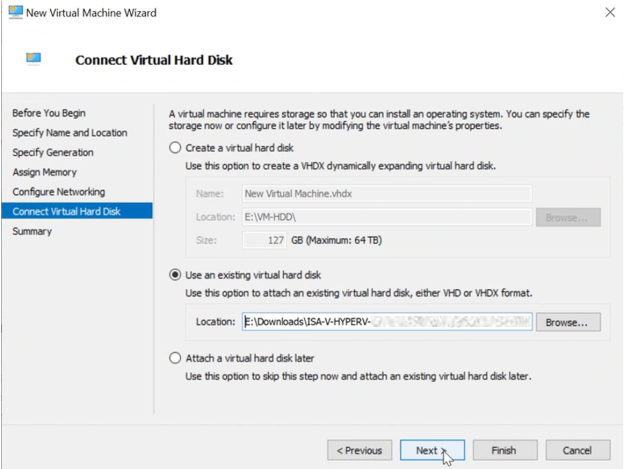
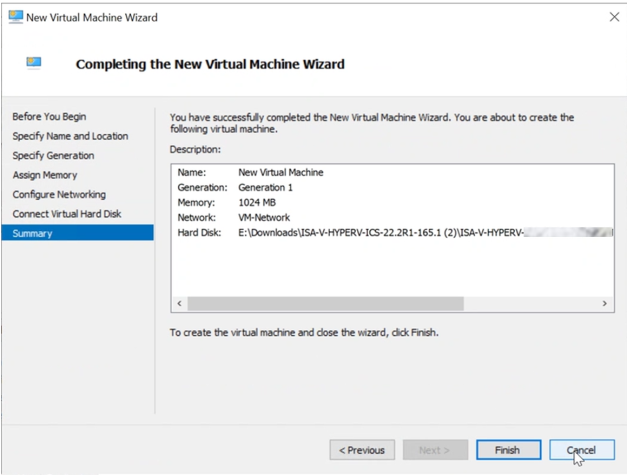
10. Click on Finish. Hyper-V Server creates an entry under Virtual Machines.
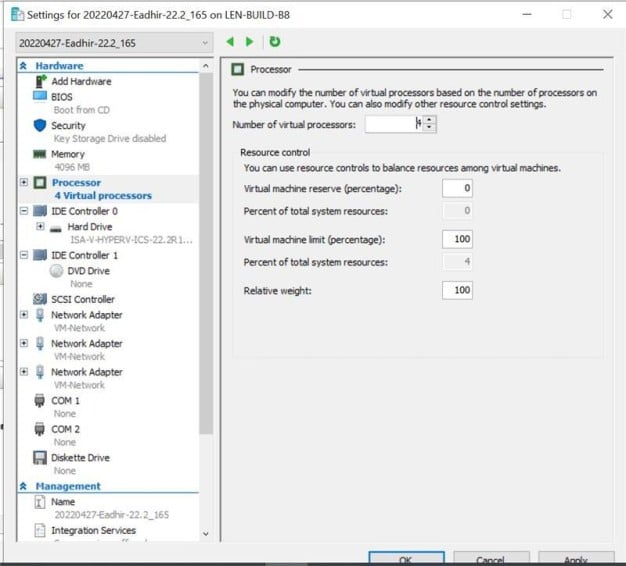
11. Now, add number on vCPUs and network adapter for External Port and Management Port.
a. Right click on the VM Name, and click on Settings.
b. Enter Number of virtual processors required.
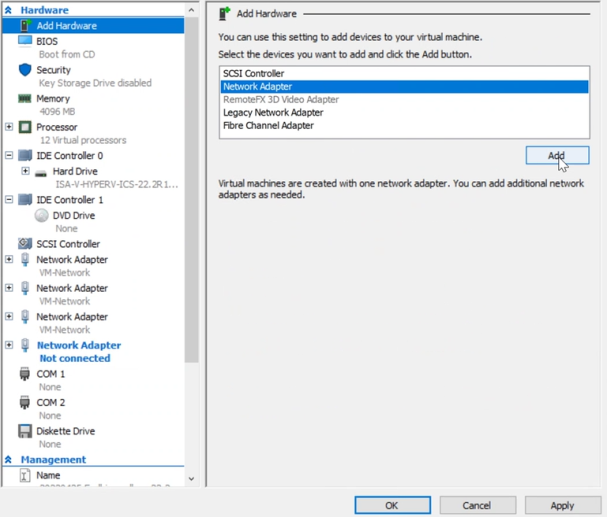
c. In the dialog box that opens, click on Add Hardware in the left pane.
d. On the right pane, select Network Adapter.
e. Click on Add.
It is important to add all the three network adapters to Hyper-V ISA-V before powering on the VM. Adding network adapters after powering-on the Hyper-V ISA-V may result in network connectivity issues. The following list indicates the order of virtual adapters:
1. Network Adapter: Internal
2. Network Adapter 2: External
3. Network Adapter 3: Management
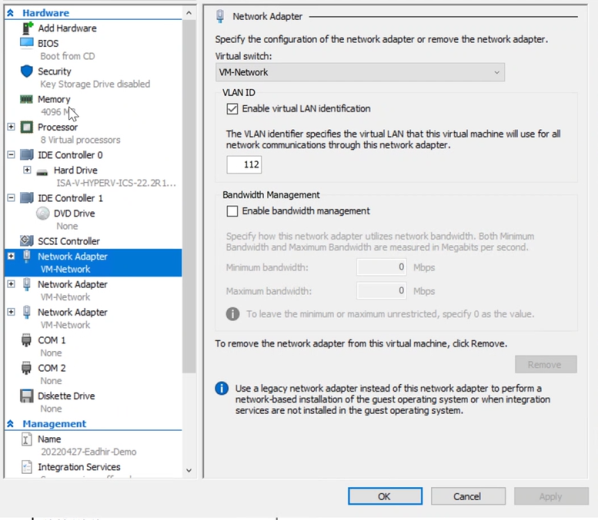
12. Select the virtual switch for External Port, and click on Apply.
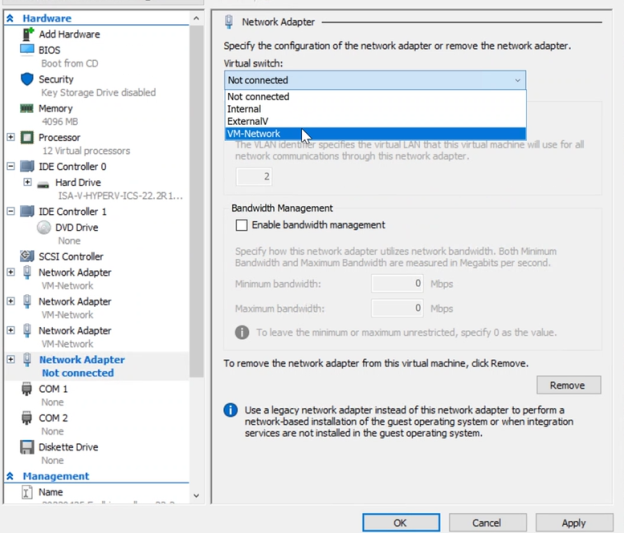
13. Now add network adapter for Management port.
a. Click on Add Hardware on the left pane. Select Network Adapter, click on Add.
b. Select the Virtual Switch for Management Port, and click on Apply.
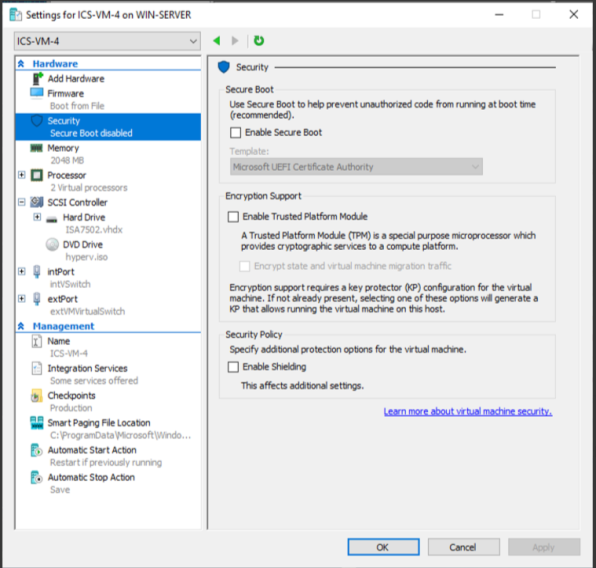
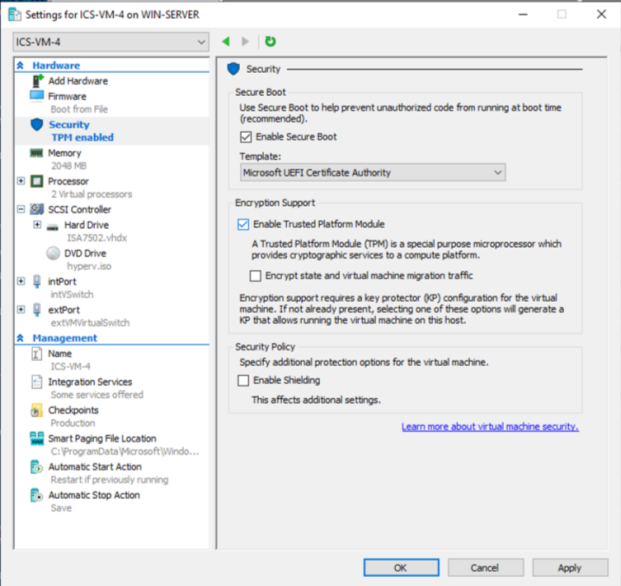
14. Before starting the virtual machine, go to Settings > Security.
a. Change the Template to Microsoft UEFI Certificate Authority.
b. Clear the Enable Secure Boot option to disable it before the first boot.
c. Clear the Enable Trusted Platform Module option to disable TPM for the first boot.
