Configuring Gateways
•Workflow: Creating a Gateway in VMware vSphere
•Workflow: Creating a Gateway in Amazon Web Services
•Workflow: Creating a Gateway in Microsoft Azure
•Workflow: Creating a Gateway in KVM/OpenStack
•Workflow: Creating a Gateway in Google Cloud Platform
•Workflow: Creating a Gateway in Oracle Cloud Platform
Introduction
This guide describes how to configure a ZTA gateway for your secure applications and resources. To learn more about configuring Ivanti Connect Secure (ICS) Gateways, refer instead to the ICS Tenant Admin Guide available from the nZTA documentation portal.
A Gateway is a virtual machine instance that you use to control access to your applications. You deploy Gateway instances at each location your applications reside - at a physical datacenter, a private or public cloud-based service, or some hybrid combination. Each Gateway communicates with the controller to ensure that application access requests received from end-user devices are authenticated.
Before you deploy a Gateway instance, you register a new Gateway record in the controller through the Tenant Admin portal. This record contains all basic identification, type, and network details required to enable secure communication between the controller and the Gateway instance. The registration process produces a package of settings, known as a Gateway definition, that you publish to the Gateway virtual machine instance during deployment. These settings enable the Gateway to establish communication back to the controller.
Make sure the Gateway virtual machine instance does not exist prior to registration with the controller. Each ZTA gateway must be deployed from the controller directly. The Gateway definition file is designed to be published to a new virtual machine Gateway instance during its initial deployment.
You deploy a Gateway virtual machine instance from a supplied template. Each Gateway template is pre-configured to define the required virtual machine settings and network interfaces for the target platform. During deployment, you specify the values for each defined interface according to the public and private subnets configured in your network infrastructure.
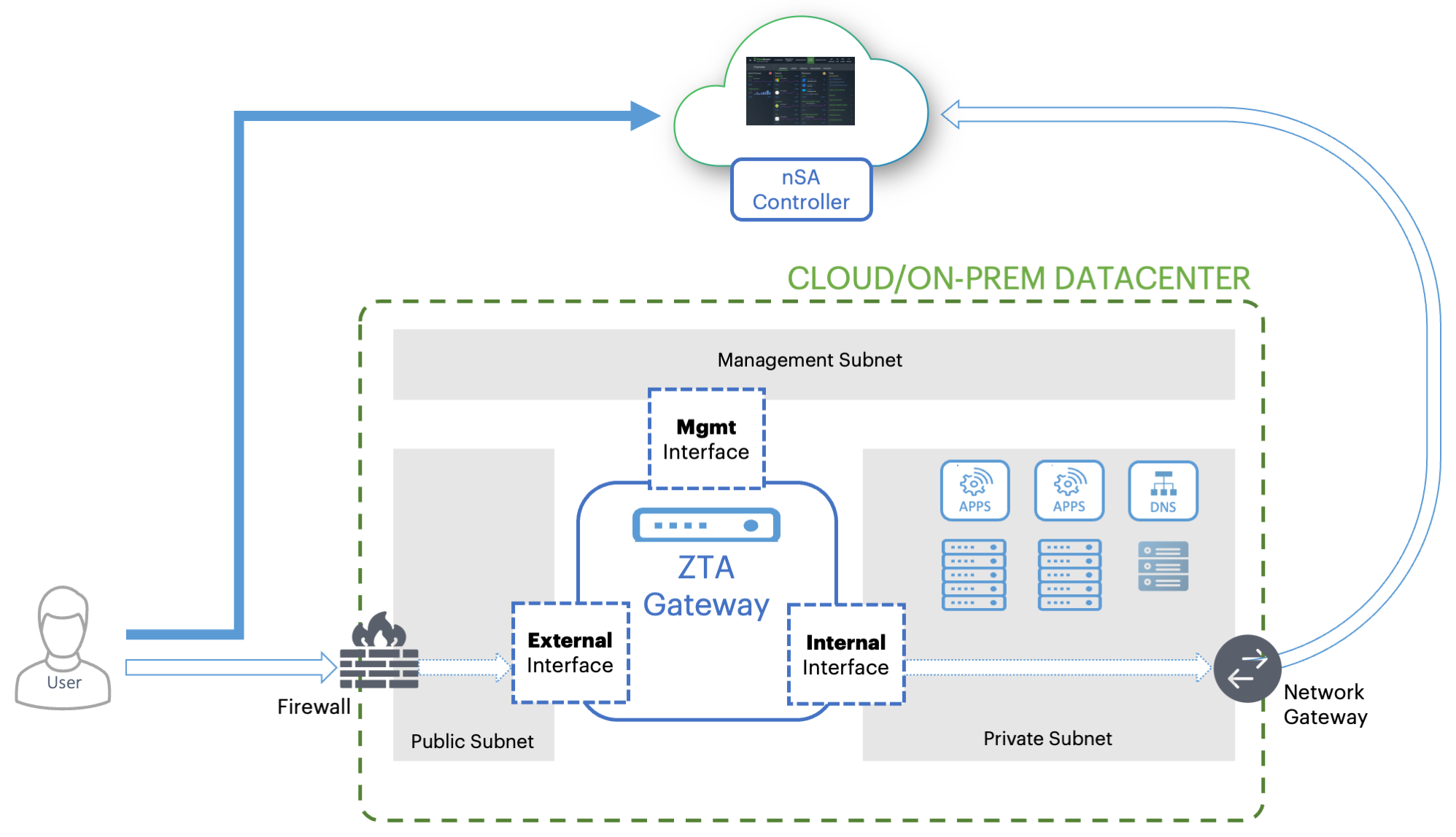
Each ZTA Gateway virtual machine uses a number of network interfaces:
- External network interface: Configured with a public subnet IP address and used for external client access to the applications deployed in that datacenter. Use this IP address during the process of creating your Gateway record on the controller.
- Internal network interface: Configured with a private subnet IP address and used for internal connections to the deployed applications, and for external communication with the controller.
- (Optional) Management network interface: Configured with an IP address and port on a further, separate, network subnet for deployments where a specific management interface is required.
When the management interface is enabled, the Gateway communicates with the controller through this interface instead. In this scenario, the Gateway still uses the internal network interface for DNS resolution and NTP server communication. As such, the Gateway DNS server should resolve the controller and NTP server FQDNs through the internal interface (internet access is required).
To ensure communication between your Gateways, the controller, and your client users, make sure the following network connections are enabled:
- Configure the firewall rules for the Public Subnet in which your ZTA Gateway External Interface resides is configured to accept inbound client connections on TCP port 443.
- Configure the Network Gateway serving your Private Subnet to allow outbound TCP traffic to the controller on port 443.
- Configure the Network Gateway serving your
Private Subnet to allow outbound UDP traffic to the
following Network Time Protocol (NTP) services:
- time.windows.com (port 123)
- time.nist.gov (port 123)
- If you are planning to use your ZTA Gateway to serve SaaS (Software-as-a-Service) applications, configure the application to restrict inbound connections to your network gateway IP address. This ensures that your SaaS application can be reached only by clients connecting through the ZTA gateway.
- If you maintain your own DNS service at the datacenter, use these details during Gateway record creation on the controller.
White-listing Required IP Addresses for your Services
The controller service uses a series of IP addresses and ports to facilitate access to the admin and user web consoles, for user enrollment, and for connections to a ZTA Gateway. To ensure network access, make sure the following IP addresses and ports are white-listed (or added to the allowed list) in your network firewalls and routing infrastructure. Select the IP addresses and ports for your corresponding region only:
-
North America:
52.186.44.249 (port 443)
52.188.33.186 (port 443)
-
Europe:
51.138.111.17 (port 443)
20.50.150.82 (port 443)
-
APJ:
20.44.238.229 (port 443)
20.44.237.67 (port 443)
-
UAE
20.233.40.108 (port 443)
20.233.41.69 (port 443)
-
Canada:
20.220.157.85 (port 443)
20.220.157.158 (port 443)
High Availability
nZTA allows you to deploy multiple Gateways at a single location to support high availability. This arrangement can be used to provide scaling, redundancy, and load distribution for your application delivery.
High availability is implemented in the Controller through Gateway Groups. You add individual Gateways to a group, and then associate the group with your Secure Access Policy.
To learn more about high availability and using Gateway Groups, see the Tenant Admin Guide.
Configuring a Default Gateway
nZTA directs requests from each application towards the Gateway defined in the secure access policy for the application.
A default ZTA Gateway can be defined. This Gateway handles all requests from application that are not referenced by any secure access policy. This enables packet analysis to be conducted on requests passing through the Gateway to assess the validity of the requests. Two default Gateway scenarios are supported:
- Any single Gateway at v21.1 (or later) can be assigned to act as the default Gateway. This Gateway is exclusively used as the default Gateway.
- Alternatively, any Gateway Group whose Gateways are all at v21.1 (or later) can be assigned to act as the default Gateway. In this scenario, the Gateways are used exclusively as the default Gateway. The Gateway Group is typically fronted by a load balancer to enable the required distribution of requests across the Gateways in the group.
To configure a default ZTA Gateway, you must edit and update the built-in Application discovery secure access policy.
The default Gateway (or Gateway Group) then handles all requests from applications on enrolled devices that are not referenced by any other secure access policy.
To learn more about using a default Gateway, see the Tenant Admin Guide.
Gateway Deployment Workflows
nZTA supports Gateway virtual machine instances deployed in the following environments:
- VMware vSphere: see
Workflow: Creating a Gateway in VMware vSphere. - Amazon Web Services (AWS): see
Workflow: Creating a Gateway in Amazon Web Services. - Microsoft Azure: see
Workflow: Creating a Gateway in Microsoft Azure. - KVM/OpenStack: see
Workflow: Creating a Gateway in KVM/OpenStack. - Google Cloud Platform: see
Workflow: Creating a Gateway in Google Cloud Platform.
For 22.7R1.3 release, 22.7R2.2 ZTA Gateway version is not supported with Oracle, AWS, and KVM platforms.
Workflow: Creating a Gateway in VMware vSphere
This workflow leads you through the process for setting up a Gateway in VMware vSphere. It contains two main procedures, in sequence:
- Creating the Gateway record in the Controller.
- Creating the Gateway virtual machine instance in VMware vSphere.
After these steps have been completed successfully, the Controller and Gateway establish communication with each other.
Before you start, make sure you have the following information and files for the Gateway:
- An identifying name for the Gateway
- The public IP address for the Gateway. This is the IP address at which clients can externally reach the Gateway instance.
- The Gateway geographic location
- (Optional) The name of the Gateway Group to which you want to add this new Gateway record. To learn more about Gateway Groups, see the Tenant Admin Guide.
Additionally, if you want to manually specify Gateway network interface settings:
-
The internal/private subnet IP address, subnet mask, and network gateway IP address.
-
The primary (and optional secondary) DNS server IP address, and search domain.
-
The external interface IP address, subnet mask, and network gateway IP address
-
(Optional) The management interface IP address, subnet mask, and network gateway IP address.
-
Credentials for the vSphere Console.
These credentials must include sufficient permissions to create a virtual machine from a template image.
To set up a ZTA Gateway in VMware vSphere, perform the following steps:
-
Log into the Tenant Admin Portal using the credentials provided in your welcome email. Two outcomes are possible:
- On unconfigured nZTA systems, the Secure Access Setup (Onboarding) wizard appears. In this case, click Add Gateway.
- On configured nZTA systems, the Network Overview page
appears. In this case:
From the nZTA menu, click the Secure Access icon, then select Gateways > Gateway List.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller.
To add a new Gateway, select Create from the top-right:
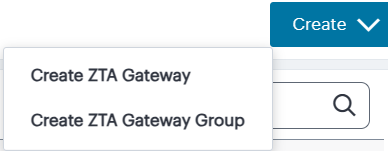
In the drop-down menu, click Create ZTA Gateway.
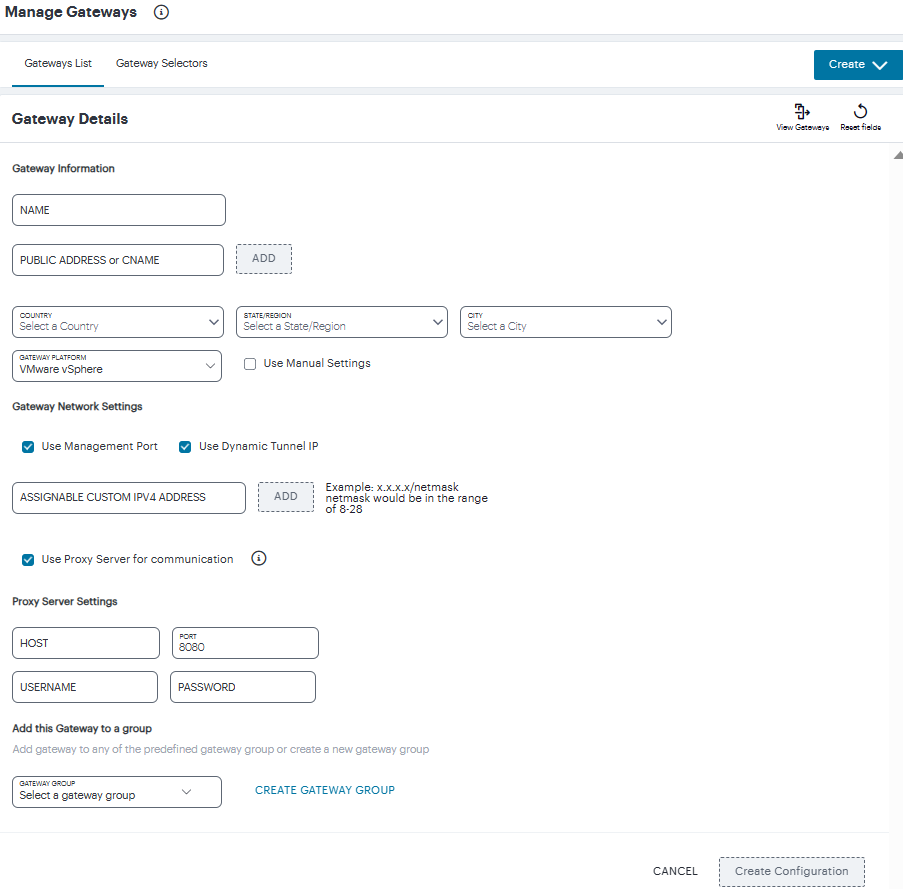
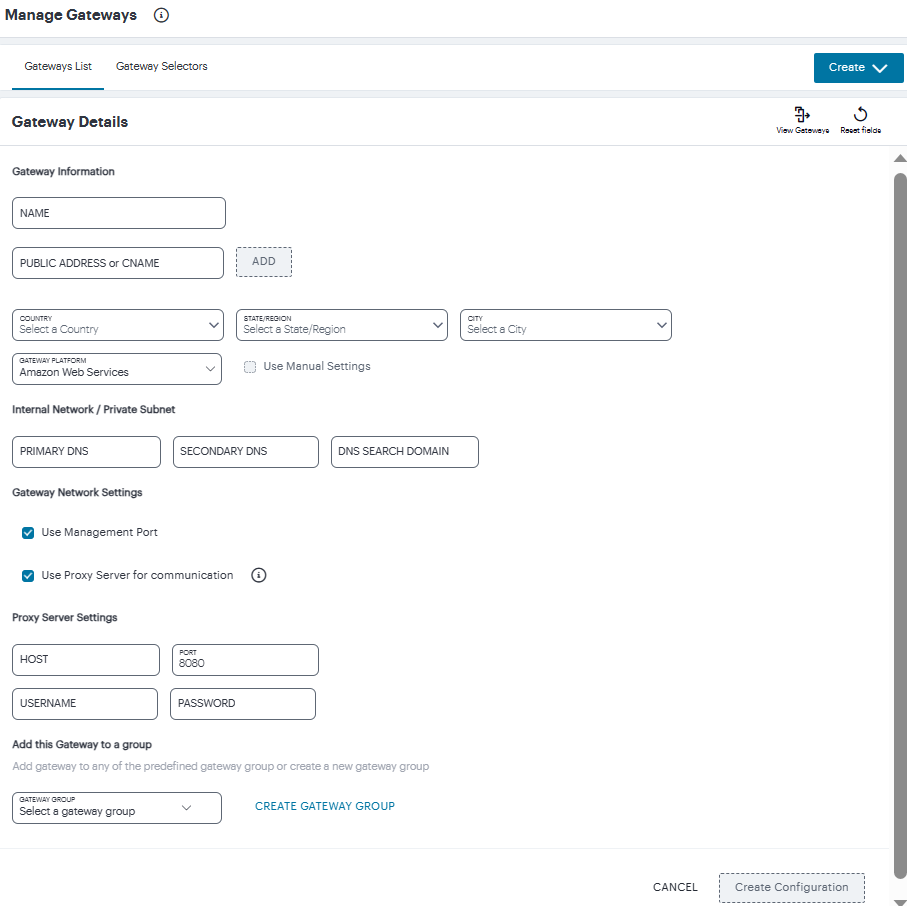
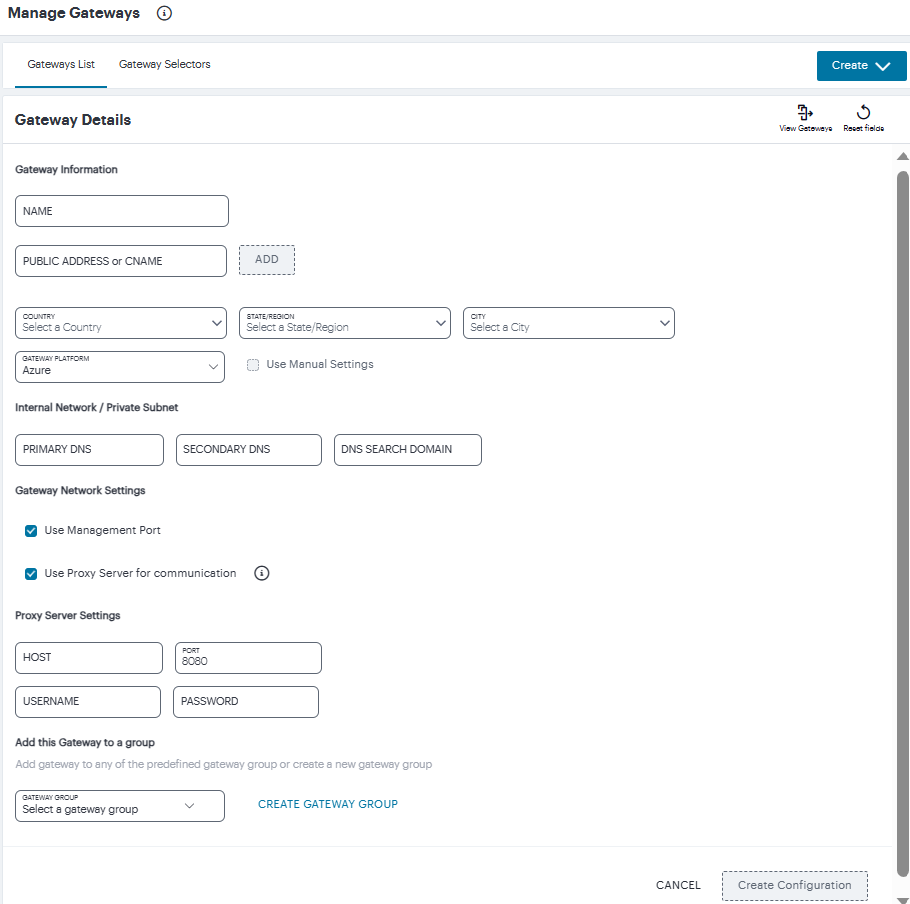
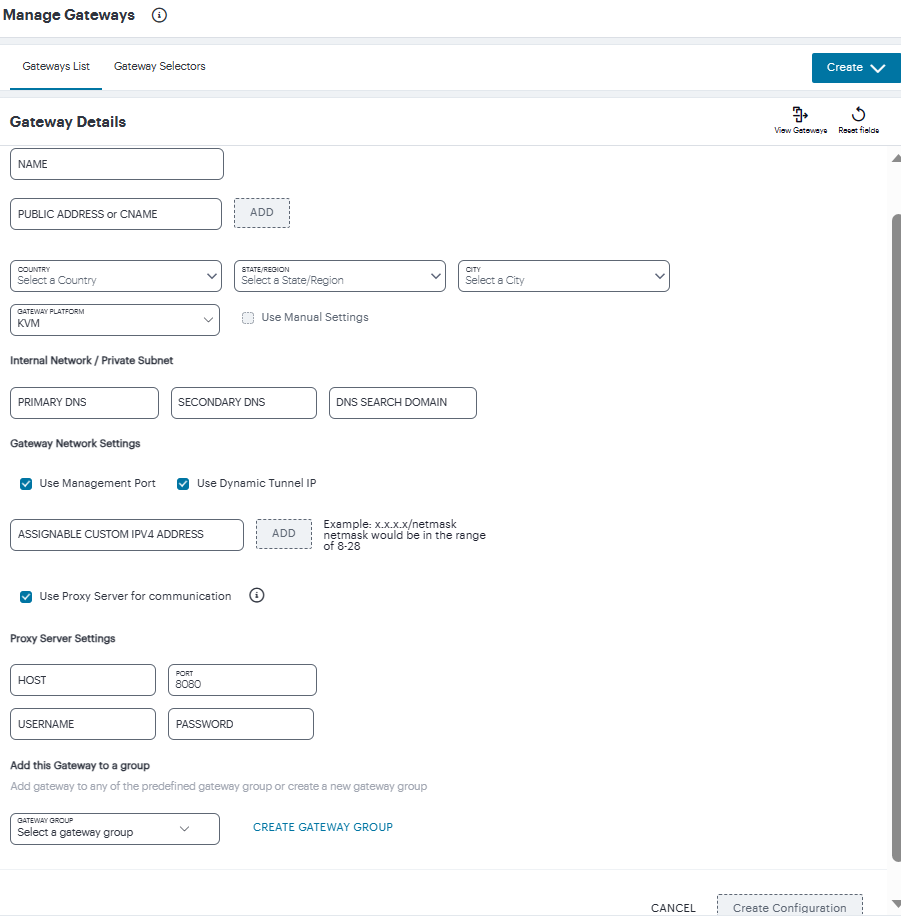
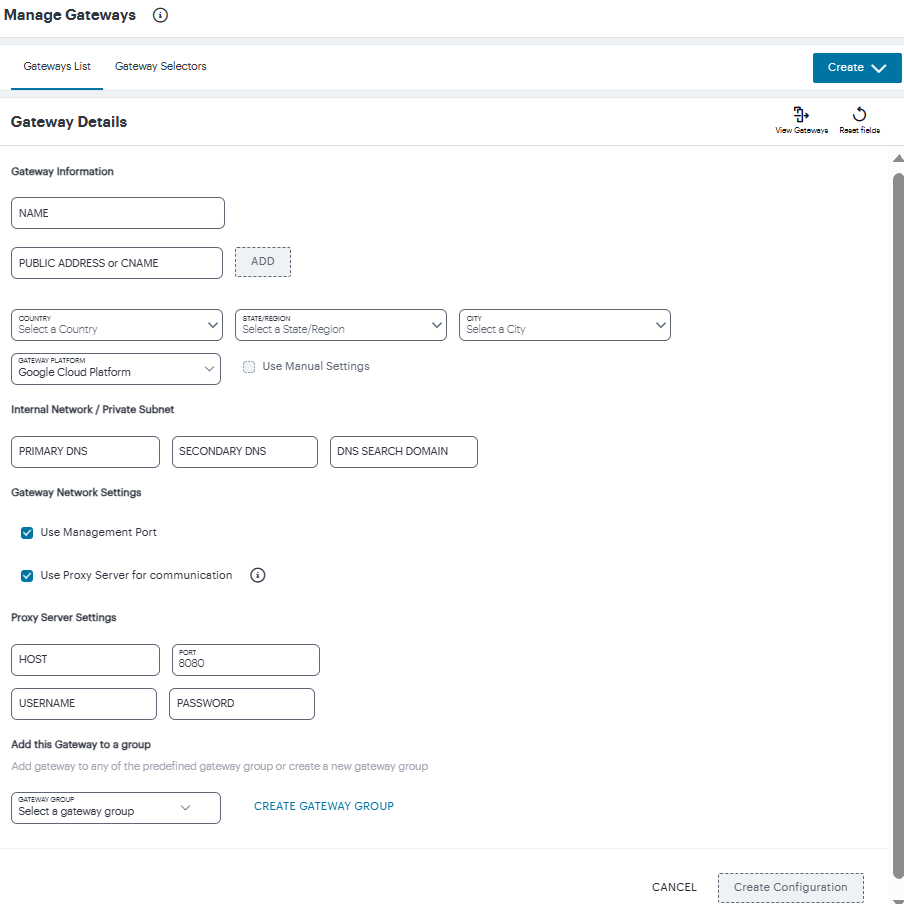
In both cases, the Gateway Details dialog appears.
To learn more about the settings on this page, see the Tenant Admin Guide.
-
(Optional) To enter your vSphere Gateway instance DNS and network interface settings manually, select Use Manual Settings. To instead allow nZTA to use DHCP-derived settings for DNS and network interfaces, leave Use Manual Settings un-selected.
-
