Configuring IPS with MDM Servers
Configuring an Authentication Protocol Set
The authentication protocol set associated with the sign-in page must include the EAP method selected in the MDM Wi-Fi profile. The predefined authentication protocol set named 802.1x can be used as-is because it includes all the EAP methods currently configurable on MDMs.
To configure the authentication protocol set:
- Select Signing In > Authentication Protocols to display the configuration page.
- Click New Authentication Protocol or select the predefined 802.1x set. If anything other than MAC address is used as a device identifier then you must use cert auth and the protocol set has to be used for cert auth.
- Click Save.
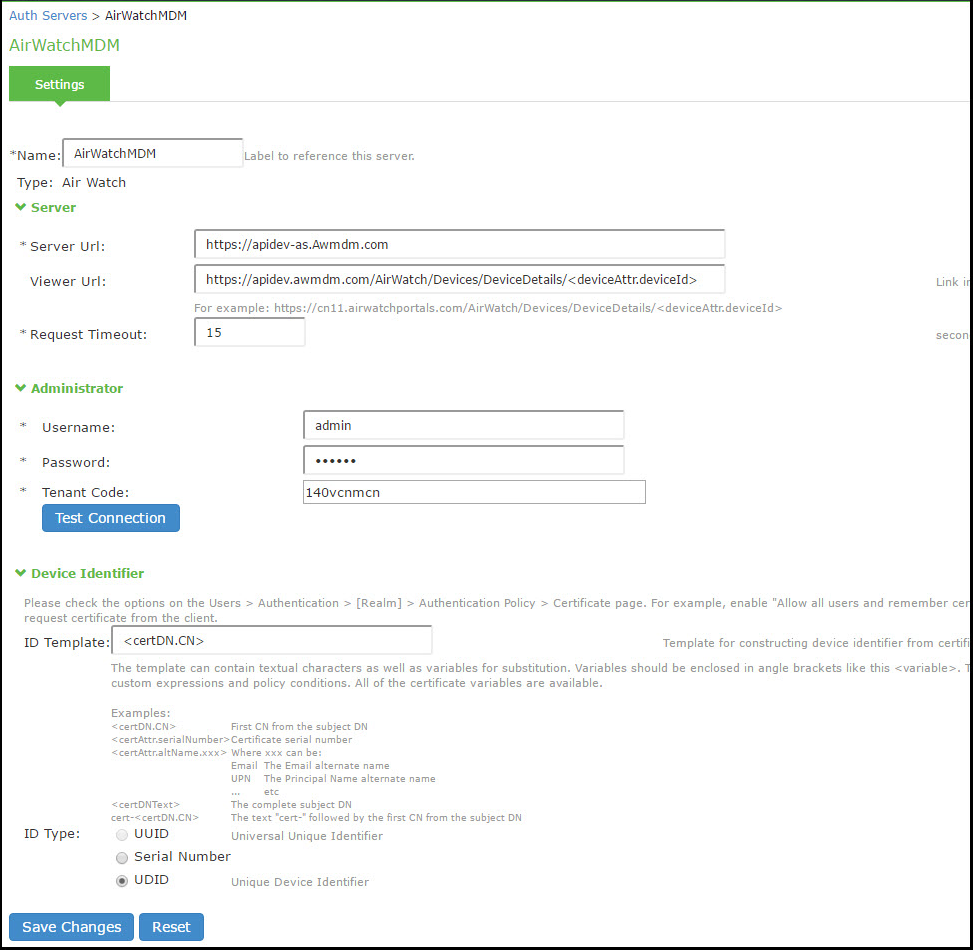
Configuring the MDM Authentication Server
The MDM authentication server configuration is used by IPS to communicate with the MDM. In the device access management framework, the MDM server is used as the device authorization server.
To configure the authentication server:
- Select Authentication > Auth Servers to navigate to the authentication server configuration pages.
- Select MDM Server and click New Server to display the configuration page.
- Complete the configuration as described in Table below.
- Save the configuration.