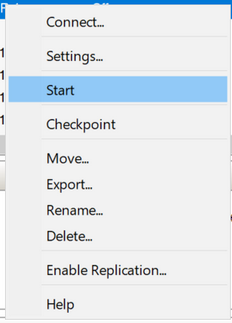
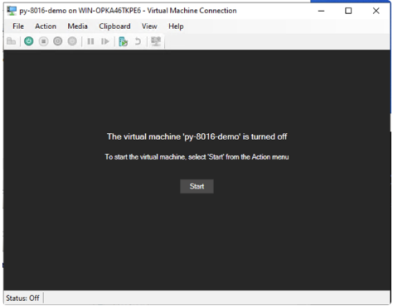
15. Select Start to power on the virtual machine.
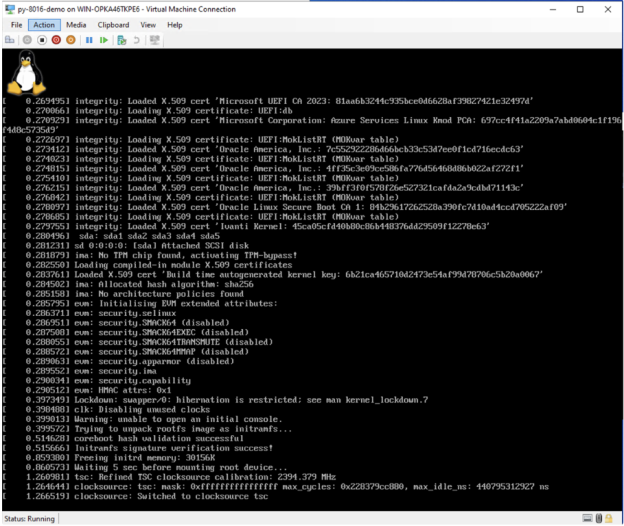
16. Virtual machine will boot, and it will automatically shut down when it detects Secure Boot is disabled. This step is very much needed, as it will install Ivanti Secure Boot certificate in this first boot. The following screenshot may or may not appear during the fast booting process and after the system is turned off.
17. Before starting the virtual machine again, go to Settings > Security.
a. Make sure the Template is Microsoft UEFI Certificate Authority.
b. Select the Enable Secure Boot option.
c. Select the Enable Trusted Platform Module option.
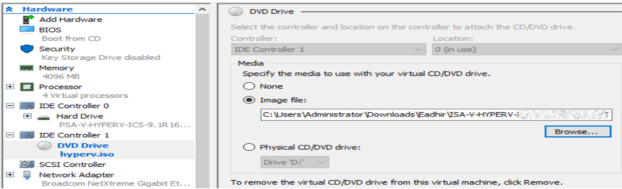
d. Optional step is to add a DVD drive with automatic initial configurations For details, see Deploying Connect Secure with Automatic Initial Configurations.
18. Select Start to power on the virtual machine.
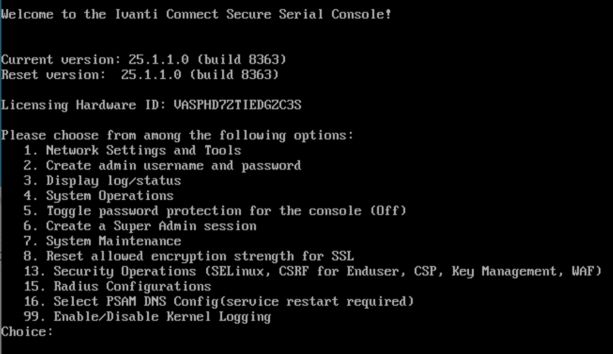
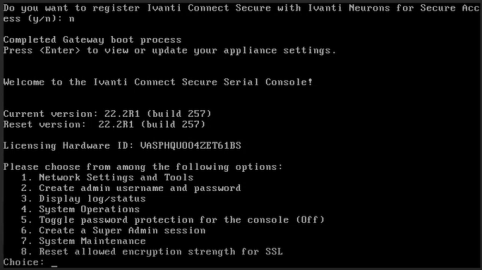
Once Deployment is successful, the deployed VM Console is shown.
Deploying Connect Secure with Automatic Initial Configurations
1.Download the Hyper-V package file and find the hyperv_template.xml file.
2.Customize the required fields like IP address/Subnet Mask/Default Gateway for internal, external, and management ports and then convert to .iso image (hyperv.iso) using the following command.
Command Sample: mkisofs -l -o hyperv.iso hyperv_template.xml.
3.Under DVD Drive, click Browse and upload the .iso file and then start the VM.
4.You can add DVD Drive when the virtual machine is switched off automatically after the first.
Note:
When deploying a Hyper-V image using a script (.ps1 file), it is essential to use the file name hyperv_template.xml with the mkisofs command. If you use any other file name, the deployment will not recognize hyperv.iso as a drive.
For example, the following commands will not work:
mkisofs -l -o hyperv.iso hyperv_template-AP.xml
mkisofs -l -o hyperv.iso hyperv_template-AP1.xml
or
with any other file name in place of hyperv_template.xml.
Always use the file name hyperv_template.xml with the mkisofs command:
mkisofs -l -o hyperv.iso hyperv_template.xml
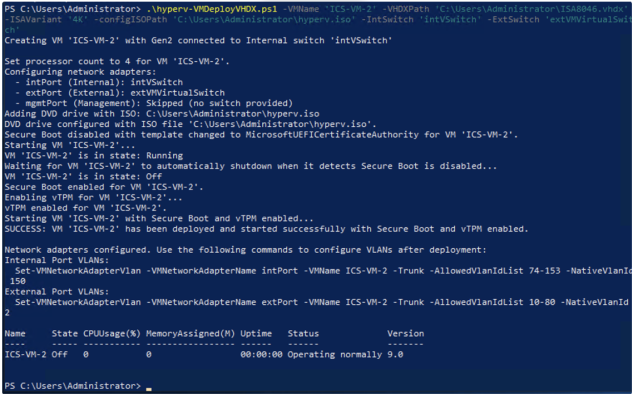
Deploying a Hyper-V ISA-V through Powershell cmdlets
To deploy a Hyper-V ISA-V through Powershell cmdlets:
•either run the powershell commands manually from powershell script "hyperv-VMDeployVHDX.ps1".
•or call the powershell script(Method1) with proper arguments to automate all the steps and directly get a running VM with secure boot enabled.
Launch Hyper-V ISA-V in an automated fashion with secure boot enabled.
1.Copy the Hyper-V ISA-V Package and hyperv-VMDeployVHDX.ps1 to the Hyper-V Server.
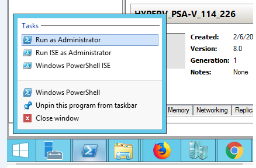
2.Open PowerShell as administrator.
3.PowerShell script takes the following inputs:
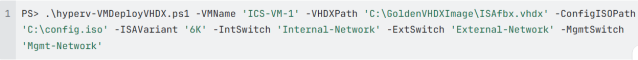
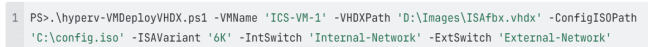
•VMName: Name of the VM to create (mandatory)
•VHDXPath: Path to the existing VHDX file (mandatory)
•ISAVariant: ISA variant determining VM resources - "4K", "6K", or "8K" (mandatory)
•4K: 8GB RAM, 4 vCPUs
•6K: 16GB RAM, 8 vCPUs
•8K: 32GB RAM, 12 vCPUs
•IntSwitch: Name of the Hyper-V virtual switch for Internal network adapter (mandatory)
•ExtSwitch: Name of the Hyper-V virtual switch for External network adapter (mandatory)
•MgmtSwitch: Name of the Hyper-V virtual switch for Management network adapter (optional)
•ConfigISOPath: Path to an ISO file to mount as a DVD drive for auto configuration (optional)
4.Keep the VMName, VHDXPath, ISAVariant, Internal Switch name, External Switch name ready.
5.Example deployment commands:
With all three network adapters:
With Internal and External adapters only:
Cloning of VM on Hyper-V
Cloning is no longer supported for Generation 2 VMs because of TPM (Trusted platform modules) limitations.
Increasing the Disk Size in Hyper-V
Fresh installation 80 GB disk space is available by default. You can modify or increase the disk size only once on fresh installation or upgrade of the ICS images, but not on rollback or factory reset images.
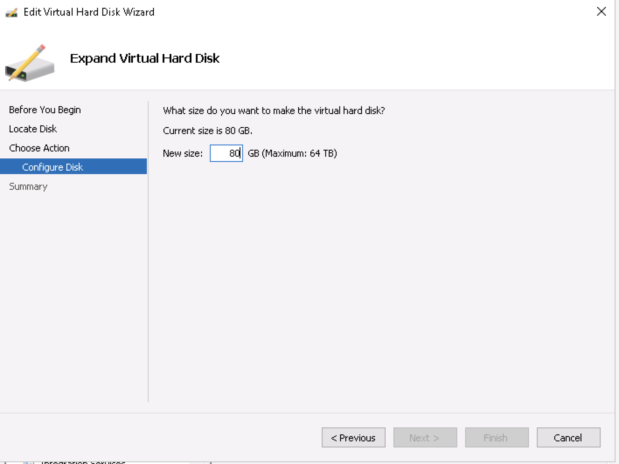
To increase the disk space:
1.Click IDE Controller > Hardware, click Edit.
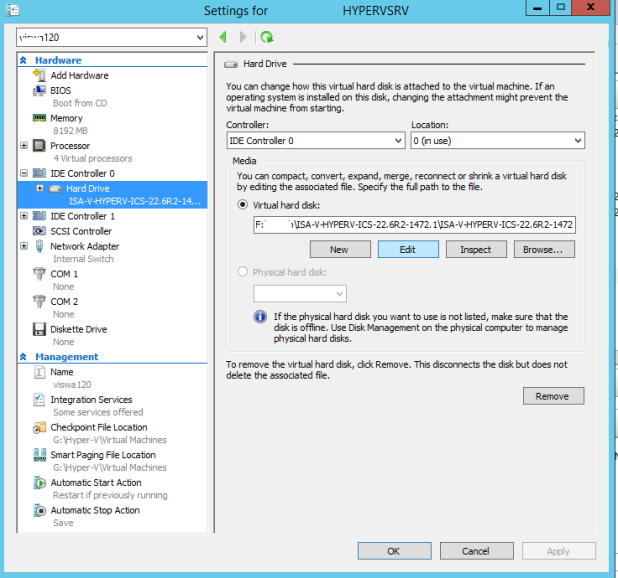
2.Select Expand and click Next>.
