Upgrade information
This section provides the upgrade information for this release and contains the following sections:
- Before you upgrade Ivanti Standalone Sentry
- Ivanti Standalone Sentry upgrade paths
- Upgrade URL for CLI upgrades for Ivanti Standalone Sentry
- TLS compliance utility
- Upgrade notes for Standalone Sentry
- Upgrade steps for Ivanti Standalone Sentry
Before you upgrade Ivanti Standalone Sentry
- Ensure that the Ivanti Standalone Sentry System Manager (MICS) portal certificate has not expired.
If the Standalone Sentry portal certificate has expired prior to a software upgrade, Standalone Sentry generates a new self-signed certificate after the upgrade and does not initialize correctly. As a result, the Standalone Sentry System Manager (MICS) on port 8443 and the Standalone Sentry server on port 443 will not be accessible. The "show log message" CLI displays the following error: "portal-ca-setup: /mi/portalCA/ca-cert.pem not valid for /mi/portalCA/server-cert.pem". - Plan for 5 to 20 minutes downtime. Email and app tunnel traffic will be down during the upgrade.
- If you have multiple Standalone Sentry in your installation, allow for a rolling upgrade to minimize downtime. Do not upgrade all Sentry instances at the same time.
- Ensure that Ivanti EPMM is running and reachable to allow Standalone Sentry to upgrade successfully.
- Verify that your current environment meets the requirements as listed in the Support and compatibility of this document.
- Check disk space availability. At least 5 GB of disk space must be available in the / (root) directory for an upgrade to be successful.
- Back up the Standalone Sentry installation configuration.
- Test your connection to support.mobileiron.com. You can use the following command:
telnet support.mobileiron.com 443. - Ensure that supportcdn.mobileiron.com is reachable.
- For improved security, Ivanti recommends that TLS v1.2 is used and TLS v1.0 and v1.1 are disabled. Run the TLS compliance utility to check the TLS compliance for the servers connecting to Standalone Sentry. See TLS compliance utility.
- See also Upgrade notes for Standalone Sentry.
Ivanti Standalone Sentry upgrade paths
The following table provides the supported upgrade paths for Ivanti Standalone Sentry for this release.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.7.0 |
|
10.5.0 |
10.5.0 > 10.7.0 |
|
10.6.0 |
10.6.0 > 10.7.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.6.1 |
|
10.4.2 |
10.4.2 > 10.6.1 |
|
10.5.0 |
10.5.0 > 10.6.1 |
|
10.5.1 |
10.5.1 > 10.6.1 |
|
10.6.0 |
10.6.0 > 10.6.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.6.0 |
|
10.4.1 |
10.4.1 > 10.6.0 |
|
10.4.1 |
10.4.1 > 10.5.0 > 10.6.0 |
|
10.5.0 |
10.5.0 > 10.6.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.5.1 |
|
10.3.1 |
10.3.1 > 10.5.1 |
|
10.4.1 |
10.4.1 > 10.5.1 |
|
10.4.2 |
10.4.2 > 10.5.1 |
|
10.5.0 |
10.5.0 > 10.5.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.5.0 |
|
10.3.1 |
10.3.1 > 10.5.0 |
|
10.4.0 |
10.4.0 > 10.5.0 |
|
10.4.0 |
10.4.0 > 10.4.1 > 10.5.0 |
|
10.4.1 |
10.4.1 > 10.5.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.4.2 |
|
10.2.1 |
10.2.1 > 10.4.2 |
|
10.3.1 |
10.3.1 > 10.4.2 |
|
10.4.1 |
10.4.1 > 10.4.2 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.4.1 |
|
10.2.0 |
10.2.0 > 10.4.1 |
|
10.3.0 |
10.3.0 > 10.4.1 |
|
10.3.1 |
10.3.1 > 10.4.1 |
|
10.4.0 |
10.4.0 > 10.4.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.4.0 |