|
Settings |
Guidelines |
|---|---|
|
Name |
Specify a name for the configuration. |
|
Type |
Select the MDM server. |
|
Port Selection |
Choose the communicating interface/network for each auth server independently. This enables you to communicate using Internal, external, or management interface. |
|
Server |
|
|
Server Url |
Specify the URL for your AirWatch server. This is the URL AirWatch has instructed you to use to access its RESTful Web API (also called a RESTful Web service). The URL for the AirWatch MDM server used in this example has the following form: https://m.mobileiron.net/pulsesecuretest You must configure your firewalls to allow communication between these two nodes over port 443. |
|
Viewer Url |
Specify the URL for the AirWatch report viewer. This URL is used for links from the Active Users page to the AirWatch report viewer. The URL for the AirWatch MDM viewer for this example has the following form: https://apidev.awmdm.com/AirWatch/Devices/DeviceDetails/<deviceAttr.deviceId https://m.mobileiron.net/pulsesecuretest/admin/admin.html#smartphones:all |
|
Request Timeout |
Specify a timeout period (0-60 seconds) for queries to the MDM server. The default is 15 seconds. Calibrate this value based on your observations on how long a query to the MDM server takes over your network. If your network experiences latency when querying the MDM cloud service, increase the timeout to account for the latency. The system queries the MDM when a user attempts to sign in. If a timeout occurs, role mapping proceeds without attributes. |
|
Administrator |
|
|
Username |
Specify the username for an account that has privileges to access the MDM RESTful Web API. |
|
Password |
Specify the corresponding password. |
|
Tenant Code |
Copy and paste the AirWatch API tenant code. |
|
Device Identifier |
|
|
Device identity |
Select an option on whether to require that the MDM certificate is presented by the endpoint when signing in: •Require — Require that the device certificate pushed to client devices during enrollment be used at sign-in. If this option is selected, and the client device does not have a certificate, authorization fails. Use this option when you require endpoints to adhere to your certificate security requirements. •Use Certificate if present — Use the certificate to derive the device ID if the certificate is presented at sign-in, but do not reject authentication if the certificate is not present. You can use this option in conjunction with a role mapping rule and a remediation VLAN to identify devices that have not perfected MDM enrollment. •Always Use MAC address — In some cases, the MDM certificate might be configured without a device identifier. When the endpoint uses an 802.1x framework to authenticate, IPS can obtain the MAC address from the RADIUS return attribute callingStationID. The system can then use the MAC address as the device identifier. |
|
ID Template |
Construct a template to derive the device identifier from the certificate attributes. The template can contain textual characters as well as variables for substitution. The variables are the same as those used in role mapping custom expressions and policy conditions. Enclose variables in angle brackets like this <variable>. For example, suppose the certificate DN is: CN=<EnrollmentUser>, serialNumber=<DeviceUid>, o=Company. With this configuration, the certificate could identify both the user and the device. In this example, the device ID template is <certDN.serialNumber>. |
|
ID Type |
Select the device identifier type that matches the selection in the MDM certificate configuration: •UUID— The device universal unique identifier. This is the key device identifier supported by MobileIron MDM. •Serial Number—The device serial number. •UDID—The device unique device identifier. This is supported by the AirWatch MDM.
|
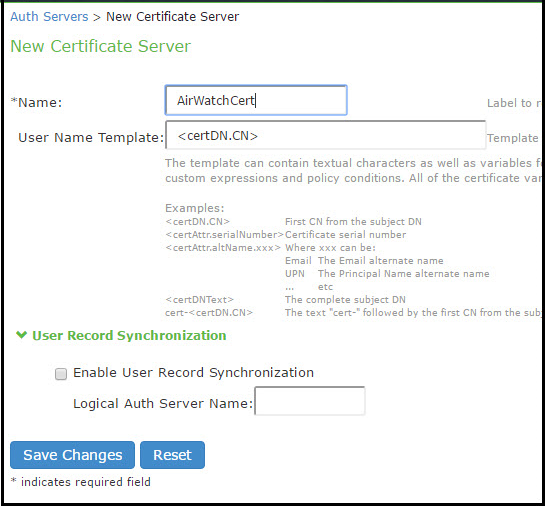
Configuring the Certificate Server
The certificate server configuration enables device users to authenticate using the certificate pushed to the device by the MDM. The certificates are used for user authentication, and the users do not have to enter user credentials.
To configure authentication with the certificate server:
- Select Authentication > Auth. Servers.
- Select Certificate Server and click New Server to display the configuration page.
- Complete the configuration as described in table below.
- Save the configuration.