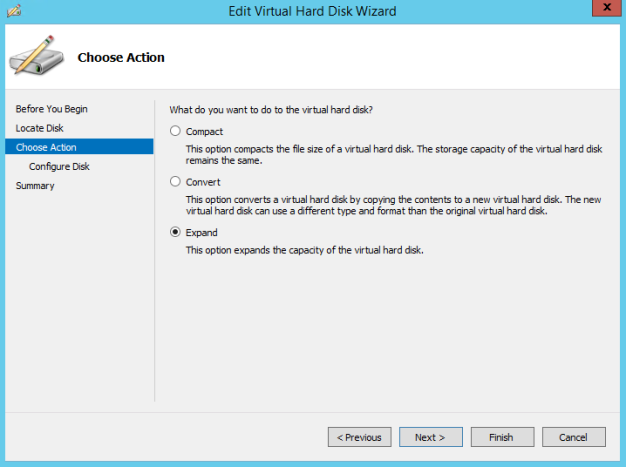
3.Change the disk size in GB and click Finish.
ICS Provisioning Parameters
Provisioning parameters are those parameters which are required during the deployment of a virtual appliance. ICS accepts the following parameters as provisioning parameters in the XML format.
|
<PropertySection> <Property oe:key="vaIPAddress" oe:value=""/> <Property oe:key="vaNetmask" oe:value=""/> <Property oe:key="vaGateway" oe:value=""/> <Property oe:key="vaDefaultVlan" oe:value=""/> <Property oe:key="vaExternalIPAddress" oe:value=""/> <Property oe:key="vaExternalNetmask" oe:value=""/> <Property oe:key="vaExternalGateway" oe:value=""/> <Property oe:key="vaExternalDefaultVlan" oe:value=""/> <Property oe:key="vaManagementIPAddress" oe:value=""/> <Property oe:key="vaManagementNetmask" oe:value=""/> <Property oe:key="vaManagementGateway" oe:value=""/> <Property oe:key="vaManagementDefaultVlan" oe:value=""/> <Property oe:key="vaPrimaryDNS" oe:value=""/> <Property oe:key="vaSecondaryDNS" oe:value=""/> <Property oe:key="vaWINSServer" oe:value="1.2.3.4"/> <Property oe:key="vaDNSDomain" oe:value="ics.company.com"/> <Property oe:key="vaAdminUsername" oe:value="admin"/> <Property oe:key="vaAdminPassword" oe:value="Password123$"/> <Property oe:key="vaCommonName" oe:value="ics-ext-port.company.com"/> <Property oe:key="vaOrganization" oe:value="Ivanti"/> <Property oe:key="vaRandomText" oe:value="randomtextrandomtextrandomtextrandomtext"/> <Property oe:key="vaAcceptLicenseAgreement" oe:value="y"/> <Property oe:key="vaEnableLicenseServer" oe:value="n"/> <Property oe:key="vaAdminEnableREST" oe:value=""/> <Property oe:key="vaAuthCodeLicense" oe:value=""/> <Property oe:key="vaConfigURL" oe:value="http://a.b.c.d/ics_config.xml"/> <Property oe:key="vaConfigServerCACertPEM" oe:value=""/> <Property oe:key="vaConfigData" oe:value=""/> <Property oe:key="vaInternalPortReconfigWithValueInVAppProperties" oe:value="1"/> <Property oe:key="vaManagementPortReconfigWithValueInVAppProperties" oe:value="1"/> <Property oe:key="vaExternalPortReconfigWithValueInVAppProperties" oe:value="1"/> </PropertySection> |
|
Parameter Name |
Type |
Description |
|---|---|---|
|
vaIPAddress |
IP address |
Internal interface IP |
|
vaNetmask |
IP address |
Internal interface subnet mask |
|
vaGateway |
IP address |
Internal interface IP gateway |
|
vaDefaultVlan |
integer |
VLAN number to assign to this interface |
|
vaExternalIPAddress |
IP address |
External interface IP |
|
vaExternalNetmask |
IP address |
External interface subnet mask |
|
vaExternalGateway |
IP address |
External interface IP gateway |
|
vaExternalDefaultVlan |
integer |
VLAN number to assign to this interface |
|
vaManagementIPAddress |
IP address |
Management interface IP |
|
vaManagementNetmask |
IP address |
Management interface subnet mask |
|
vaManagementGateway |
IP address |
Management interface IP gateway |
|
vaExternalDefaultVlan |
integer |
VLAN number to assign to this interface |
|
vaPrimaryDNS |
IP address |
Primary DNS IP |
|
vaSecondaryDNS |
IP address |
Secondary DNS IP |
|
vaWINSServer |
IP address |
Windows server IP |
|
vaDNSDomain |
string |
Windows domain name |
|
VaAdminUsername |
string |
Admin username |
|
vaAdminPassword |
string |
Admin password |
|
vaCommonName |
string |
Common name |
|
vaOrganization |
string |
Organization name |
|
vaRandomText |
string |
Random text to generate self-signed certificate |
|
vaAcceptLicenseAgreement |
character |
“y” to accept the license agreement |
|
vaEnableLicenseServer |
character |
“y” to enable it as VLS server. “n” to bring it up as a ICS node. |
|
vaAdminEnableREST |
character |
“y” to enable REST for administrator user |
|
vaAuthCodeLicense |
string |
Authentication code that needs to be obtained from Ivanti. |
|
vaConfigURL |
string URL |
Http based URL where XML based ICS configuration can be found. |
|
vaConfigServerCACertPEM |
string |
PEM format of CA certificate. |
|
vaConfigData |
string |
base64 encoded XML based ICS configuration. |
|
vaInternalPortReconfigWithValueIn VAppProperties |
integer |
The Internal port overwrite property. If set to 1, overwrites the virtual appliance’s internal port settings with the ones specified during deployment. Set this value as 1. |
|
vaManagementPortReconfigWithValueIn VAppProperties |
integer |
The Management port overwrite property. If set to 1, overwrites the management port-related parameters in the ICS with the ones defined here. Set this value as 1. |
|
vaExternalPortReconfigWithValueIn VAppProperties |
integer |
The External port overwrite property. If set to 1, overwrite the external port-related parameters in ICS/IPS with the ones defined here. Set this value as 1. |
v6 Parameters
| Parameter | Type | Description |
|---|---|---|
| vaNetworkStack | IPv4 or IPv6 address |
It indicates network address configured during deployment. v4 : IPv4 addresses are allowed to configured. v6 : IPv6 addresses are allowed to configured. Both: IPv4 and IPv6 addresses are allowed to configured. |
| vaIPv6Address | IPv6 address | Internal interface IPv6 address |
|
vaPrefix |
IPv6 address |
Internal interface IPv6 prefix length. |
|
vaIPv6Gateway |
IPv6 address |
Internal interface IPv6 gateway address. |
|
vaManagementIPv6Address |
IPv6 address |
Management interface IPv6 address |
|
vaManagementPrefix |
IPv6 address |
Management interface IPv6 prefix length. |
|
vaManagementIPv6Gateway |
IPv6 address |
Management interface IPv6 gateway address. |
|
vaExternalIPv6Address |
IPv6 address |
External interface IPv6 address |
|
vaExternalPrefix |
IPv6 address |
External interface IPv6 prefix length. |
|
vaExternalIPv6Gateway |
IPv6 address |
External interface IPv6 gateway address. |
ICS supports zero touch provisioning. This feature can detect and assign DHCP networking settings automatically at the ICS boot up. The following ICS parameters should be set to null in order to fetch the networking configuration automatically from the DHCP server.
|
vaIPAddress |
vaExternalIPAddress |
vaManagementIPAddress |
vaNetworkStack |
vaManagementIPv6Address |
vaExternalPrefix |
|
vaNetmask |
vaExternalNetmask |
vaManagementNetmask |
vaIPv6Address |
vaManagementPrefix |
vaExternalIPv6Gateway |
|
vaGateway |
vaExternalGateway |
vaManagementGateway |
vaPrefix |
vaManagementIPv6Gateway |
|
|
vaPrimaryDNS |
vaSecondaryDNS |
vaDNSDomain |
vaIPv6Gateway |
vaExternalIPv6Address |
Deploying Ivanti Connect Secure Appliance on OpenStack KVM
Overview
Assumptions
The basic understanding of deployment models of ICS on a data center and basic experience in using OpenStack is needed for the better understanding of this guide.
Prerequisites and System Requirements
The OpenStack Fabric has various components such as Controller, Compute, Identity, Image, Networking etc. that are separately installed. For details about these services,
To deploy the ICS VA on OpenStack, you need the following:
•Access to the OpenStack Dashboard
•An OpenStack account with deployment rights
•ICS KVM Image
•(Optional) ICS licenses
•(Optional) ICS configuration in xml format, required only for zero touch deployment
•Desired flavors of ISA-V (ISA4000-V, ISA6000-V, ISA8000-V).
•Desired ICS KVM image on OpenStack
•Internal, External and Management networks on OpenStack
•Security Groups for Internal, External and Management Ports
•Compute nodes should support vTPM.
•Compute nodes should support secure boot for virtual machines.
•Compute nodes should have Ivanti released OVMF firmware binary (OVMF_CODE.secboot.ivanti.fd) and NVRAM file (OVMF_VARS_4M.ivanti.fd) for secure boot.
Deploying ICS on OpenStack Using Horizon Dashboard
Before proceeding with the ICS deployment, ensure that the necessary prerequisites are set up. For details, see Appendix A: Setting Up Prerequisites
To deploy ICS on OpenStack, do the following:
1.Log in to the OpenStack.
2.In the OpenStack dashboard displayed, select Project > Compute > Imagesand then create an image. For more information, see Create Image.
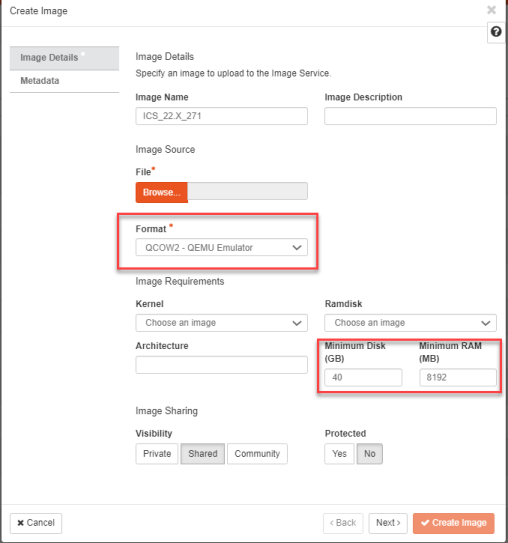
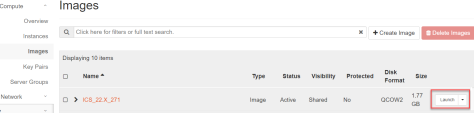
3.From the list of images displayed, click on Launch corresponding to the ICS KVM image you want to launch.