Enter a Name for the Gateway.
-
Enter one or more Public Address or CNAME (Public IP address or CNAME) for the Gateway. Select Add to add each entry to the list.
-
Select a geographic Location for the Gateway.
-
For Gateway Platform, select "VMware vSphere".
-
(Optional) Select a Gateway Group to which the new Gateway is to be added.
-
(Optional) Select the Use Management Port check box to use management network ports for nZTA traffic rather than internal ports.
When the management port is enabled, the will Controller still use the internal port for DNS resolution. If the internal DNS cannot resolve the Controller domain, the internal interface will require internet access.
-
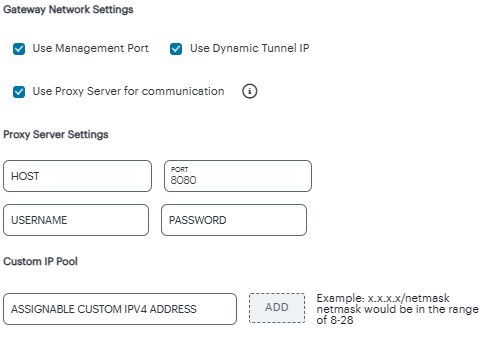
(Optional) Select the Use Dynamic Tunnel IP check box to configure a pool of IP addresses that are dynamically mapped to client sessions with this Gateway, such that user traffic from the Gateway to an application can be identified as originating from a specific client.
The Custom IP Pool dialog appears:
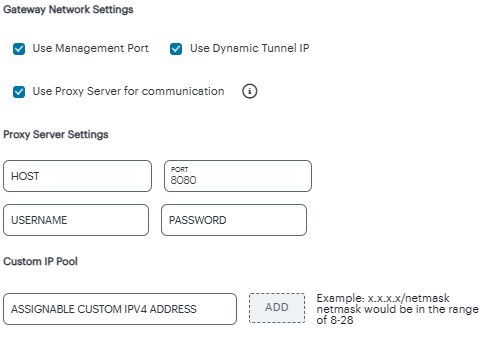
Dynamic Tunnel IP addresses are not supported in Gateway Groups.
Use the Assignable Custom IPv4 Address field to enter an IP address and subnet (in the range 8-28) in CIDR notation, then click Add. Repeat this step for each address/subnet you want to use.
-
(Optional) Select the Use proxy server for communication check box to enable nZTA to Controller communication via proxy server. Proxy is supported on both internal and management interfaces of the Gateway. Once enabled, enter host name and port. Optionally, if your proxy server requires further authentication, enter a username and password to log in to the proxy server.
Admin can configure proxy for existing Gateway after upgrading it to 22.4R3 version or later.
-
If you elected to use manual settings, the following panel appears:
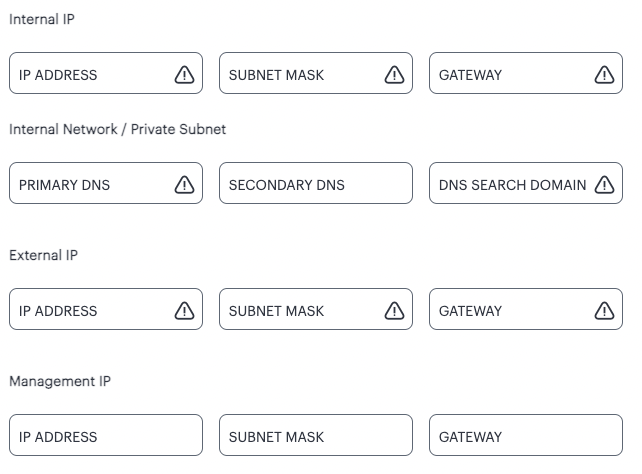
Enter the following details:
-
Specify the internal IP Address for the Gateway.
-
Specify the internal Subnet Mask for the Gateway.
-
Specify the internal network gateway IP address as the Gateway setting.
-
Enter the Primary DNS IP address for the Gateway.
-
(Optional) Enter the Secondary DNS IP address for the Gateway.
-
Enter the DNS Search Domain for the Gateway.
-
Specify the external IP Address for the Gateway.
-
Specify the external Subnet Mask for the Gateway.
-
Specify the external network gateway IP address as the Gateway setting.
Management network settings are optional, unless the Use Management Port check box is selected.
-
Specify the management IP Address for the Gateway.
-
Specify the management Subnet Mask for the Gateway.
-
Specify the management network gateway IP address as the Gateway setting.
-
-
To add a Gateway definition based on the settings you specified in this dialog, select Create Configuration.
After you complete this process, an unregistered Gateway record is created on the Controller. You can view this Gateway record on the Gateways > Gateways List page.
-
On the Gateways List page, select your vSphere Gateway and click the Download icon to obtain a copy of the Gateway definition file.
Retain this file for a later step.
The Gateway definition file is valid for 24 hours. If this period expires, you must replace the Gateway to generate a new Gateway definition file.
-
(Optional) If you have not yet downloaded the latest version of your Gateway VM file, click the Download icon and select Download gateway VM image. Save the archive file and unpack to a local workstation. Make sure the resulting file set is accessible from the vSphere Console.
-
Access the vSphere management interface, either from a client or a web browser, and log in using your vSphere credentials.
-
In the vSphere console, start the Deploy OVF Template wizard to create a new virtual machine based on the nZTA vSphere Gateway template.
-
In the wizard:
-
Choose to deploy from a local file.
-
Locate and upload your ZTA Gateway OVF/VMDK template files.
-
Provide an identifying name and location for the new Gateway virtual machine.
-
Choose any required compute resource.
For reference, the recommended minimum requirements for a Gateway virtual machine instance in vSphere are:
- 4 vCPU's and 8 GB memory, or
- 8 vCPU's and 32 GB memory
-
Choose the required storage settings.
-
Customize the vApp properties of your virtual machine and, in the VA IVE Configuration parameter, paste the raw text of the Gateway definition file downloaded earlier.
-
Confirm all settings.
-
Finish the wizard to create the Gateway virtual machine.
-
-
Locate the new Gateway virtual machine in the hosts and clusters.
-
Start the Gateway virtual machine by powering it on.
Wait until the boot up process is complete.
-
Return to the Gateways List page on the Controller.
-
Locate the new Gateway record in the list and confirm that its Connection Status has updated to Connected.
After you have registered a Gateway, you can configure it (or the Gateway Group to which it belongs) as the default Gateway if required. See the Tenant Admin Guide for details.
Workflow: Creating a Gateway in Amazon Web Services
For 22.7R1.3 release, 22.7R2.2 ZTA Gateway version is not supported with Oracle, AWS, and KVM platforms.
This workflow leads you through the process for setting up a Gateway in Amazon Web Services (AWS). It contains two main procedures, in sequence:
- Creating the Gateway record in the Controller.
- Creating the Gateway virtual machine instance in AWS.
After these steps have been completed successfully, the Controller and Gateway establish communication with each other.
Before you start, make sure you have the following information and files:
-
An identifying name for the Gateway
-
The public IP address for the Gateway. This is the IP address at which clients can externally reach the Gateway instance, typically an elastic IP address provided by AWS.
-
The Gateway geographic location.
-
(Optional) The name of the Gateway Group to which you want to add this new Gateway record. To learn more about Gateway Groups, see the Tenant Admin Guide.
-
The primary (and optional secondary) DNS server IP address, and search domain.
-
The Gateway AMI identifier. nZTA gateway AMIs are available in all AWS regions (except China). To obtain the AMI applicable to your region, follow these steps:
- Log into the AWS console.
- Navigate to EC2 > Images > AMIs.
- Select "Public Images".
- Search for the image corresponding to your selected hypervisor:
- Nitro: "ISA-V-NITRO-ZTA-22.7R2.2-607.1.img"
- Make a note of the corresponding AMI ID.
-
Credentials for the AWS Management Console.
These credentials must include sufficient permissions to create a stack.
-
The SSH public key that you are using with the AWS Management Console.
To set up a ZTA Gateway in AWS, perform the following steps:
-
Log into the Tenant Admin Portal using the credentials provided in your welcome email. Two outcomes are possible:
- On nZTA unconfigured systems, the Secure Access Setup (Onboarding) wizard appears. In this case, click Add Gateway.
- On nZTA configured systems, the Network Overview page
appears. In this case:
From the nZTA menu, click the Secure Access icon, then select Gateways > Gateway List.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller.
To add a new Gateway, select Create from the top-right:
In the drop-down menu, click Create ZTA Gateway.
In both cases, the Gateway Details dialog appears.
To learn more about the settings on this page, see the Tenant Admin Guide.
-
Enter a Name for the Gateway.
-
Enter one or more Public Address or CNAME (Public IP address or CNAME) for the Gateway. Select Add to add each entry to the list.
-
Select a geographic Location for the Gateway.
-
For Gateway Platform, select "Amazon Web Services".
-
(Optional) Select a Gateway Group to which the new Gateway is to be added.
-
(Optional) Select the Use Management Port check box to use management network ports for nZTA traffic rather than internal ports.
When the management port is enabled, the Controller will still use the internal port for DNS resolution. If the internal DNS cannot resolve the Controller domain, the internal interface will require internet access.
-
(Optional) Select the Use proxy server for communication check box to enable nZTA to Controller communication via proxy server. Proxy is supported on both internal and management interfaces of the Gateway. Once enabled, enter host name and port. Optionally, if your proxy server requires further authentication, enter a username and password to log in to the proxy server.
Admin can configure proxy for existing Gateway after upgrading it to 22.4R3 version or later.
-
Enter the Primary DNS IP address for the Gateway.
-
(Optional) Enter the Secondary DNS IP address for the Gateway.
-
Enter the DNS Search Domain for the Gateway.
Make sure the specified DNS service can resolve the IP address of your Controller. Issues here can cause registration of the Gateway with the Controller to fail.
-
To add a Gateway definition based on the settings you specified in this dialog, select Create Configuration.
After you complete this process, an unregistered Gateway record is created on the Controller. You can view this Gateway record on the Gateways > Gateways List page.
-
On the Gateways List page, select your new Gateway and click the Download icon to obtain a copy of the Gateway definition file.
Retain this file for a later step.
The Gateway definition file is valid for 24 hours. If this period expires, you must replace the Gateway to generate a new Gateway definition file.
-
(Optional) If you have not yet downloaded the latest version of your Gateway VM file, click the Download icon and select Download gateway VM image. Save the archive file and unpack to a local workstation. Make sure the resulting file set is accessible from the AWS Management Console.
-
Access the AWS Management Console and log in using your AWS credentials.
-
In the AWS Services menu, select CloudFormation.
The CloudFormation home page appears.
-
Click Create Stack and then, from the sub-menu, select With new resources (standard).
The Specify template step of the Create Stack wizard appears.
-
Under Prerequisite - prepare template, select the Template is ready option.