|
10.2.0 |
10.2.0 > 10.4.0 |
|
10.3.0 |
10.3.0 > 10.4.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.3.1 |
|
10.1.0 |
10.1.0> 10.3.1 |
|
10.2.0 |
10.2.0 > 10.3.1 |
|
10.2.1 |
10.2.1 > 10.3.1 |
|
10.3.0 |
10.3.0 > 10.3.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.3.0 |
|
10.1.0 |
10.1.0 > 10.3.0 |
|
10.2.0 |
10.2.0 > 10.3.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.2.1 |
|
10.0.2 |
10.0.2 > 10.2.1 |
|
10.1.0 |
10.1.0 > 10.2.1 |
|
10.2.0 |
10.2.0 > 10.2.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.2.0 |
|
10.0.0 |
10.0.0 > 10.2.0 |
|
10.0.1 |
10.0.1 > 10.2.0 |
|
10.0.2 |
10.0.2 > 10.2.0 |
|
10.0.0 |
10.0.0 > 10.0.2 > 10.1.0 |
|
10.1.0 |
10.1.0 > 10.2.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.1.0 |
|
10.0.0 |
10.0.0 > 10.1.0 |
|
10.0.1 |
10.0.1 > 10.1.0 |
|
10.0.2 |
10.0.2 > 10.1.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.0.2 |
|
9.20.0 |
9.20.0 > 10.0.2 |
|
9.20.1 |
9.20.1 > 10.0.2 |
|
9.20.2 |
9.20.2 > 10.0.2 |
|
10.0.0 |
10.0.0 > 10.0.2 |
|
10.0.1 |
10.0.1 > 10.0.2 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 10.0.1 |
|
9.20.0 |
9.20.0 > 10.0.1 |
|
9.20.1 |
9.20.1 > 10.0.1 |
|
10.0.0 |
10.0.0 > 10.0.1 |
We recommend you upgrade to the latest Sentry version. To upgrade to the Sentry 10.0.1 release, you must first upgrade to version 9.20.0.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.20.2 |
|
9.18.0 |
9.18.0 > 9.20.2 |
|
9.18.1 |
9.18.1 > 9.20.2 |
|
9.19.0 |
9.19.0 > 9.20.2 |
|
9.19.1 |
9.19.1 > 9.20.2 |
|
9.19.2 |
9.19.2 > 9.20.2 |
|
9.20.0 |
9.20.0 > 9.20.2 |
|
9.20.1 |
9.20.1 > 9.20.2 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.20.1 |
|
9.20.0 |
9.20.0 > 9.20.1 |
|
9.19.0 |
9.20.0 > 9.20.1 |
|
9.19.1 |
9.19.1 > 9.20.1 |
|
9.19.2 |
9.19.2 > 9.20.1 |
|
9.18.0 |
9.18.0 > 9.20.1 |
|
9.18.1 |
9.18.1 > 9.20.1 |
We recommend you upgrade to the latest Sentry version. To upgrade to the Sentry 10.0.1 release, you must first upgrade to version 9.20.0.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.20.0 |
|
9.19.0 |
9.19.0 > 9.20.0 |
|
9.19.1 |
9.19.1 > 9.20.0 |
|
9.19.2 |
9.19.2 > 9.20.0 |
|
9.18.0 |
9.18.0 > 9.20.0 |
|
9.18.1 |
9.18.1 > 9.20.0 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.19.2 |
|
9.19.0 |
9.19.0 > 9.19.2 |
|
9.19.1 |
9.19.1 > 9.19.2 |
|
9.18.0 |
9.18.0 > 9.19.2 |
|
9.18.1 |
9.18.1 > 9.19.2 |
|
9.17.0 |
9.17.0 > 9.19.2 |
|
9.17.1 |
9.17.1 > 9.19.2 |
We recommend you upgrade to the latest Sentry version. To upgrade to the Sentry 10.0.1 release, you must first upgrade to version 9.20.0.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.19.1 |
|
9.19. 0 |
9.19.0 > 9.19.1 |
|
9.18.0 |
9.18.0 > 9.19.1 |
|
9.18.1 |
9.18.1 > 9.19.1 |
|
9.17.0 |
9.17.0 > 9.19.1 |
|
9.17.1 |
9.17.1 > 9.19.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.19.0 |
|
9.18.0 |
9.18.0 > 9.19.0 |
|
9.18.1 |
9.18.1 > 9.19.0 |
|
9.17.0 |
9.17.0 > 9.19.0 |
|
9.17.1 |
9.17.1 > 9.19.0 |
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.18.1 |
|
9.18.0 |
9.18.0 > 9.18.1 |
|
9.17.0 |
9.17.0 > 9.18.1 |
|
9.17.1 |
9.17.1 > 9.18.1 |
|
9.16.0 |
9.16.0 > 9.18.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.18.0 |
|
9.17.0 |
9.17.0 > 9.18.0 |
|
9.17.1 |
9.17.1 > 9.18.0 |
|
9.16.0 |
9.16.0 > 9.18.0 |
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.17.1 |
|
9.17.0 |
9.17.0 > 9.17.1 |
|
9.16.0 |
9.16.0 > 9.17.1 |
|
9.15.0 |
9.15.0 > 9.17.1 |
We recommend you upgrade to the latest Sentry version.
