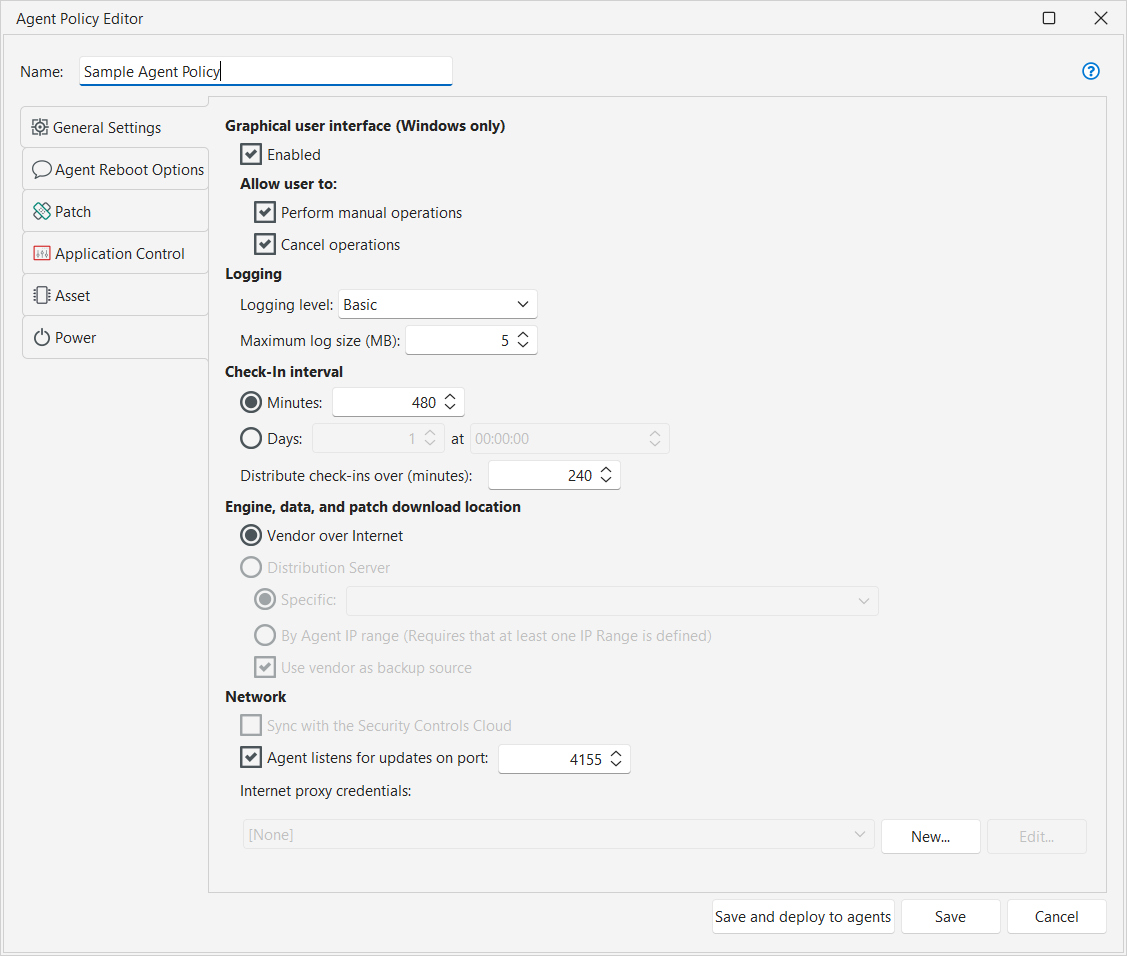
Configuring General Settings for a Security Controls Agent Policy
There are a number of general settings to configure for a Security Controls Agent policy. You must configure these settings before installing the agents on the desired target machines.
|
Field |
Description |
|---|---|
|
Enabled |
(Windows-based machines only) Specifies if the agent user interface will be installed. One reason you may not want the agent client program installed is if you do not allow Microsoft .NET on your agent machines; the agent client requires the use of Microsoft .NET. If the agent client is not installed, you can use the stagentctl command-line utility to control the agent on the target machine. |
|
Perform manual operations |
(Windows-based machines only) Enables a user on a target machine to manually initiate an operation such as a patch scan. |
|
Cancel operations |
(Windows-based machines only) Enables a user on a target machine to stop an operation that is in progress. |
|
Logging level |
Specify the amount of logging you want the agent to perform. The options are:
The log files will reside on each agent machine in the following location: C:\ProgramData\LANDESK\Shavlik Protect\Logs |
|
Maximum log size |
Specify the maximum log size. Specifying a very large log size will enable you to record a longer log history but it will of course require more system resources. The default value is 5 MB. If the log file becomes full a new log file is opened and logging will continue. If the second log file becomes full, the first log file is deleted and a new log file will be created. This means there will always be a maximum of two log files on the console. |
|
Check-In interval |
Specifies how often the agents will check in (synchronize) with the console. At each check-in the agent refreshes its license, it looks for any policy changes and it determines if a newer version of the agent is available. It also checks if it is assigned a distribution server. If it is assigned a distribution server it will use it to download the latest engine components and data definition files. If it is not assigned to a distribution server then the agent downloads the engines and data files from the Web. If an agent machine is offline when the next check-in interval occurs, the agent will immediately check in when network connectivity is restored. Agent licenses must be refreshed at least once every 45 days or they will expire.
|
|
Engine, data, and patch download location |
Specifies if a distribution server will be used by the agents when downloading the latest engine components, data definition files, and patches. The agents will look for updated files every time they perform a scan. The available options are: In Linux agent environments, distribution servers can be used to download core files but not patches. Linux agents use YUM to download any patches that must be deployed.
If the agents are being used to deploy custom patches then you must specify the use of a distribution server. This is because there is no download URL for custom patches, meaning the agents cannot pull the custom patches from a vendor and must therefore be able to pull them from one or more distribution servers. |
|
Bandwidth Utilization |
Specifies the throttle percentage controls of the available network bandwidth the agent is allowed to use during patch downloads. It allows to configure LAN and WAN/Internet bandwidth limits. 100% indicates that the agent can use the full available bandwidth and it is the default value. Minimum throttling limit that can be set is 1%. |
|
Network |
Only shared credentials are contained in this list. If the credential you are looking for is not listed it probably means it is not defined as a shared credential. See Defining Credentials for information on how to share a credential. |
|
Save and deploy to agents |
Saves all changes to the policy file and stores it on the console. Also updates any agent machines that are currently assigned this policy as follows:
The Agent Policy Editor will be closed. |
|
Cancel |
Indicates you want to exit the Agent Policy Editor without saving your most recent changes. A "Do you want to save your changes?" prompt will appear that gives you a second chance to save your changes. If you click Yes the policy will be saved and the associated agents updated (the same as Save and deploy to agents). If you click No the Agent Policy Editor will be closed without saving your changes. |