Configuring Pulse Policy Secure for Dot1x Authentication
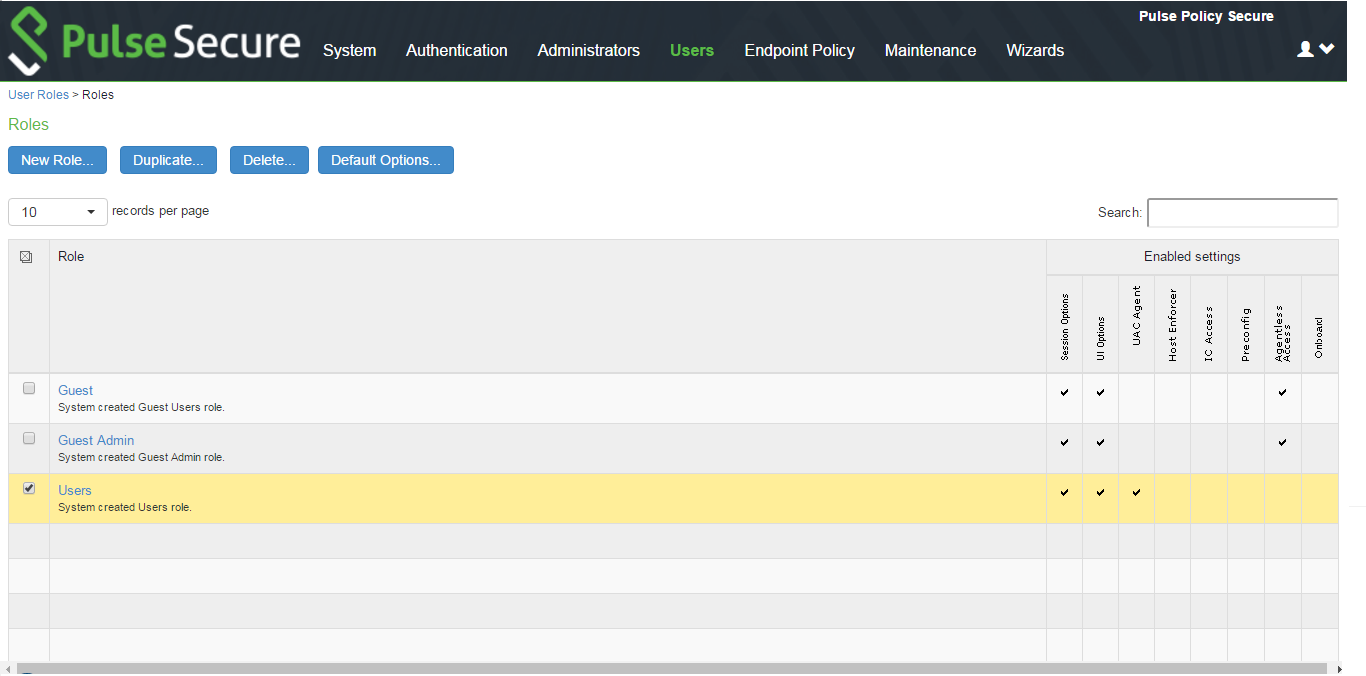
Configuring User Role for Dot1x Authentication
Pulse Policy Secure(PPS) access management framework evaluates authentication requests to match endpoints to roles. You must configure user roles for the various types of endpoints authenticated by the MAC address authentication framework.
To create a user role:
1.Select Users > User Role to navigate to the role configuration page.
2.Click New Role to display the configuration page shown in figure.
3.Complete the configuration for general options.
4.Save the configuration.