Image selected must have following attributes for secure boot and vTPM supported ICS image.
•hw_disk_bus='virtio'
•hw_firmware_type='uefi'
•hw_machine_type='q35'
•hw_tpm_model='tpm-crb'
•hw_tpm_version='2.0'
•os_secure_boot='required'
The following figure depicts the ICS VA Images screen:
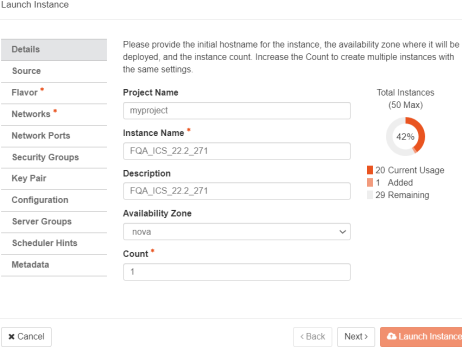
4.In the Launch Instance Details window, fill the following and then click Next.
•Instance Name: Specify host name of the ICS Virtual instance
•Description: Enter a brief description on this instance
•Availability Zone: Select the zone where the instance is deployed
•Count: Number of VM instances
The following figure depicts the Device Details screen:
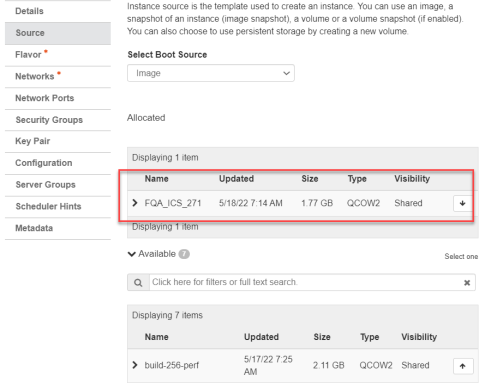
5.The Source window displays the details of the image used. Click Next.
The following figure depicts the Source Selection screen.
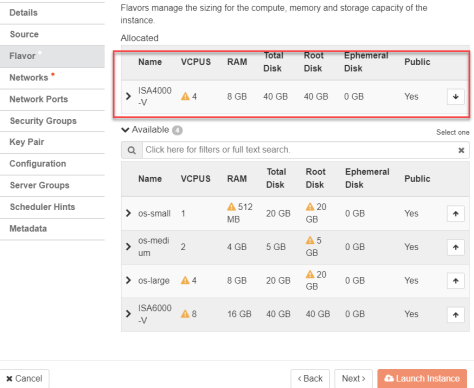
6.In the Flavor window, select required flavors of ISA-V (ISA4000-V, ISA6000-V, ISA8000-V) from the list based on the memory and storage capacity of the instance. Click Next.
The following figure depicts the Flavor Selection screen.
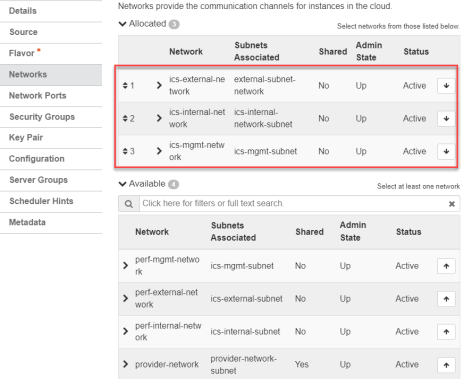
7.In the Networks window, select networks from the list that specifies internal, external and management subnets. ICS supports VM with 2-NICs model and 3-NICs model for deployment. Click Next.
The following figure depicts the Network Selection screen:
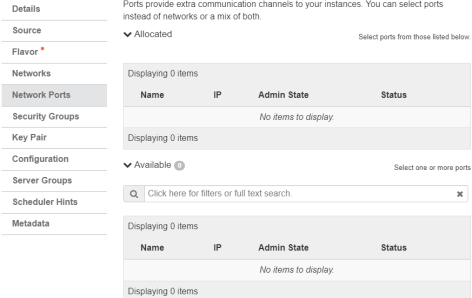
8.(Optional) Network Ports window. Click Next.
The following figure depicts the Network Ports Selection screen:
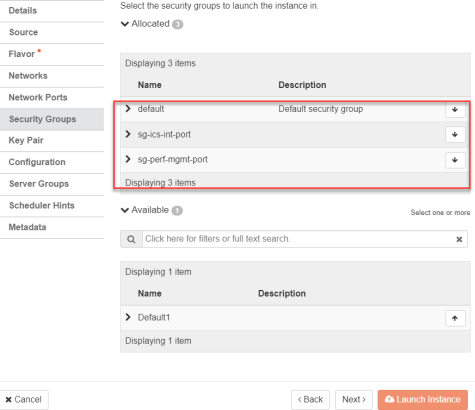
9.In the Security Groups window, select the required network security groups from the list for internal, external and management ports. Click Next. To create new security groups, refer Creating Required Security Groups for Internal, External and Management Ports
The following figure depicts the Security Groups Selection screen:
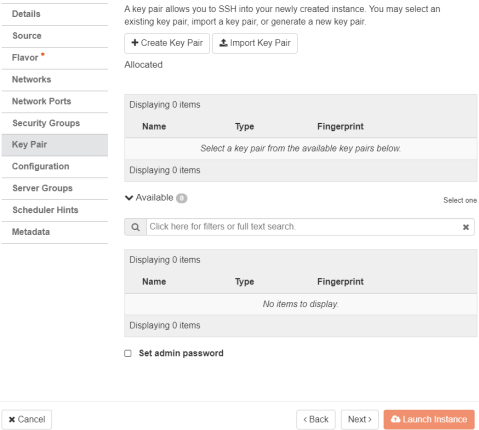
10.Key Pair is not used. Click Next.
The following figure depicts the Key Pair screen:
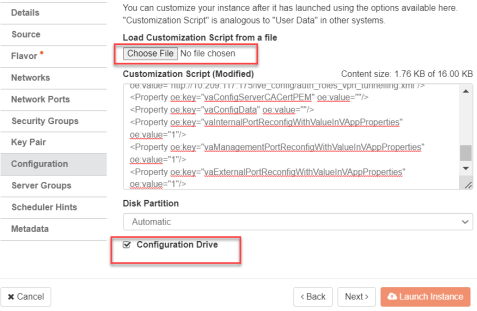
11.Click Choose File and import the file that contains the provisioning parameters in XML format OR paste the Customization script and do the required modifications. Select the Configuration Drive check box. The template file is available for ISA-V instance and click Launch Instance upon selecting the Configuration Drive option.
The following figure depicts the Configuration Script screen:
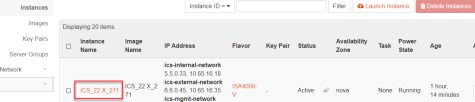
12.The Instances window lists all the ICS VA instances. The blue bar in the Task column shows the status of creation of the instance. This will take a few minutes.
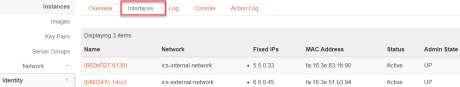
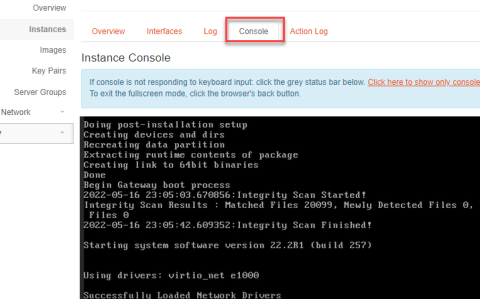
Open the created ICS VA instance by clicking on the Instance Name link.
The Interface tab shows the networks that are created.
The Log tab shows the log details of the device that is created.
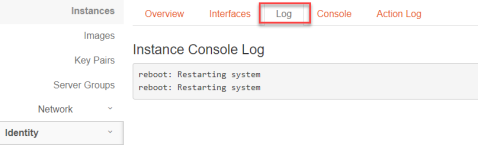
The console tab provides the virtual console to view the device coming up.
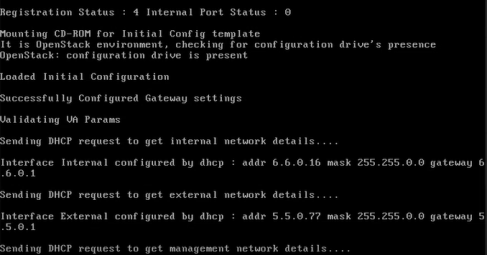
13.Next, the Internal and External interfaces are configured by DHCP (Zero touch configuration).
The following figure depicts the Internal and External Interfaces Configuration by DHCP screen:
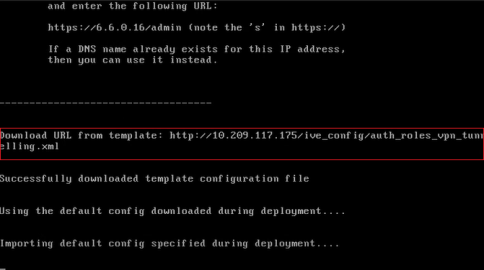
14.The Config URL is downloaded for initial configuration.