-
Under Specify Template, select the Upload a template file template source option.
-
Under Upload a template file, click Choose File and select the Gateway template file that you downloaded at the start of this process.
The file uploads, and the AWS S3 URL for the uploaded template file appears automatically.
-
Click Next.
The Specify stack details step of the Create Stack wizard appears. This page displays the details and parameters required by the Gateway template.
-
Enter a Stack name.
-
Specify the parameters as appropriate for your deployment:
- If you are deploying the Gateway instance into a new VPC, you can accept the default values used for all parameters.
- If you are deploying the instance into an existing VPC, you must manually specify the details of your existing VPC into the parameters on the page. For more information, contact Technical Support.
-
Under nZTA Configuration, identify the required Gateway AMI using its nZTA Gateway AMI ID. Choose the designated AMI for the region in which you are deploying the Gateway instance.
-
For Instance Type, select the instance type that fits your hypervisor choice (Nitro) and minimum requirements, based on the following recommended types:
For reference, the recommended minimum requirements for a Gateway virtual machine instance in AWS are:
For Nitro hypervisor-based instances, use M5 types:
- m5.large (2 vCPU, 8 GB Memory) (2NIC min)
- m5.xlarge (4 vCPU, 16 GB Memory) (3NIC min)
- m5.2xlarge (8 vCPU, 32 GB Memory)
- m5.4xlarge (16 vCPU, 64 GB Memory)
-
Under nZTA Config Data, paste in the raw text of the Gateway definition file downloaded earlier.
-
For SSH Key Name, specify your existing SSH key pair name.
-
For Load Balancer Configuration, If you plan to deploy multiple Gateways inside a Gateway Group, select "Yes" to deploy a new internet-facing network load balancer instance alongside the Gateway. Select "No" to launch only this Gateway instance.
This option is applicable only for new VPC templates.
If you elect to launch a load balancer, the following pre-configuration is applied:
- An Elastic IP address is assigned to the load balancer.
- A TCP listener is configured on port 443.
- An IP-based Target Group is created and the private IP address of the deployed Gateway's external network interface is added as a target.
- A health-check is configured on TCP port 443.
- Stickiness is enabled on the Target Group.
After you have deployed the Gateway and Load Balancer, you must return to the Tenant Admin Portal on the Controller and update the Gateway Group Load Balancer IP ADDRESS setting to be the Load Balancer's public IP address.
If you want to configure the Load Balancer to balance across further Gateway instances from the Gateway Group, you must deploy each subsequent Gateway into an existing VPC and then update the Load Balancer Target Group.
With new VPC templates, a NAT gateway is deployed for routing outbound Internet traffic from the Gateway's internal network interface in order for the Gateway to be able to reach the Controller.
Public IP addresses are not automatically assigned to any of your Gateway's network interfaces. If you are deploying a Gateway into an existing VPC, in order for the Gateway to be able to reach the Controller from it's internal network interface, make sure you allow outbound Internet traffic from the Private Subnet for the deployed Gateway.
To learn more about high availability and Gateway Groups, see the Tenant Admin Guide.
-
Click Next.
The Configure stack options step of the Create Stack wizard appears. All properties that were specified either in the template or in earlier steps are populated automatically.
No changes or new inputs are required.
-
Click Next.
-
The Review step of the Create Stack wizard appears.
-
Confirm all displayed details.
-
Click Create stack.
The Stacks page appears. The new stack is listed using the Stack name you specified during the wizard. The new stack has a status of CREATE_IN_PROGRESS.
-
Wait for the status of the new stack to reach CREATE_COMPLETE.
-
(This step is required only if you have not deployed your Gateway with a Load Balancer or NAT at the front-end) Elastic IP addresses are not automatically assigned to any of the Gateway's network interfaces. Therefore, before you can access the new Gateway instance from the Controller, you must associate a new Public IP address with the external interface of the Gateway. Then, return to the Tenant Admin Portal and update the Gateway Public IP Address setting to match this address.
-
In the Tenant Admin Portal Secure Access > Gateways > Gateways List page, locate the new Gateway record and confirm that its Connection Status has updated to Connected.
You can directly access your AWS instance over SSH using AWS EC2 Instance Connect. To configure AWS EC2 Instance Connect, refer to the Amazon Web Service Documentation. You can then connect to the instance directly as a serial console using SSH from inside the AWS Management Console, refer to the Amazon Web Service Documentation.
After you have registered a Gateway, you can configure it (or the Gateway Group to which it belongs) as the default Gateway if required. See the Tenant Admin Guide for details.
Workflow: Creating a Gateway in Microsoft Azure
This workflow leads you through the process for creating and registering a ZTA Gateway in Microsoft Azure. It contains two main procedures, to be completed in sequence:
-
Create the Gateway record in the Controller.
-
Create the Gateway virtual machine instance in Azure and register it with the Controller.
Azure offers two methods for launching a Gateway virtual machine instance:
- Through the Azure Marketplace
- Using the provided template and image files
ZTA Gateway instances in Azure Marketplace is limited to version 21.3R1. To use a Gateway version later than 21.3R1, either launch the Azure Marketplace version and upgrade in-place to the latest version, or use the alternate procedure described below to launch a Gateway instance using the template and image files.
Before you start, make sure you have the following information and files:
-
An identifying name for the Gateway
-
The Gateway geographic location.
-
(Optional) The name of the Gateway Group to which you want to add this new Gateway record. To learn more about Gateway Groups, see the Tenant Admin Guide.
-
The primary (and optional secondary) DNS server IP address, and search domain.
-
The SSH public key that you are using with the Azure Portal or Management Console.
SSH keys can be generated using sshkeygen on Linux and macOS, or PuTTyGen on Windows. For further details about generating SSH key pairs, see:
For Windows: https://docs.microsoft.com/en-us/azure/virtual-machines/linux/ssh-from-windows
For MacOS and Linux: https://docs.microsoft.com/en-us/azure/virtual-machines/linux/mac-create-ssh-keys -
Credentials for the Azure Portal or Management Console.
These credentials must include sufficient permissions to create a virtual machine.
-
A public IP address or CNAME for the Gateway. This is the IP address or CNAME at which client devices can externally reach the Gateway instance.
To create a Gateway record in the Controller, perform the following steps:
-
Log into the Tenant Admin Portal using the credentials provided in your welcome email. Two outcomes are possible:
- On nZTA unconfigured systems, the Secure Access Setup (Onboarding) wizard appears. In this case, click Add Gateway.
- On nZTA configured systems, the Network Overview page
appears. In this case:
From the nZTA menu, click the Secure Access icon, then select Gateways > Gateway List.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller.
To add a new Gateway, select Create from the top-right:
In the drop-down menu, click Create ZTA Gateway.
In both cases, the Gateway Details dialog appears.
To learn more about the settings on this page, see the ICS Tenant Admin Guide.
-
Enter a Name for the Gateway.
-
Enter one or more Public Address or CNAME (Public IP address or CNAME) for the Gateway. Select Add to add each entry to the list.
For Azure Marketplace deployments, a public IP address or CNAME is typically allocated at deployment time through the Azure Portal. Therefore, if you do not yet know the expected address/CNAME, enter a dummy value in this field now and update the setting after you have deployed and registered the Gateway instance. For more details on this process, see
Creating a Gateway through Azure Marketplace. -
Select a geographic Location for the Gateway.
-
For Gateway Platform, select "Azure".
-
(Optional) Select a Gateway Group to which the new Gateway is to be added.
-
(Optional) Select the Use Management Port check box to use management network ports for nZTA traffic rather than internal ports.
When the management port is enabled, the Controller will still use the internal port for DNS resolution. If the internal DNS cannot resolve the Controller domain, the internal interface will require internet access.
-
(Optional) Select the Use proxy server for communication check box to enable nZTA to Controller communication via proxy server. Proxy is supported on both internal and management interfaces of the Gateway. Once enabled, enter host name and port. Optionally, if your proxy server requires further authentication, enter a username and password to log in to the proxy server.
Admin can configure proxy for existing Gateway after upgrading it to 22.4R3 version or later.
-
Enter the Primary DNS IP address for the Gateway.
-
(Optional) Enter the Secondary DNS IP address for the Gateway.
-
Enter the DNS Search Domain for the Gateway.
Make sure the specified DNS service can resolve the IP address of your Controller. Issues here can cause registration of the Gateway with the Controller to fail.
-
To add a Gateway definition based on the settings you specified in this dialog, select Create Configuration.
After you complete the first part of this workflow, an unregistered Gateway record is created on the Controller. This Gateway record can be seen on the Gateways > Gateways List page.
-
On the Gateways List page, select your new Gateway and click the Download icon to obtain a copy of the Gateway definition file.
Retain this file for a later step.
The Gateway definition file is valid for 24 hours. If this period expires, you must replace the Gateway to generate a new Gateway definition file.
-
(Optional) If you have not yet downloaded the latest version of your Gateway VM file, click the Download icon and select Download gateway VM image. Save the archive file and unpack to a local workstation. Make sure the resulting file set is accessible from the Microsoft Azure Console.
Next, decide which Azure deployment process you want to follow - launching an instance through Azure Marketplace, or creating an instance using the supplied template and image files.
- To launch an instance from Azure Marketplace, see
Creating a Gateway through Azure Marketplace. - To create an instance using the nZTA template and image files, see
Configuring Gateways.
Creating a Gateway through Azure Marketplace
ZTA Gateway instances in Azure Marketplace are limited to version 21.3R1 at the
present time. To use a Gateway version later than 21.3R1, either launch
the Azure Marketplace version and upgrade in-place to the latest version
(for more details, see the Tenant Admin Guide) or use the
alternate procedure described in Configuring Gateways
To launch a Gateway virtual machine in Microsoft Azure from the Azure Marketplace, perform the following steps:
-
Log into the Microsoft Azure Portal (http://portal.azure.com).
-
Navigate to the Azure Marketplace by clicking Create a resource.
-
In the Search the Marketplace text box, enter "Ivanti".
Azure Marketplace presents the results relevant to your search term.
-
Locate Ivanti Neurons Zero Trust Access Gateway and click Create.
-
In the drop-down list, choose the option that is applicable to your needs:
- Ivanti Neurons Zero Trust Access Gateway - BYOL 3 NIC: Includes 3 network interfaces (internal, external, and management)
- Ivanti Neurons Zero Trust Access Gateway - BYOL 2 NIC: Includes 2 network interfaces (internal and external)
To first learn more about Ivanti Neurons Zero Trust Access Gateway, click the product banner and view the associated information page. You can launch a new Gateway instance from this page.
The Create Ivanti Neurons Zero Trust Access Gateway process appears.
-
On the Basics tab, enter the following details:
- Subscription: If you are using the "PZT_Dev" subscription, leave this field as the default value. Otherwise, enter your subscription name.
- Resource Group: Specify the resource group in which the Gateway needs to be deployed, or create a new resource group using the link provided. An Azure Resource Group is a container for a collection of connected assets that you assign to a virtual machine. To learn more, see the Azure documentation (https://docs.microsoft.com/azure).
- Region: Specify the geographic region in which the Gateway instance is deployed.
- Ivanti Neurons Zero Trust Access Gateway VM Name: Enter a suitable name for your Gateway instance. This name must be 1-9 characters long, using only lowercase letters or numbers.
- SSH Public Key Source: Select "Use existing public key".
- SSH Public Key: Copy and paste an RSA public key in a single-line format or the multi-line PEM format.
SSH keys can be generated using sshkeygen on Linux and macOS, or PuTTyGen on Windows. For further details about generating SSH key pairs, see:
For Windows: https://docs.microsoft.com/en-us/azure/virtual-machines/linux/ssh-from-windows
For MacOS and Linux: https://docs.microsoft.com/en-us/azure/virtual-machines/linux/mac-create-ssh-keysTo continue, click Next: Network Settings >.
-
On the Network Settings page, enter the following details:
-
Virtual Network: A virtual network is a logical isolation of the Azure cloud dedicated to your services. The value you enter here affects the IP address and subnet allocations for all network interfaces shown on this page. Azure pre-populates this field with a new virtual network name, although you can select your own predefined virtual network as necessary.
To create a new virtual network, perform the following steps:
-
Click the Create New link under the Virtual Network setting.
The Create virtual network dialog appears.
-
Enter a virtual network name.
-
Enter an address space in CIDR notation (for example, 192.0.2.0/24).
-
For each interface subnet, use the automatically-populated name and address values provided, or enter your own details. Each subnet must be contained by the address space entered in the previous setting.
-
To save your changes, click OK.
Your new virtual network settings are populated into the corresponding interface settings in the main Network Settings page.
-
-
Internal Subnet: The subnet identifier for the Internal network, pre-populated by either the selected Virtual Network or your newly-entered virtual network settings.
-
External Subnet: The subnet identifier for the External network, pre-populated by either the selected Virtual Network or your newly-entered virtual network settings.
-
(For 3 NIC instances only) Management Subnet: The subnet for the Management network, pre-populated by either the selected Virtual Network or your newly-entered virtual network settings.
-
Public IP for Ivanti Neurons Zero Trust Access Gateway external interface LB: The public IP address identifier at which clients can externally reach the Gateway instance, typically provided by Azure.
Before you can connect to the new Gateway instance from the Controller, you must update the Controller with the Public IP address or CNAME assigned to the external interface of the Gateway load balancer. This process is described later.
-
DNS prefix for external interface LB: The unique DNS name for the public IP address specified for the external interface load balancer.
-
Public IP for NAT Gateway: The public IP address identifier of a NAT Gateway for the virtual machine to communicate with the Controller and other public resources.
-
DNS prefix for NAT Gateway public IP: The unique DNS name for the public IP address specified for the internal interface NAT Gateway.
-
Deploy Ivanti Neurons Zero Trust Access Gateway with Load Balancer: To deploy this Gateway with a load balancer, select "Yes" from the drop-down list. The front-end IP address of the load balancer is then used as the public IP address for your Gateway.
If you select "No" to not deploy a load balancer, you must create and associate a public IP address to the external interface of your instance after deployment is complete.
In all cases, on completion of this process, you must update the Controller Gateway definition with the correct public IP address for your Azure Gateway instance.
To continue, click Next: Instance Configuration >.
-
-
On the Instance Configuration page, enter the following details:
- Ivanti Neurons Zero Trust Access Gateway VM Size:
This is the specification of the virtual machine. Choose from:
- For 2nic instances, select "1 x Standard DS2 v2"
- For 3nic instances, select "1 x Standard DS4 v2"
- Diagnostic storage account: The storage account for the virtual machine diagnostics. The default value is a new account based on your VM name.
- Ivanti Neurons Zero Trust Access Gateway Version: Specify the version applicable to the current nSA version, or the version you require. Ivanti recommends you select the latest available version.
- Ivanti Neurons Zero Trust Access Gateway Config Data: Paste in the raw text of your Gateway definition file. To obtain the Gateway definition file, see the process described earlier in this section.
To continue, click Next: Review + create >.
- Ivanti Neurons Zero Trust Access Gateway VM Size:
This is the specification of the virtual machine. Choose from:
-
On the Review + create page, verify the proposed configuration is validated successfully, and then click Create to create your new Gateway instance.
After a short wait, your instance is created and deployed.
-
Access the virtual machine settings for your new Gateway instance, and click Networking from the Settings menu.
The Networking dialog appears, showing your attached network interfaces (internal, external, and (optionally) management).
-
Click the tab that corresponds to the external network interface.
The settings for the external network interface appear.
-
Locate the NIC Public IP field and make a note of the IP address shown there. This is the public IP address you use to reconfigure the Controller record for this Gateway.
If no public IP address is shown, determine if a load balancer was deployed together with your Gateway instance by selecting the Load balancing tab.
- If a load balancer was deployed, make a note of the Frontend IP address displayed in this tab and use this as the Gateway public IP address on the Controller.
- If a load balancer was not deployed, create a public IP address and associate it with the external interface. Then, use this IP address as the Gateway public IP address on the Controller.
To learn about configuring IP addresses in the Azure portal, see the Microsoft Azure documentation.
-
Return to the nZTA Tenant Admin Portal, and click Secure Access > Gateways > Gateways List.
The Gateways List page appears.
-
Make sure the new Azure Gateway instance is shown in the list of configured Gateways and is connected (Connection Status is Connected).
-
Select the new Gateway, then select Secure Access > Gateways > Configuration and locate Gateway Network Settings. Enter the Public IP address you noted from the Azure virtual machine settings. Make sure you remove any previously-entered dummy values.
-
To save your changes, click Save Changes.
This completes the Azure Gateway registration process. Your enrolled client devices should now be able to connect to the Gateway.
Workflow: Creating a Gateway in KVM/OpenStack
For 22.7R1.3 release, 22.7R2.2 ZTA Gateway version is not supported with Oracle, AWS, and KVM platforms.
This workflow leads you through the process for setting up a KVM Gateway in OpenStack. It contains two main procedures, in sequence:
- Preparing to create a KVM gateway, see
Preparing to Create a KVM Gateway. - Creating the gateway record in the Controller, see
Adding a KVM Gateway in nSA. - Preparing Metadata for OpenStack, see
Preparing Metadata for OpenStack. - Creating the KVM Gateway virtual machine instance in OpenStack, see
Creating the KVM Gateway Virtual Machine Instance in OpenStack.
After these steps have been completed successfully, the Controller and Gateway establish communication with each other.
Preparing to Create a KVM Gateway
Before you start, make sure you have the following information and files:
- An identifying name for the Gateway
- The public IP address for the Gateway. This is the IP address at which clients can externally reach the Gateway instance.
- The Gateway geographic location
- (Optional) The name of the Gateway Group to which you want to add this new Gateway record. To learn more about Gateway Groups, see the Tenant Admin Guide.
Additionally, to manually specify KVM Gateway network interface settings:
-
The primary (and optional secondary) DNS server IP address, and search domain.
-
The required internal/private subnetworks must already be defined on OpenStack. Please refer to the OpenStack documentation for details.
-
The required external subnetworks must already be defined on OpenStack. Please refer to the OpenStack documentation for details.