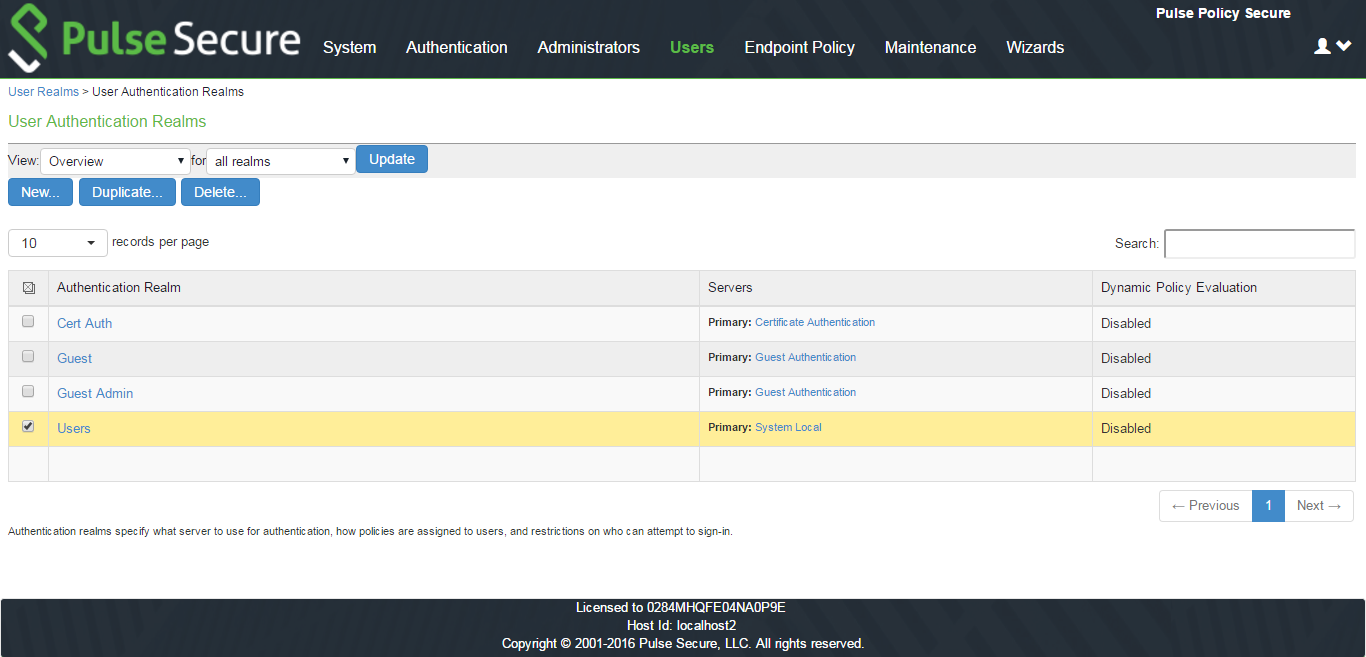
Configuring User Realm for Dot1x
The user realm configuration associates the MDM server data with user roles.
To configure the realm and role mapping rules:
1.Select Users > User Realms > New User Realm to display the configuration page shown in figure.
2.Make necessary changes and save the configuration.