The following figure depicts the Download Config URL from Template screen:
ICS Provisioning Parameters
Provisioning parameters are those parameters which are required during the deployment of a virtual appliance. ICS accepts the following parameters as provisioning parameters in the XML format.
|
<PropertySection> <Property oe:key="vaIPAddress" oe:value=""/> <Property oe:key="vaNetmask" oe:value=""/> <Property oe:key="vaGateway" oe:value=""/> <Property oe:key="vaDefaultVlan" oe:value=""/> <Property oe:key="vaExternalIPAddress" oe:value=""/> <Property oe:key="vaExternalNetmask" oe:value=""/> <Property oe:key="vaExternalGateway" oe:value=""/> <Property oe:key="vaExternalDefaultVlan" oe:value=""/> <Property oe:key="vaManagementIPAddress" oe:value=""/> <Property oe:key="vaManagementNetmask" oe:value=""/> <Property oe:key="vaManagementGateway" oe:value=""/> <Property oe:key="vaManagementDefaultVlan" oe:value=""/> <Property oe:key="vaPrimaryDNS" oe:value=""/> <Property oe:key="vaSecondaryDNS" oe:value=""/> <Property oe:key="vaWINSServer" oe:value="1.2.3.4"/> <Property oe:key="vaDNSDomain" oe:value="ics.company.com"/> <Property oe:key="vaAdminUsername" oe:value="admindb"/> <Property oe:key="vaAdminPassword" oe:value="Password123$"/> <Property oe:key="vaCommonName" oe:value="ics-ext-port.company.com"/> <Property oe:key="vaOrganization" oe:value="Ivanti"/> <Property oe:key="vaRandomText" oe:value="randomtextrandomtextrandomtextrandomtext"/> <Property oe:key="vaAcceptLicenseAgreement" oe:value="y"/> <Property oe:key="vaEnableLicenseServer" oe:value="n"/> <Property oe:key="vaAdminEnableREST" oe:value=""/> <Property oe:key="vaAuthCodeLicense" oe:value=""/> <Property oe:key="vaConfigURL" oe:value="http://a.b.c.d/ics_config.xml"/> <Property oe:key="vaConfigServerCACertPEM" oe:value=""/> <Property oe:key="vaConfigData" oe:value=""/> <Property oe:key="vaInternalPortReconfigWithValueInVAppProperties" oe:value="1"/> <Property oe:key="vaManagementPortReconfigWithValueInVAppProperties" oe:value="1"/> <Property oe:key="vaExternalPortReconfigWithValueInVAppProperties" oe:value="1"/> </PropertySection> |
|
Parameter Name |
Type |
Description |
|---|---|---|
|
vaIPAddress |
IP address |
Internal interface IP |
|
vaNetmask |
IP address |
Internal interface subnet mask |
|
vaGateway |
IP address |
Internal interface IP gateway |
|
vaDefaultVlan |
integer |
VLAN number to assign to this interface |
|
vaExternalIPAddress |
IP address |
External interface IP |
|
vaExternalNetmask |
IP address |
External interface subnet mask |
|
vaExternalGateway |
IP address |
External interface IP gateway |
|
vaExternalDefaultVlan |
Integer |
VLAN number to assign to this interface. |
|
vaManagementIPAddress |
IP address |
Management interface IP |
|
vaManagementNetmask |
IP address |
Management interface subnet mask |
|
vaManagementGateway |
IP address |
Management interface IP gateway |
|
vaManagementDefaultVlan |
Integer |
VLAN number to assign to this interface |
|
vaPrimaryDNS |
IP address |
Primary DNS IP |
|
vaSecondaryDNS |
IP address |
Secondary DNS IP |
|
vaWINSServer |
IP address |
Windows server IP |
|
vaDNSDomain |
string |
Windows domain name |
|
VaAdminUsername |
string |
Admin username |
|
vaAdminPassword |
string |
Admin password |
|
vaCommonName |
string |
Common name |
|
vaOrganization |
string |
Organization name |
|
vaRandomText |
string |
Random text to generate self-signed certificate |
|
vaAcceptLicenseAgreement |
character |
“y” to accept the license agreement |
|
vaEnableLicenseServer |
character |
“y” to enable it as VLS server. “n” to bring it up as a ICS node. |
|
vaAdminEnableREST |
character |
“y” to enable REST for administrator user |
|
vaAuthCodeLicense |
string |
Authentication code that needs to be obtained from Ivanti. |
|
vaConfigURL |
String URL |
Http based URL where XML based ICS configuration can be found. |
|
vaConfigServerCACertPEM |
string |
PEM format of CA certificate. |
|
vaConfigData |
string |
base64 encoded XML based ICS configuration. |
|
vaInternalPortReconfigWithValueIn |
integer |
The Internal port overwrite property. If set to 1, overwrite the virtual appliance’s internal port settings with the ones specified during deployment. Set this value as 1. |
|
vaManagementPortReconfigWithValueIn |
integer |
The Management port overwrite property. If set to 1, overwrite the management port-related parameters in the ICS with the ones defined here. Set this value as 1. |
|
vaExternalPortReconfigWithValueIn |
integer |
The External port overwrite property. If set to 1, overwrite the external port-related parameters in ICS/IPS with the ones defined here. Set this value as 1. |
IICS supports zero touch provisioning. This feature can detect and assign DHCP networking settings automatically at the ICS boot up. The following ICS parameters should be set to null in order to fetch the networking configuration automatically from the DHCP server.
|
•vaIPAddress |
•vaExternalIPAddress |
•vaManagementIPAddress |
|
•vaNetmask |
•vaExternalNetmask |
•vaManagementNetmask |
|
•vaGateway |
•vaExternalGateway |
•vaManagementGateway |
|
•vaPrimaryDNS |
•vaSecondaryDNS |
•vaDNSDomain |
Leased IP from DHCP server should be valid for a long time as ICS does not request for DHCP renewals.
vTPM and Secure Boot Support on OpenStack
This section provides guidance on enabling virtual Trusted Platform Module (vTPM) and Secure Boot features for Ivanti Connect Secure virtual appliances deployed on OpenStack. Implementing vTPM and Secure Boot improves data protection by supporting encrypted secrets and secure firmware validation.
vTPM Overview
This section describes the process and prerequisites for enabling vTPM (virtual Trusted Platform Module) and Secure Boot for Ivanti Connect Secure virtual appliances on OpenStack. Enabling these security features ensures that sensitive data such as encryption keys are stored securely and validates the integrity of the virtual appliance firmware during boot. The guidance provided here will help you configure a compliant and robust OpenStack environment for secure ICS deployments.
Enabling vTPM
To enable vTPM (virtual Trusted Platform Module) support on OpenStack for Ivanti Connect Secure virtual appliances, ensure the following requirements and steps are met on each compute host:
Prerequisites:
•An OpenStack key manager service, such as Barbican, must be deployed and configured on the controller node. This service is required to store the secrets used for encrypting virtual device files at rest.
•The user deploying the ICS virtual appliance must have the creator role in the corresponding OpenStack project to allow Barbican to create ICS secrets.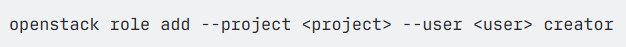
•The swtpm binary and associated libraries must be installed on each compute node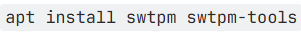
•/etc/nova/nova-compute.conf should have following configuration to support virtual TPM.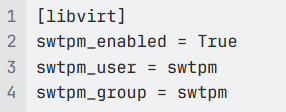
•Set the  config option to 'True' in
config option to 'True' in of compute node. This will enable support for both TPM version 1.2 and 2.0.
of compute node. This will enable support for both TPM version 1.2 and 2.0.
With the above requirements satisfied, verify vTPM support by inspecting the traits on the compute node’s resource provider: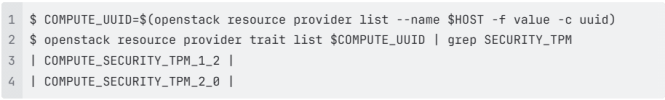
Enabling Secure Boot
To enable UEFI secure boot on OpenStack, follow steps as per OpenStack documentation.
You can verify UEFI Secure Boot support by inspecting the traits on the compute node’s resource provider: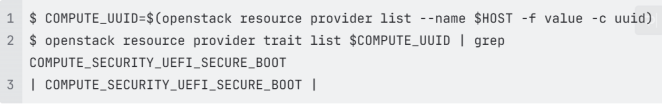
In order to boot Ivanti virtual ICS in secure boot mode, perform following steps.
1.Extract Ivanti released OVMF firmware and VARS file from KVM ZIP artifact.
2.Ivanti released OVMF firmware and VARS file needs to be copied to /usr/share/OVMF directory of compute nodes.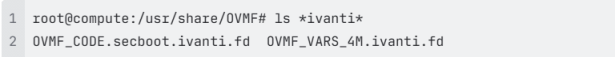
Ivanti released VARS file has secure boot certificate required to boot virtual ICS in secure boot mode.
3.Copy 40-edk2-x86_64-secure-enrolled.json to 10-edk2-x86_64-secure-enrolled.json and modify 10-edk2-x86_64-secure-enrolled.json file in /usr/share/qemu/firmware directory to use Ivanti’s secure boot OVMF files.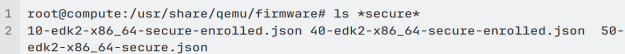
b. Following contents need to be changed to use Ivanti’s released OVMF files.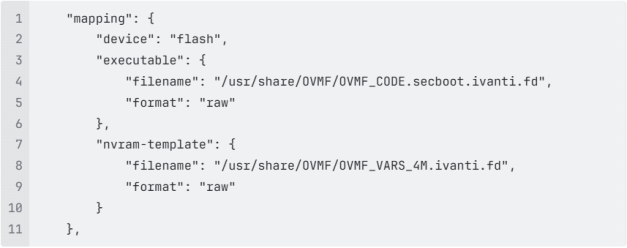
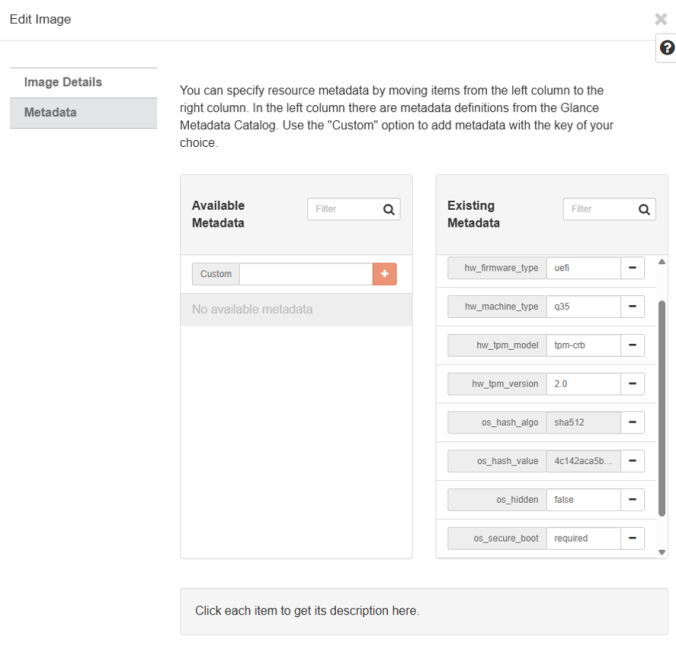
4.Restart libvirtd and nova-compute on compute nodes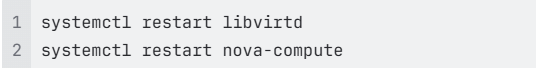
Setting Virtual ICS Image Attributes
Following attributes need to be set to enable secure boot for virtual ICS.