-
(Optional) Any required management subnetwork must already be defined on OpenStack. Please refer to the OpenStack documentation for details.
-
Credentials for the OpenStack Console.
These credentials must include sufficient permissions to create a virtual machine from a template image.
After you have all required information, you can set up a nZTA KVM
gateway, see Adding a KVM Gateway in nSA.
Adding a KVM Gateway in nSA
To set up a nZTA KVM Gateway, perform the following steps:
-
Log into the Tenant Admin Portal using the credentials provided in your welcome email. Two outcomes are possible:
- On nZTA unconfigured systems, the Secure Access Setup (Onboarding) wizard appears. In this case, click Add Gateway.
- On nZTA configured systems, the Network Overview page
appears. In this case:
From the nZTA menu, click the Secure Access icon, then select Gateways > Gateway List.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller .
To add a new Gateway, select Create from the top-right:
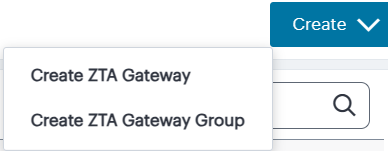
In the drop-down menu, click Create ZTA Gateway.
In both cases, the Gateway Details dialog appears.
To learn more about the settings on this page, see the Tenant Admin Guide.
-
Enter a Name for the Gateway.
-
Enter one or more Public Address or CNAME (Public IP address or CNAME) for the Gateway. Select Add to add each entry to the list.
-
Select a geographic Location for the Gateway.
-
For Gateway Platform, select "KVM".
-
(Optional) Select a Gateway Group to which the new Gateway is to be added.
-
(Optional) Select the Use Management Port check box to use management network ports for nZTA traffic rather than internal ports.
When the management port is enabled, the Controller will still use the internal port for DNS resolution. If the internal DNS cannot resolve the Controller domain, the internal interface will require internet access.
-
(Optional) Select the Use Dynamic Tunnel IP check box to configure a pool of IP addresses that are dynamically mapped to client sessions with this Gateway, such that user traffic from the Gateway to an application can be identified as originating from a specific client.
The Custom IP Pool dialog appears:
Dynamic Tunnel IP addresses are not supported in Gateway Groups.
Use the Assignable Custom IPv4 Address field to enter an IP address and subnet (in the range 8-28) in CIDR notation, then click Add. Repeat this step for each address/subnet you want to use.
-
(Optional) Select the Use proxy server for communication check box to enable nZTA to Controller communication via proxy server. Proxy is supported on both internal and management interfaces of the Gateway. Once enabled, enter host name and port. Optionally, if your proxy server requires further authentication, enter a username and password to log in to the proxy server.
Admin can configure proxy for existing Gateway after upgrading it to 22.4R3 version or later.
-
Enter the Primary DNS IP address for the Gateway.
-
(Optional) Enter the Secondary DNS IP address for the Gateway.
-
Enter the DNS Search Domain for the Gateway.
Make sure the specified DNS service can resolve the IP address of your Controller. Issues here can cause registration of the Gateway with the Controller to fail.
-
To add a Gateway definition based on the settings you specified in this dialog, select Create Configuration.
After you complete the first part of this workflow, an unregistered Gateway record is created on the Controller. This Gateway record can be seen on the Gateways > Gateways List page.
You can now prepare your metadata, see Preparing Metadata for OpenStack.
Preparing Metadata for OpenStack
The preparation of metadata for use on OpenStack currently requires some manual steps:
-
Log into and nZTA access the Gateways > Gateways List page.
-
On the Gateways List page, select your new Gateway and click the Download icon to obtain a copy of the Gateway definition file.
-
Specify a save location for your Gateway definition file.
The Gateway definition file is valid for 24 hours. If this period expires, you must replace the Gateway to generate a new Gateway definition file.
-
(Optional) If you have not yet downloaded the latest version of your Gateway VM file, click the Download icon and select Download gateway VM image. Save the archive file and unpack to a local workstation. Make sure the resulting file set is accessible from the OpenStack Management Console.
-
View the gateway definition file in a text editor.
-
Start a separate text editor file, and paste the following template text block into it:
<pulse-config> <config-download-url> '<insert vaConfigURL value here>' </config-download-url> <appliance-id> <insert vaApplianceID value here> <secondary-dns> <insert vaSecondaryDNS here> </secondary-dns> <primary-dns> <insert vaPrimaryDNS here> </primary-dns> <dns-domain> <insert vaDnsSearchDomain here> </dns-domain> </appliance-id> <cert-common-name> <insert vaCommonName value here> </cert-common-name> <accept-license-agreement> y </accept-license-agreement> <controller-enrolled-hostname> <insert vaControllerEnrolledHostname value here> </controller-enrolled-hostname> <dns-search-domain> <insert vaDnsSearchDomain value here> </dns-search-domain> <controller-hostname> <insert vaControllerHostname value here> </controller-hostname> </pulse-config> -
For each parameter block in the template text block file:
-
Locate the required metadata property for the line.
For example, in the following block:
<appliance-id> <insert vaApplianceID value here> </appliance-id>You require the vaApplianceID value from the gateway definitions file.
-
Locate the required value in the gateway definitions file.
For example, the vaApplianceID value is 99ce3aa3c9494cbabb51c085c9c3f6ad.
-
Copy and paste this value from the gateway definitions file into the template text file.
For example, the <appliance-id> block will now read as follows:
<appliance-id> 99ce3aa3c9494cbabb51c085c9c3f6ad </appliance-id>
You do not need to change the <accept-license-agreement> block, and can retain its y setting.
-
-
After you have added all required text to the template text file, save that file for use in the next section.
You can now create a KVM gateway VM in Openstack, see Creating the KVM Gateway Virtual
Machine Instance in OpenStack.
Creating the KVM Gateway Virtual Machine Instance in OpenStack
To create a KVM VM instance in OpenStack:
-
Access the OpenStack Management Portal, either from a client or a web browser, and log in using your OpenStack credentials.
In the OpenStack console, the Overview page appears.
-
In the left menu, click Compute > Images.
The Images page appears. This shows a list of images.
-
Above the list of images, click Create Image.
The Create Image wizard appears. In this wizard, you upload a KVM gateway image for use.
-
Under Image Details:
- Enter an Image Name. Typically, this incorporates a version number. For example, ZTA_GWY_100.
- Enter an Image Description. For example: ZTA KVM Image.
- Under Image Source, click Browse and select the unpacked KVM disc image file. Then, click Format and select QCOW2 - QEMU Emulator.
- Under Image Requirements, set Minimum Disk (GB) to 40 and Minimum RAM (KB) to 2048.
- Set Visibility Setting as required. Public will enable the image to be used in other projects. Private will not.
- Set Image Sharing as required.
- Use the default settings for all other properties.
-
Click Next.
The Metadata page of the wizard appears. No action is required on this page, all properties can use their default settings.
-
Click Create Image.
The wizard closes, and the new KVM gateway image is added to the Images page.
-
Wait until the image has been uploaded and processed and shows as Active.
The upload image process typically takes 15-20 minutes.
-
After the image has uploaded and is Active, click its Launch button.
The first page of the Launch Instance wizard appears. In this wizard, you create a KVM gateway instance.
-
Under Details:
- Enter an Instance Name. This will be the displayed name of the gateway in nZTA.
- Enter a Description for the KVM gateway. For example ZTA KVM Gateway.
- Use the default settings for all other properties.
-
Click Next.
The Source page of the wizard appears. This page lists the selected disk image and selected/default settings for the instance. No action is required on this page, all properties can use their displayed settings.
-
Click Next.
The Flavor page of the wizard appears. This page lists the available types of gateway you can create.
-
Locate the ISA4000-V entry and click its "up arrow" button to select it.
-
Click Next.
The Networks page of the wizard appears. This page lists the available networks (and associated subnetworks) for the gateway. It enables you to select the required subnetworks for your gateway.
-
In the available list, locate the required subnetworks.
For example, you may require a subnetwork for internal ports and a subnetwork for external ports, but not a subnetwork for management interfaces.
If the required subnetworks do not yet exist, you must define them. Please refer to the OpenStack documentation for details of this process.
-
Click the "up arrow" button for each subnetwork to select it.
For each selected subnetwork, a fixed IP address is added automatically to the gateway. These appear later in this process, so that they can be assigned to floating IP addresses.
-
Click Next.
The Network Ports page of the wizard appears. No action is required on this page, all properties can use their displayed settings.
-
Click Next.
The Security Groups page of the wizard appears. No action is required on this page, all properties can use their displayed settings.
-
Click Next.
The Security Groups page of the wizard appears. No action is required on this page, all properties can use their displayed settings.
If there is no default security group defined, you must define one. Please refer to the OpenStack documentation for details of this process.
-
Click Next.
The Key Pair page of the wizard appears. No action is required on this page, all properties can use their displayed settings.
-
Click Next.
The Configuration page of the wizard appears. This page enables you to configure the gateway instance using metadata you prepared earlier, see
Adding a KVM Gateway in nSA -
Open your template text file and copy the entire text block that starts with
<pulse-config>and ends with</pulse-config>. -
Paste the text block into the Customization Script block.
You cannot directly paste metadata for your gateway from nZTA. You must prepare a suitable text block from the metadata, see
Adding a KVM Gateway in nSA -
Enable the Configuration Drive check box.
-
Click Launch Instance.
The wizard closes, and the new KVM gateway instance is added.
-
Access the Instances page.
The new KVM gateway instance is listed on this page.
-
Wait until the Power State of the gateway instance is Running.
This process may take several minutes.
-
After the instance state changes to Running, make a note of the subnetworks and their automatically-assigned fixed IP addresses in the IP Address column for the instance. For example:
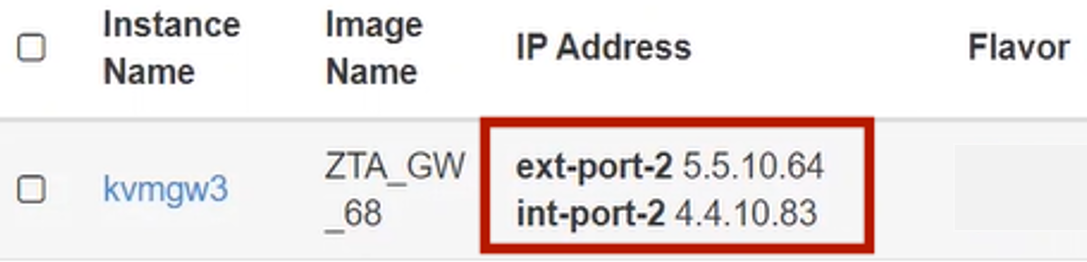
In this example, floating IP addresses are listed after the fixed IP addresses, so all are unassociated:
- The fixed IP address on the int-port-2 subnetwork is 4.4.10.83.
- The fixed IP address on the ext-port-2 subnetwork is 5.5.10.64.
-
Access the Network > Floating IPs page.
The Floating IPs page shows the floating IP addresses associated with your account. Both associated and unassociated floating IP addresses are listed.
Associated floating IPs have a Mapped Fixed IP Address listed.
-
Identify an unassociated floating IP address that you want to associate with a fixed IP address.
-
Click the Associate button for the fixed IP address.
The Manage Floating IP Associations dialog appears.
-
Select a fixed port to be associated for the selected floating IP address.
-
Click Associate to conform the association.
-
Repeat the association process until each of the fixed IP addresses for your gateway instance is associated with a floating IP address.
-
Wait until the status of these floating IP addresses all show as Active.
-
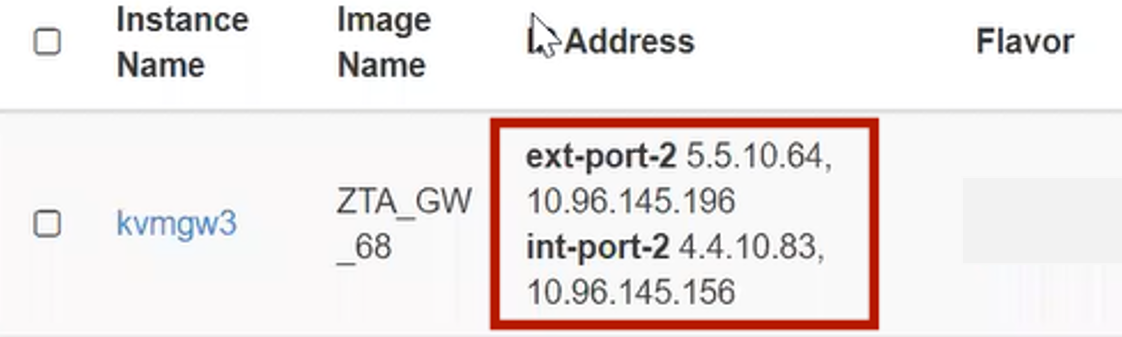
Return to the Compute > Instances page.
This page now shows a fixed IP address associated with floating IP address for each port. For example:
-
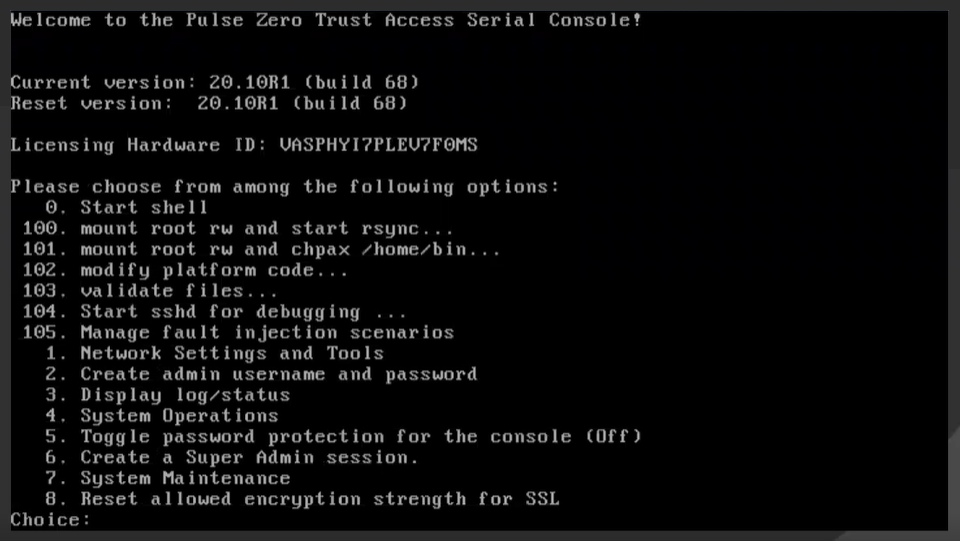
Click the Console tab.
A console monitor view shows the ongoing boot-up process for the instance.
-
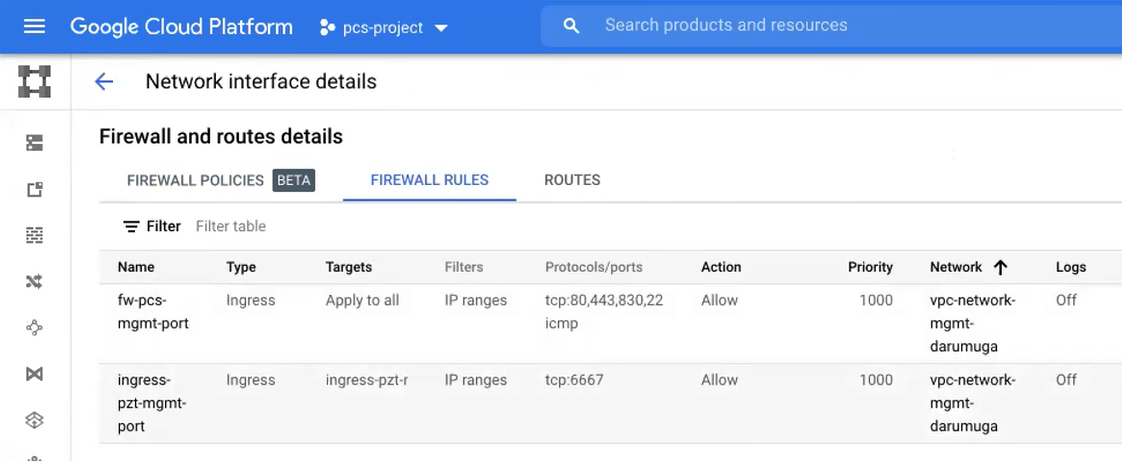
Wait until the instance shows a screen similar to the following:
-
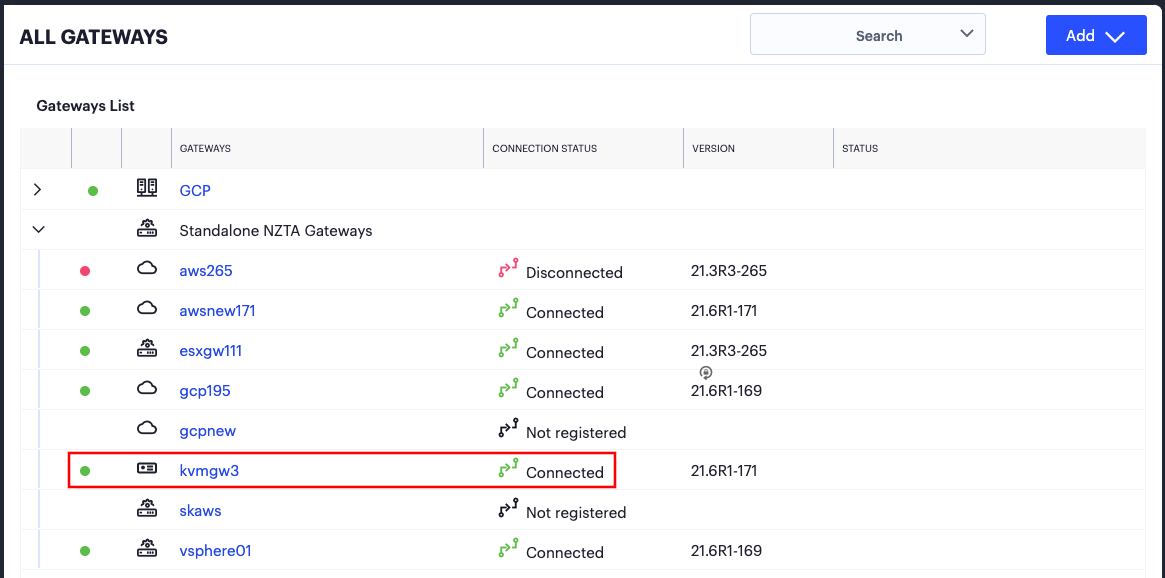
Return to the Gateways List page on the Controller .
