Configuring email attachment control
Use the Admin Portal to configure email attachment control.
Before you begin
•If you require different options for different users, use a different Ivanti Standalone Sentry for each set of users.
•If you plan to encrypt email attachments, Open only with Docs@Work and protect with encryption option for iOS devices, you must also configure the Docs@Work app.
Make sure you have checked Enable Docs@Work in the Admin Portal, Settings > Preferences. For a description of email attachment control options, see Email attachment control options.
•For a list of supported secure email apps, see the Standalone Sentry Release Notes.
Procedure
| 1. | Go to Services > Sentry in the Admin Portal. |
| 2. | Click the Edit icon for the Ivanti Standalone Sentry entry configured for ActiveSync. |
| 3. | Select Enable Attachment Control. |
This option is available only if you selected Enable ActiveSync.
Not selecting this option means the Ivanti Standalone Sentry delivers attachments as is to all devices.
| 4. | For iOS Using Native Email, select the type of attachment control that you want to use. |
| 5. | For iOS And Android Using Secure Apps, select the type of attachment control that you want to use. |
| 6. | For Other Platforms (Including Android Using Unsecured Apps), select the type of attachment control that you want to use. |
This option does not impact iOS devices at all.
| 7. | For File Name Exclusion List, enter any file extensions that you always want Ivanti Standalone Sentry to deliver as is, regardless of the attachment control option selected. Specify a comma-separated list. |
If you make no entry into the text box, the default file name extension list is applied.
| 8. | Click Save. |
The Standalone Sentry restarts when you click Save. A restart can cause a brief interruption in email service to device users.
If you changed to or from the option Open only with Docs@Work and protect with encryption, you will see the following warning:
Figure 1. Warning message due to encryption option changes
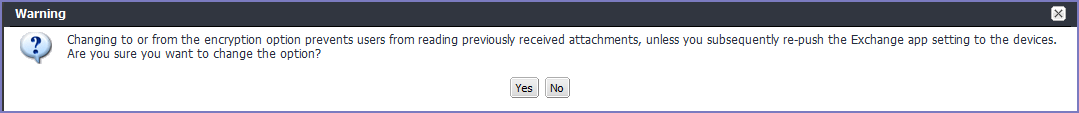
| 9. | Click Yes if you understand and agree to the impact. |
Next steps
Go to Checking for configuration errors.
| • | Impact of changing the encryption option. |
•Regenerating the encryption key.
•AES-256-GCM encryption for email attachments .
Checking for configuration errors
If the Ivanti Standalone Sentry is not available when you click Save, it does not receive the new settings. You can check if the changes were applied to Standalone Sentry.
Procedure
| 1. | In the Ivanti EPMM Admin Portal, go to Services > Sentry. |
| 2. | If there are errors, click View Errors on Ivanti Standalone Sentry’s setting for the detailed error message. |
When the Ivanti Standalone Sentry is available again, open the Edit Standalone Sentry view and click Save to send the new settings.
Impact of changing the encryption option
Changing the option from Open only with Docs@Work, and protect with encryption to a different option prevents iOS device users who use the iOS native email client from reading previously received attachments. If device users need to read previously received attachments, re-push the Exchange setting to the devices. Ivanti advises caution when re-pushing the Exchange setting. Re-pushing the Exchange setting increases the load on the Exchange server.
Change to or from the encryption option only if:
•you can make the change during a planned maintenance period or non-peak operating hours.
•you have notified users about what to expect.
Regenerating the encryption key
Standalone Sentry uses an encryption key to encrypt email attachments when the attachment control option is Open only with Docs@Work, and protect with encryption. Ivanti EPMM generates the encryption key the first time you select the encryption option. Ivanti EPMM provides one encryption key to all Standalone Sentrys using the encryption option.
Regenerate the encryption key only if:
•the key has been compromised.
The encryption key is compromised if malicious third-party apps are using it to view email attachments.
•you are switching from AES-128-bit encryption to AES-256-bit encryption.