1.Select virtual ICS image.
2.Edit image.
3.Select Metadata section.
4.Update following attributes.
•hw_disk_bus='virtio'
•hw_firmware_type='uefi'
•hw_machine_type='q35'
•hw_tpm_model='tpm-crb'
•hw_tpm_version='2.0'
•os_secure_boot='required'
If above listed attributes are enabled then virtual ICS will boot with secure boot enabled and vTPM attached.
OpenStack Limitations
1.Snapshot and Restore functionality does not work in OpenStack for ICS with vTPM.
a. Source
b. Spawning from an image created by snapshotting a VM with a vTPM will result in a fresh, empty vTPM
2.Operations like “hard reboot” or “shut off/start” may fail to start ICS with vTPM. Refer Bug link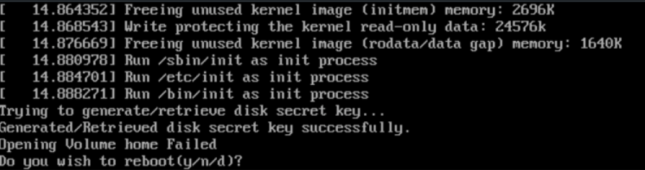
a. Above error may be seen.
b. OpenStack fix link is needed to solve this issue.
c. Alternately, following workaround can be added in your OpenStack environment.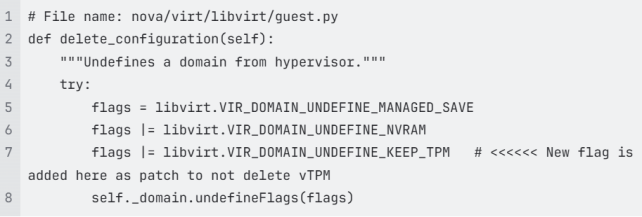
Deploying Ivanti Connect Secure Appliance on Azure
Prerequisites and System Requirements on Azure
To deploy the Ivanti Connect Secure Virtual Appliance on Azure custom deployment, you need the following:
•A Microsoft Azure account
•Access to the Microsoft Azure portal (https://portal.azure.com)
•Ivanti Connect Secure Virtual Appliance Image (.vhd file).
•Azure Resource Manager template (ARM template)
Supported Platform Systems
This section helps you in choosing the instance types that should be deployed with Ivanti Connect Secure for Azure.
•ISA4000-V
•ISA6000-V
•ISA8000-V
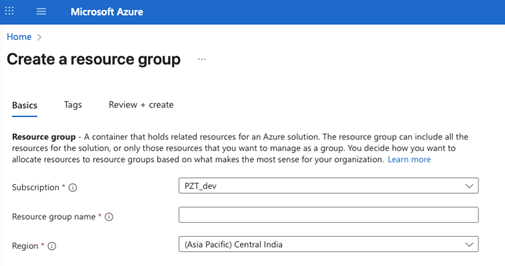
Create a Resource Group
To create a Resource group, do the following:
1.Log into Azure portal.
2.Navigate to Resource Groups. Enter unique resource group name.
3.Click Review + create to finalize and create resource group.
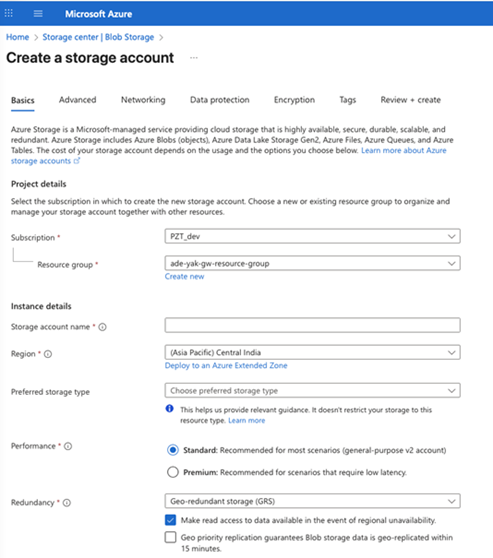
Create a Storage Account
To create a Storage Account, do the following:
1.Log in to the Azure portal.
2.Click New and create a Storage Account.
3.Choose the resource group you have already created.
4.Enter a unique name for the storage account name.
5.Click Review + create to create storage account.
Upload ICS Appliance Image to Storage Account
To upload Ivanti Connect Secure Virtual Appliance image to Stroage Account, do the following:
1.Download the Azure ICS image file (ics-azure-isa-v-<releaseno>-<buildno>-package.zip) which is in the zipped format.
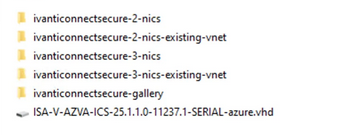
•The package contains the following components:
•ISA-V-AZVA-ICS-<releaseno>-<buildno>-SERIAL-azure.vhd: VHD disk image for Ivanti Connect Secure VA, to upload to Azure
•ivanticonnectsecure-gallery: Publish VHD as Shared Image Gallery image
•ivanticonnectsecure-2-nics: Deploy ICS with 2 NICs (new VNet)
•ivanticonnectsecure-2-nics-existing-vnet: Deploy ICS with 2 NICs (existing VNet)
•ivanticonnectsecure-3-nics: Deploy ICS with 3 NICs (new VNet)
•ivanticonnectsecure-3-nics-existing-vnet: Deploy ICS with 3 NICs (existing VNet)
•azuredeploy.json: ARM deployment templates
2.Unzip the file and look for the Ivanti Connect Secure Virtual Appliance vhd image.
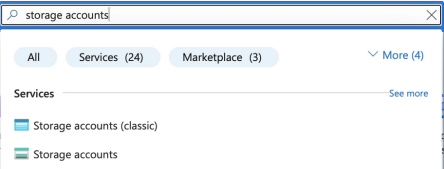
3.Log in to the Azure portal.
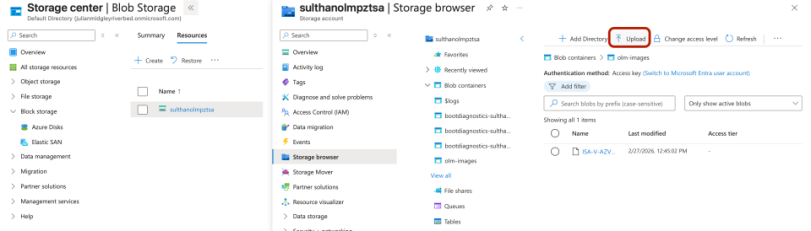
4.In the Azure portal, search for storage accounts and select the Storage Account you have created.
5.To upload ICS Virtual Appliance image. Select Storage browser in the left menu.
6.Click Blob containers and select your target container.
7.Click Upload at the top, browse for your file and hit the final Upload button and upload.
8.Inside your Storage Account, go to the left menu and click Storage browser under Data storage.
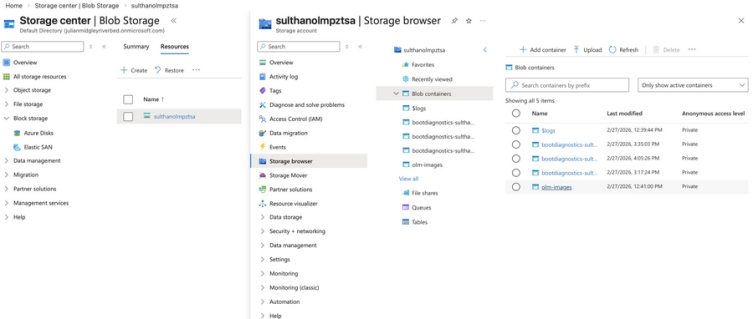
9.Under Blob containers, find and select your container (e.g., az-images) where the VHD file is uploaded.
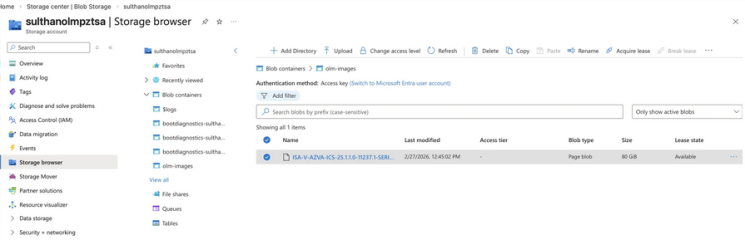
10.Inside the container, find your VHD file (e.g., ISA-V-AZVA-ICS-<releaseno>-<buildno>-SERIAL-azure.vhd). Click on the file to open its properties.
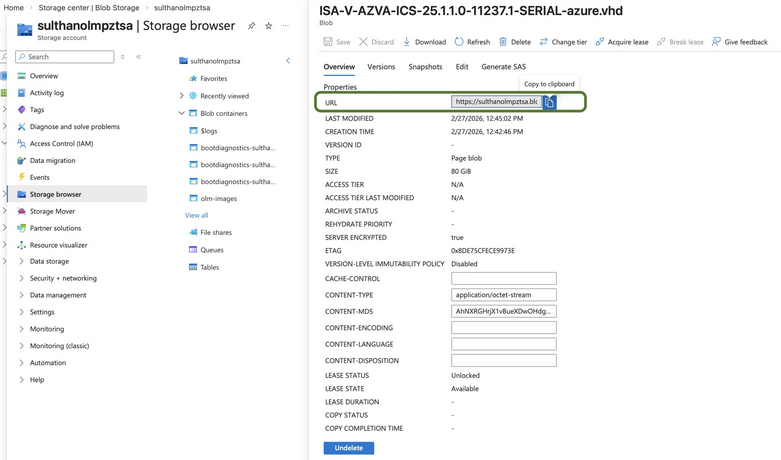
11.In the Overview or properties pane, look for the field named URL. Click the copy icon next to it.