-
Locate the new Gateway record in the list and confirm that its status has updated to Connected. For example:
After you have registered a Gateway, you can configure it (or the Gateway Group to which it belongs) as the default Gateway if required. See the ICS Tenant Admin Guide for details.
Workflow: Creating a Gateway in Google Cloud Platform
This workflow leads you through the processes for setting up a Gateway on the Google Cloud Platform (GCP). These processes must be performed in sequence:
- Preparing to create a GCP gateway, see
Preparing to Create a GCP Gateway. - Creating the gateway record in the Controller, see
Adding a GCP Gateway in nSA. - Downloading Metadata for Google Cloud Platform, see
Downloading Metadata for Google Cloud Platform. - Uploading the GCP Image onto the Google Cloud Platform, see
Uploading the GCP Virtual Machine Image onto the Google Cloud Platform. - Creating a VM Instance of the GCP image. Either:
- Creating a VM Instance of the Uploaded GCP Image Manually, see
Creating a VM Instance of the Uploaded GCP Image Manually. - Creating a VM Instance of the Uploaded GCP Image Using a
Script/Template, see
Creating a VM Instance of the Uploaded GCP Image Using a Script/Template.
- Creating a VM Instance of the Uploaded GCP Image Manually, see
- Completing the Configuration of the Controller, see
Completing the Configuration of the Controller.
After these steps have been completed successfully, the Controller and Gateway establish communication with each other.
Preparing to Create a GCP Gateway
Before you start, make sure you have the following information and files:
-
An identifying name for the Gateway.
-
The public IP address for the Gateway. This is the IP address at which clients can externally reach the Gateway instance, such as an LB/NAT or Datacenter network forward rules.
If you want Google Cloud platform to allocated a public IP address automatically, you can use a dummy IP address (for example, 1.1.1.1) when you create the Gateway on nZTA. You must then update the with the Controller allocated public IP address afterwards.
-
The Gateway geographic location.
-
(Optional) The name of the Gateway Group to which you want to add this new Gateway record. To learn more about Gateway Groups, see the Tenant Admin Guide.
A Gateway Group may have a defined public IP address, which you can specify during the creation of the Gateway.
Additionally, to manually specify GCP Gateway network interface settings:
-
The primary (and optional secondary) DNS server IP address, and search domain.
-
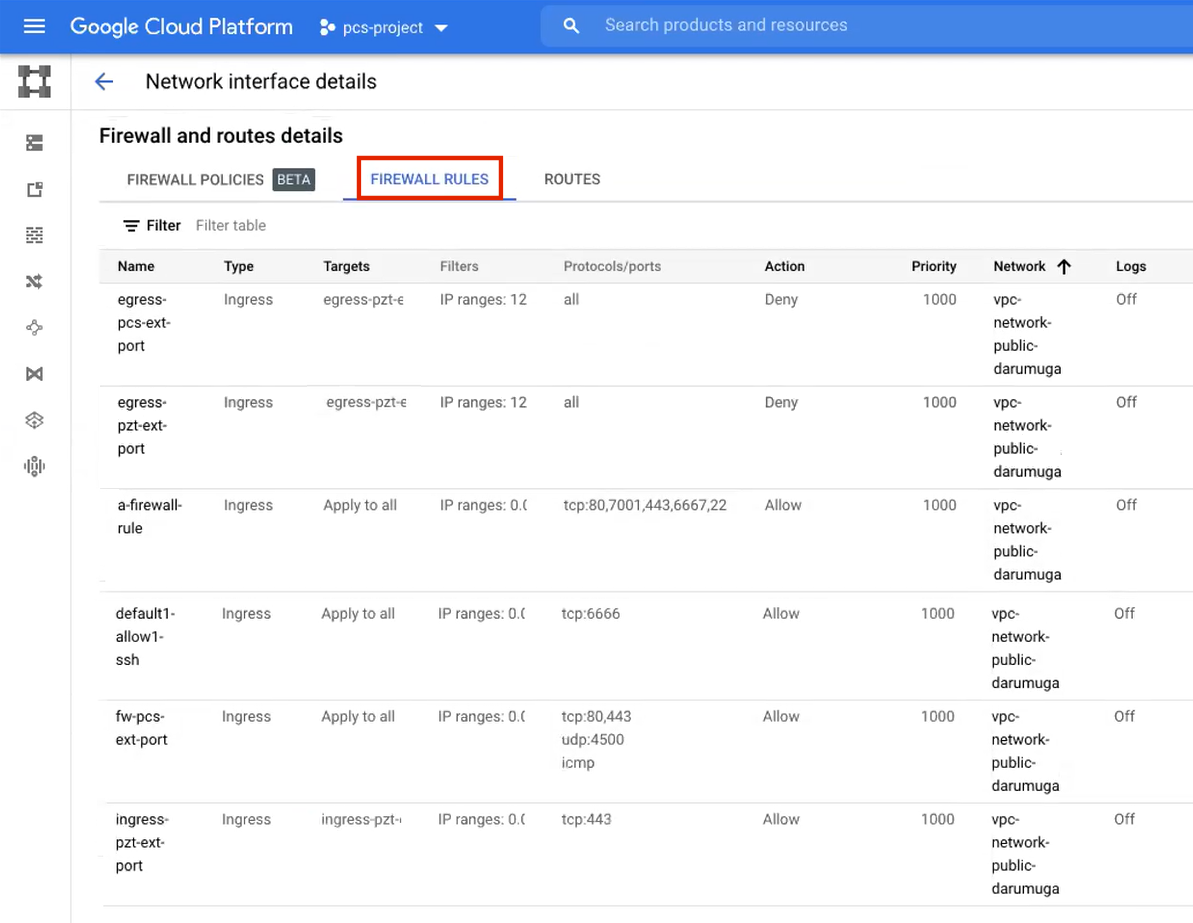
The required internal/private subnetworks must already be defined on Google Cloud Platform, including firewall settings. All required firewall settings for this interface are shown below.
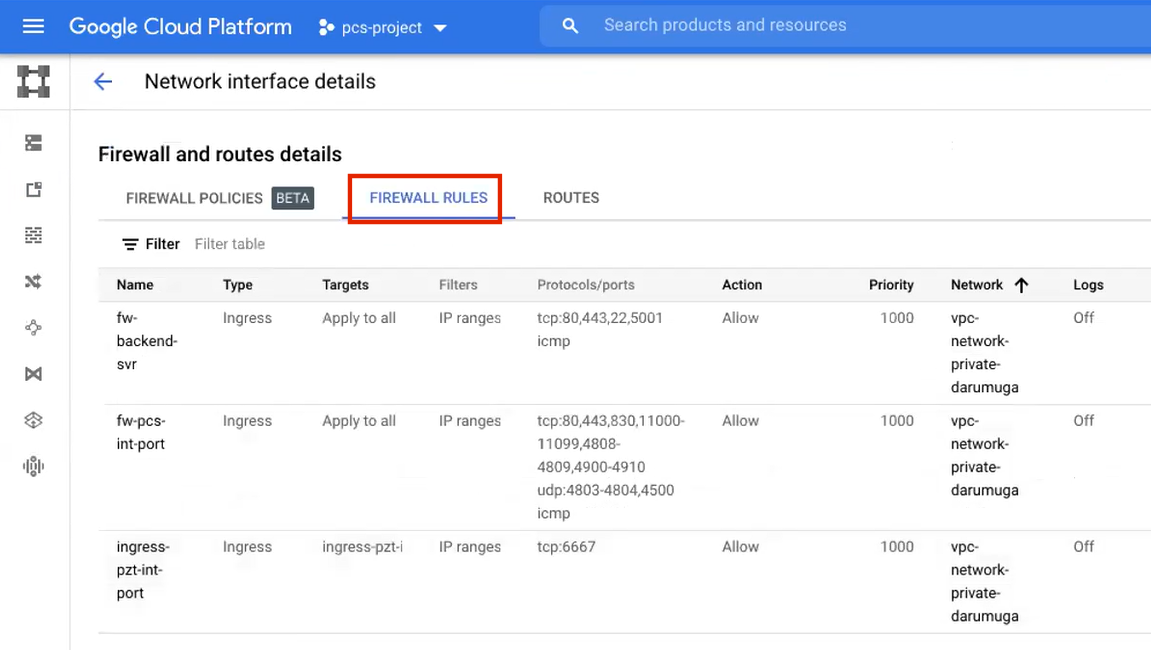
Refer to the Google Cloud Platform documentation for details.
-
The required external/public subnetworks must already be defined on Google Cloud Platform, including firewall settings. All required firewall settings for this interface are shown below.
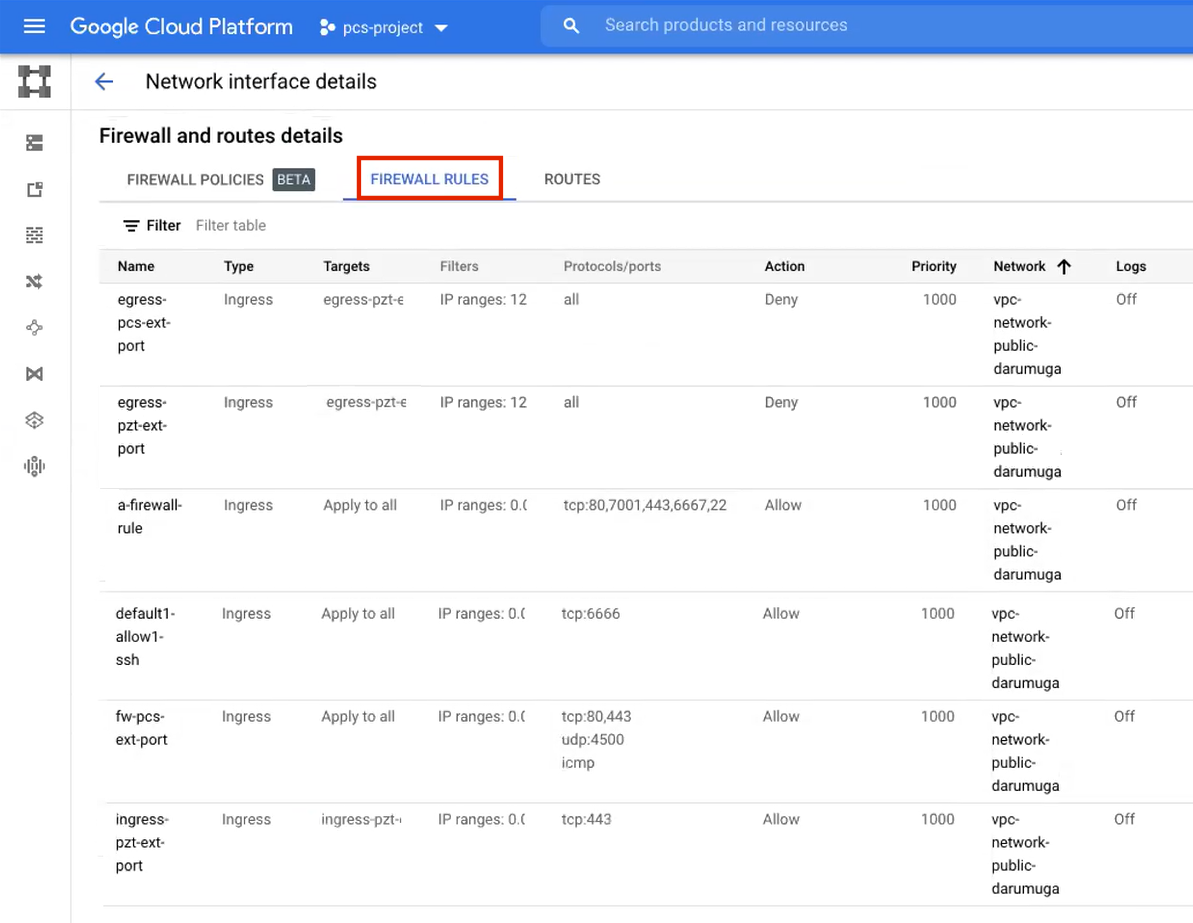
Refer to the Google Cloud Platform documentation for details.
-
(Optional) Any required management subnetwork must already be defined on Google Cloud Platform, including firewall settings. All required firewall settings for this interface are shown below.
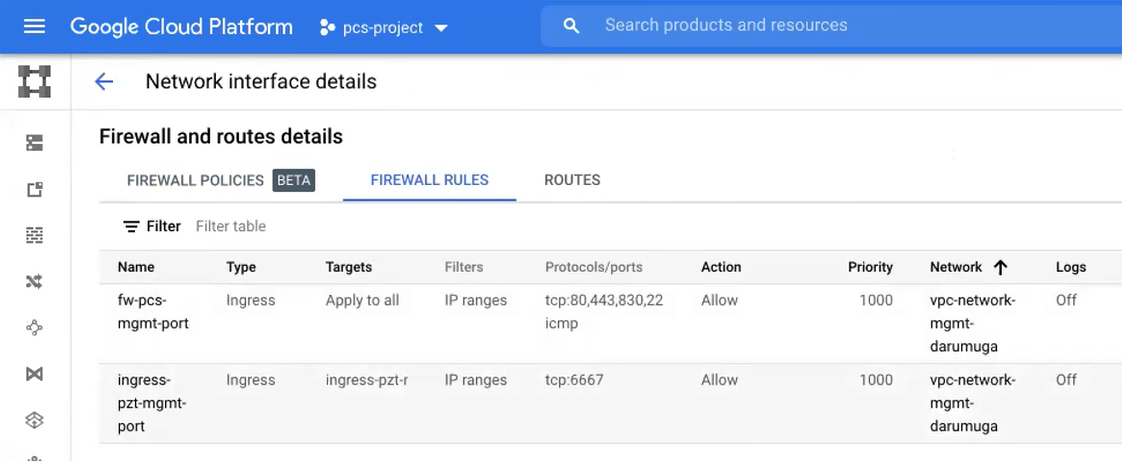
Refer to the Google Cloud Platform documentation for details.
-
Credentials for the Google Cloud Platform Console.
These credentials must include sufficient permissions to create a virtual machine from a template image.
After you have all required information, you can set up a nZTA GCP
gateway, see Adding a GCP Gateway in nSA.
Adding a GCP Gateway in nSA
To set up a nZTA GCP Gateway, perform the following steps:
-
Log into the Tenant Admin Portal using the credentials provided in your welcome email. Two outcomes are possible:
- On nZTA unconfigured systems, the Secure Access Setup (Onboarding) wizard appears. In this case, click Add Gateway.
- On nZTA configured systems, the Overview of Network page
appears. In this case:
From the nZTA menu, click the Secure Access icon, then select Gateways > Gateway List.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller .
To add a new Gateway, select Create from the top-right:
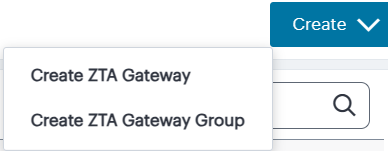
In the drop-down menu, click Create ZTA Gateway.
In both cases, the Gateway Details dialog appears.
To learn more about the settings on this page, see the ICS Tenant Admin Guide.
-
Enter a Name for the Gateway.
-
Enter one or more Public Address or CNAME (Public IP address or CNAME) for the Gateway. Select Add to add each entry to the list.
If you want Google Cloud Platform to allocate a public IP address automatically, you can use a dummy IP address (for example, 1.1.1.1) at this point. You must then update the Controller with the allocated public IP address after the GCP VM instance is created.
-
Select a geographic Location for the Gateway.
-
For Gateway Platform, select "Google Cloud Platform".
-
(Optional) Select a Gateway Group to which the new Gateway is to be added.
A Gateway Group may have a defined public IP address, which you can specify as the Public Address, see above.
-
(Optional) Select the Use Management Port check box to use management network ports for nZTA traffic rather than internal ports.
When the management port is enabled, the Controller will still use the internal port for DNS resolution. If the internal DNS cannot resolve the Controller domain, the internal interface will require internet access.
-
(Optional) Select the Use proxy server for communication check box to enable nZTA to Controller communication via proxy server. Proxy is supported on both internal and management interfaces of the Gateway. Once enabled, enter host name and port. Optionally, if your proxy server requires further authentication, enter a username and password to log in to the proxy server.
Admin can configure proxy for existing Gateway after upgrading it to 22.4R3 version or later.
-
Enter the Primary DNS IP address for the Gateway.
-
(Optional) Enter the Secondary DNS IP address for the Gateway.
-
Enter the DNS Search Domain for the Gateway.
Make sure the specified DNS service can resolve the IP address of your Controller. Issues here can cause registration of the Gateway with the Controller to fail.
-
To add a Gateway definition based on the settings you specified in this dialog, select Create Configuration.
By completing the Gateway Details workflow, an unregistered Gateway record is created on the Controller. You can view this Gateway record on the Gateways > Gateways List page.
You can now download your metadata, see Downloading Metadata for Google Cloud
Platform.
Downloading Metadata for Google Cloud Platform
The preparation of metadata for use on Google Cloud Platform currently requires some manual steps:
-
Log into nZTA and access the Gateways > Gateways List page.
-
Select your GCP Gateway and click the Download icon to obtain a copy of the Gateway definition file.
-
Specify a save location for your Gateway definition file.
The Gateway definition file is valid for 24 hours. If this period expires, you must replace the Gateway to generate a new Gateway definition file.#
-
(Optional) If you have not yet downloaded the latest version of your Gateway VM image and optional YAML templates, click the Download icon and select Download gateway VM image. Save the archive file and unpack to a local workstation. Make sure the resulting file set is accessible from the Google Cloud Platform Management Portal.