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.17.0 |
|
9.16.0 |
9.16.0 > 9.17.0 |
|
9.15.0 |
9.15.0 > 9.17.0 |
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.16.0 |
|
9.14.0 |
9.14.0 > 9.16.0 |
|
9.14.0 |
9.14.0 > 9.15.0 > 9.16.0 |
|
9.15.0 |
9.15.0 > 9.16.0 |
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.15.0 |
|
9.13.0 |
9.13.0 > 9.14.0 > 9.15.0 |
|
9.13.0 |
9.13.0 > 9.15.0 |
|
9.14.0 |
9.14.0 > 9.15.0 |
|
Current Ivanti Standalone Sentry version |
Upgrade path to 9.14.0 |
|
9.12.0 |
9.12.0 > 9.14.0 |
|
9.13.0 |
9.13.0 > 9.14.0 |
Sentry upgrade from Sentry 9.12.0 to Sentry 9.14.0 is not supported for AWS.
Upgrade URL for CLI upgrades for Ivanti Standalone Sentry
To upgrade Ivanti Standalone Sentry, use the following URL if you specify an alternate URL:
Use the following URL if you are upgrading from 10.6.0 to 10.7.0:
https://support.mobileiron.com/mi/sentry/10.7.0-8/
Use the following URL if you are upgrading from 10.6.0 to 10.6.1:
https://support.mobileiron.com/mi/sentry/10.6.1-7/
Use the following URL if you are upgrading from 10.5.0 to 10.6.0:
https://support.mobileiron.com/mi/sentry/10.6.0-18/
Use the following URL if you are upgrading from 10.4.1 to 10.6.0:
https://support.mobileiron.com/mi/sentry/10.6.0-18/
Use the following URL if you are upgrading from 10.5.0 to 10.5.1:
https://support.mobileiron.com/mi/sentry/10.5.1-7/
Use the following URL if you are upgrading from 10.4.1 to 10.5.0:
https://support.mobileiron.com/mi/sentry/10.5.0-7/
Use the following URL if you are upgrading from 10.4.1 to 10.4.2:
https://support.mobileiron.com/mi/sentry/10.4.2-7/
Use the following URL if you are upgrading from 10.4.0 to 10.4.1:
https://support.mobileiron.com/mi/sentry/10.4.1-3/
Use the following URL if you are upgrading from 10.3.0 to 10.4.0:
https://support.mobileiron.com/mi/sentry/10.4.0-5/
Use the following URL if you are upgrading from 10.3.0 to 10.3.1:
https://support.mobileiron.com/mi/sentry/10.3.1-3/
Use the following URL if you are upgrading from 10.2.0 to 10.3.0:
https://support.mobileiron.com/mi/sentry/10.3.0-17/
Use the following URL if you are upgrading from 10.2.0 to 10.2.1:
https://support.mobileiron.com/mi/sentry/10.2.1-4/
Use the following URL if you are upgrading from 10.1.0 to 10.2.0:
https://support.mobileiron.com/mi/sentry/10.2.0-16/
Use the following URL if you are upgrading from 10.0.1 to 10.1.0:
https://support.mobileiron.com/mi/sentry/10.1.0-27/
Use the following URL if you are upgrading from 10.0.1 to 10.0.2:
https://support.mobileiron.com/mi/sentry/10.0.2-4/
Use the following URL if you are upgrading from 9.20.x to 10.0.2:
https://support.mobileiron.com/mi/sentry/10.0.2-4/upgrader/sentry-mobileiron-10.0.2-4/
Use the following URL if you are upgrading from 9.20.1 to 9.20.2:
https://support.mobileiron.com/mi/sentry/9.20.2-10/
Use the following URL if you are upgrading from 10.0.0 to 10.0.1:
https://support.mobileiron.com/mi/sentry/10.0.1-10/
Use the following URL if you are upgrading from 9.20.x to 10.0.1:
https://support.mobileiron.com/mi/sentry/10.0.1-10/upgrader/sentry-mobileiron-10.0.1-10/
https://support.mobileiron.com/mi/sentry/9.20.0/
https://support.mobileiron.com/mi/sentry/9.19.1/
https://support.mobileiron.com/mi/sentry/9.19.0/
https://support.mobileiron.com/mi/sentry/9.18.0/
https://support.mobileiron.com/mi/sentry/9.17.0/
https://support.mobileiron.com/mi/sentry/9.16.0/
https://support.mobileiron.com/mi/sentry/9.15.0/
https://support.mobileiron.com/mi/sentry/9.14.0/
TLS compliance utility
Ivanti provides an utility that checks if Sentry can successfully connect with the server on TLS v1.2.