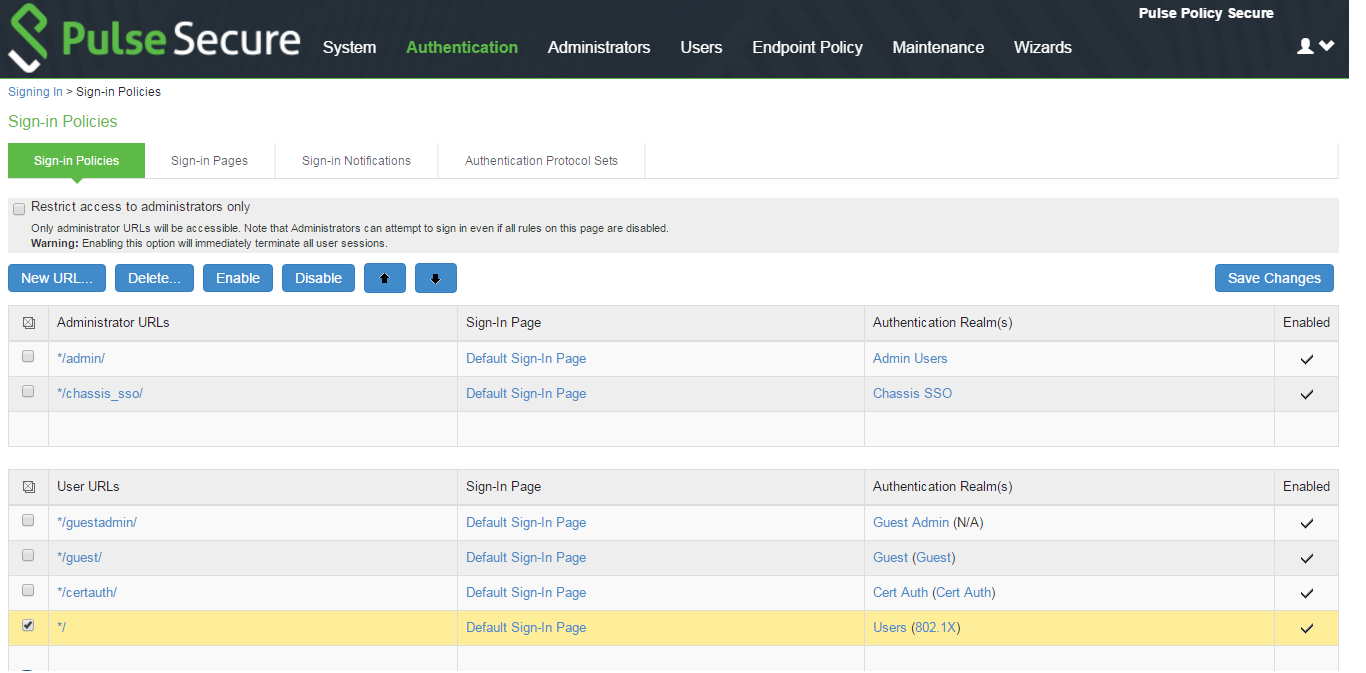
Configuring a Sign-In Policy for Dot1x
A sign-in policy associates devices with a realm.
To configure a sign-in policy:
1.Select Authentication > Signing In > Sign-In Policies to navigate to the sign-in policies configuration page.
2.Click New URL to display the configuration page shown in figure.
3.Make necessary changes and save the configuration.
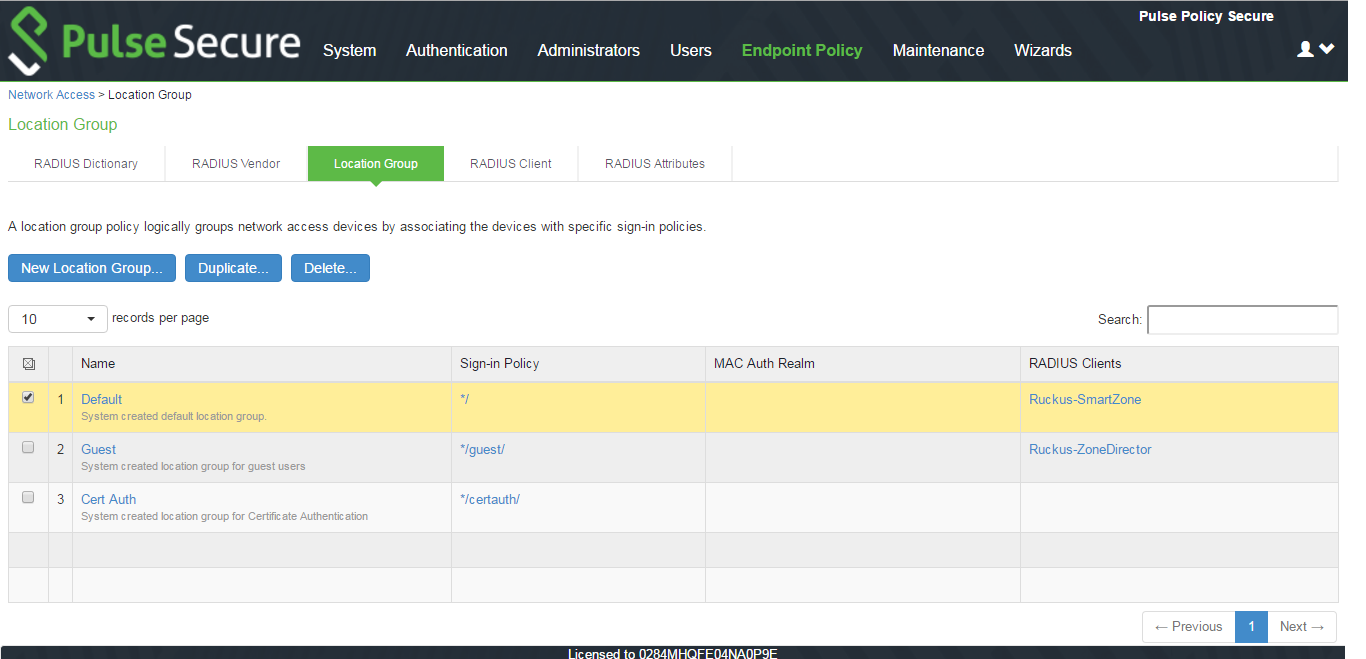
Configuring Location Group for Dot1x
To configure Policy Secure 802.1x framework for non-supplicant endpoints, you must configure Location Group.