You can now create a GCP gateway VM in Google Cloud Platform, see
Uploading the GCP Virtual Machine Image
onto the Google Cloud Platform.
Uploading the GCP Virtual Machine Image onto the Google Cloud Platform
To upload a GCP Gateway virtual machine image into Google Cloud Platform:
-
Access the Google Cloud Platform Management Portal, either from a client or a web browser, and log in using your Google Cloud Platform credentials.
-
In the Google Cloud Platform console, select your required project from the pull-down list on the title bar. For example:

-
Click the Navigation menu, and then select Cloud Storage > Browser.
A list of GCP storage buckets appears.
-
Select the bucket into which you wish to place the GCP image.
A page listing the current contents of the bucket appears.
-
(Optional) Navigate to the required folder within the bucket.
-
Click Upload Files. For example:
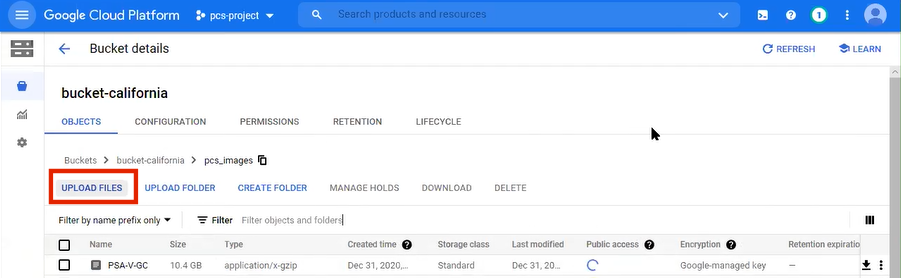
An upload dialog appears.
-
Select the ZTA Gateway GCP virtual machine image .tar file from your local workstation (see Preparing to Create a GCP Gateway), and click Open.
If you want to use the provided YAML templates to automate the creation of your VM instance (see
Creating a VM Instance of the Uploaded GCP Image Using a Script/Template), select these in addition to the image archive.The image archive and any selected template files are added to the bucket.
-
Wait until the upload completes. This may take several minutes.
-
Start a command line session from the title bar. For example:
A command line session starts.
-
Navigate to the project folder.
-
Create an image from the ZTA Gateway image archive using the following command:
gcloud compute images create <instance_name> --source-uri=gs://<bucket_name>/<optional_path>/<image_name>.tar --guest-os-features MULTI_IP_SUBNET
You can now create a VM instance of the uploaded GCP image. To do this, either:
- Perform the task manually, see
Creating a VM Instance of the Uploaded GCP Image Manually. - Perform the task with a script/template, see
Creating a VM Instance of the Uploaded GCP Image Using a Script/Template.
Creating a VM Instance of the Uploaded GCP Image Manually
This section describes how to manually create a virtual machine
instance of the ZTA Gateway image inside Google Cloud Platform. You can also perform
this process automatically using a script/template, see Creating a VM Instance of the
Uploaded GCP Image Using a Script/Template
-
Click the Navigation menu, and then select Compute Engine > Images.
The Images page appears. For example:
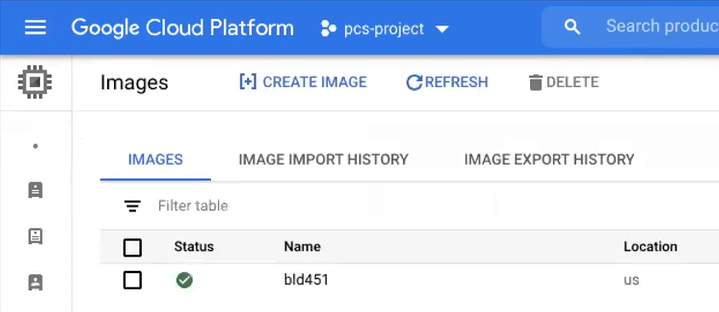
-
Locate the new image in the list of images.
-
At the end of the image entry, click the action menu and select Create Instance.
The Create Instance page appears. For example:
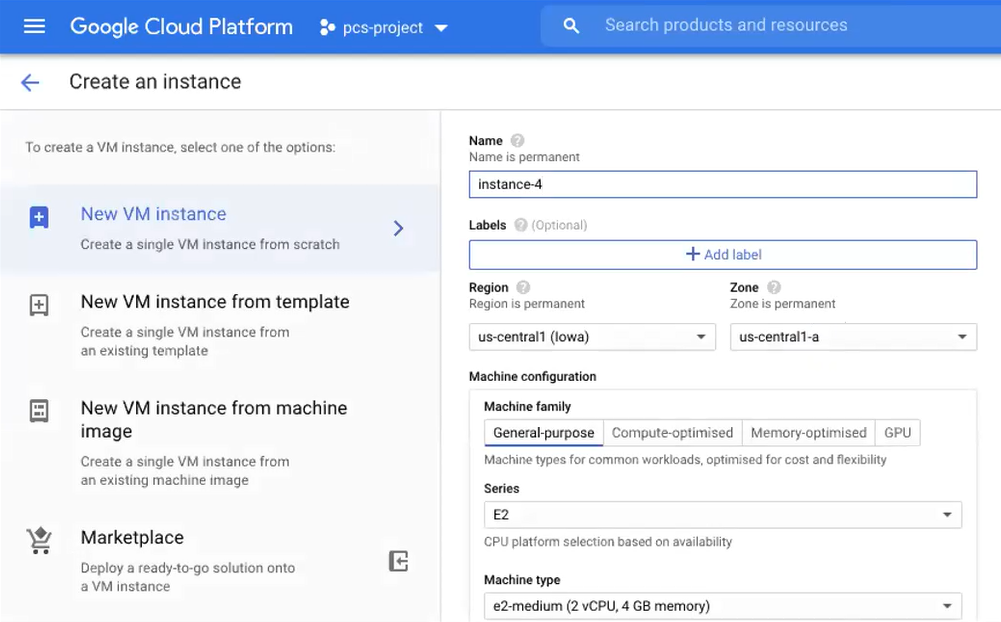
-
On the Create Instance page:
-
Enter a Name for the new instance.
-
Select a Region and Zone.
-
Under Machine configuration:
- For Series, select N1.
- For Machine Type, select a minimum of n1-standard-2.
- For Boot Disk, confirm that the correct image is already selected.
- For Firewall, select the required HTTP/HTTPS options.
-
Expand the Management, security, disks, networking, sole tenancy options.
-
Select the Management tab.
-
Under Metadata:
- For Key, enter pulse-config.
- For Value, paste the text of the metadata file you downloaded earlier.
-
Select the Networking tab.
-
Under Network interfaces, click the Edit icon to change the default network interface selection.
The Network interface options appear.
-
Under Network interface, specify a private (internal) network interface:
- For Network, select the required private VPC.
- For Subnetwork, select the required subnetwork.
- Click Done to confirm the settings for the private network interface.
-
Under Network interfaces, click Add network interface.
The Network interface options appear.
-
Under Network interface, specify a public (external) network interface:
- For Network, select the required public VPC.
- For Subnetwork, select the required subnetwork.
- Click Done to confirm the settings for the public network interface.
-
(Optional) Click Add network interface and specify a management network interface.
-
Click Create to confirm the settings and instantiate a VM instance of the image.
The VM Instances page appears. This page shows the new VM instance of the image. For example:
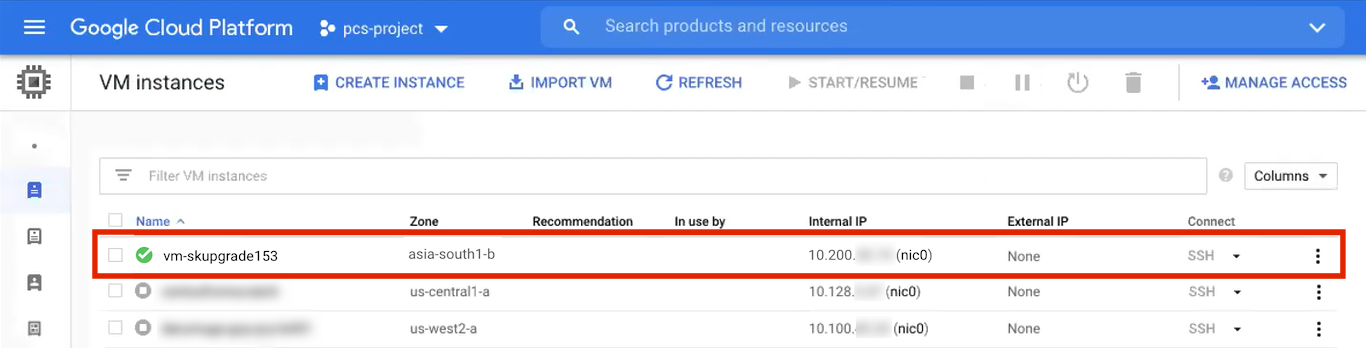
-
-
On the VM Instances page, wait until the creation of the VM instance completes. This may take several minutes.
-
After the VM instance is created, click on it in the list of VM instances.
The VM instance details page appears for the instance.
-
Confirm the details for the VM instance, including the number of network interfaces.
-
Make a note of the public IP address of the EXT interface (typically, this is nic1. This is required inside nZTA.
-
Under Network interfaces, confirm that the firewall settings from your VPCs are present for your specified network interfaces:
-
Click nic0. A summary page for this network interface appears.
Under Firewall and route details, click the Firewall Rules tab and confirm that the following firewall rules are defined.
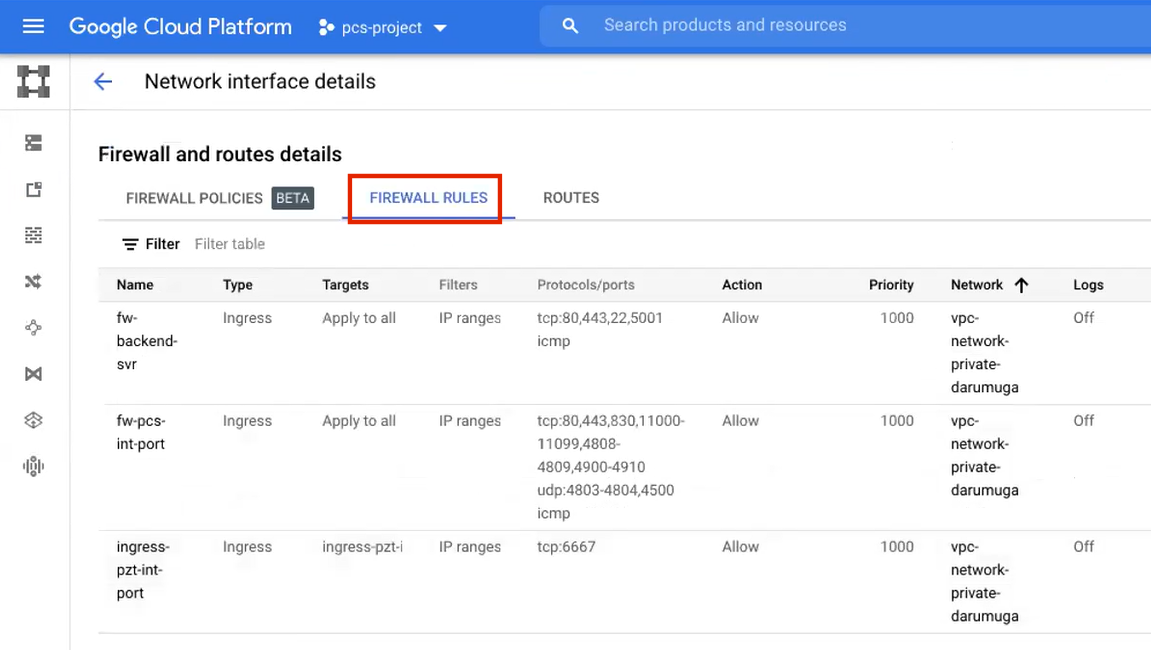
-
Click nic1. A summary page for this network interface appears.
Under Firewall and route details, click the Firewall Rules tab and confirm that the following firewall rules are defined.
-
(Optional) Click nic2. A summary page for this optional network interface appears.
Under Firewall and route details, click the Firewall Rules tab and confirm that the following firewall rules are defined.
-
-
The VM instance details* page, click Connect to serial console
A console monitor view (in a separate browser tab) shows the ongoing boot-up process for the instance.
-
Wait until the instance boot up is complete, and shows a screen similar to the following:
You can then complete this process by updating the Gateway details on
the Controller, see Completing the Configuration of
the Controller.
Creating a VM Instance of the Uploaded GCP Image Using a Script/Template
This section describes how to automatically create a virtual machine
instance of the ZTA Gateway image inside Google Cloud Platform using a
script/template. You can also perform this process manually, see Creating a VM Instance of the
Uploaded GCP Image Manually.
Ivanti provides YAML-based templates to create an instance of the ZTA Gateway image in the following configurations:
-
Two network interfaces in an existing VPC.
-
Three network interfaces in an existing VPC.
-
Two network interfaces in a new VPC.
Download:
https://pulsezta.blob.core.windows.net/gateway/templates/GCP/25-4-579/ivanti-zta-2-nics-new-vpc.zip -
Three network interfaces in a new VPC.
Download:
https://pulsezta.blob.core.windows.net/gateway/templates/GCP/25-4-579/ivanti-zta-3-nics-new-vpc.zip
You can obtain these templates through the links given here, or as part of the archive file set provided through the Download link on the Gateways Overview page in the Tenant Admin Portal after you have defined a Gateway record.
To use a template:
-
Download the required template archive file to your local workstation.
-
Unpack the downloaded archive file to a location that is accessible from Google Cloud Platform. Each archive contains three files. For example, for the two-interface (existing VPC) version of the archive:
pulsesecure-zta-2nics-existing-vpc.jinja pulsesecure-zta-2nics-existing-vpc.jinja.scheme pulsesecure-zta-2nics-existing-vpc.yaml -
Edit the YAML file
propertiessection to reflect your project and instance requirements, including theuser_dataproperty.An example of an existing VPC YAML file is provided here:
imports: - path: pulsesecure-zta-2-nics-existing-vpc.jinja resources: - name: my-vm properties: project: zta-gw-263035 email: [email protected] region: asia-south1 zone: asia-south1-b image: ztagcp123 machine_type: n1-standard-2 int_network: ext_network: int_subnetwork: ext_subnetwork: user_data: type: pulsesecure-zta-2-nics-existing-vpc.jinja
An example of a new VPC YAML file is provided here:
imports: - path: pulsesecure-zta-2-nics-new-vpc.jinja resources: - name: my-vm properties: deploy_with_lb: yes project: zta-gw-263035 email: [email protected] region: asia-south1 zone: asia-south1-b image: ztagcp123 machine_type: n1-standard-2 user_data: <pulse-config><primary-dns>8.8.8.8<\primary-dns> ... int_cidr: 192.0.2.0/24 ext_cidr: 192.0.2.0/24 type: pulsesecure-zta-2-nics-new-vpc.jinja
Where you are specifying a new VPC for your virtual machine instance, make sure you use properties (for example, networking settings) that do not conflict with an existing VPC.
-
Save the YAML file.
-
On the Google Cloud Platform, start a command line session from the title bar. For example:
A command line session starts.
-
Select the required project:
gcloud config set project <project-name> -
Within the project folder, create a deploymentmanager folder.
-
Copy the three script files to this folder.
-
Create a VM instance from the ZTA Gateway image archive file using the following command:
gcloud deployment-manager deployments create <vm-name> --config <yaml_file>For example:
gcloud deployment-manager deployments create vm-gcp-123 --config pulsesecure-zta-3-nics-existing-vpc.yaml -
Wait until the command completes.
-
On the VM Instances page, click on the new VM in the list of VM instances.
The VM instance details page appears for the instance.
-
Confirm the details for the VM instance, including the number of network interfaces.
-
Make a note of the public IP address of the EXT interface (typically, this is nic1. This is required inside nZTA.
You can now complete this process by updating the Gateway details on
the Controller, see Completing the Configuration of
the Controller.
Completing the Configuration of the Controller
If you specified a dummy public IP address (for example, 1.1.1.1) when you created the Gateway on the Controller, you now need to update the Controller with the allocated public IP address for the Gateway VM instance on Google Cloud Platform.
You do not need to perform the following procedure if you specified
the correct public IP address when you created the Gateway on the Controller, see
Adding a GCP Gateway in nSA.
- Return to the Gateways List page in the nZTA Tenant Admin Portal.
- Locate the new Gateway record in the list and confirm that its status has updated to Connected.
- Select the Gateway, and then select Secure Access > Gateways > Configuration.
- Under Gateway Network Settings, delete the current public IP setting and replace it with the public IP address if the nic1 (external) interface for the VM instance.
After you have registered a Gateway, you can configure it (or the Gateway Group to which it belongs) as the default Gateway if required. See the ICS Tenant Admin Guide for details.
Workflow: Creating a Gateway in Oracle Cloud Platform
For 22.7R1.3 release, 22.7R2.2 ZTA Gateway version is not supported with Oracle, AWS, and KVM platforms.
This workflow leads you through the processes for setting up a Gateway on the Oracle Cloud Platform (OCI).
These processes must be performed in sequence:
- Preparing to create an Oracle gateway, see Preparing to Create an Oracle Gateway.
- Creating the gateway record in the Controller, see Adding an Oracle Gateway.
- Downloading Metadata for Oracle Cloud Platform, see Downloading Metadata for Oracle Cloud Platform.
- Uploading the Oracle Image onto the Oracle Cloud Platform, see Uploading the Oracle Virtual Machine Image onto the Oracle Cloud Platform.
- Creating a VM Instance of the OCI image:
- Creating a VM Instance of the Uploaded Oracle Image Using a Script/Template, see Creating a VM Instance of the Uploaded OCI Image Using Terraform Script.
- Refer Terraform Configurations for details on the configuration, see Terraform Configurations.
- Creating a VM Instance of the Uploaded OCI Image Using any Other Methods, see Creating a VM Instance of the Uploaded OCI Image Using any Other Methods
Preparing to Create an Oracle Gateway
Before you start, make sure you have the following information and files:
- An identifying name for the Gateway.