The URL will be in this format: https://<name>.blob.core.windows.net/az-images/ISA-V-AZVA-ICS-<releaseno>-<buildno>-SERIAL-azure.vhd. This URL is need to deploy the Azure Gallery
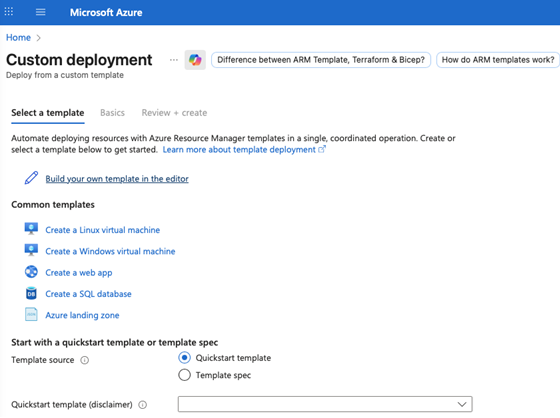
Upload Azure Resource Manager Template to Gallery
1.Navigate to Custom Deployment.
2.Select Build your template in the editor.
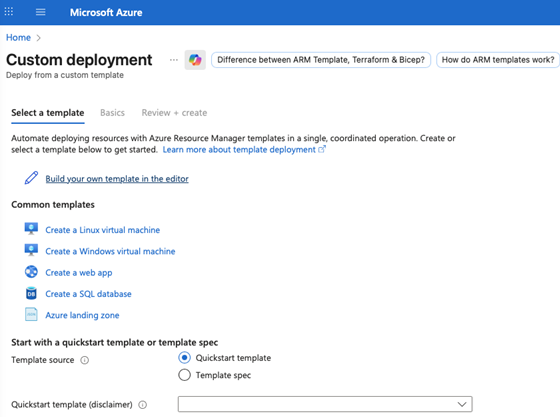
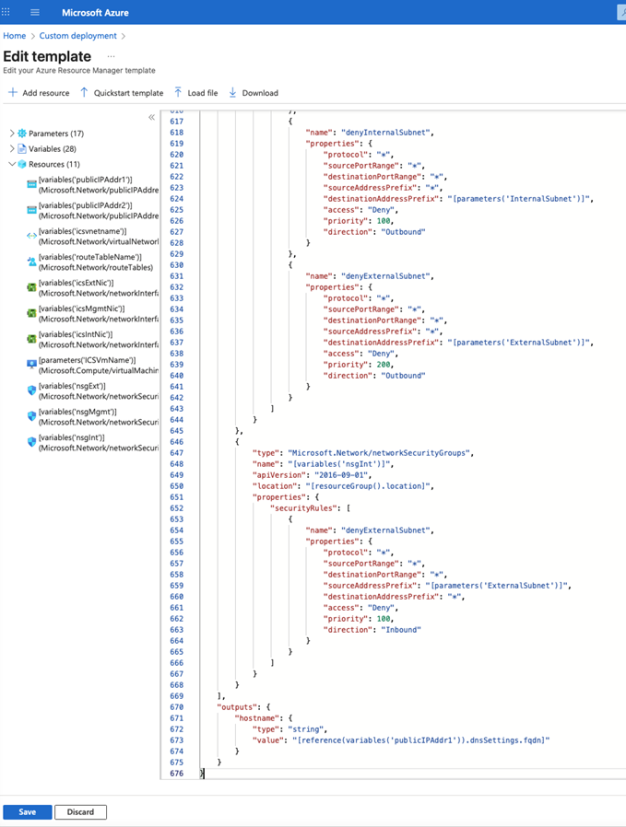
3.Locate the Azure Gallery deployment template file in folder (ivanticonnectsecure-gallery/azure-gallery-deploy.json).
4.Open this file and Copy its content and paste the into the designated field.
5.Click Save to apply the template.
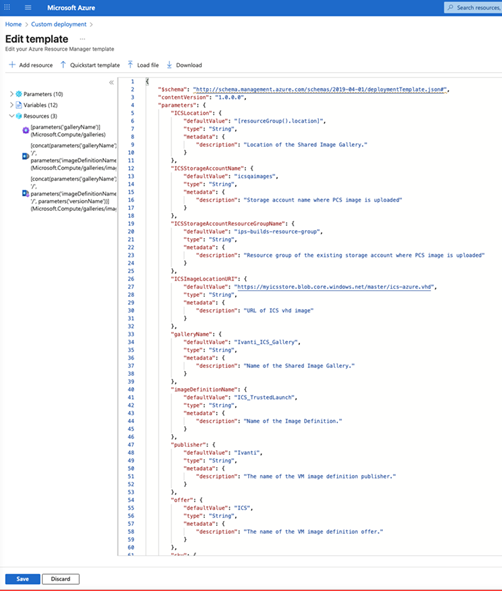
6.Fill or modify the following parameters:
•Region (mandatory): place
•ICS Location: Location of the Shared Image Gallery (Where Azrure Gallery image is deployed)
•Resource Group (mandatory): A resource group is a collection of resources that share the same lifecycle, permissions, and policies, where ICS is getting deployed
•ICS Storage Account Name: Storage account name where ICS image is uploaded
•ICS Storage Account Resource Group Name: Resource group of the existing storage account where ICS image is uploaded
•ICS Image Location URI: The is the URL to the location where ICS Azure vhd image is stored
•Gallery Name: The name of the Shared Image Gallery (this value is from Azure Gallery image)
•Image Definition Name: The name of the Image Definition (this value is from Azure Gallery image)
•Publisher: The name of the VM image definition publisher
•Offer: The name of the VM image definition offer
•SKU: The name of the VM image definition SKU
•Version Name: The VM image version name in semantic version pattern. The allowed characters are digit and period. For example: 0.0.1, 15.35.0. (this value is from Azure Gallery image)
|
Resource Type |
Allowed Characters |
Disallowed Characters |
Length |
Start/End |
Rule Example |
|---|---|---|---|---|---|
| Gallery Name | Letters (A-Z, a-z), digits (0-9), underscores (_), periods (.) | Dashes (-), spaces, other special characters | 1–80 chars | Cannot start/end with _ or . | Ivanti_ICS.Gallery |
| Image Definition | Letters, digits, underscores (_), periods (.), hyphens (-) | Name Spaces, other special characters | 1–80 chars | None | ICS-Trusted_Launch.25 |
| Image Version Name | Digits (0-9), periods (.) | Letters, hyphens, other characters | 1–80 chars | Must follow X.Y.Z format | 25.1.1 |
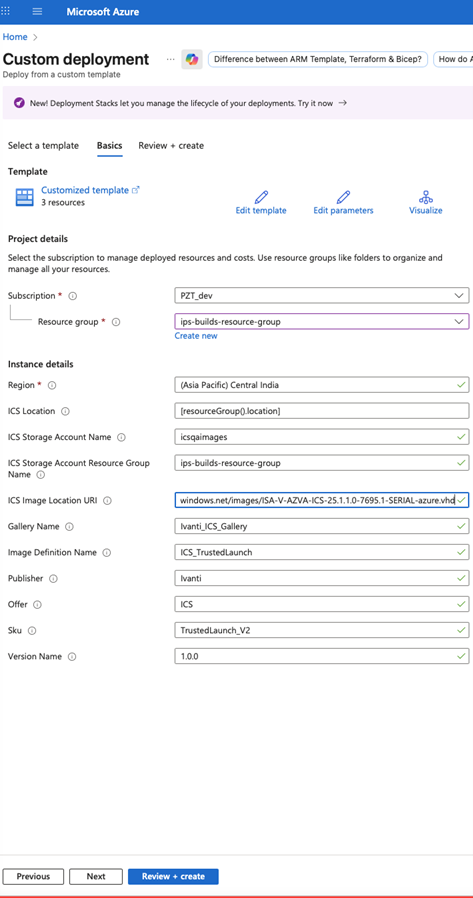
1.Click Review+ create to review your selections.
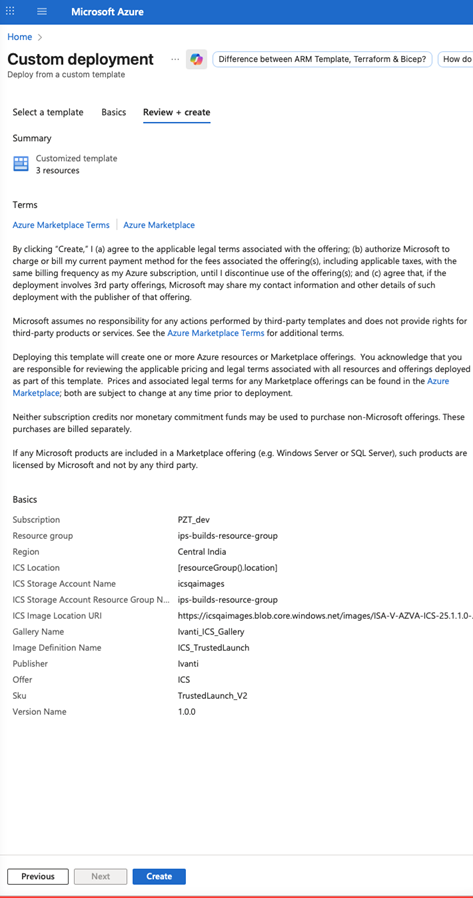
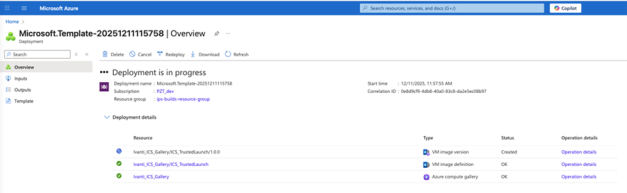
2.Click Create. Deployment will take 10 to 15 Minutes.
After a successful deployment, the Azure Gallery image for ICS will be ready for deploying the ICS virtual appliance.
ICS Virtual Machine Deployment
1.Navigate to Custom Deployment.
2.Select Build your own template in the editor.
3.Download the Azure deployment template 2-NIC or 3-NIC from "Azure-template" folder (ivanticonnectsecure-3-nics/azuredeploy.json) to get azuredeploy.json.