1.Select Endpoint Policy > Network Access > Location Group.
2.Complete the configuration as shown in figure.
3.Save the configuration.
Configuring Authentication Protocol Set for Dot1x
Switches from various vendors may use the Standard Password Authentication Protocol (PAP), CHAP, or EAP-MD5 protocols for MAC authentication. These protocols are not included in the default authentication protocol set for 802.1x deployments.
To add PAP, CHAP, and EAP-MD5 to the 802.1x protocol set:
1.Log into Policy Secure Web administrator interface.
2.Select Authentication > Signing In > Authentication Protocols Sets to display the Authentication Protocol Sets page.
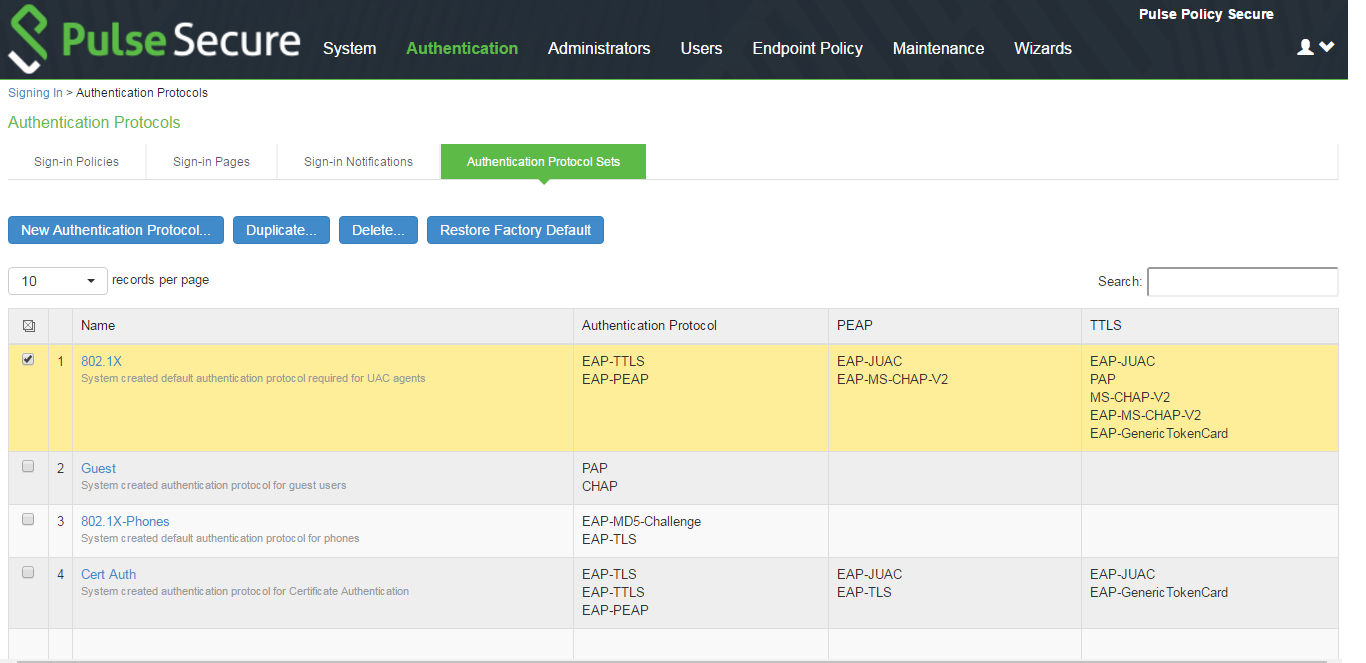
3.Click the 802.1x link to edit the 802.1x authentication protocol set configuration.
4.Use the selector buttons to add PAP, CHAP, and EAP-MD5-Challenge to the 802.1x authentication protocol set.
Configuring RADIUS Client
To configure a Radius Client:
1.Select Endpoint Policy > Network Access > RADIUS Client.
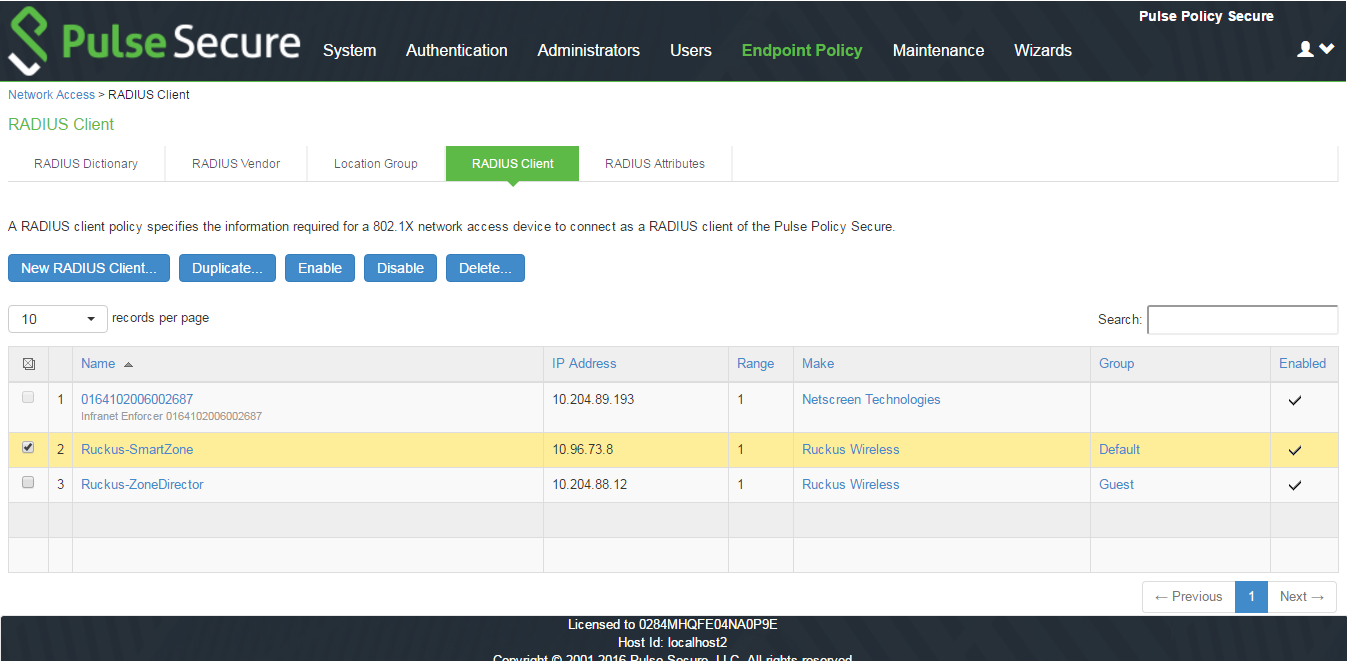
2.Enter the Name, IP Address, Shared Secret and Make model as Ruckus Wireless.