|
Settings |
Guidelines |
|---|---|
|
Name |
Specify a name to identify the server within the system. |
|
User Name Template |
Specify a username template. Specify how the system should construct a username. You may use any combination of certificate variables contained in angle brackets and plain text. The username template you configure must be consistent with the MDM certificate template configuration. Your goal is to identify the values specified in the MDM certificate that are to be used as the username in IPS system. This value populates the <USER> and <USERNAME> session variables for use throughout the rest of the system configuration. For example, suppose the certificate DN is: CN=<EnrollmentUser>, serialNumber=<DeviceUid>, o=Company. With this configuration, the certificate could identify both the user and the device. In this example, the username template is <certDN.CN>. |
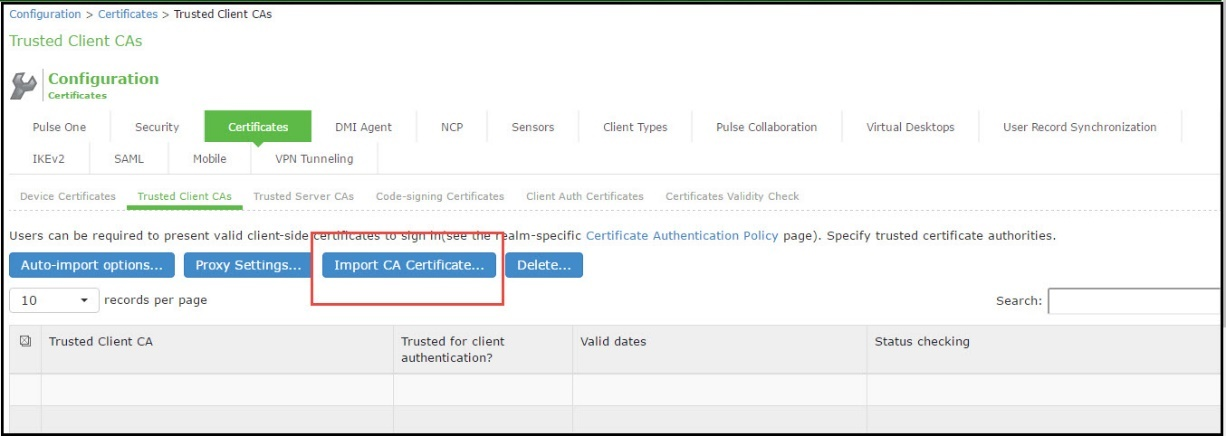
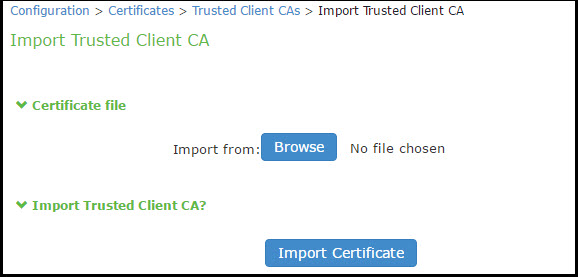
Adding the MDM Certificate to the Trusted Client CA Configuration
The system uses the uploaded certificate to verify that the browser-submitted certificate is valid. You must upload the MDM certificate that signed the client certificate that was pushed to the mobile devices. Typically, you obtain this certificate from the MDM when your company establishes its account with them.
To import a trusted client CA certificate:
- Select System > Configuration > Certificates > Trusted Client CAs.
- Click Import Trusted Client CA Certificate.