You must have Sentry 9.6.0 or later as a minimum version of TLS compliance utility.
TLS 1.1 and TLS 1.0 support: TLS 1.1 and TLS 1.0 is not supported with Sentry 9.16.0 and later versions. For more information, see KB article.
From the Standalone Sentry command line interface, enter the following command in EXEC PRIVILEGED mode to run the utility:
#install rpm url https://support.mobileiron.com/tlscheck/mobileiron-sentry-tlscheck-1.0.0-1.noarch.rpm
The command executes a script that checks the servers that Sentry connects with and returns an OK or FAILED value for each server it checks. The script uninstalls after each run.
The results are also recorded into a log file /var/log/TLSTrafficTool-timestamp.log. The log file is included in ShowTech-All. In case of failure, additional error message content as provided by OpenSSL displays and is recorded in the log file. Ivanti recommends upgrading the failed servers to support TLS v1.2.
After upgrading to 9.7.0, use the tlscheck command from the Standalone Sentry command line interface (CLI) to check TLS compliance. See "Using CLI command to check TLS compliance" in the Sentry Guide.
Upgrade notes for Standalone Sentry
Before you upgrade, read the following upgrade notes:
Telnet
Telnet server capability is not supported from Standalone Sentry 9.5.0 onwards. Disable Telnet before upgrading to 9.7.0. Upgrade fails if Telnet is not disabled. You will see the following Preflight check failed error message if Telnet is enabled.
Figure 1. Preflight check failed error message
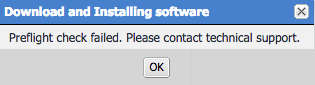
Click OK, then disable Telnet. To disable Telnet, in Standalone Sentry system manager, go to Settings > CLI.
You will also see the following log message in Monitoring > Alert Viewer:
Upgrade failure: Telnet server is not supported anymore. You must first disable telnet before upgrade. The system will continue to run as Current Sentry Version.
Support for SMB
Ivanti dropped support for SMB 1.0 CIFS servers and added support for SMB 3.x, 2.0, and 2.1. If you were accessing an SMB 1.0 CIFS server through Standalone Sentry, upgrading to Standalone Sentry 9.4.1 through the latest version as supported by Ivanti results in users not being able to authenticate and therefore access the CIFS server.
SMB 3.x is enabled by default after upgrading to 9.17.0
Workaround: Ivanti recommends updating the file server to SMB 3.x, 2.0, or 2.1 before upgrading to Standalone Sentry 9.4.1 through the latest version as supported by Ivanti.
Supported upgrade versions for Ivanti Standalone Sentry
If you are upgrading from a version not listed in Ivanti Standalone Sentry upgrade paths, then you need to complete one or more previous upgrades first. See the release notes for the version to which you will upgrade.
Upgrade steps for Ivanti Standalone Sentry
For upgrade instructions, see the following sections in the Sentry Guide for the release:
- For upgrade instructions using the Ivanti Standalone Sentry System Manager UI, see “Standalone Sentry software updates.”
- For upgrade instructions using the Ivanti Standalone Sentry command line interface (CLI), see “Upgrading using CLI.”
- For multiple Sentry upgrade instructions using the Ivanti Standalone Sentry CLI, see "Upgrading multiple Standalone Sentry."