AES-256-GCM encryption for email attachments
•you can regenerate the key during a planned maintenance period or non-peak operating hours.
•you have notified users about what to expect.
•Key regeneration causes a restart for all Standalone Sentrys that are using encryption for attachment control.
A restart can cause a brief interruption in email service to device users.
•Key regeneration prevents iOS device users who use the iOS native email client from reading previously received attachments.
Previously received attachments are encrypted with the old key, but Mobile@Work and the Docs@Work app use the new key after key regeneration. Therefore, they cannot display the old attachment.
Furthermore, consider the scenario when a device user forwards an email with an attachment encrypted with the old key.The Standalone Sentry is unable to decrypt the attachment because it is using the new key. In this case, the Ivanti Standalone Sentry replaces the attachment with a text file with an explanatory message.
Procedure
| 1. | In the Admin Portal, go to Services > Sentry > Preferences. |
| 2. | In the Standalone Sentry section, click Regenerate Key. |
Figure 2. Key regenerate warning
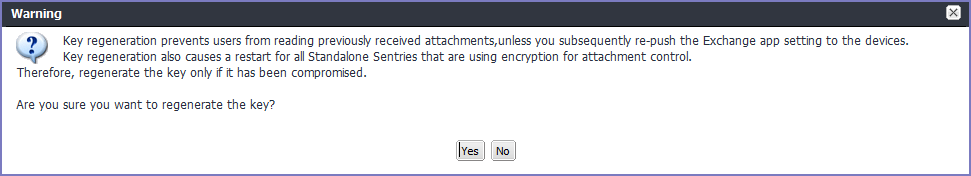
| 3. | Click Yes if you are sure you want to regenerate the key. |
If an Ivanti Standalone Sentry is not available when you regenerate the key, its entry in Sentry > Settings displays an error.
AES-256-GCM encryption for email attachments
Ivanti Standalone Sentry 6.1 adds support for AES-256-GCM for encrypting email attachments. If you already have Docs@Work (original) enabled and are now enabling Docs@Work, the system continues to use 128-bit encryption for email attachments.
To use 256-bit encryption with the Docs@Work app, you must first disable Docs@Work (Original) and then regenerate the attachment encryption key. A 256-bit key is only generated if Docs@Work (Original) is disabled and all Standalone Sentry servers that are configured on Ivanti EPMM are at least Version 6.1.
|
Docs@Work (Original) |
Docs@Work |
Sentry Version |
Encryption key generated |
|
Enabled |
Enabled |
- |
AES-128-ECB |
|
Disabled |
Enabled |
Some Standalone Sentrys are less than Version 6.1 |
AES-128-ECB |
|
Disabled |
Enabled |
All Sentrys are at least Version 6.1 |
AES-256-GCM |
•Key regeneration causes a restart for all Ivanti Standalone Sentrys that use encryption for attachment control. A restart can cause a brief interruption in email service to device users.
•After regenerating the encryption key, iOS device users who use the iOS native email client cannot read previously received attachments. If device users need to read previously received attachments, re-push the Exchange setting to the devices. Ivanti advises caution when re-pushing the Exchange setting. Re-pushing the Exchange setting increases the load on the Exchange server. See Re-pushing Exchange settings.
Configuring AES-256-GCM encryption for email attachments
If you previously had Docs@Work (Original) enabled, attachments are encrypted with AES-128. To use 256-bit encryption, you must disable Docs@Work (Original) and enable Docs@Work.
Procedure
| 1. | Ensure that all Sentrys configured on Ivanti EPMM are at least Version 6.1. |
| 2. | In the Admin Portal, go to Settings > Preferences. |
| 3. | Scroll down to the Additional Products section. |
| 4. | De-select Enable Docs@Work (Original). |
| 5. | Ensure that Enable Docs@Work is enabled. |
| 6. | Click Save. |
| 7. | Go to Services > Sentry, and click Preferences. |
| 8. | In the Standalone Sentry section, click Regenerate Key. |