Policy Change Requests
In this section:
- About Policy Change Requests
- Configure Change Requests for a Rule
- Configure Request Types
- Request Methods
- ISM Integration (2021.3)
About Policy Change Requests
Desktop and mobile users can use the Policy Change Request feature to request an update to an Application Control configuration via email or telephone. Application Control 2021.3 also offers Ivanti Service Manager (ISM) users the ability to submit requests directly to ISM. Users can make requests from a link on the Application Control Access Denied dialog or by using the Application Control Policy Change Request executable installed on their desktop.
Policy Change Request settings are configured per rule and are evaluated at session connect and when a configuration changes. The email address, telephone number, and text for change requests is set globally and used for all groups with the appropriate settings applied.
Ivanti Service Manager (ISM) Integration 2021.3
For organizations with licenses for Ivanti Neurons for ITSM (or Ivanti Service Manager), Application Control 2021.3 introduces the ability to integrate Policy Change Requests directly into your service desk system. This enables optimization of your service desk processes and auditing of the complete change request workflow. Refer to ISM Integration (2021.3).
Note that screen images used in this help topic include the 2021.3 feature.
The Policy Change Request feature is compatible with 32-bit and 64-bit versions of Chrome, Edge and Internet Explorer 9, 10 and 11 .
Upgrading Policy Change Request settings
Policy Change Request behavior changed from being a global setting to being applied for each rule in Application Control 10.1. This change prevents agents from current software from processing change requests created from endpoints with pre-10.1 configurations.
To ensure the Policy Change Request feature continues to function correctly in the 10.1 release, you will need to upgrade all configurations within the 10.1 Application Control console and redeploy.
The Application Control Agent and the Application Control Web Services must be at the same version.
Configure Change Requests for a Rule
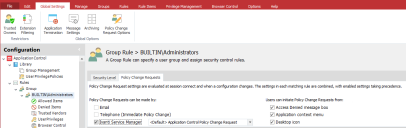
Configure which request types and features are available to users for each rule. Policy Change Request settings are available for all rule types, apart from Process rules.
- Select a rule in the navigation pane.
- Select the Policy Change Requests tab.
- Select how Policy Change Requests can be made:
- Telephone (Immediate Policy Change)
- Ivanti Service Manager
Select the Ivanti Service Manager checkbox and click the request template required. Refer to ISM Integration (2021.3)
- Select the methods by which users can initiate Policy Change Requests:
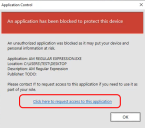
- Access Denied message box - Users click a link in the message box that displays when a user attempts to access a prohibited application.
- Application context menu - Users select an option from the context menu of prohibited applications.
- Desktop icon - Users use a desktop shortcut icon to raise change requests from the Policy Request dialog.
Note, it is possible to select both the Email and Telephone option, or the Ivanti Service Manager option.
Details for each setting are configured using the Policy Change Requests dialog, accessed from the Global Settings ribbon.
Configure Request Types and Methods
To configure request types and methods, select Policy Change Request Options from the Global Settings ribbon.
Request Types
Configure email and immediate policy change requests in the Request Types tab on the Policy Change Requests dialog.
Email Requests
When a user is prompted to elevate their privileges to run an application, they can click a link in the Access Denied message box to request a permanent configuration change. When the user clicks the link, they are prompted to enter the reason for the change request, which is sent to the email address configured in the Application Control console.
The Email Request function uses Messaging Application Programming Interface (MAPI) to send emails. An Application Control administrator reviews the request, and if the request is granted, updates the configuration and deploys the AAMP file.
To set up email change requests, enter the email address to which change requests are sent in the Mail To field.
You can only add one email address. To send the request to multiple email addresses you can configure a group email (distribution list).
Immediate Requests
Immediate requests allow users, typically mobile users, to request a permanent or temporary configuration change. When users click the immediate request link, they are provided with a phone number to call and issued with details of the request and a request code. The request code and the configuration change request are relayed to IT Support, who enter the details in the Help Desk Portal. IT Support generate a response code and send it to the user to enter in the Policy Change Request dialog.