- Browse to the certificate file, select it, and click Import Certificate to complete the import operation.
- Click the link for the Trusted Client CA to display its details.
Configuring User Roles
User roles are classifiers for network access control policies. You create a set of roles to use in your classification scheme: device status is MDM enrollment complete or incomplete; device status is MDM-policy compliant or noncompliant; device is employee owned or company owned; device platform is iOS, Android, or neither; and so forth.
The user role configuration also includes options to customize user interface features that are appropriate for a particular role. For MDM deployments, you can use the Personalized Greeting UI option to send a notification message to the device when the role has been applied.
To configure user roles:
- Select Users > User Role to navigate to the role configuration page.
- Click New Role to display the configuration page.
- Complete the configuration for general options as described in below table.
- Save the configuration.
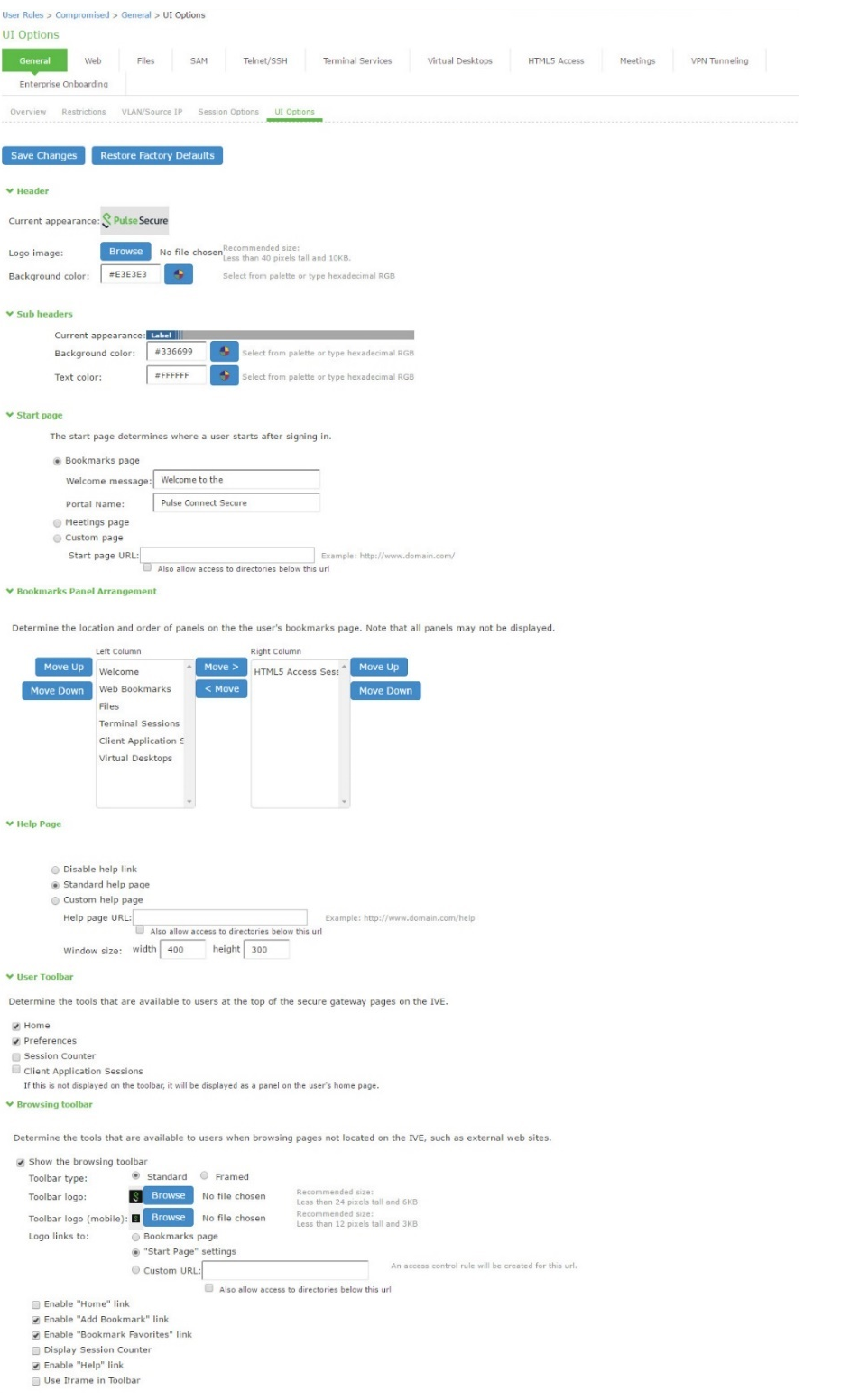
- Click UI options to display the configuration page.
- Complete the configuration for UI options as described in below table.
- Save the configuration.
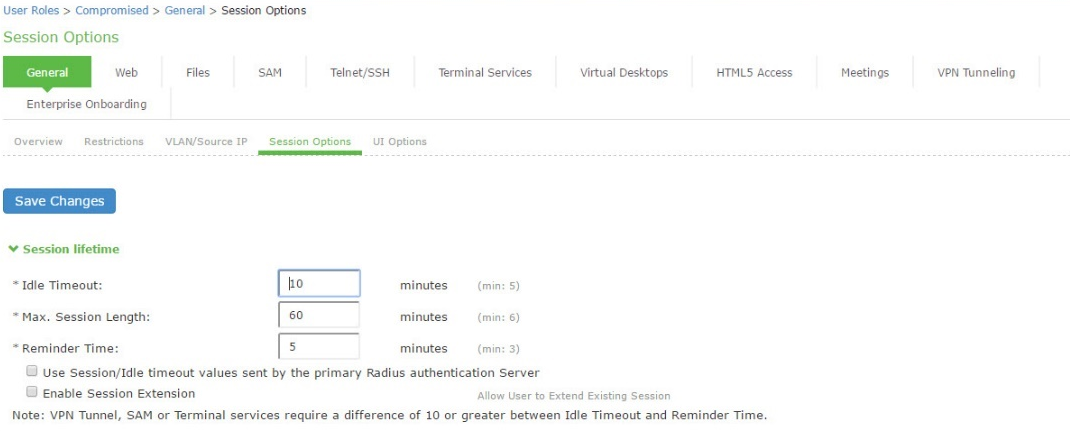
- Click Session Options to display the configuration page.
- Complete the configuration for session options as described in below table.
- Save the configuration.
- Click Agentless to display the configuration page.
- Complete the configuration for agentless options as described in below table.
- Save the configuration.
