Self Elevation
Self-Elevation gives users the ability to elevate specific applications.
Privilege Management is used to configure self-elevation, you specify a list of file types and associated applications that users can open with elevated or administrative privileges.
You can apply self-elevation to files, folders and file hashes that usually require administrative privileges to run and function. Self-Elevation provides an option from the right-click Windows Explorer shortcut menu to run an item with elevated rights. You can specify that when a user attempts to elevate a specified item they must submit a reason for the elevation before it is applied.
Audit self-elevation so you can monitor the types of applications that users typically want to self-elevate. You can then decide whether to add these items to the appropriate Privilege Management rule set, so users can access them without request.
Try it yourself
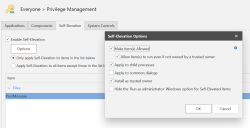
- In the Application Control Configuration Editor select Rule Sets > Group > Everyone > Privilege Management.
- In the right-hand work area select the Self-Elevation tab.
- Turn the Self-Elevation functionality on by selecting Enable Self-Elevation.
- Build the list of files, folders or file hashes by adding items. In this example we'll add file Procmon.exe which requires administrator rights to install.
- Select whether self-elevation is to only apply to the list of items or to apply to all items except for those in the list. We'll select to Only apply Self-Elevation to items in the list below.
- Save and deploy the configuration.
You will need to select Options > Make item(s) Allowed and Allow item(s) to run even if it not owned by a trusted owner if any users are not on the trusted owners list as Trusted Ownership is a higher priority in the rule processing order, see Creating an AC Configuration for more details.
Test it
- Download Procmon.exe and attempt to install it, access will be denied.
- Now right-click on the file and select Run with Administrative Privileges (Audited), the installer should now run.