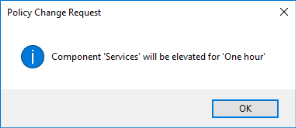
Users get three attempts to enter a response code. After three incorrect attempts the dialog closes and the changes are not applied. If configured, when the dialog closes, a 9091 event is raised. If the user requires further configuration changes, they must restart the process. If the code is entered correctly, users have elevated access to the application. Upon confirmation, users are presented with details of the elevation.
Configure the following fields in the Request Types tab:
- Helpdesk Phone Number - The number users are prompted to call to request the immediate configuration change.
-
Shared Key - The shared key is an integral part in processing Immediate requests and is embedded and encrypted in the configuration. The shared key must match in both the Application Control Console and the Help Desk Portal. If the shared keys do not match, a response code cannot be created and configuration change will not be authorized for deployment to the user's endpoint.
The shared key can be changed using the Help Desk Portal, however if the shared key is amended in the Portal, the same key must also be entered in the Application Control Console.
Once you have configured the Immediate Request settings in a configuration file, deploy it to your endpoints. Before the feature is fully activated, the Help Desk Administrator and Help Desk Operator roles must be assigned to members of your Support Team. Once you have deployed the configuration and assigned Help Desk Administrator role, the Help Desk Administrator can assign or remove additional Help Desk Operators and/or Administrators.
Request Methods
In the Request Methods tab, configure the text for policy change request items:
- Link from Access Denied Message Box
Link Text - Text for the request link displayed in the Access Denied Message Box presented to the end user. The default text is Click here to request access to this application. - Policy Change Request
Text - Text for the context menu displayed when a user right-clicks an item eligible for a policy change requests - Policy Change Request desktop icon
Text - The name of the policy change request desktop icon. Users can click or select the icon to open the Application Control Policy Change Request dialog and create change requests.
ISM Integration (2021.3)
Integration of Ivanti Service Manager (ISM) and Application Control enables optimized and fully audited request handling. The configuration tasks - and the functionality available to end users as a result - are summarized in the following table:
| Application Control - Administrator Tasks | Ivanti Service Desk Manager - Administrator Tasks | Application Control - End User Functionality |
|---|---|---|
|
Configure access to the ISM server and the options available to end users when they raise a change request. Refer to: •Policy Change Request Options - ISM Integration
|
Import the Application Control template and configure the request offering and request form. Ensure the workflow performs as expected. Links below open ISM help topics in a new browsing tab |
Create and submit Policy Change Requests, monitor the status of requests as required. Refer to: |
Request Status
The status of all service requests is changed according to its processing within the workflow. The number of different stages used in the process - and name used to describe each status - is configured within the ISM system.
Typically, when a service request is first raised, it is in the Submitted state, and only when it has been reviewed and analyzed against a set of criteria will it be Approved.
Only service requests in the Approved state are fulfilled by Application Control.
Policy Change Request Options - ISM Integration
Policy Change Request options allow you to enable or disable end user access to the Policy Change request feature, and determine the request template available to them. The options determine how requests are communicated to the ISM system and also what selection choices end users have when creating change requests.
1.From the Menu ribbon select Global Settings > Policy Change Request Options, then select the ISM Integration tab:
2.Specify details for your ISM system:
• ISM Server Enter the web address for the ISM server
•API Key Enter the API Key required.
API Keys are available from the ISM Configuration Interface (under Configure \ Security Controls \ API Keys). You will need to select the name of the Key Group you wish to use and copy the API Key into the Application Control Console. The API Key is encrypted with the AppSense Configuration.
•Polling Interval Modify the polling interval if required.
3.Available Request Templates are listed. On first use, or to add a new template, select Browse for Request Templates.
The Browse ISM Service Requests dialog is displayed. It lists available Service Requests.