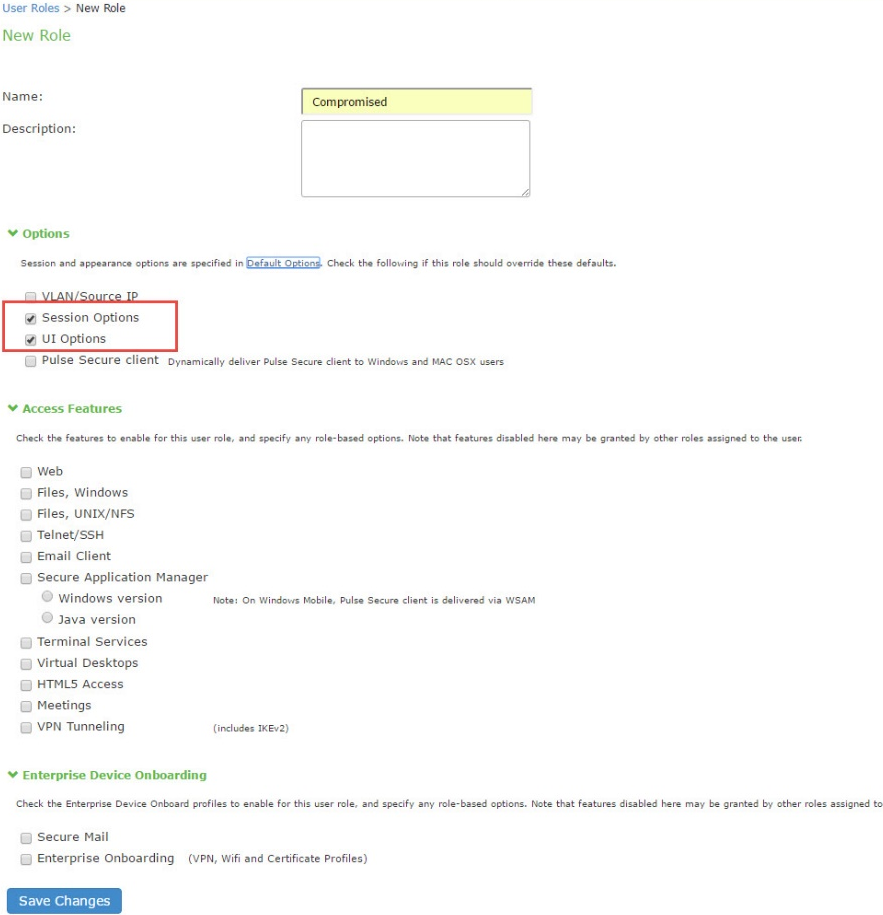
|
Settings |
Guidelines |
|---|---|
|
Overview tab |
|
|
Name |
Specify a name for the configuration. |
|
Description |
Describe the purpose of the role so that other administrators are aware of it. |
|
Options |
Select UI Options so that you can customize a message to be sent to the device when the role is applied. |
|
UI Options tab |
|
|
Personalized greeting |
Select the Show notification message option and enter a message to be sent to the device (through the MDM API) after sign-in and this role has been applied, or after role reevaluation if it results in a role change to this role. In this example, we are using the system to enforce MDM enrollment by flagging compromised devices. The message, therefore, is: Your device is compromised. Network access may be limited. The message is forwarded to the device using the MDM server Push Notification feature. The content of your notification message can vary depending on whether the switch or access point supports change of authorization (CoA). If the CoA is supported, reauthentication is automatic, so your message might simply state that “your level of access has changed.” If CoA is not supported, reauthentication needs to be done manually by the user in which case the message might state that “your level of access has changed, please reconnect.” NOTE: When multiple roles are assigned, UI options are not merged. The UI options for the first role that matches are applied. |
|
Session Options |
|
|
Allow VPN Through Firewall |
Enable this option to allow Infranet Enforcer traffic to act as a heartbeat and keep the session alive. This option is useful for iOS devices. |
|
Agentless |
|
|
Enable agentless access |
Select this option for roles that you provision to access the network from BYOD devices. The solution that integrates with MDMs depends on the native supplicant, not an Ivanti agent. |
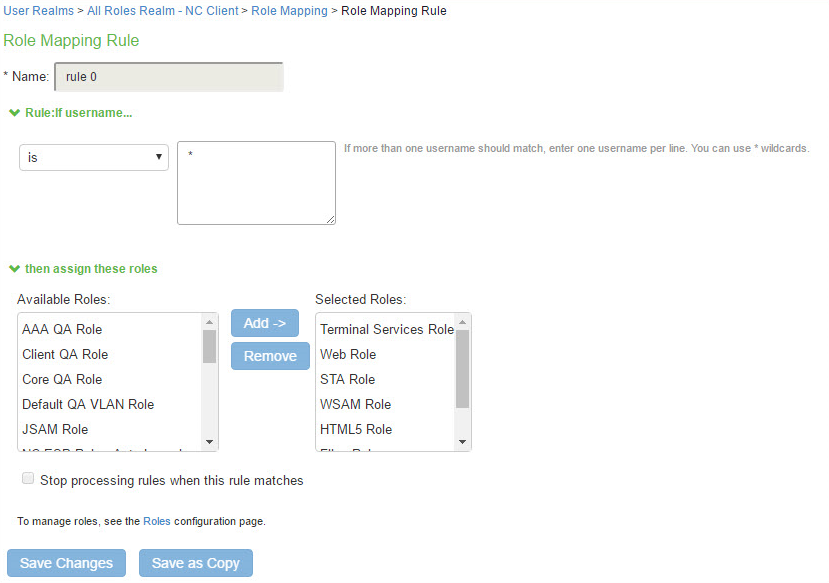
Configuring a Realm and Role Mapping Rules
The user realm configuration associates the authentication server data and MDM server data with user roles.
To configure the realm and role mapping rules:
- Select Users > User Realms > New User Realm to display the configuration page.
- Upon saving the new realm, the system displays the role mapping rules page.
- Click New Rule to display the configuration page.
- Complete the configuration as described in table.
