Configuring federated pairs
A federated pair is the identity provider (IdP) and service provider (SP) pair for which Ivanti Access is used as the intermediary. Federated pairs are configured in Federated Pairs. The Federated Pairs link in the left navigation pane changes to Federation if delegated IdP is enabled.
Before you begin
Before you configure a federated pair, ensure the following:
- You have an existing federated authentication setup, using SAML or WS-Fed, between the cloud service provider (SP) and the identity provider (IdP).
- The existing federated authentication setup between the SP and IdP works without Ivanti Access in the path.
- You have the SP and IdP metadata.
- For instructions on getting cloud service provider (SP) metadata see the following Knowledge Base article
How do I access Service Provider (SP) metadata? - For instructions on getting identity provider metadata see the Knowledge Base article at
How do I access Identity Provider (IdP) metadata?
- For instructions on getting cloud service provider (SP) metadata see the following Knowledge Base article
- Microsoft Azure Active Directory as an IdP is qualified only with Salesforce (SP) and G Suite (SP).
- Microsoft Azure Active Directory as an IdP is not supported with Office 365 (SP).
- G Suite as an IdP is qualified only with Salesforce (SP) and Facebook Workplace (SP).
- G Suite as an IdP is not supported with Office 365 (SP).
- OneLogin as an IdP is not supported with Office 365 (SP).
- WebEx as an SP is qualified only with Microsoft ADFS (IdP) and Okta (IdP).
- For Office 365 Using WS-Federation only the following IdP are supported: Microsof ADFS and Ping Identity.
Procedure
- In the Ivanti Access administration portal, go to Profile > Federated Pairs.
-
Click +Add New Pair.
The set of supported cloud service providers displays.
-
Click the appropriate service provider to configure service provider settings.
To add a service provider that is not listed, select either Custom SAML Service Provider or Custom WS-Federation Service Provider.
Concur is a compatible app. Concur as a service provider is tested only with Okta and Microsoft ADFS.
-
Enter the requested information for the service provider.
The requested information includes the signing certificate, encryption certificate for SAML assertions, service provider metadata, checkbox to validate signature for authentication requests sent by service provider, and the option to configure single sign-on (SSO).
If you had previously uploaded signing certificates, select the certificate from the Signing Certificate drop-down list. Ivanti also provides a default signing certificate, which is also available in the drop-down list.
-
Previously, the service provider signing certificates existed but were not validated and user could log in to the service provider regardless of the signing certificate status. Now, a checkbox is introduced to validate the service provider signature and log an error in the Reports > Access. For the existing federated pairs, the checkbox is disabled and for the new federated pairs, it is enabled by default. This field is supported for Salesforce and Custom SAML service provider only.
-
When configuring a Federated Pair, the checkbox labeled "Validate signature for authentication requests" should be enabled. For backward compatibility, this option is unchecked for the existing pairs. Ensure that the SP/IdP metadata is updated and enable the checkbox.
-
-
Click Next.
The set of supported identity providers displays.
- Click the appropriate identity provider to configure identity provider settings.
-
Enter the requested information.
The requested information includes the signing certificate and the identity provider metadata.
- Click Done to complete the federated pair configuration.
- Click OK in the Federated Pairs Setup is Complete message.
The new pair is displayed on the Federated Pairs tab in Access.
You can also edit a federated pair. On the Federation page, click  for the federated pair that you want to edit. When editing a federated pair, you can switch from add metadata URL to upload metadata or vice versa or only provide the metadata URL for the federated pair.
for the federated pair that you want to edit. When editing a federated pair, you can switch from add metadata URL to upload metadata or vice versa or only provide the metadata URL for the federated pair. 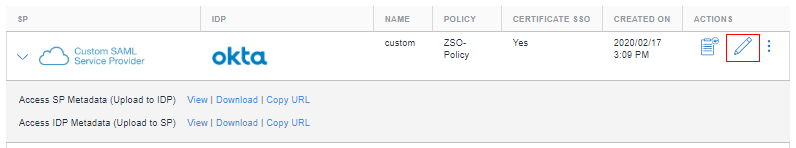
- Signing certificates
- Generating a signing certificate in Ivanti Access
- Service provider (SP) metadata
- Configuring Mobile App Single Sign-on (SSO)
- IdP initiated login
- SAML response signature
- Identity provider (IdP) metadata
- Office 365 settings
- For more information on configuring federated pairs, see Ivanti Access cookbooks.
Next steps
- Publish the profile.
See Publishing a profile. - Upload metadata from Access to SP and IdP.
See Uploading proxy metadata. - Verify traffic flow.
See Verifying traffic flow.