•Click Browse and select the request required.
•Note, the Service Request selected must be specific to Application Control, and its status must be Published.
•The selected template is added to the Available Request Templates.
Where multiple request templates exist, one can be identified as the Default for use. Refer to Default Request Template.
4.Select Browse for User
The Browse for ISM User dialog is displayed. It is populated using ISM system Employees data.
•Click Browse and select the user required.
Note, because this selection determines the user of a request template (not a user-specific request), it is recommended that an alias or representative ISM User account is created for this process. This enables the template to be utilized by many users, in each case the individual user name is added to the request as a specific attribute.
•The selected user is now added to the Available Request Templates.
5.The Ignore Service Requests section allows you to manage the list of change requests awaiting processing. Change requests created before a specified date are ignored. For example, this function may be useful when a new configuration has been deployed and where the changes made to it render earlier policy change requests as invalid.
•Select the radio button required and specify the date required.
6.When you have completed the Policy Change Request Options, select OK to save your changes.
Application Control Service Request Template
The Application Control Service Request Template is freely available for download from the Ivanti Marketplace.
The template includes a list of actions, components and durations. Administrators can remove items easily to ensure options available are relevant to your users and organization. For example, to remove the option for users to make a request indefinitely, you remove the indefinite value from the Duration list.
Organizations may require a number of different request templates, these could be configured to enable different options for specific user groups or functions. Administrators need to consider which template they select as a default especially as user groups typically overlap with individuals belonging to multiple groups.
Overlapping user groups - example:
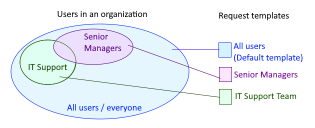
Here, a senior manager within the IT Support team belongs to all three user groups but only one template request template can be assigned to an individual.
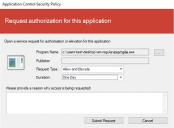
Endpoint User - Create a Policy Change Request
When ISM integration is enabled, endpoint users can initiate and create Policy Change Requests according to the methods configured in the template (refer to step 4 in Configure Change Requests for a Rule).
Initiate a Request
Program NameDepending upon how the request was initiated, this field may be pre-populated. Ensure the required item is specified.
If required, click the ellipses icon and browse to select the application required.
Publisher If the selected application is signed the software publisher name is displayed. The field will remain blank for unsigned executables.
Request Type Users select the permission required. The options available are determined by the request configuration but will typically include: Allow or Allow and Elevate for example.
Duration Users select the duration required for the change in policy. The options available are determined by the request configuration.
Please provide a reason why access is being requested:Optionally, the user can enter a reason for the request.
Click Submit Request or Cancel
Endpoint User - Challenge Response dialog
The Application Control Challenge Response dialog lists Policy Change Requests submitted by the individual user. It shows the request status and date of expiry.
Users can right-click a request and select options from the context menu:
• DetailsThe Service Request Details window is displayed. It lists attributes of the request. Depending upon the request status, the Owner of the request is included and this can assist with any required progress chasing or querying of specific requests.
•Resubmit The availability of this option depends upon the request status.
The dialog is automatically displayed when a poll to the ISM server returns a change to the status of a user's request. A toast notification is also displayed and a taskbar icon indicates that ISM is active. The user can open the dialog at any time via the following methods:
•Double-click the Policy Change Request desktop icon
•Select Create New Request within Application Control
•Double-click the taskbar icon (![]() ).
).
The different status names (or states), and the number of them, is configured within the ISM system. Typically this includes: Submitted, Active, Approved and Expired.
Approved status signals that the change request has been fulfilled. In the case of requesting access to a specific application for example, Approved means user has access with immediate effect.
Note, Policy Change Requests processed via ISM enable Administrators to revoke request approval if required. For example, if a risk or question emerges relating to an Approved change the ISM Administrator may change the request status to Active and request advice. With the status returned to Active, the permission is withheld.