-
The public IP address for the Gateway. This is the IP address at which clients can externally reach the Gateway instance, such as an LB/NAT or Datacenter network forward rules.
If you want Oracle Cloud platform to allocate a public IP address automatically, you can use a dummy IP address (for example, 1.1.1.1) when you create the Gateway on nZTA.
- The Gateway geographic location.
-
(Optional) The name of the Gateway Group to which you want to add this new Gateway record. To learn more about Gateway Groups, see Configuring Gateways.
Gateway Group may have a defined public IP address, which you can specify during the creation of the Gateway.
-
Credentials for the Oracle Cloud Platform Console.
These credentials must include sufficient permissions to create a virtual machine using terraform scripts.
- The primary (and optional secondary) DNS server IP address, and search domain.
Adding an Oracle Gateway
To register a Gateway on your Controller, use the Gateway Details dialog. To begin, log into the Controller Tenant Admin Portal using the credentials provided in your welcome email. Two outcomes are possible:
- On unconfigured nZTA systems, the Secure Access Setup Onboarding wizard appears (see Working with the Onboarding Wizard). In this case, click Add Gateway.
-
On configured nZTA systems, the Network Overview page appears. In this case:
-
From the nZTA menu, click the Secure Access icon, then select Manage Gateways.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller.
- To add a new Gateway, select Create from the top-right.
-
From the drop-down menu, click Create ZTA Gateway.
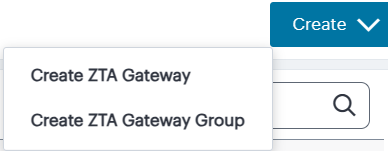
The Gateway Details dialog appears.
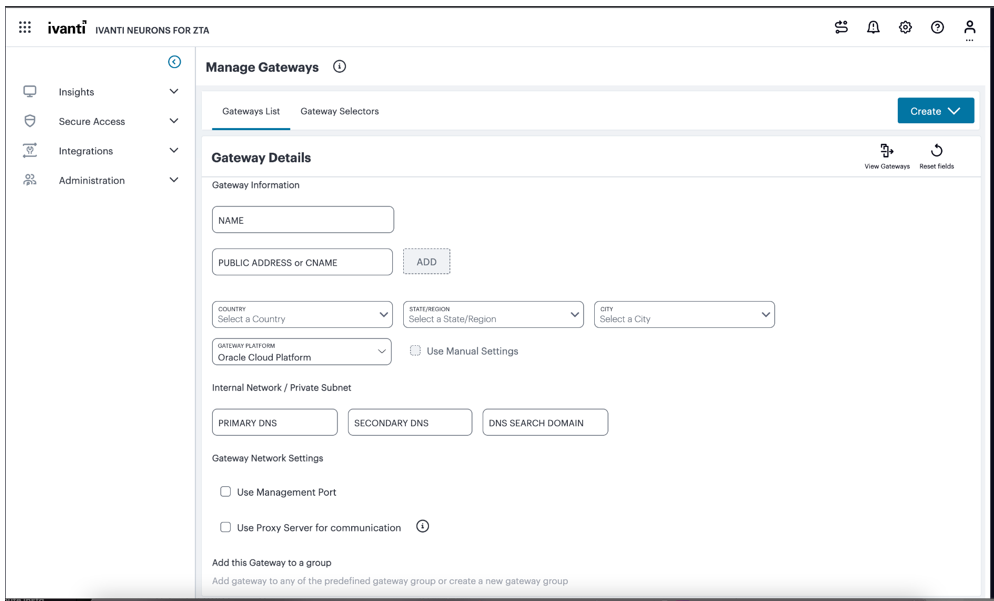
-
Enter the following details:
- Enter a Name for the Gateway.
- Enter one or more Public Address or CNAME (Public IP address or CNAME) for the Gateway.
-
Select Add to add each entry to the list. To learn more about this setting, see Configuring Gateways.
If you want Oracle Cloud Platform to allocate a public IP address automatically, you can use a dummy IP address (for example, 1.1.1.1) at this point. You must then update the Controller with the allocated public IP address after the Oracle VM instance is created (if it is not updated automatically).
- Select the geographic location details for the Gateway.
- For Gateway Platform, select Oracle Cloud Platform.
- Enter the Primary DNS IP address for the Gateway.
- (Optional) Enter the Secondary DNS IP address for the Gateway.
- Enter the DNS Search Domain for the Gateway.
-
(Optional) Select the Use Management Port check box to use management network ports for nZTA traffic rather than internal ports.
When the management port is enabled, Gateway will use management interface to communicate with Controller and NTP Server.
The Gateway will still use the internal port for DNS resolution and NTP server name resolution.
If the internal DNS cannot resolve the Controller domain, the internal interface will require internet access.
-
(Optional) Select the Use proxy server for communication check box to enable nZTA to Controller communication via proxy server.
Proxy is supported on both internal and management interfaces of the Gateway. Once enabled, enter host name and port.
Optionally, if your proxy server requires further authentication, enter a username and password to log in to the proxy server.
-
(Optional) Select a Gateway Group to which the new Gateway is to be added. To learn more about Gateway Groups, see Configuring Gateways.
A Gateway Group may have a defined public IP address, which you can specify as the Public Address.
- To add a Gateway definition based on the settings you specified in this dialog, select Create Configuration.
You can now download your metadata, see Downloading Metadata for Oracle Cloud Platform.
In case of registration failure due to Gateway configuration mistakes in firewall rules, DNS, etc., you can re-register the gateway. It does not require re-deploying of Gateway.
Downloading Metadata for Oracle Cloud Platform
The preparation of metadata for use on Oracle Cloud Platform currently requires some manual steps:
- Log into the Controller as a Tenant Admin, see Logging in as a Tenant Administrator.
-
From the nZTA menu, click the Secure Access icon, then select Manage Gateways > Gateways List.
The Gateways List page appears, showing the full list of Gateway Groups and standalone Gateways currently configured on the Controller.
-
Locate and select your Oracle cloud Gateway.
The Gateways Overview page appears.
- Click the Download icon, then choose Download gateway init config to obtain a copy of the Gateway definition file.
-
Specify a save location for your Gateway definition file.
The Gateway definition file is valid for 24 hours. If this period expires, you must replace the Gateway to generate a new Gateway definition file.
- (Optional) If you have not yet downloaded the latest version of your Gateway VM image and optional YAML templates, click the Download icon and select Download gateway VM image. Save the archive file and unpack to a local workstation. Make sure the resulting file set is accessible from the Oracle Cloud Platform Management Portal.
You can now create an Oracle cloud gateway VM in Oracle Cloud Platform, see Uploading the Oracle Virtual Machine Image onto the Oracle Cloud Platform.
Uploading the Oracle Virtual Machine Image onto the Oracle Cloud Platform
To upload a Oracle Gateway virtual machine image into Oracle Cloud Platform:
- Access the Oracle Cloud Platform Management Portal, either from a client or a web browser, and log in using your Oracle Cloud Platform credentials.
- Click the Navigation menu, and then select Storage > Buckets.
- Select the right compartment and then the list of OCI storage buckets appears as below.
-
Select the bucket into which you wish to place the OCI image.
A page listing the current list of the files from the bucket appears.
-
Click Upload.
An upload dialog appears.
- Select the ZTA Gateway OCI virtual machine image.tar file from your local workstation and click Open.
- Wait until the upload completes. This may take several minutes.
- Once upload completes. Create an image from the bucket using the following method:
- Click the Navigation menu, and then select Compute > Custom Images.
- Select the right compartment and then the list of current images appears.
- Click on Import image. An import dialog will appear and then choose the .tar file that was uploaded in the bucket. Refer to the below screenshots.
- Ensure the OS is selected as CentoS.
- Ensure Launch mode is chosen as Paravirtualized mode.
- Ensure Image type is chosen as QCOW2.
- Wait until the import completes. This may take several minutes.
- Perform the task manually, see Configuring Gateways.
- Perform the task with a script, see Creating a VM Instance of the Uploaded OCI Image Using Terraform Script.
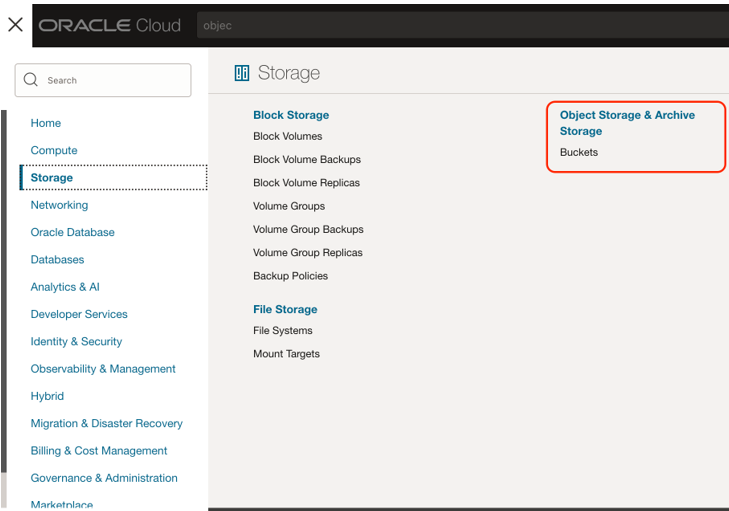
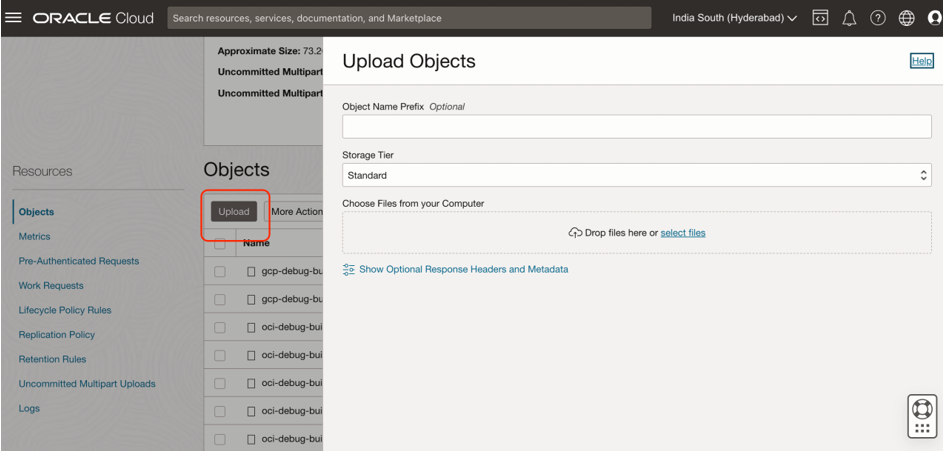
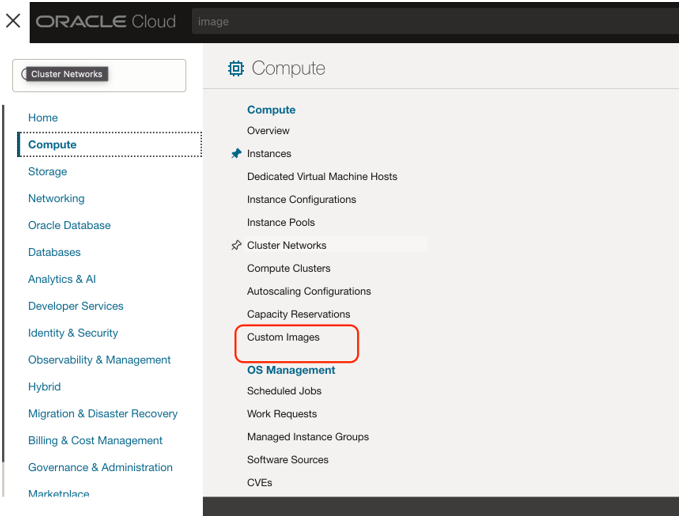
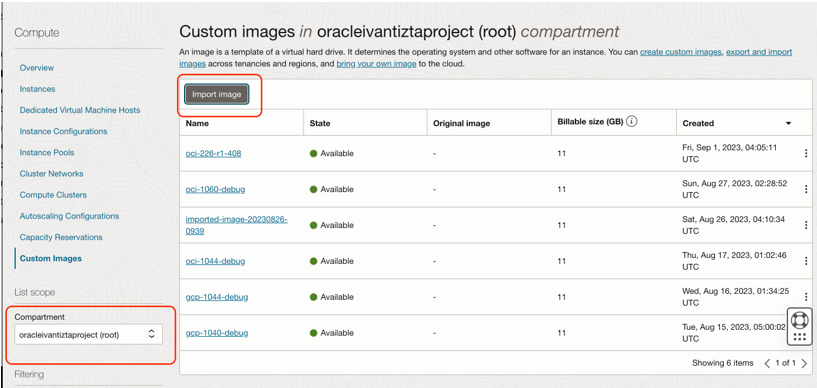
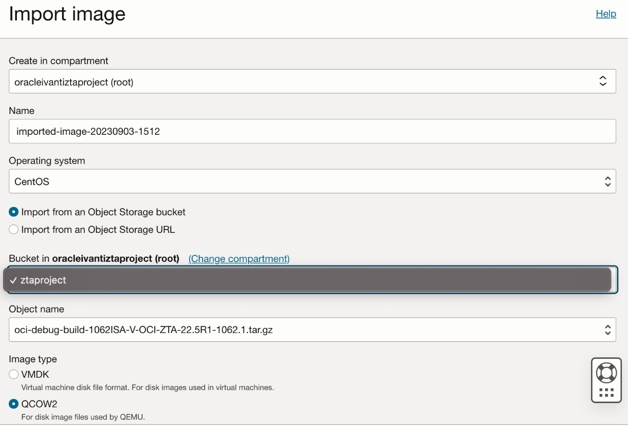
You can now create a VM instance of the uploaded OCI image. To do this, either:
Creating a VM Instance of the Uploaded OCI Image Using Terraform Script
Pre-requisites: Ensure OCI configurations required for CLI access is enabled. This is one-time process. Please see here for details:
- Download the required template archive file to your local workstation.
- Upload all the scripts to Oracle cloud shell as below:
- Open the cloud shell using the option as shown below.
- Upload the terraform scripts using the upload option from the cloud shell settings as shown below. Once it is uploaded, the scripts will be present in the user’s home directory.
- Edit the config.auto.vars file as per the intended deployment. Refer Terraform Configurations for details on the configuration.
- Run terraform init.
- Run terraform validate. This will let the admin know if there are any issues with the configurations.
- Run terraform apply. This will trigger the deployment process.
- If any resource deployment fails, retry running the command Terraform apply again.