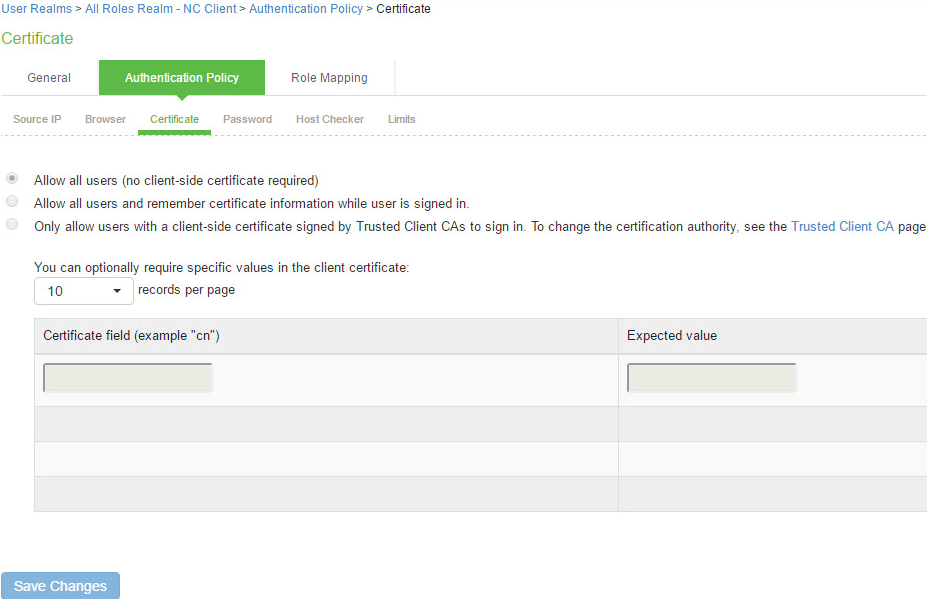
- Click the Authentication Policy tab and then click the Certificate subtab to display the certificate restriction configuration page.
|
Settings |
Guidelines |
|---|---|
|
Name |
Specify a name for the realm. If you enable sign-in using a realm suffix in the sign-in policy configuration, the realm name must match the username realm suffix configured in the MDN Wi-Fi profile. |
|
Description |
Describe the purpose of the realm so that other administrators are aware of it. |
|
Servers |
|
|
Authentication |
Select the user authentication server for this realm’s users. This example uses the certificate server configured in the earlier step. When you use a certificate server, users are not prompted for their credentials. You can also select the authentication server used for employees. In that case, users are prompted by the sign-in page to provide their username and password. |
|
User Directory/Attribute |
This option is not used. |
|
Accounting |
This option is not used. |
|
Device Attributes |
Select the MDM server configured for device authorization. |
|
Device Check Interval |
Select this feature to leverage the MDM posture assessment checks and enforce compliance. For example, the MDM might detect that a device is out of compliance with its security policies, such as a password policy. At the next device check interval, IPS queries the MDM for updated attribute data. In this example, it learns that a formerly compliant device is now noncompliant. It assigns the device the noncompliant role and sends the 802.1x authenticator the corresponding RADIUS attribute to place it in a remediation VLAN. Specify the interval at which to query the MDM for updated attribute data. Specify 0 to disable periodic queries. The minimum is 10 minutes and the maximum is 10080 minutes (7 days). Specify an interval that is appropriate for the MDM. Some MDMs, for example, update records every 4 hours, so a 10-minute interval would not be productive. |
|
Dynamic Policy Evaluation |
|
|
Dynamic Policy Evaluation |
This option is not used. |
|
Settings |
Guidelines |
|
Rule based on |
Select Device Attribute and click Update to update the configuration page so that it displays settings for role mapping using device attributes. |
|
Name |
Specify a name for the configuration. |
|
Rule |
Select a device attribute and a logical operator (is or is not), and type a matching value or value pattern. In this example, select isCompromised and the logical operator is, and enter the value 1 (true). This means that devices with a compromised status match the rule. |
|
Role assignment |
Select the roles to apply if the data matches the rule. |
The following table describes the AirWatch record attributes that can be used in role mapping rules.