ISA4000-V supports only 2-NIC deployment. ISA6000-V and ISA8000-V support 2-NIC and 3-NIC deployments.
|
Standard Model |
vCPU |
RAM(GiB) |
Disk Space |
NICs |
|---|---|---|---|---|
| ISA4000-V (Standard_D4s_v6) | 4 | 16 GB | 80 GB | 2 |
| ISA4000-V (Standard_D4ds_v6) | 4 | 16 GB | 80 GB | 2 |
| ISA6000-V (Standard_D8s_v6) | 8 | 32 GB | 80 GB | 3 |
|
ISA6000-V (Standard_D8ds_v6) |
8 | 32 GB | 80 GB | 3 |
|
ISA8000-V (Standard_D16ds_v6) |
16 |
64 GB |
80 GB |
3 |
|
ISA4000-V (Standard_F4as_v6) |
4 |
16 GB |
80 GB |
2 |
|
ISA6000-V (Standard_F8as_v6) |
8 | 32 GB | 80 GB | 3 |
|
ISA8000-V (Standard_F16as_v6) |
16 |
64 GB |
80 GB |
3 |
4.Copy and paste the azuredeploy.json into the designated field.
5.Edit Virtual Machine Standards - variables section "variables": ["VirtualMachineSize": "Standard_D8ds_v6",]
6.Click Save to apply the template.
You can modify the following parameters in the VM Template to suit your requirements:
•Gallery name, Image Definition name, and Image Version number
•Network Details
7.Fill or modify the following parameters:
•ICS Storage Account Name: Storage account name where ICS image is uploaded
•ICS Storage Account Resource Group Name: Resource group of the existing storage account where ICS image is uploaded
•Gallery Name: The name of the Shared Image Gallery (This value is from Azure gallery image created)
•Image Definition Name: The name of the Image Definition (This value is from Azure gallery image created)
•Version Name: The VM image version name in semantic version pattern. The allowed characters are digit and period. For example: 0.0.1, 15.35.0 (This value is from Azure gallery image created)
•ICS VM Name: This is the name given to ICS Virtual Appliance.
•ICS Admin User: Ivanti Connect Secure Admin User, value must be 2-30 characters long.
•ICS Admin Password: Ivanti Connect Secure Admin Password, value must be 12-128 characters long and no special characters.
•SSH Public Key: This is an RSA public key that is used to access Ivanti Connect Secure via SSH.
•ICS Config: This section contains provisioning parameters that are required during the deployment of a Virtual Appliance. An XML-based configuration file can be present in another Virtual Machine in Azure cloud or in the corporate network which is accessible for Ivanti Connect Secure through site-to-site VPN between Azure and the corporate data center.
•Key pair name: The new ssh key pair name.
•DNS Label Prefix Ext: This is the prefix for External Interface DNS label.
•DNS Label Prefix Mgmt: This is the prefix for Management Interface DNS label.
In case of two NIC deployment, the management port would not be auto-populated and admin has to provide details for internal port manually.
•VNet Address Space: This is a Virtual Network address space
•Internal Subnet: Subnet from which Ivanti Connect Secure Internal Interface needs to lease IP.
•External Subnet: Subnet from which Ivanti Connect Secure External Interface needs to lease IP.
•Management Subnet: Subnet from which Ivanti Connect Secure Management Interface needs to lease IP.
•Tunnel Subnet: Subnet which will be configured as Tunnel IP pool in Ivanti Connect Secure VPN profile.
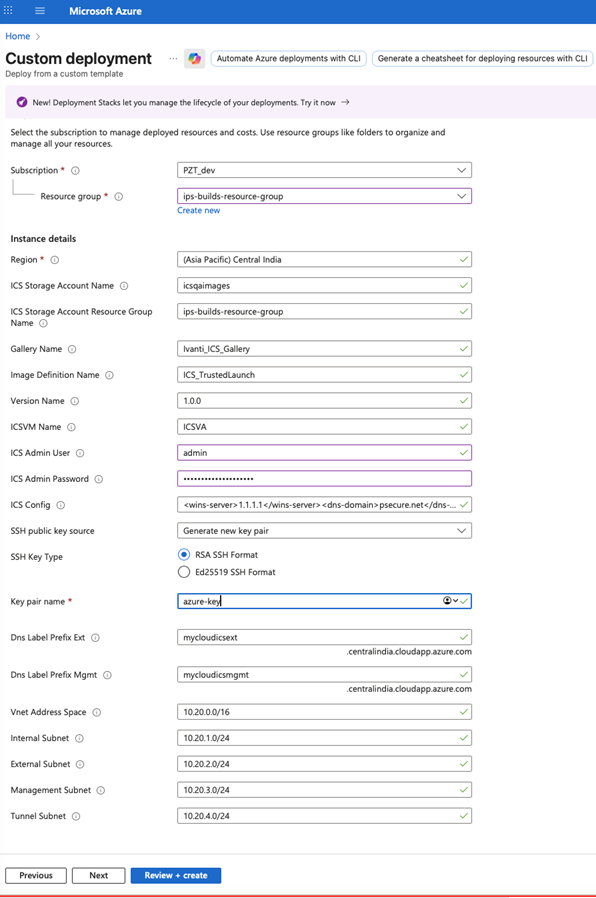
8.Click Review + create to review your selections.
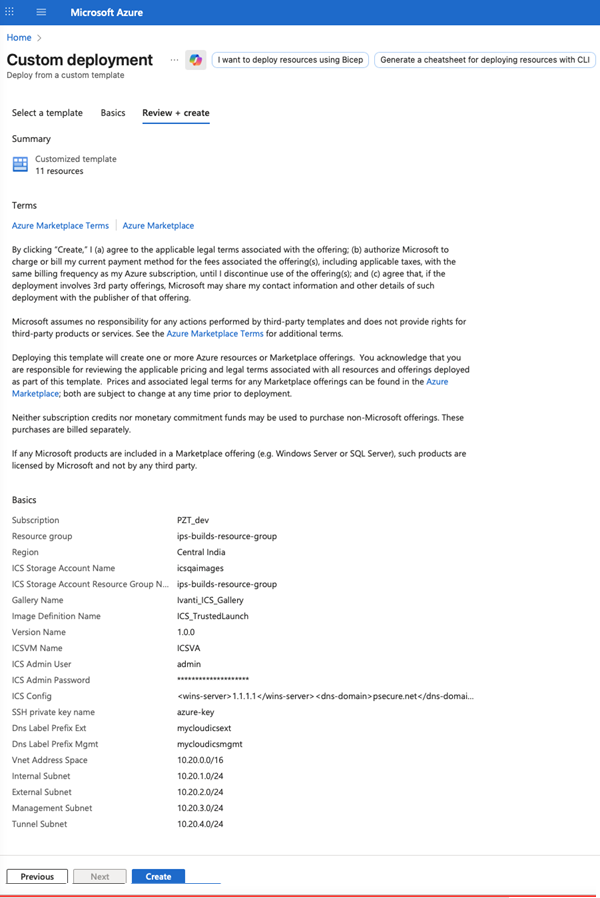
9.Click Create. A prompt will appear for generating new key pairs
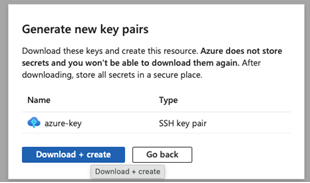
10.Click "Download + Create" to download the PEM key and begin deploying the virtual appliance (VA).
This action will create all required network resources, routes, and deploy the VA.
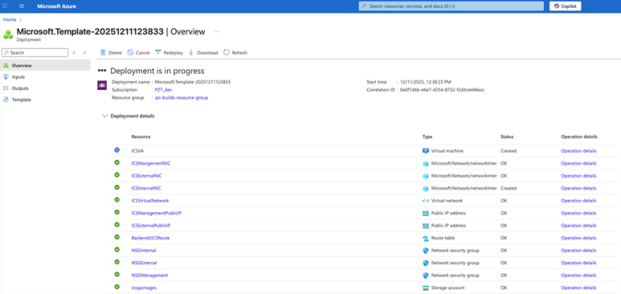
11. Once the virtual appliance (VA) status shows as "Created," the VA will appear in the list of Virtual Machines.
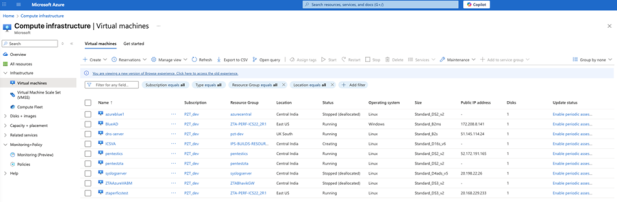
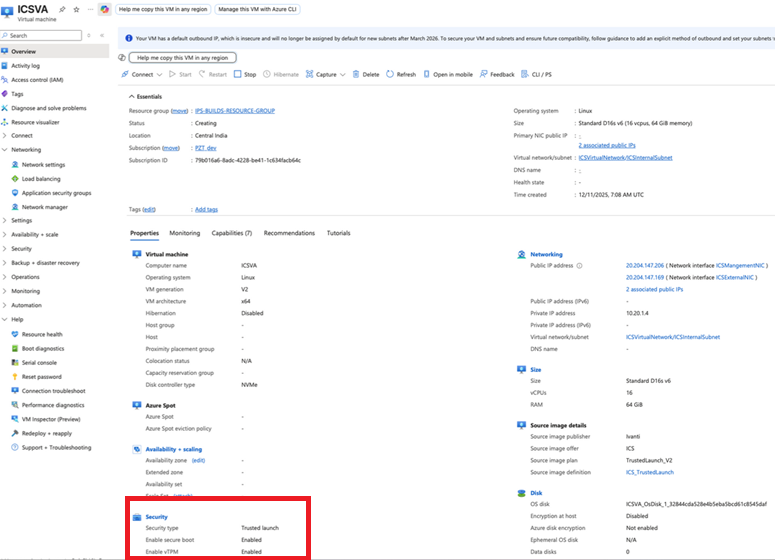
The new ICS virtual appliance will boot with the following features enabled:
•Secure Boot
•vTPM (virtual Trusted Platform Module)
•Disk controller type set to NVME
Security Best Practices
•Ensure BIOS/UEFI is enabled with Administrative password for every ISA Hardware Appliance. This ensures only authorized Admins can enter BIOS/UEFI settings.
•Ensure Toggle password protection for the console is ON for every appliance console access to prevent unauthorized access to Admin console.
•Ensure Secure Boot/vTPM features are always in Enabled state for BIOS/UEFI and VM settings.