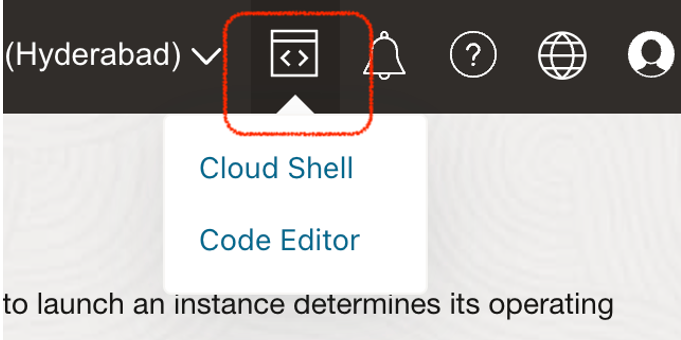
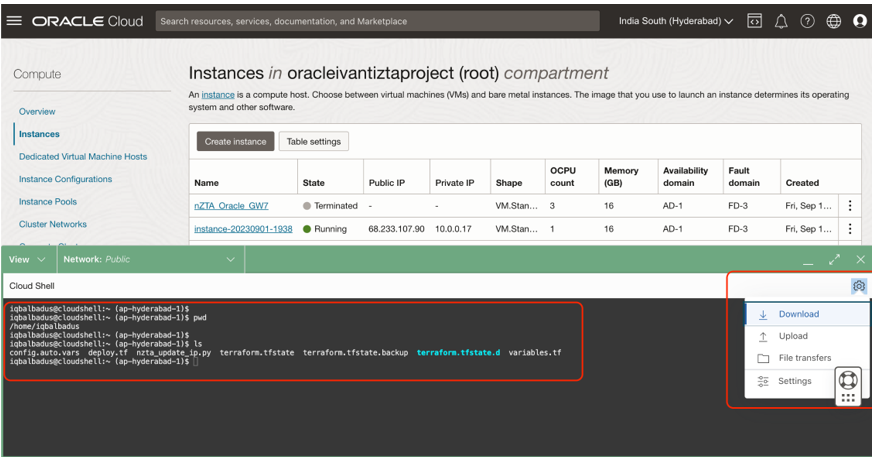
Terraform Configurations
| Serial No. | Configuration | Description | Sample Value |
|---|---|---|---|
| 1 | enable_management | This defines, if nZTA needs an additional NIC for management interface. | enable_management = true |
| 2 | internal_existing_vcn | This defines, if existing VCN to be used for internal(primary) interface. If true, then we need to provide the vcn-id for the configuration internal_vcn_id. | internal_existing_vcn = false |
| 3 | external_existing_vcn | This defines, if existing VCN to be used for external interface.If true, then we need to provide the vcn-id for the configuration external_vcn_id. | external_existing_vcn = false |
| 4 | management_existing_vcn | This defines, if existing VCN to be used for management interface.If true, then we need to provide the vcn-id for the configuration management_vcn_id. | management_existing_vcn = false |
| 5 | use_internal_vcn_for_all | This defines, if internal VCN to be used for all interfaces(external/management). | use_internal_vcn_for_all = false |
|
6 |
internal_existing_subnet |
This defines, if existing subnet from the existing VCN to be used for internal(primary) interface. If true, then we need to provide the configuration internal_vcn_id and internal_subnet_id. |
internal_existing_subnet = false |
|
7 |
external_existing_subnet |
This defines, if existing subnet from the existing VCN to be used for external interface. If true, then we need to provide the configuration external_vcn_id and external_subnet_id. |
external_existing_subnet = false |
|
8 |
management_existing_subnet |
This defines, if existing subnet from the existing VCN to be used for management interface. If true, then we need to provide the configuration management_vcn_id and management_subnet_id. |
management_existing_subnet = false |
|
9 |
create_management_nat |
This defines, if NAT needs to be created for management interface. This is required for management interface to access controller deployed in the internet. |
create_management_nat = true |
|
10 |
create_internal_nat |
This defines, if NAT needs to be created for internal(primary) interface. This is required for internal interface to access controller deployed in the internet. |
create_internal_nat = true |
|
11 |
create_external_ig |
This defines, if internet gateway needs to be created for external interface. This is required for ISAC client to reach the external interface for resource access. |
create_external_ig = true |
|
12 |
use_static_external_ip |
This defines, if static private ip to be used for external interface. |
use_static_external_ip = false |
|
13 |
use_static_internal_ip |
This defines, if static private ip to be used for internal interface. |
use_static_internal_ip = false |
|
14 |
use_static_management_ip |
This defines, if static private ip to be used for management interface. |
use_static_management_ip = false |
| 15 | use_load_balancer | This defines, if load balancer needs to be configured for external interface. | use_load_balancer = false |
|
16 |
use_existing_lb_for_ext_nic |
This defines, if existing load balancer to be used for external interface. If true, then we need to provide the configuration external_lb_id. |
use_existing_lb_for_ext_nic = false |
|
17 |
use_existing_bs_for_ext_nic |
This defines, if existing backend set to be used for external interface. If true, then we need to provide the configuration bs_display_name. |
use_existing_bs_for_ext_nic = false |
|
18 |
use_existing_ls_for_ext_nic |
This defines, if existing listeners to be used for external interface. If true, then we need to provide the configuration listener_display_name. |
use_existing_ls_for_ext_nic = false |
|
19 |
compartment_id |
The OCID of the compartment where the nZTA gateway will be deployed |
compartment_id = "ocid1.tenancy.oc1..aaaaaaaarod5yc3653ujwgvjbqui3s6r6ntfbs3d4uwxlkitku5flcbkrety" |
|
20 |
vm_display_name |
Display name for the nZTA gateway VM. |
vm_display_name = "skrn-new-2" |
|
21 |
image_id |
OCID of the image to use for the nZTA gateway deployment. |
image_id = "ocid1.image.oc1.ap-hyderabad-1.aaaaaaaapw7vnd4fqbp3heuk5kikfhlmhpcxjhcrl7tz7a3ln52gg7jr3htq" |
|
22 |
shape |
VM shape for the nZTA gateway (e.g., VM.Standard.E4.Flex and etc.) . If the shape is of type fles, then we need to provide the configuration total_flex_OCPUs and total_flex_RAM as mandatory. |
shape = "VM.Standard.E4.Flex" |
|
23 |
total_flex_OCPUs |
Number of required OCPU's for the flex VM. |
total_flex_OCPUs = 3 |
|
24 |
total_flex_RAM |
RAM size for the flex VM |
total_flex_RAM = 16 |
|
25 |
availability_domain |
Availability domain where the shape belong to. |
availability_domain = "bsUY:AP-HYDERABAD-1-AD-1" |
|
26 |
internal_vcn_cidr_block |
Internal CIDR block for the internal Virtual Cloud Network to be created. |
internal_vcn_cidr_block = "10.0.0.0/16" |
|
27 |
internal_vcn_display_name |
Display name for the internal Virtual Cloud Network to be created. |
internal_vcn_display_name = "ZTA_internal_vnc_2" |
|
28 |
internal_vcn_id |
OCID of the existing vcn to use for the nZTA internal interface (Primay VNIC) |
internal_vcn_id = "ocid1.vcn.oc1.ap-hyderabad-1.amaaaaaatgkbhxyaia3zy75gt3cqxqotgdagfsw7vdy2sylscjvavm2526ha" |
|
29 |
internal_subnet_id |
OCID of the subnet to use for the nZTA internal interface (Primay VNIC). |
internal_subnet_id = "ocid1.subnet.oc1.ap-hyderabad-1.aaaaaaaafscfkn7nzwsnv5xgjscybresi55fyxreqrqeu67umiz2sw7giawa" |
|
30 |
internal_subnet_cidr_block |
CIDR block for the internal subnet to be created. |
internal_subnet_cidr_block = "10.0.0.0/18" |
|
31 |
internal_subnet_display_name |
Display name for the internal subnet to be created. |
internal_subnet_display_name = "internal_Subnet_2" |
|
32 |
internal_rt_name |
Display name of the routing table for the internal subnet to be created. |
internal_rt_name = "internal_rt_name" |
|
33 |
internal_nat_name |
Display name of the nat for the internal subnet to be created. |
internal_nat_name = "internal_nat_name" |
|
34 |
internal_nic_display_name |
Display name for the internal NIC (Primary VNIC) to be created. |
internal_nic_display_name = "internal" |
|
35 |
internal_ip_address |
Static IP address of the internal nic (optional) |
internal_ip_address = "10.1.1.2" |
|
36 |
internal_is_public_ip_enabled |
This defines, if we need to ssign public IP to internal nic. |
internal_is_public_ip_enabled = false |
|
37 |
internal_nsg_name |
Display name of the network security group to be associated with internal NIC which will be created. |
internal_nsg_name = "internal_nsg_name" |
|
38 |
internal_nsg_rules |
Defines the network security group for the internal interface. Protocol - Protocol to be allowed. Values : 6 (TCP) ,17 (UDP) Destination : Destination CIDR block to be allowed. Source: Source CIDR block to be allowed. min_dstport : Min destination port to be allowed max_dstport : Max destination port to be allowed min_srcport : Min destination port to be allowed max_srcport : Max destination port to be allowed description : Description about the NSG rules. direction : INGRESS or EGRESS |
protocol = "6"//TCP destination ="0.0.0.0./0" source = "0.0.0.0./0" min_dstport = 6667 max_dstport = 6667 min_srcport = 0 max_srcport = 0 description = "internal ingess" direction = "INGRESS" |
|
39 |
external_vcn_cidr_block |
External CIDR block for the external Virtual Cloud Network to be created. |
External_vcn_cidr_block = "10.0.0.0/16" |
|
40 |
external_vcn_display_name |
Display name for the external Virtual Cloud Network to be created. |
external_vcn_display_name = "ZTA_external_vnc_2" |
|
41 |
external_vcn_id |
OCID of the existing vcn to use for the nZTA external interface (Primay VNIC). |
external_vcn_id = "ocid1.vcn.oc1.ap-hyderabad-1.amaaaaaatgkbhxyaia3zy75gt3cqxqotgdagfsw7vdy2sylscjvavm2526ha" |
|
42 |
external_subnet_id |
OCID of the subnet to use for the nZTA external interface (Primay VNIC). |
external_subnet_id = "ocid1.subnet.oc1.ap-hyderabad-1.aaaaaaaafscfkn7nzwsnv5xgjscybresi55fyxreqrqeu67umiz2sw7giawa" |
|
43 |
external_subnet_cidr_block |
CIDR block for the external subnet to be created. |
external_subnet_cidr_block = "10.0.0.0/18" |
|
44 |
external_subnet_display_name |
Display name for the external subnet to be created. |
external_subnet_display_name = "external_Subnet_2" |
|
45 |
external_rt_name |
Display name of the routing table for the external subnet to be created. |
external_rt_name = "external_rt_name" |
|
46 |
external_ig_name |
Display name of the internal gateway for the external subnet to be created. |
external_ig_name = "external_ig_name" |
|
47 |
external_nic_display_name |
Display name for the external NIC (Primary VNIC) to be created. |
external_nic_display_name = "external" |
|
48 |
external_ip_address |
Static IP address of the external nic (optional) |
external_ip_address = "10.1.1.2" |
|
49 |
external_is_public_ip_enabled |
This defines, if we need to ssign public IP to external nic. |
external_is_public_ip_enabled = true |
|
50 |
external_nsg_name |
Display name of the network security group to be associated with external NIC which will be created. |
external_nsg_name = "external_nsg_name" |
|
51 |
external_nsg_rules |
Defines the network security group for the external interface. Protocol - Protocol to be allowed. Values : 6 (TCP) ,17 (UDP) Destination : Destination CIDR block to be allowed. Source: Source CIDR block to be allowed. min_dstport : Min destination port to be allowed max_dstport : Max destination port to be allowed min_srcport : Min destination port to be allowed max_srcport : Max destination port to be allowed description : Description about the NSG rules. direction : INGRESS or EGRESS |
protocol = "6"//TCP destination ="0.0.0.0./0" source = "0.0.0.0./0" min_dstport = 6667 max_dstport = 6667 min_srcport = 0 max_srcport = 0 description = "external ingess" direction = "INGRESS" |
|
52 |
management_vcn_cidr_block |
management CIDR block for the management Virtual Cloud Network to be created. |
management_vcn_cidr_block = "10.0.0.0/16" |
|
53 |
management_vcn_display_name |
Display name for the management Virtual Cloud Network to be created |
management_vcn_display_name = "ZTA_management_vnc_2" |
|
54 |
management_vcn_id |
OCID of the existing vcn to use for the nZTA management interface (Primay VNIC) |
management_vcn_id = "ocid1.vcn.oc1.ap-hyderabad-1.amaaaaaatgkbhxyaia3zy75gt3cqxqotgdagfsw7vdy2sylscjvavm2526ha" |
|
55 |
management_subnet_id |
OCID of the subnet to use for the nZTA management interface (Primay VNIC). |
management_subnet_id = "ocid1.subnet.oc1.ap-hyderabad-1.aaaaaaaafscfkn7nzwsnv5xgjscybresi55fyxreqrqeu67umiz2sw7giawa" |
|
56 |
management_subnet_cidr_block |
CIDR block for the management subnet to be created. |
management_subnet_cidr_block = "10.0.0.0/18" |
|
57 |
management_subnet_display_name |
Display name for the management subnet to be created. |
management_subnet_display_name = "management_Subnet_2" |
|
58 |
management_rt_name |
Display name of the routing table for the management subnet to be created. |
management_rt_name = "management_rt_name" |
|
59 |
management_nat_name |
Display name of the nat for the management subnet to be created. |
management_nat_name = "management_nat_name" |
|
60 |
management_nic_display_name |
Display name for the management NIC (Primary VNIC) to be created. |
management_nic_display_name = "management" |
|
61 |
management_ip_address |
Static IP address of the management nic (optional). |
management_ip_address = "10.1.1.2" |
|
62 |
management_is_public_ip_enabled |
This defines, if we need to ssign public IP to management nic. |
management_is_public_ip_enabled = false |
|
63 |
management_nsg_name |
Display name of the network security group to be associated with management NIC which will be created. |
management_nsg_name = "management_nsg_name" |
|
64 |
management_nsg_rules |
Defines the network security group for the management interface. Protocol - Protocol to be allowed. Values : 6 (TCP) ,17 (UDP) Destination : Destination CIDR block to be allowed. Source: Source CIDR block to be allowed. min_dstport : Min destination port to be allowed max_dstport : Max destination port to be allowed min_srcport : Min destination port to be allowed max_srcport : Max destination port to be allowed description : Description about the NSG rules. direction : INGRESS or EGRESS |
protocol = "6"//TCP destination ="0.0.0.0./0" source = "0.0.0.0./0" min_dstport = 6667 max_dstport = 6667 min_srcport = 0 max_srcport = 0 description = "management ingess" direction = "INGRESS" |
|
65 |
init_config |
Init config that nZTA will pickup while deployment. This value needs to be taken from the init file downloaded from the nZTA controller interface as explained in admin guide section “Downloading Metadata for Oracle Cloud Platform”. |
init_config = "PHB1bHNlLWNvbmZpZz48cHJpbWFyeS1kbnM+OC44LjguODwvcHJpbWFyeS1kbnM+PHNlY29uZGFyeS1kbnM+OC44LjQuNDwvc2Vjb25kYXJ5LWRucz48ZG5zLWRvbWFpbj5wc2VjdXJlLm5ldDwvZG5zLWRvbWFpbj48Y2VydC1jb21tb24tbmFtZT5za3JuLW9jaS5nLmUyZTIuZS5qdW5pcGVyLnB6dC5kZXYucGVyZnNlYy5jb208L2NlcnQtY29tbW9uLW5hbWU+PGFjY2VwdC1saWNlbnNlLWFncmVlbWVudD55PC9hY2NlcHQtbGljZW5zZS1hZ3JlZW1lbnQ+PGNvbmZpZy1kb3dubG9hZC11cmw+J2h0dHBzOi8vZTJlMi5qdW5pcGVyLnB6dC5kZXYucGVyZnNlYy5jb20vYXBpL2dhdGV3YXlzLzBjYTNlNmUwLWZmMTItNDUxNy1hYTYzLWM5NjY5MWUzNDMzYi9vcmNoZXN0cmF0aW9uL2luaXRpYWwtY29uZmlnP3Q9Z0FBQUFBQmstQUFmYXIwYjgtNXowMXo4aVZSS1VBUTVIVURYaHJQcnFxcWZQc1JPY0pjS0pjQUZTQnhWZGFLbTRnNDhSVW53bTY3REFtWUlwQWp2c2JEWGUzcnA1X2VmU3Joc1lSWTM1SU96WmE3dlZsaDRXalNSQ3ZXa3JFVkVVek5mOTdqeDl1T1A1VktxQmdaN3NhLV93SUdkVnNBcUc3OWl4TTU2WVJXblYzc21NTm5maFhfNUxDTkFTYmV1T3BKWk5qNXpYWDdOa2Y5STZlWUctUWI0aHRENzNOZnZyYjhzNmRYZGo0WUlIaXItdXA0YnJ5d1I0dUdiVThuZ20zR3ZWanFPakRfbGJSYkFsT2VJdXpOMUJGaWpDeXhVc09nZDkwbmVRdkppUHdMc3pJLUJ1TW5FRktnVG1pX1RZTUFmY1E4YTM5MmRFUlQ1OVhWM3p4QkRvaklQQ1l1RlNtbExCd2NKckRjZC1oTVMwSmpxYUE1NHhLMDNsMDdMTHBQZ2ZrMmFOeWhBSHR4QUIyVFlEUDUtcV9iOFdRa2pCZXNhVmh5bkVRX0RkV0JoNGotMUF4TT0nPC9jb25maWctZG93bmxvYWQtdXJsPjxhcHBsaWFuY2UtaWQ+MGNhM2U2ZTBmZjEyNDUxN2FhNjNjOTY2OTFlMzQzM2I8L2FwcGxpYW5jZS1pZD48Y29udHJvbGxlci1ob3N0bmFtZT5lMmUyLmp1bmlwZXIucHp0LmRldi5wZXJmc2VjLmNvbTwvY29udHJvbGxlci1ob3N0bmFtZT48Y29udHJvbGxlci1lbnJvbGxlZC1ob3N0bmFtZT5lMmUyLmUuanVuaXBlci5wenQuZGV2LnBlcmZzZWMuY29tPC9jb250cm9sbGVyLWVucm9sbGVkLWhvc3RuYW1lPjxkbnMtc2VhcmNoLWRvbWFpbj5wc2VjdXJlLm5ldDwvZG5zLXNlYXJjaC1kb21haW4+PGNvbm5lY3QtdmlhLW1nbXQtaW50ZXJmYWNlPm48L2Nvbm5lY3QtdmlhLW1nbXQtaW50ZXJmYWNlPjwvcHVsc2UtY29uZmlnPg==" |
|
66 |
lb_display_name |
Display name of the load balancer that should be created. |
lb_display_name = "external_lb_name" |
|
67 |
listener_display_name |
Display name of the listener that should be associated with the loadbalancer. |
listener_display_name = ["external_ls_name_443" , "external_ls_name_80"] |
|
68 |
bs_display_name |
Display name of the backend sets that should be associated with the loadbalancer. |
bs_display_name = ["external_bs_name_443","external_bs_name_80"] |
|
69 |
external_lb_id |
OCI id of the external loadbalancer |
external_lb_id = "ocid1.networkloadbalancer.oc1.ap-hyderabad-1.amaaaaaatgkbhxyanzrjec4irpjuumytyuk5qugcuatjc2oiejpjcvo6hlaa" |
|
70 |
ports |
Load balancer ports for the listener and backendsets. The orfer of port number should be matching the order mentioned in listener and backend set configurations listener_display_name andbs_display_name |
ports = [443,80] |
|
71 |
bs_policy |
Backend set policy that should be used for traffic distribution in load balancer. |
bs_policy = "FIVE_TUPLE" |
|
72 |
protocol |
TCP is only protocol supported for load balancer configuration. |
protocol = "TCP" |
Creating a VM Instance of the Uploaded OCI Image Using any Other Methods
Deploy a VM with nZTA gateway image uploaded to the OCI, with following requisites:
- Configure 2 nic’s in the order Internal, External, if the Management port is not required for the nZTA gateway deployment.
- Configure 3 nic’s in the order Internal, External and Management. If management port is configured for the nZTA gateway deployment.
- Ensure custom metadata “pulse-config” is configured for the VM. The value of pulse-config metadata needs to be taken from the init file downloaded from the nZTA controller interface as explained in admin guide section Downloading Metadata for Oracle Cloud Platform.
- Ensure internal NIC can access the controller present in the azure cloud and application resources.
- Ensure external NIC public ip is reachable by the ISAC clients over the port 443.
- Ensure management NIC can access the controller present in the azure cloud , if management port is enabled for controller communication.
- Ensure load balancer ip is reachable by the ISAC clients over port 443, if load balancer is used for gateway deployment.
- Recommended Firewall rules:
- Internal - INGRESS (TCP: 6667), EGRESS (TCP: ANY, UDP: ANY)
- External - INGRESS (TCP: 443)
- Management - INGRESS (TCP: 6667), EGRESS (TCP: ANY, UDP: ANY)
Next Steps
After you have defined your user authentication policies, move on to
create your device policies. See Creating Device
Policies and Device Rules.