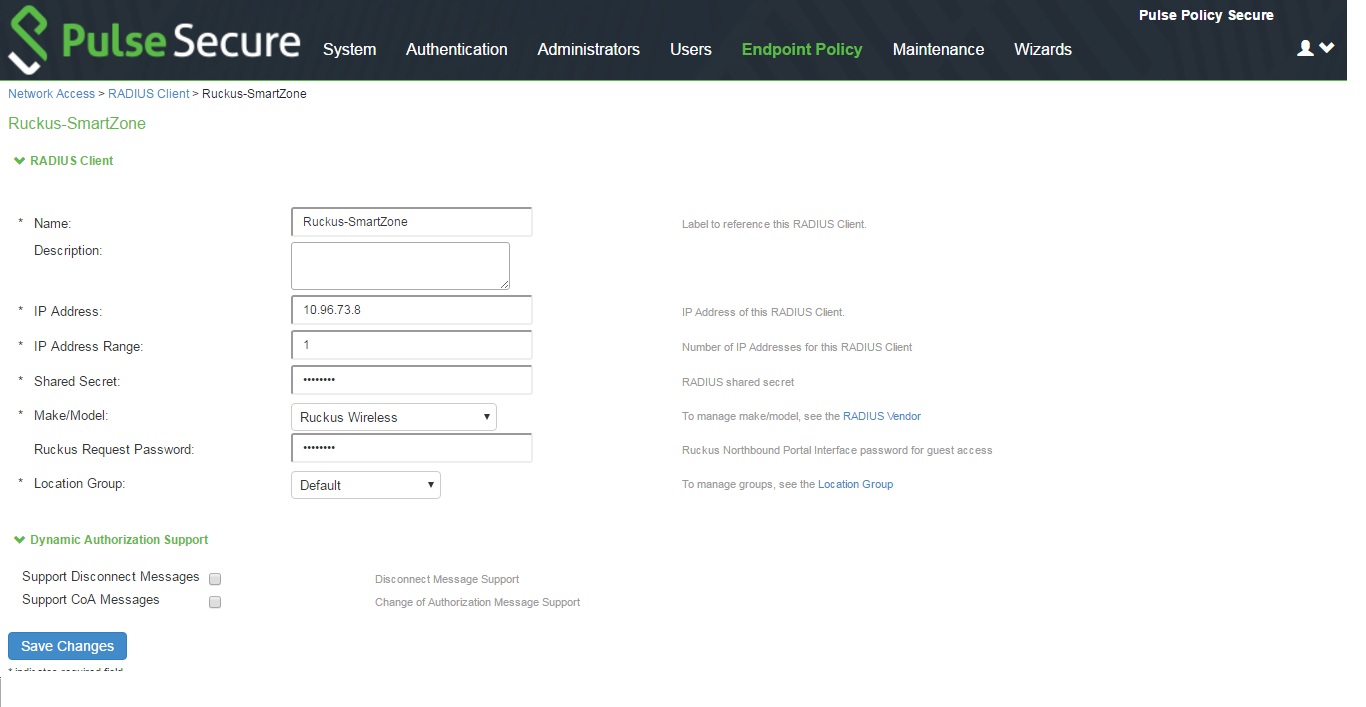
3.Here Ruckus Request password should be the same which is configured in “NorthBound Polar Interface” of SmartZone WLC and select default location group.