|
Role Mapping Attribute Name |
AirWatch Attribute Name |
Description |
Data Type |
|---|---|---|---|
|
BlockLevelEncryption |
BlockLevelEncryption |
True if block-level encryption is enabled; false otherwise. |
Boolean |
|
complianceReason |
ComplianceStatus |
Values: Compliant, Non-Compliant. |
String |
|
CompromisedStatus |
CompromisedStatus |
True if the status is compromised; false otherwise. |
Boolean |
|
DataProtectionEnabled |
DataProtectionEnabled |
True if data protection is enabled; false otherwise. |
Boolean |
|
deviceId |
Id.Value |
Device identifier. |
String |
|
deviceName |
DeviceFriendlyName |
The concatenated name used to identify the device/user combination. |
String |
|
FileLevelEncryption |
FileLevelEncryption |
True if file-level encryption is enabled; false otherwise. |
Boolean |
|
IMEI |
Imei |
IMEI number of the device. |
String |
|
isCompliant |
ComplianceStatus |
Values: Compliant. |
String |
|
isCompromised |
CompromisedStatus |
True if the device is compromised; false otherwise. |
Boolean |
|
isEnrolled |
EnrollmentStatus |
True if MDM value is Enrolled; false otherwise. |
Boolean |
|
IsPasscodeCompliant |
IsPasscodeCompliant |
True if the passcode is compliant with the MDM policy; false otherwise |
Boolean |
|
IsPasscodePresent |
IsPasscodePresent |
True if a passcode has been configured; false otherwise. |
Boolean |
|
LastComplianceCheckOn |
LastComplianceCheckOn |
The refresh date and timestamp of the last status reported. |
Timestamp |
|
LastCompromisedCheckOn |
LastCompromisedCheckOn |
The refresh date and timestamp of the last status reported. |
Timestamp |
|
lastSeen |
LastSeen |
Date and time the device last made successful contact with the MDM. |
Timestamp |
|
LocationGroupName |
LocationGroupName |
MDM location group configuration value. |
String |
|
macAdress |
MacAddress |
The Wi-Fi MAC address. |
String |
|
model |
Model |
Model is automatically reported by the device during registration. |
String |
|
osVersion |
OperatingSystem |
OS version. |
String |
|
ownership |
Ownership |
Values: C, E, or S (Corporate, Employee, or Shared). |
String |
|
phoneNumber |
PhoneNumber |
Phone number entered during registration. |
String |
|
platform |
Platform |
Platform specified during registration. |
String |
|
serialNumber |
SerialNumber |
Serial number. |
String |
|
UDID |
Udid |
Unique device identifier. |
String |
|
userEmail |
UserEmailAddress |
E-mail address of device user. |
String |
|
userName |
UserName |
Name of device user. |
String |
|
UUID |
Uuid |
Universal unique identifier. |
String |
The following table describes the MobileIron record attributes that can be used in role mapping rules.
|
Role Mapping Attribute Name |
MobileIron Attribute Name |
Description |
Data Type |
|---|---|---|---|
|
blockedReason |
blockedReason |
Reason MDM has blocked the device. Can be a multivalued string. Values are: •AllowedAppControlPolicyOutOfCompliance •AppControlPolicyOutOfCompliance •DataProtectionNotEnabled •DeviceAdminDeactivated •DeviceComplianceStatusUnknown •DeviceCompliant •DeviceCompromised •DeviceExceedsPerMailboxLimit •DeviceManuallyBlocked •DeviceNotRegistered •DisallowedAppControlPolicyOutOfCompliance •ExchangeReported •HardwareVersionNotAllowed •OsVersionLessThanSupportedOsVersion •PolicyOutOfDate •RequiredAppControlPolicyOutOfCompliance |
String |
|
complianceReason |
compliance |
MDM policy compliance status. Can be a multivalued string. Values are: •AllowedAppControlPolicyOutOfCompliance •AppControlPolicyOutOfCompliance •DataProtectionNotEnabled •DeviceAdminDeactivated •DeviceComplianceStatusUnknown •DeviceCompliant •DeviceCompromised •DeviceExceedsPerMailboxLimit •DeviceManuallyBlocked •DeviceNotRegistered •DisallowedAppControlPolicyOutOfCompliance •ExchangeReported •HardwareVersionNotAllowed •OsVersionLessThanSupportedOsVersion •PolicyOutOfDate •RequiredAppControlPolicyOutOfCompliance |
String |
|
countryName |
countryName |
Country name corresponding with the country code of the device. |
String |
|
deviceId |
@id |
Device identifier. |
String |
|
deviceName |
name |
The concatenated name used to identify the device/user combination. |
String |
|
homeOperator |
homeOperator |
The service operator for the device when it is not roaming. |
String |
|
Imei |
iPhone IMEI (iOS), imei (Android) |
IMEI number of the device. |
String |
|
isBlocked |
isBlocked |
True if the device is blocked from accessing the ActiveSync server; false otherwise. |
Boolean |
|
isCompliant |
compliance |
True if the device is in compliance with its MDM security policies; false otherwise. |
Boolean |
|
isCompromised |
compliance |
True if the device is compromised; false otherwise. |
Boolean |
|
isEnrolled |
statusCode |
True if the device has completed enrollment or registration; false otherwise. |
Boolean |
|
isQuarantined |
isQuarantined |
True if the device is quarantined by the MDN; false otherwise. |
Boolean |
|
lastSeen |
lastConnectAt |
Date and time the device last made successful contact with the MDM. |
Timestamp |
|
manufacturer |
manufacturer |
Manufacturer is automatically reported by the device during registration. |
String |
|
macAdress |
wifi_mac (iOS), wifi_mac_addr (Android) |
The Wi-Fi MAC address. |
String |
|
mdmManaged |
mdmManaged |
True if the MDM profile is enabled on the device; false otherwise. This field applies only to iOS devices. For other devices, the value is always false. |
Boolean |
|
model |
ModelName, model, device_model |
Model is automatically reported by the device during registration. |
String |
|
operator |
operator |
Service provider. The value PDA indicates no operator is associated with the device. |
String |
|
osVersion |
OSVersion (iOS), os_version (Android) |
OS version. |
String |
|
ownership |
employeeOwned |
Values: Employee or Corporate. |
String |
|
phoneNumber |
currentPhoneNumber |
Phone number entered during registration. |
String |
|
platform |
platform |
Platform specified during registration. |
String |
|
quarantinedReason |
quarantinedReason |
MDM policy compliance status. Can be a multivalued string. Values are: •AllowedAppControlPolicyOutOfCompliance •AppControlPolicyOutOfCompliance •DataProtectionNotEnabled •DeviceAdminDeactivated •DeviceComplianceStatusUnknown •DeviceCompliant •DeviceCompromised •DeviceExceedsPerMailboxLimit •DeviceManuallyBlocked •DeviceNotRegistered •DisallowedAppControlPolicyOutOfCompliance •ExchangeReported •HardwareVersionNotAllowed •OsVersionLessThanSupportedOsVersion •PolicyOutOfDate •RequiredAppControlPolicyOutOfCompliance |
|
|
serialNumber |
SerialNumber |
Serial number. |
String |
|
UDID |
iPhone UDID |
Unique device identifier. |
String |
|
userEmail |
emailAddress |
E-mail address of device user. |
String |
|
userId |
principal |
User ID. |
String |
|
userName |
userDisplayName |
Name of device user. |
String |
|
UUID |
uuid |
Universal unique device identifier. |
String |
|
Role Mapping Attribute Name |
Microsoft Intune Attribute Name |
Description |
Data Type |
|---|---|---|---|
|
deviceid |
azureDeviceId |
The device Id of the device after it has work place joined with Azure Active Directory. |
String |
|
IMEI |
imei |
The device unique identifier. IMEI (15 decimal digits: 14 digits plus a check digit) or IMEISV (16 digits) includes information on the origin, model, and serial number of the device. |
String |
|
isCompliant |
complianceState |
True or false (string) based on whether device is compliant or non-compliant. |
Boolean |
|
isEnrolled |
isManaged |
True or false (indicating whether the client is managed by Intune or not). |
Boolean |
|
lastSeen |
lastContactTimeutc |
The date time when the device last checked in with the Intune management service endpoint. |
String The format is MM/DD/YYYY HH:MM:SS |
|
macAddress |
macAddress |
MAC address of the device. |
String |
|
manufacturer |
manufacturer |
Device Manufacturer. |
String |
|
meid |
meid |
MEID is 56 bits long (14 hex digits). It consists of three fields, including an 8-bit regional code (RR), a 24-bit manufacturer code, and a 24-bit manufacturer-assigned serial number. |
String |
|
model |
model |
Model of the device. |
String |
|
osVersion |
osVersion |
OS Version of the device. |
String |
|
serialNumber |
serialNumber |
Serial number of the device. Applies to iOS Devices only. |
String |
|
UDID |
udid |
The device unique identifier. Unique Device Identifier (UDID), which is a sequence of 40 letters and numbers that is specific to iOS devices. |
String |
|
UUID |
uuid |
Universal unique device identifier. |
String |
|
Settings |
Guidelines |
|---|---|
|
Allow all users |
Do not select this option. If you select this option, the system does not request a client certificate during the TLS handshake. |
|
Allow all users and remember certificate |
If you select this option, the system requests a client certificate during the TLS handshake. It does allow endpoints to authenticate without a client certificate. For those with a client certificate, the certificate attributes are placed in the session context. |
|
Only allow users with a client-side certificate |
If you select this option, the system requests a client certificate during the TLS handshake. It does not allow endpoints to authenticate without a valid client certificate. If the realm is configured with a certificate server, like this example, this option is the only option that can be selected. |
Configuring a Sign-In Policy
A sign-in policy associates devices with a realm.
To configure a sign-in policy:
- Select Authentication > Signing In > Sign-In Policies to navigate to the sign-in policies configuration page.
- Click New URL to display the configuration page.
- Complete the configuration as described below.
- Save the configuration.
|
Settings |
Guidelines |
|---|---|
|
User type |
Select Users. |
|
Sign-in URL |
Enter a URL. |
|
Description |
Describe the purpose of the sign-in policy so that other administrators are aware of it. |
|
Sign-In Page |
Select a sign-in page. |
|
Authentication Realm |
|
|
Realm |
Select the realm you configured in the earlier step. |
|
Authentication Protocol Set |
Select the protocol you configured in the earlier step. |
|
Realm name as a username suffix |
Select this option if the username sent during sign-in includes a realm suffix. To use this option, the realm name must match the username realm suffix configured in the MDN Wi-Fi profile. This configuration enables you to dedicate the realm to the MDM traffic. Non-MDM traffic passing through the same switch then belongs to a different realm. NOTE: In some cases, you can use authentication protocol sets to segregate traffic into a particular realm. For example, assuming only mobile endpoints use TLS and other endpoints do not, an authentication protocol set containing only TLS can be created and associated with a particular realm through a sign-in policy. |
|
Remove realm suffix |
Remove the realm suffix within system processes, such as rule processing and logs. |